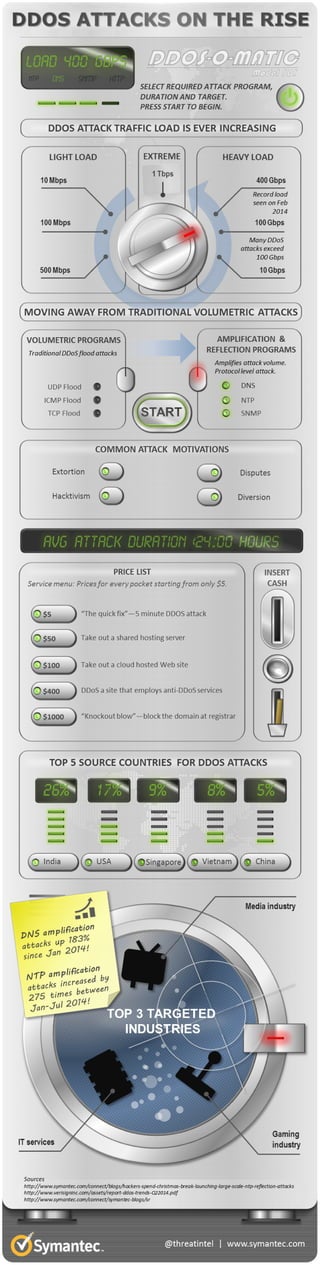
INFOGRAPHIC▶DDoS Attacks on the Rise
Distributed denial-of-service (DDoS) attacks are not a new concept, but they have proven to be effective. In the last few years they have grown in intensity as well as in number, whereas the duration of an attack is often down to just a few hours. Such attacks are simple to conduct for the attackers, but they can be devastating for the targeted companies. Amplification attacks especially are very popular at the moment as they allow relatively small botnets to take out large targets. For such an attack, spoofed traffic is sent to a third-party service, which will reflect the answer to the spoofed target. In order to amplify the response traffic, a smart query is chosen that leads to a very large answer from the service. For example, this could be requesting all records from a DNS server or using the monlist command for NTP servers. There are a handful of protocols that can be used to achieve this effect, sometimes with an amplification factor of up to 500. From January to August 2014, Symantec has seen a 183 percent increase in DNS amplification attacks, making it the most popular method seen by Symantec’s Global Intelligence Network. Amplification DDoS attacks using NTP were prominent in Q1, but have since been steadily decreasing. This may be due to various people upgrading and reconfiguring their servers. Attackers are also experimenting with other protocols like the Simple Network Management Protocol (SNMPv2) or, as seen in September, the Simple Service Discovery Protocol (SSDP). Multiple methods are often used by attackers in order to make mitigation difficult and, to make matters worse, DDoS attack services can be hired for less than US$10 on underground forums. Another trend seen in 2014 is the increase in Unix servers being compromised and their high bandwidth being used in DDoS attacks. PHP.Brobot and Backdoor.Piltabe are two examples of such threats, but the trend came to the forefront again when the ShellShock Bash vulnerability was exploited within hours of the bug’s discovery, allowing attackers to install DDoS scripts on a variety of servers. Various DDoS scripts and malicious ELF files were downloaded through the Bash vulnerability, creating a powerful DDoS botnet. The forecast for the future looks dark, as we expect to see many DDoS attacks during Guy Fawkes Day on November 5, as the Anonymous collective has already announced various activities under the Operation Remember campaign. However, hacktivists protesting for their ideological beliefs are not the only ones using DDoS attacks. We have also seen cases of extortion where targets have been financially blackmailed, as well as some targeted attacks using DDoS as a diversion to distract the local CERT team while the real attack was being carried out.