The document provides information about implementing the IBM Storwize V3700 storage system. It includes an overview of the hardware components and features of the Storwize V3700. The document also covers initial configuration tasks such as planning the hardware and network setup, performing the first-time setup, and configuring features like expansion enclosures, alerts, and inventory. It provides guidance on using the graphical and command-line interfaces to manage and monitor the storage system.



























































































































































































































































































































































![356 Implementing the IBM Storwize V3700
Figure 7-68 illustrates the concept of Child Pools.
Figure 7-68 Child Pool representation
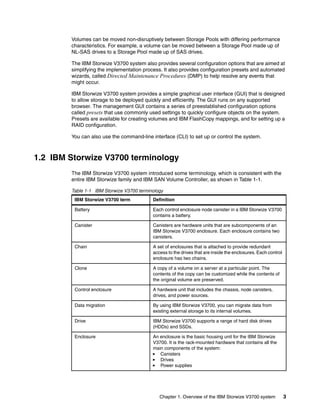
7.4.1 Create Child Pools
Example 7-9 demonstrates how to create a Child Pool using the CLI.
Example 7-9 Creating a Child Pool
IBM_Storwize:ITSO_V3700:superuser>svctask mkmdiskgrp -name V37K_ChildP_1 -warning
80 -parentmdiskgrp V3700_Pool2 -unit gb -size 100
MDisk Group, ID [0], successfully created
The following parameters must be specified when creating Child Pools:
-name (Child Pool name)
-warning (Generates a warning when the used disk capacity exceeds the specified
threshold)
-parentmdiskgrp (The ID or name of the Parent Pool)
-unit (Specifies the data unit; it must be in multiples of extent size of the parent pool)
-size (Specifies the capacity of the Child Pool)
Note: The capacity of the Child Pool is always limited by the free capacity of the parent
pool.](https://image.slidesharecdn.com/implementingtheibmstorwizev3700-160802150058/85/Implementing-the-ibm-storwize-v3700-376-320.jpg)





















































































































































































































































































![662 Implementing the IBM Storwize V3700
2. Enter lshost to see a list of all configured hosts on the system, as shown in Example A-3.
Example: A-3 List hosts
IBM_Storwize:ITSO_V3700:superuser>lshost
id name port_count iogrp_count status
0 windows2008r2 2 4 online
3. To map the volume to the hosts, enter mkvdiskhostmap, as shown in Example A-4.
Example: A-4 Map volumes to host
IBM_Storwize:ITSO_V3700:superuser>mkvdiskhostmap -host ESXi-1 -scsi 0 -force
ESXi-Redbooks
Virtual Disk to Host map, id [0], successfully created
4. To verify the host mapping, enter lsvdiskhostmap, as shown in Example A-5.
Example: A-5 List all hosts that are mapped to a volume
IBM_Storwize:ITSO_V3700:superuser>lshostvdiskmap ESXi-1
id name SCSI_id vdisk_id vdisk_name vdisk_UID
4 ESXi-1 0 2 ESXi-Redbooks 600507680185853FF000000000000011
5. In the CLI, there are more options available than in the GUI. All advanced settings can be
set (for example, I/O throttling). To enable I/O throttling, change the properties of a volume
by using the changevdisk command, as shown in Example A-6. To verify the changes, run
the lsvdisk command.
Example: A-6 Enable advanced properties: I/O throttling
IBM_Storwize:ITSO_V3700:superuser>chvdisk -rate 1200 -unit mb ESXi-Redbooks
IBM_Storwize:ITSO_V3700:superuser>
IBM_Storwize:ITSO_V3700:superuser>lsvdisk ESXi-Redbooks
id 2
name ESXi-Redbooks
.
.
vdisk_UID 600507680185853FF000000000000011
virtual_disk_throttling (MB) 1200
preferred_node_id 2
.
.
IBM_Storwize:ITSO_V3700:superuser>
Command output: The lsvdisk command lists all available properties of a volume and
its copies. To make it easier to read, lines in Example A-6 were deleted.](https://image.slidesharecdn.com/implementingtheibmstorwizev3700-160802150058/85/Implementing-the-ibm-storwize-v3700-682-320.jpg)