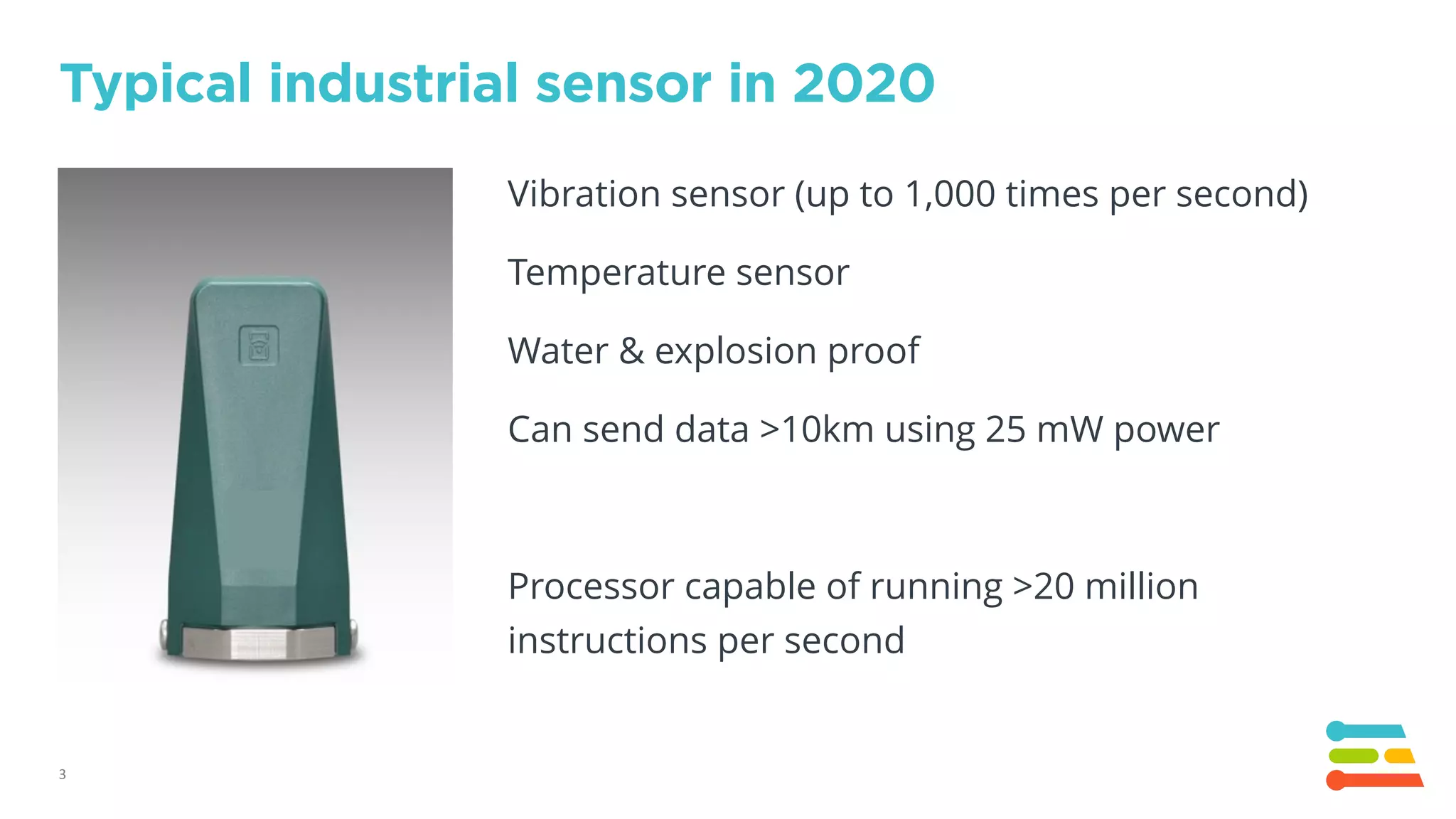
