Internet of Things - Desire for Convenience Brings Multiple New Attack Vectors
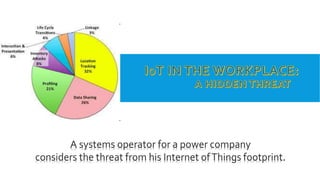
- 1. A systems operator for a power company considers the threat from his Internet ofThings footprint.
- 2. The power company I work for has tight network security. We do a SOC 1 type 2 audit every year with excellent results.
- 3. W E ’ V E N E V E R H A D A S E C U R I T Y B R E A C H . I T N E V E R O C C U R R E D T O M E T H AT A N Y T H I N G I C O U L D B E D O I N G W O U L D B E C O N S I D E R E D A T H R E AT.
- 4. I saw a video on YouTube about IoT and the threats to corporate networks that made me think about my IoT footprint.
- 5. The video said that there would be 50 billion IoT devices by 2020, and that many were not secure and could be hacked. ("IoT Connections to Grow 140% to Hit 50 Billion By 2022," n.d.)
- 6. I started thinking about my fitbit. I wonder if there are any threats associated with wearing it to work.
- 7. I did a search on the Internet. If a bad actor wanted to gain physical access to the power company where I work, any IoT devices like the fitbit that track the location of power company workers and transmit the data over the Internet could be a valuable source of information. According to Deputy Defense Secretary Patrick Shanahan, “These geolocation capabilities can expose personal information, locations, routines, and numbers of DoD personnel, and potentially create unintended security consequences and increased risk…” ("Turn Off Your Fitbit, Garmin, Apple Watch GPS NOW!," 2018)
- 8. I also found information about a malware attack from 2015. This vulnerability, discovered by Fortinet, allowed a hacker to access the fitbit by Bluetooth and then upload malware to the device. When the device is then connected to a computer, the computer could be infected with the virus. This was disputed by fitbit, but it brings up a good point. Any IoT device that an employee of the power company brings to work that is connected to their work computer could possibly infect the computer. This is alarming, because I know a lot of people who connect their smartphones to their computers at work. (Pauli, 2015)
- 9. Reading about the security concerns with the fitbit made me think about the security of my iPhone.This could potentially be a greater attack vector, because it is practically a full-blown computer with its own applications.
- 10. Not only does the iPhone’s IOS operating system have vulnerabilities that are constantly being patched, but each application could potentially be a point of vulnerability.
- 11. In 2017, it was discovered that the iTunes and the App Store both had script injection vulnerabilities that could allow an attacker to inject malicious code. (Brook, 2017)
- 12. I connect my iPhone to the company’s wireless. I don’t always update it when a new version of IOS comes out. I’m sure I need to be more vigilant when it comes to keeping my phone updated. I did some research on iPhone vulnerabilities, and what I found was quite disturbing.
- 13. Mobile remote-accessTrojans can jailbreak a device and install surveillance andTrojan software that gives the attacker remote access to the device.
- 14. There are fake IOS certificates that can allow a hacker to side-load an application with malware.
- 15. A user can be tricked into downloading a malicious profile, which can divert the traffic from the phone to a rogue server, install malicious apps, or decrypt encrypted sessions.
- 16. An attacker can perform a man-in-the-middle attack on the phone by installing a rogue wireless access point.
- 17. An attacker can exploit a vulnerability in a WebKit to execute malicious scripts on the phone with the purpose of infecting the device.
- 18. Zero-day attacks can enable a hacker to steal passwords, corporate data, and emails or capture keyboard activity or screen information from the phone. (Staff, 2014)
- 19. I STARTEDTOTHINK ABOUT MY INTERNET CAMERA AT HOME. THESE CAMERAS ARE EASILY HACKABLE.THE HACKER CAN ACCESSTHEVIDEO THE CAMERA RECORDS. I OFTENTALKTO MYWIFE ABOUTWORKWHEN I’M AT HOME. ITWOULD BEVERY BAD IF A HACKER COULD HEARTHESE PRIVATE CONVERSATIONS.
- 20. IP cameras can also be used in DDoS attacks. There was a famous attack against Dyn in October, 2016. They are an internet provider for Amazon, Netflix, and Twitter. The attack froze the internet for hours. The botnet used in the attack was composed of IoT devices, many of which were IP cameras. ("New Threat Against Corporate Security…Security Cameras," 2018)
- 21. I have an app for the camera on my phone. If the camera is compromised, it’s possible that the app on my phone could become infected and spread malware to the corporate network over the wireless connection.
- 22. Looking into the devices I bring to work every day made me start to think about how many IoT devices there are when you consider all the users in our company.
- 23. One change the power company may want to make is isolating the wireless so it can’t access the corporate network.
- 24. AN IOT SECURITY AWARENESS PROGRAM FOR ALL EMPLOYEES OF THE POWER COMPANY WOULD BE A GOOD IDEA.
- 25. A corporate policy for IoT that mandated that users keep their devices updated might also be a good idea. An MDM solution that could keep users’ phones up to date with security updates would be a good control as well. It would probably make sense to tell users that with devices like fitbit they shouldn’t connect them to corporate assets. A group policy that prevents users from installing software would help with this.
- 26. IoT security for businesses is becoming more important as the number of devices grows each year. This is especially important to a business like a power company, where an outage could be a public hazard. User awareness is key, but there are also security controls an organization can put into place to mitigate the threats to IoT devices that connect to corporate networks.
- 27. References A New Threat Against Corporate Security…Security Cameras. (2018, February 20). Retrieved from https://www.pandasecurity.com/mediacenter/security/security-cameras-threat- against-companies/ Fitbit trackers can be hacked in '10 seconds' (update: Fitbit disagrees). (2015, October 21). Retrieved from https://www.engadget.com/2015/10/21/fitbit-tracker-bluetooth- vulnerability/ IoT Connections to Grow 140% to Hit 50 Billion By 2022. (n.d.). Retrieved from https://www.juniperresearch.com/press/press-releases/iot-connections-to-grow-140- to-hit-50-billion Turn Off Your Fitbit, Garmin, Apple Watch GPS NOW! (2018, August 6). Retrieved from https://breakingdefense.com/2018/08/turn-off-your-fitbit-garmin-apple-watch-gps-now/
- 28. Brook, C. (2017, January 17). Vulnerabilities Leave iTunes, App Store Open to Script Injection. Retrieved from https://threatpost.com/vulnerabilities-leave- iTunes-app-store-open-to-script-injection/123129/ Pauli, D. (2015, October 21). '10-second' theoretical hack could jog Fitbits into malware-spreading mode. Retrieved from https://www.theregister.co.uk/2015/10/21/fitbit_hack/ Staff, C. (2014, October 14). Top 6 threats to iOS devices. Retrieved from https://www.csoonline.com/article/2826038/mobile-security/top-6-threats-to- ios-devices.html