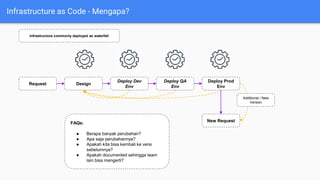
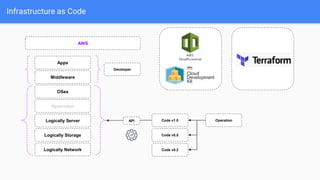
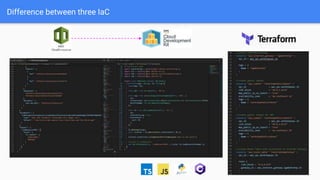
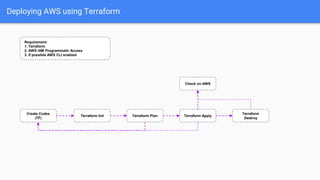
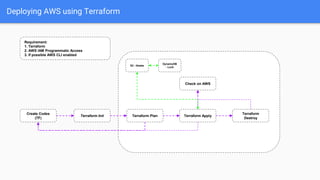
This document discusses infrastructure as code using Terraform on AWS. It introduces infrastructure as code and why it is important compared to traditional infrastructure deployment methods. Some key benefits highlighted are having code to represent infrastructure that can be version controlled, allowing infrastructure to be deployed in an automated and repeatable way. The document then demonstrates deploying AWS infrastructure like VPCs, subnets, security groups, load balancers etc. using Terraform code. It shows the workflow of initializing, planning and applying Terraform code to provision the AWS resources.