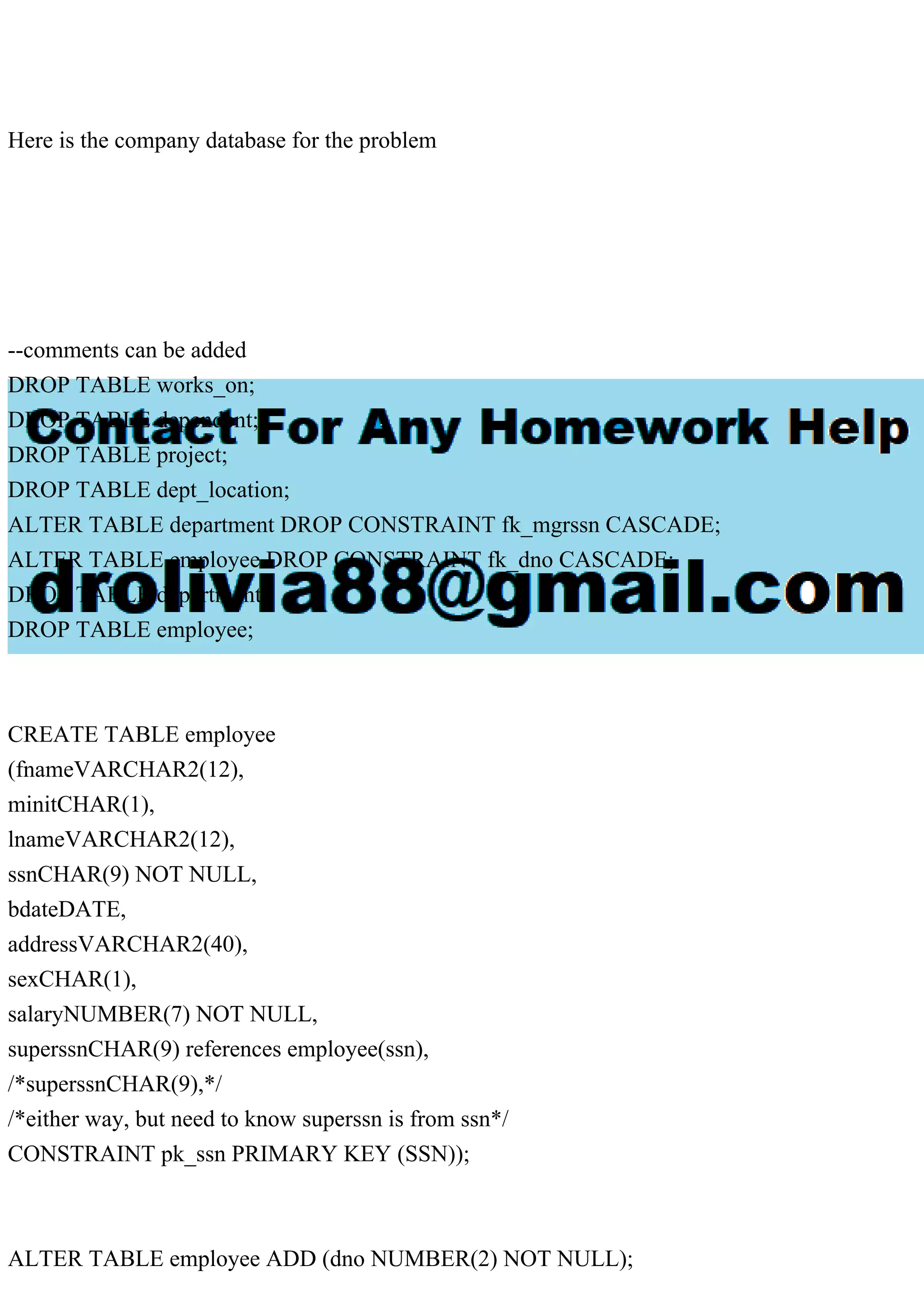
The document outlines the creation and manipulation of an employee database within Oracle, including table structures for employee, department, project, dependent, and works_on tables. It contains SQL commands to create, drop, and modify these tables, as well as insert employee and project data, while detailing foreign key relationships. Additionally, it explains how ownership of database objects impacts queries and permissions, emphasizing the necessity of using the correct account in SQL statements.