Embed presentation
Download to read offline

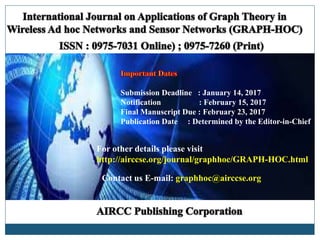
graph-hoc is a quarterly open access peer-reviewed journal that focuses on graph theory applications in wireless ad hoc networks, including mobile, vehicular, and sensor networks. It covers various topics such as connectivity, data gathering, routing, and energy efficiency, offering a platform for researchers to exchange ideas. Authors are invited to submit original papers, with specific submission deadlines and guidelines provided.