Report
Share
Download to read offline
Recommended
Open source intelligence information gathering (OSINT)

Open Source Intelligence Information Gathering
Evidon Benchmark Report 12.23.13

Evidon Benchmark Reports 12.23.13 - Covering travel, retail, finance, and online
Cyber security macau 

The convergence of information and cybersecurity is highly relevant in the context of your reputational and financial concerns, a combination of physical and cyber security applied to your requirements will strengthen your overall security posture and resilience to risk. In this article I am explaining how to protect your digital security and privacy as an individual, but the strategies are equally suited for small businesses as well.
Internet fraud and Common modes of security threats .pptx

Hello! It is my pleasure to introduce myself as Moiz Ahmed, a student in class 6. I currently live in Karachi, Pakistan. My favorite topic of the presentation is Internet fraud and common modes of security threats, and I love to make PowerPoint presentations about various topics such as science, computer technology, and much more. Hope you will find it informative.
What will activity monitoring be like in 100 years?

We first need to dive a little deeper into the term of “activity monitoring”: according to Gartner the term refers to the aggregation, analysis, and presentation of real-time information about activities inside organizations and involving customers and partners. Phew.
Recommended
Open source intelligence information gathering (OSINT)

Open Source Intelligence Information Gathering
Evidon Benchmark Report 12.23.13

Evidon Benchmark Reports 12.23.13 - Covering travel, retail, finance, and online
Cyber security macau 

The convergence of information and cybersecurity is highly relevant in the context of your reputational and financial concerns, a combination of physical and cyber security applied to your requirements will strengthen your overall security posture and resilience to risk. In this article I am explaining how to protect your digital security and privacy as an individual, but the strategies are equally suited for small businesses as well.
Internet fraud and Common modes of security threats .pptx

Hello! It is my pleasure to introduce myself as Moiz Ahmed, a student in class 6. I currently live in Karachi, Pakistan. My favorite topic of the presentation is Internet fraud and common modes of security threats, and I love to make PowerPoint presentations about various topics such as science, computer technology, and much more. Hope you will find it informative.
What will activity monitoring be like in 100 years?

We first need to dive a little deeper into the term of “activity monitoring”: according to Gartner the term refers to the aggregation, analysis, and presentation of real-time information about activities inside organizations and involving customers and partners. Phew.
Crimes in digital marketing..pptx

This presentation tells about digital marketing meaning and crimes related to it.Any illegal behavior directed by means of electronic operations. that targets the security of computer systems and the data. processed by them is termed cyber crime.
The invention of computer and Information technology related software and equipment has revolutionized the way we do things in many fields.Especially in the science, education, business and commerce it has made far reaching changes.Without using a single sheet of paper, a lot of communications and transactions are done.Automation of businesses, financial institutions and the government records have become widespread.
Many transactions such as sale of goods, transfer of information, transfer of funds and even buying air tickets could be done through the use of computers. The existing laws that governs transactions and information did not address such issues as they were made before the IT era.
The use of internet web 120

A brief definition of how spyware and adware work. A warning to avoid sharing information without realizing the consequences that it may have.
The Ins, Outs, and Nuances of Internet Privacy

Facebook recently came under fire for the discreet international roll-out of its photo facial recognition feature. This feature automatically identifies and suggests tags for individuals appearing in photos posted on Facebook. At first glance, this seemingly innocuous feature appears to quietly augment online social lives. At second glance, the rollout of this feature as a defaulted-to-on setting with no explicit user consent raises many privacy concerns. As a site with extensive power driven by the quantity, quality, and kind of data it collects, Facebook’s decision to step into the world of visual recognition of its users without formal user consent is a big no-no—or is it?
Join us for this month’s eBoost Consulting Brown Bag Lunch Webinar to explore this and other cases that raise internet privacy concerns. Learn the ins, outs, and nuances of internet privacy to determine where to draw the line on data collection and usage.
AI for humans - the future of your digital self

ABSTRACT: In this talk, George will demonstrate the extent and power of personal data collected by technology companies. He will explore the potential of personal data to do both good and bad, the dangers of giving up your "digital DNA", and the value these companies extract from this data.
Data rights are finally legally recognised. With the combination of GDPR & rising awareness of personal data abuse, we might eventually be able to control our data, or at least understand as much about our digital footprint as profit-driven companies do.
AI is only possible because it has data. Imagine your data being used to benefit you, instead of targeting you with gambling adverts. Imagine the potential for next-generation research to understand our society, which can only happen if we break data out from being locked in corporate databases. Data rights are just the start, now we need to use them.
BIO: George Punter holds a first class Masters degree from Imperial College London in Electronics & Information Engineering. He co-founded Ethi (ethi.me), a startup that aims to make controlling your personal data easier, and allow users to use their personal data for their own benefit, or for social good. Ethi is currently partnering with a cyber security firm, TurgenSec, to help create next-generation, user-centred security.
Data Privacy: What you need to know about privacy, from compliance to ethics