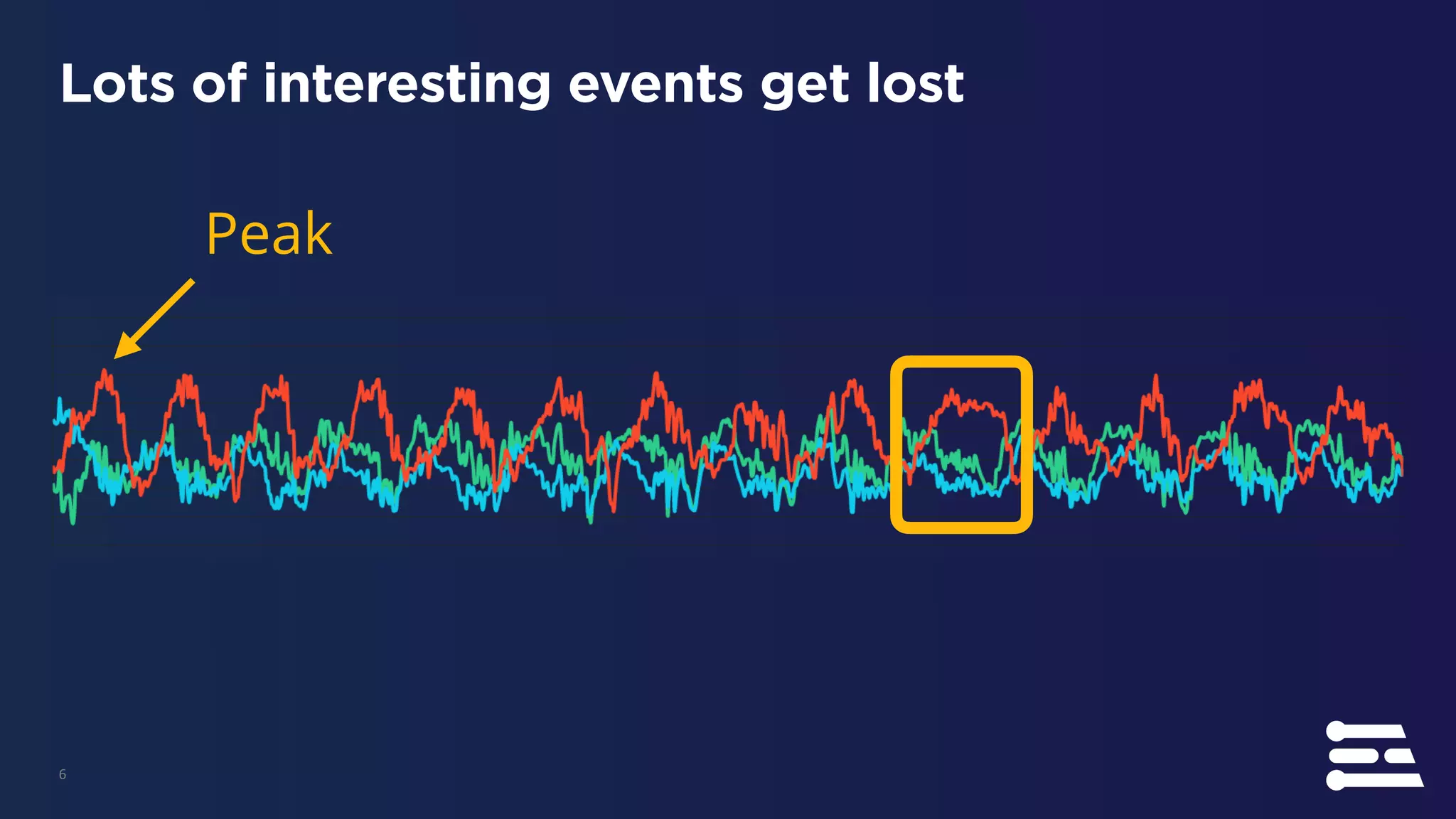
