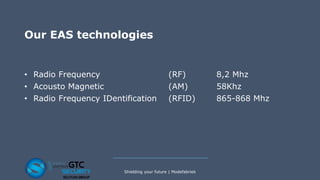
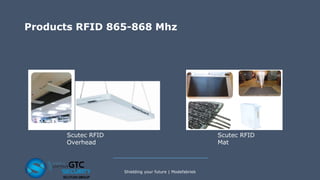
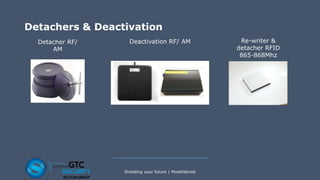
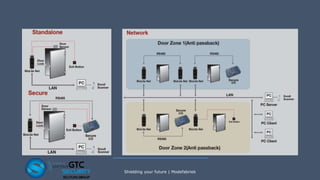
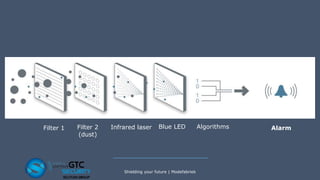
GTC Security, a member of the Scutum Group, offers a range of security solutions including access control, surveillance, intrusion detection, and electronic article surveillance across multiple European countries. Their technologies utilize methods such as RFID, RF, and AM to enhance security and operational efficiency in retail and other sectors. The company emphasizes integrating intelligent camera systems for improved management insights and provides tailored security solutions for businesses of all sizes.