Today, balancing business opportunity and customer's data protection has become a difficult challenge. As technology, data sources and targeting abilities grow, so does the crucial need to respect user privacy and ensure a good data protection. But with laws, practices and definitions that are constantly evolving around the world, it can all seem a bit confusing.
Not sure where to start? Wondering how you can better align with privacy law? Then this webinar is for you.
Behavioral tracking : Today's internet trend

Behavioral tracking : how different websites across web follow ur behavior and follow u.
Vishwadeep Presentation On NSA PRISM Spying

In this presentation we shows how NSA based PRISM works.
What methodology NSA used. What data Types NSA Collects. And How we can bypass NSA
Data breach

Many security breaches we saw in the past few years and how it affect the number of businesses it include large and small businesses. We will study what is breach and how it will effect on our business and what are the main causes of it. Why social media account is harm for us and how the largest organizations got breached and how would we stop to get breach our data. Our main target Is related to business it could be small or large business. We will discuss that how companies got lost their reputation because of data breach and how much companies got loss of money it include the organization that we all are known about it like Facebook.
↓↓↓↓ Read More:
Watch my videos on snack here: --> --> http://sck.io/x-B1f0Iy
@ Kindly Follow my Instagram Page to discuss about your mental health problems-
-----> https://instagram.com/mentality_streak?utm_medium=copy_link
@ Appreciate my work:
-----> behance.net/burhanahmed1
Thank-you !
How Data Loss Prevention End-Point Agents Use HPE IDOL’s Comprehensive Data C...

Transcript of a discussion on how cybersecurity attacks are on the rise but new capabilities are being brought to the edge to provide for better data loss prevention.
Unveiling the Threat: The Impact of Spooling Attacks in Cybersecurity

We and our partners store and/or access information on a device, such as unique IDs in
cookies to process personal data. You may accept or manage your choices by clicking
below, including your right to object where legitimate interest is used, or at any time in the
privacy policy page. These choices will be signaled to our partners and will not affect
browsing data.
More Related Content
Similar to Ghostery Data Privacy Day 2014
Crimes in digital marketing..pptx

This presentation tells about digital marketing meaning and crimes related to it.Any illegal behavior directed by means of electronic operations. that targets the security of computer systems and the data. processed by them is termed cyber crime.
The invention of computer and Information technology related software and equipment has revolutionized the way we do things in many fields.Especially in the science, education, business and commerce it has made far reaching changes.Without using a single sheet of paper, a lot of communications and transactions are done.Automation of businesses, financial institutions and the government records have become widespread.
Many transactions such as sale of goods, transfer of information, transfer of funds and even buying air tickets could be done through the use of computers. The existing laws that governs transactions and information did not address such issues as they were made before the IT era.
The use of internet web 120

A brief definition of how spyware and adware work. A warning to avoid sharing information without realizing the consequences that it may have.
The Ins, Outs, and Nuances of Internet Privacy

Facebook recently came under fire for the discreet international roll-out of its photo facial recognition feature. This feature automatically identifies and suggests tags for individuals appearing in photos posted on Facebook. At first glance, this seemingly innocuous feature appears to quietly augment online social lives. At second glance, the rollout of this feature as a defaulted-to-on setting with no explicit user consent raises many privacy concerns. As a site with extensive power driven by the quantity, quality, and kind of data it collects, Facebook’s decision to step into the world of visual recognition of its users without formal user consent is a big no-no—or is it?
Join us for this month’s eBoost Consulting Brown Bag Lunch Webinar to explore this and other cases that raise internet privacy concerns. Learn the ins, outs, and nuances of internet privacy to determine where to draw the line on data collection and usage.
AI for humans - the future of your digital self

ABSTRACT: In this talk, George will demonstrate the extent and power of personal data collected by technology companies. He will explore the potential of personal data to do both good and bad, the dangers of giving up your "digital DNA", and the value these companies extract from this data.
Data rights are finally legally recognised. With the combination of GDPR & rising awareness of personal data abuse, we might eventually be able to control our data, or at least understand as much about our digital footprint as profit-driven companies do.
AI is only possible because it has data. Imagine your data being used to benefit you, instead of targeting you with gambling adverts. Imagine the potential for next-generation research to understand our society, which can only happen if we break data out from being locked in corporate databases. Data rights are just the start, now we need to use them.
BIO: George Punter holds a first class Masters degree from Imperial College London in Electronics & Information Engineering. He co-founded Ethi (ethi.me), a startup that aims to make controlling your personal data easier, and allow users to use their personal data for their own benefit, or for social good. Ethi is currently partnering with a cyber security firm, TurgenSec, to help create next-generation, user-centred security.
Data Privacy: What you need to know about privacy, from compliance to ethics

Today, balancing business opportunity and customer's data protection has become a difficult challenge. As technology, data sources and targeting abilities grow, so does the crucial need to respect user privacy and ensure a good data protection. But with laws, practices and definitions that are constantly evolving around the world, it can all seem a bit confusing.
Not sure where to start? Wondering how you can better align with privacy law? Then this webinar is for you.
Behavioral tracking : Today's internet trend