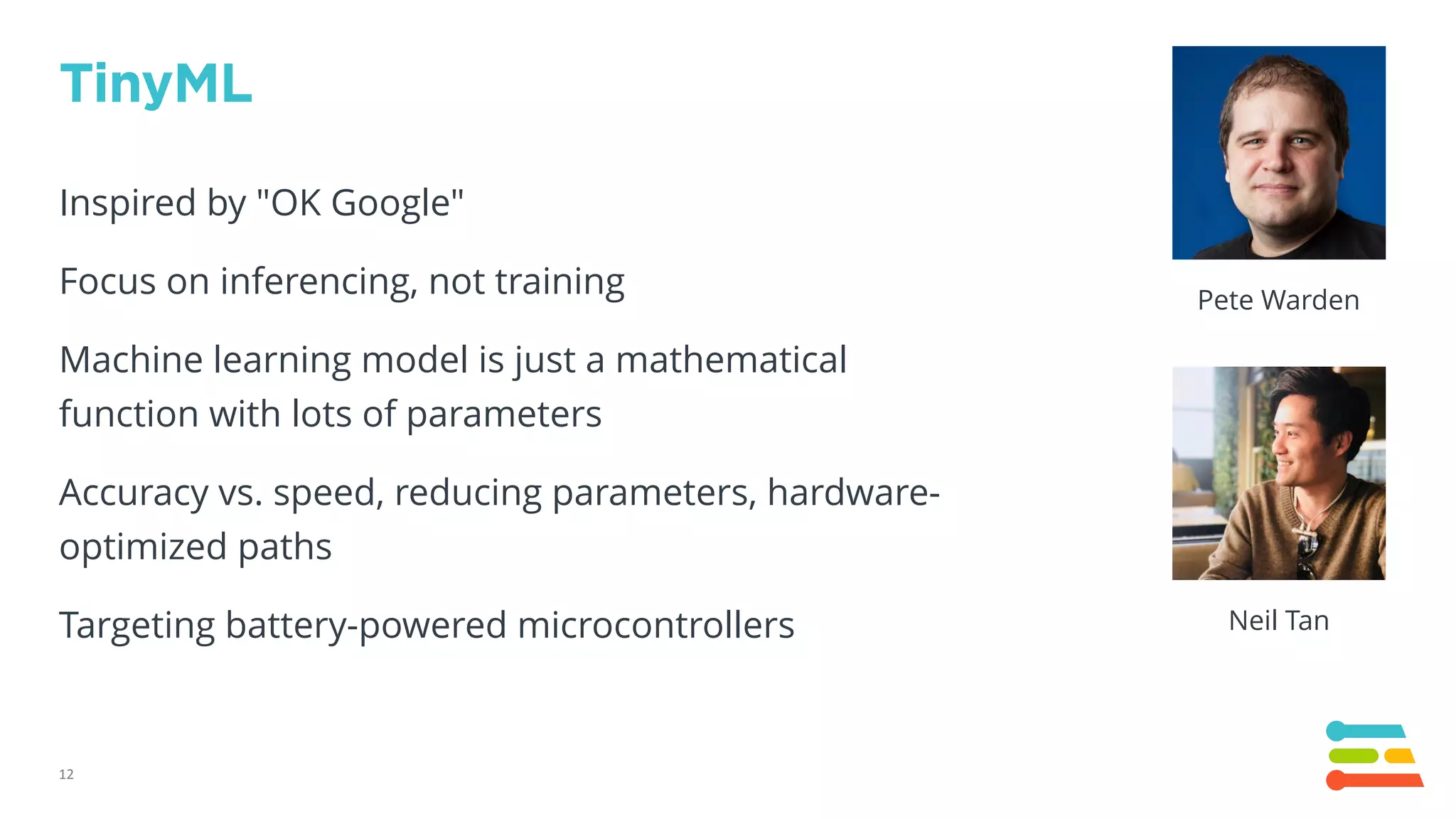
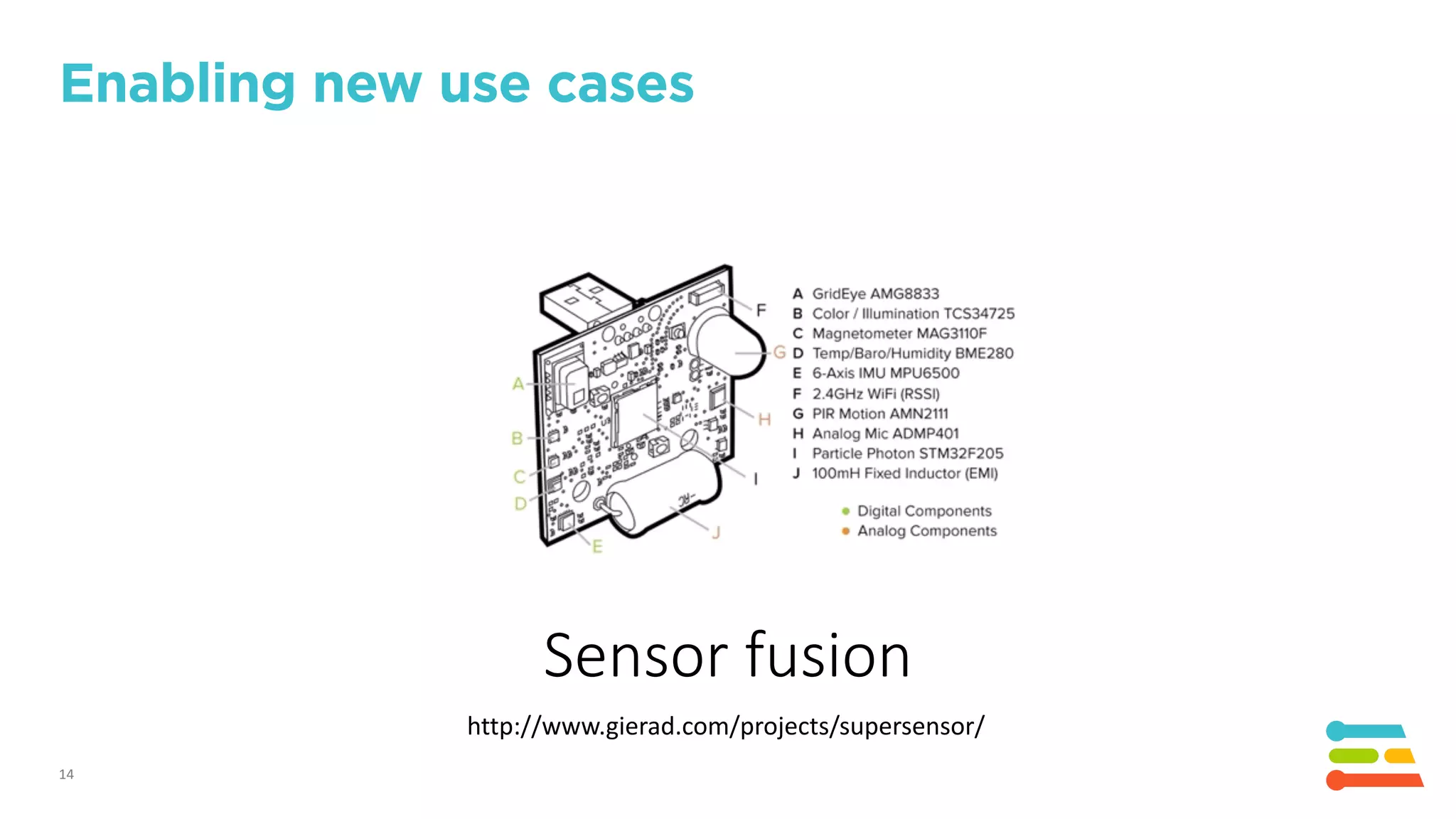