Behavioral tracking : how different websites across web follow ur behavior and follow u.
Vishwadeep Presentation On NSA PRISM Spying

In this presentation we shows how NSA based PRISM works.
What methodology NSA used. What data Types NSA Collects. And How we can bypass NSA
Data breach

Many security breaches we saw in the past few years and how it affect the number of businesses it include large and small businesses. We will study what is breach and how it will effect on our business and what are the main causes of it. Why social media account is harm for us and how the largest organizations got breached and how would we stop to get breach our data. Our main target Is related to business it could be small or large business. We will discuss that how companies got lost their reputation because of data breach and how much companies got loss of money it include the organization that we all are known about it like Facebook.
↓↓↓↓ Read More:
Watch my videos on snack here: --> --> http://sck.io/x-B1f0Iy
@ Kindly Follow my Instagram Page to discuss about your mental health problems-
-----> https://instagram.com/mentality_streak?utm_medium=copy_link
@ Appreciate my work:
-----> behance.net/burhanahmed1
Thank-you !
How Data Loss Prevention End-Point Agents Use HPE IDOL’s Comprehensive Data C...

Transcript of a discussion on how cybersecurity attacks are on the rise but new capabilities are being brought to the edge to provide for better data loss prevention.
Unveiling the Threat: The Impact of Spooling Attacks in Cybersecurity

We and our partners store and/or access information on a device, such as unique IDs in
cookies to process personal data. You may accept or manage your choices by clicking
below, including your right to object where legitimate interest is used, or at any time in the
privacy policy page. These choices will be signaled to our partners and will not affect
browsing data.
Similar to Ghostery Data Privacy Day 2014 (20)
Data Privacy: What you need to know about privacy, from compliance to ethics

Data Privacy: What you need to know about privacy, from compliance to ethics
Digital Defense for Activists (and the rest of us)

Digital Defense for Activists (and the rest of us)
How Data Loss Prevention End-Point Agents Use HPE IDOL’s Comprehensive Data C...

How Data Loss Prevention End-Point Agents Use HPE IDOL’s Comprehensive Data C...
Unveiling the Threat: The Impact of Spooling Attacks in Cybersecurity

Unveiling the Threat: The Impact of Spooling Attacks in Cybersecurity
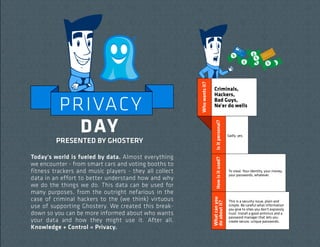
Ghostery Data Privacy Day 2014
- 1. Is it personal? How is it used? Today's world is fueled by data. Almost everything we encounter - from smart cars and voting booths to fitness trackers and music players - they all collect data in an effort to better understand how and why we do the things we do. This data can be used for many purposes, from the outright nefarious in the case of criminal hackers to the (we think) virtuous use of supporting Ghostery. We created this breakdown so you can be more informed about who wants your data and how they might use it. After all, Knowledge + Control = Privacy. Sadly, yes. To steal. Your identity, your money, your passwords, whatever. What can you do about it? PRESENTED BY GHOSTERY Who wants it? PRIVAC Y DA Y Criminals, Hackers, Bad Guys, Ne'er do wells This is a security issue, plain and simple. Be careful what information you give to sites you don't expressly trust. Install a good antivirus and a password manager that lets you create secure, unique passwords.
- 2. Is it personal? To create a profile of what you like (and specifically, what you might want to buy) based on the sites you visit. Write your representatives. Seriously. Technically, this is tough to stop. Governments can employ very deep-dive methods of collection, and compel private companies to cooperate. You can afford some protection by using services like Tor and Ghostery, but even these won't stop information gathered via subpeonas served to ISPs, email services, etc. So seriously, write your government officials and express your displeasure. What can you do about it? To create detailed profiles in order to prevent crimes. How is it used? Who wants it? Is it personal? Maybe. Most of this data doesn't involve your specfic information, but a lot can be inferred from robust profiles. How is it used? 3rd party, datadriven marketers. You bet. What can you do about it? Who wants it? Governments. Notably the US NSA, but it happens all over the world, by just about every government, to one degree or another. Lots of these guys provide opt-outs via AdChoices icons or some other program. You can also limit collection by deleting cookies and browsing in incognito or private mode. But your best bet is to use Ghostery, which can block communication with any companies you don't trust.
- 3. Not really. Usually non-specific location and activity info is as deep as it gets. Is it personal? Nope. We take lots of steps to anonymize what we collect. To create an overview of a site's audience. How is it used? Who wants it? Ghostery, via Ghostrank™ We use Ghostrank to better understand how and where data is collected across the web. We support Ghostery by selling information about that tracking activity to companies to help them better understand themselves and each other. Though this stuff is mostly harmless and can probably help the sites you like get better, if it bugs you, block and/or opt-out. Ghostery helps a lot here. What can you do about it? Is it personal? How is it used? What can you do about it? Who wants it? The sites you visit and the apps you use We won't take any data you don't tell us we can take - so just don't opt-in. (But please opt-in)