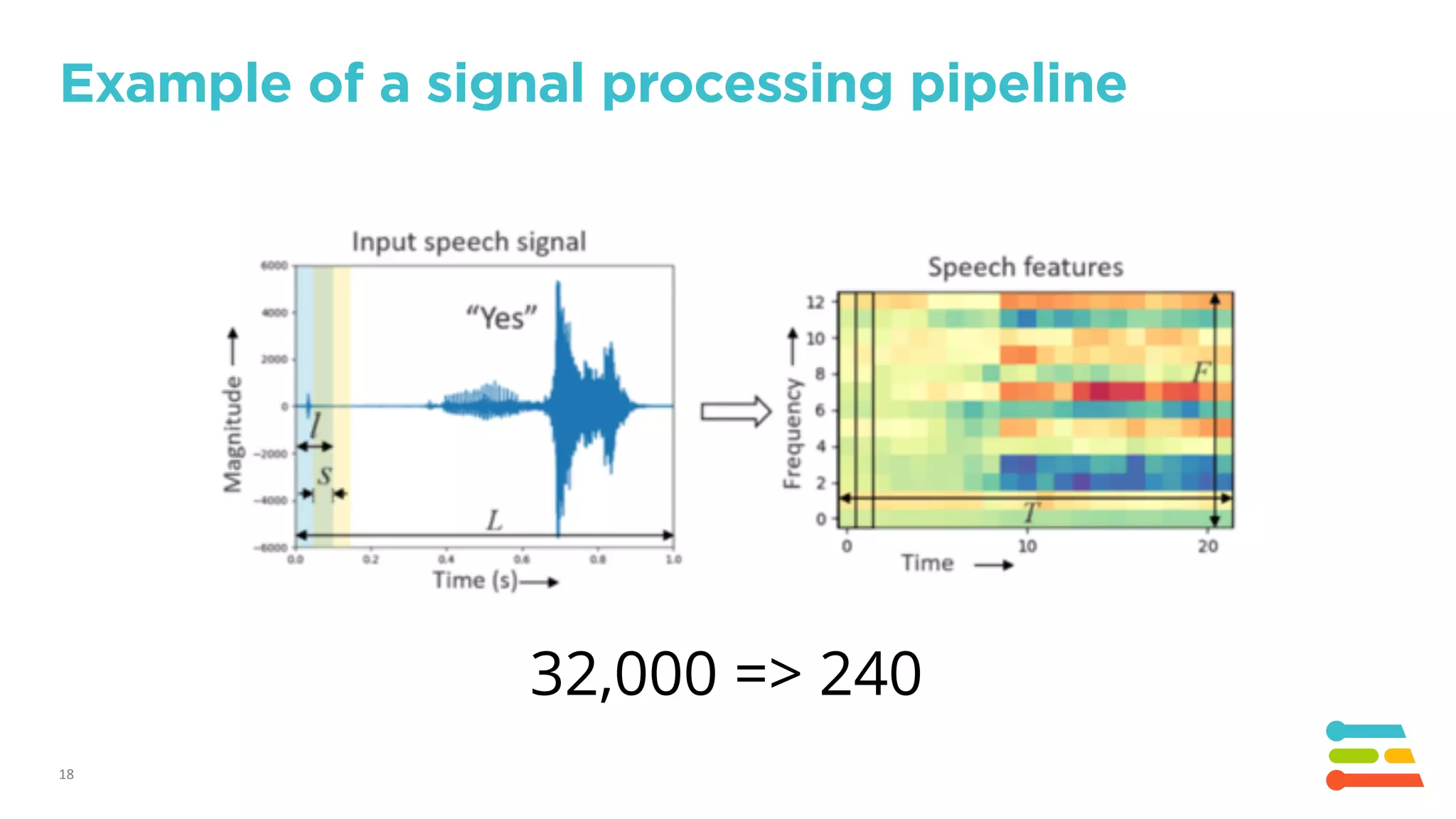
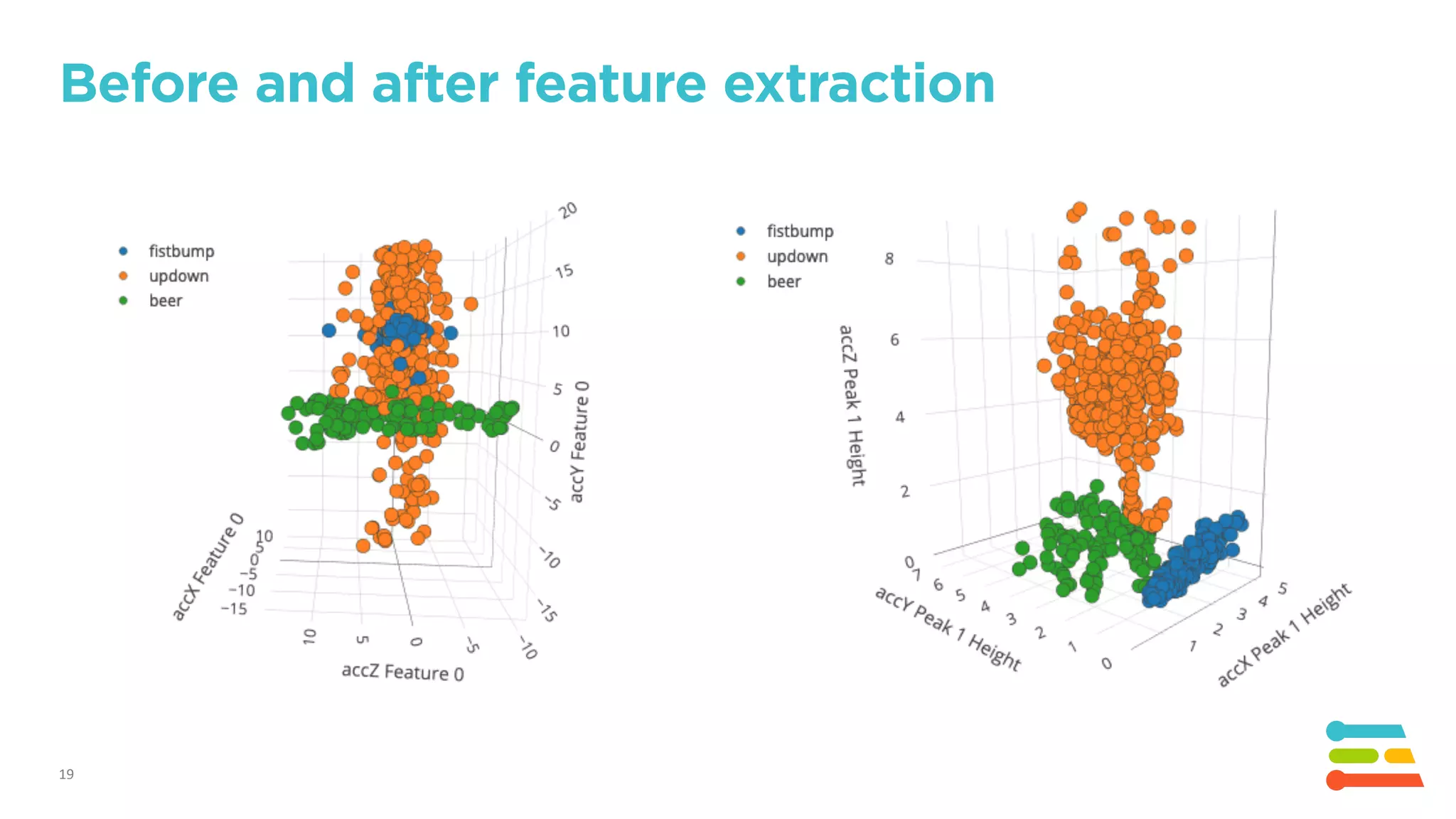
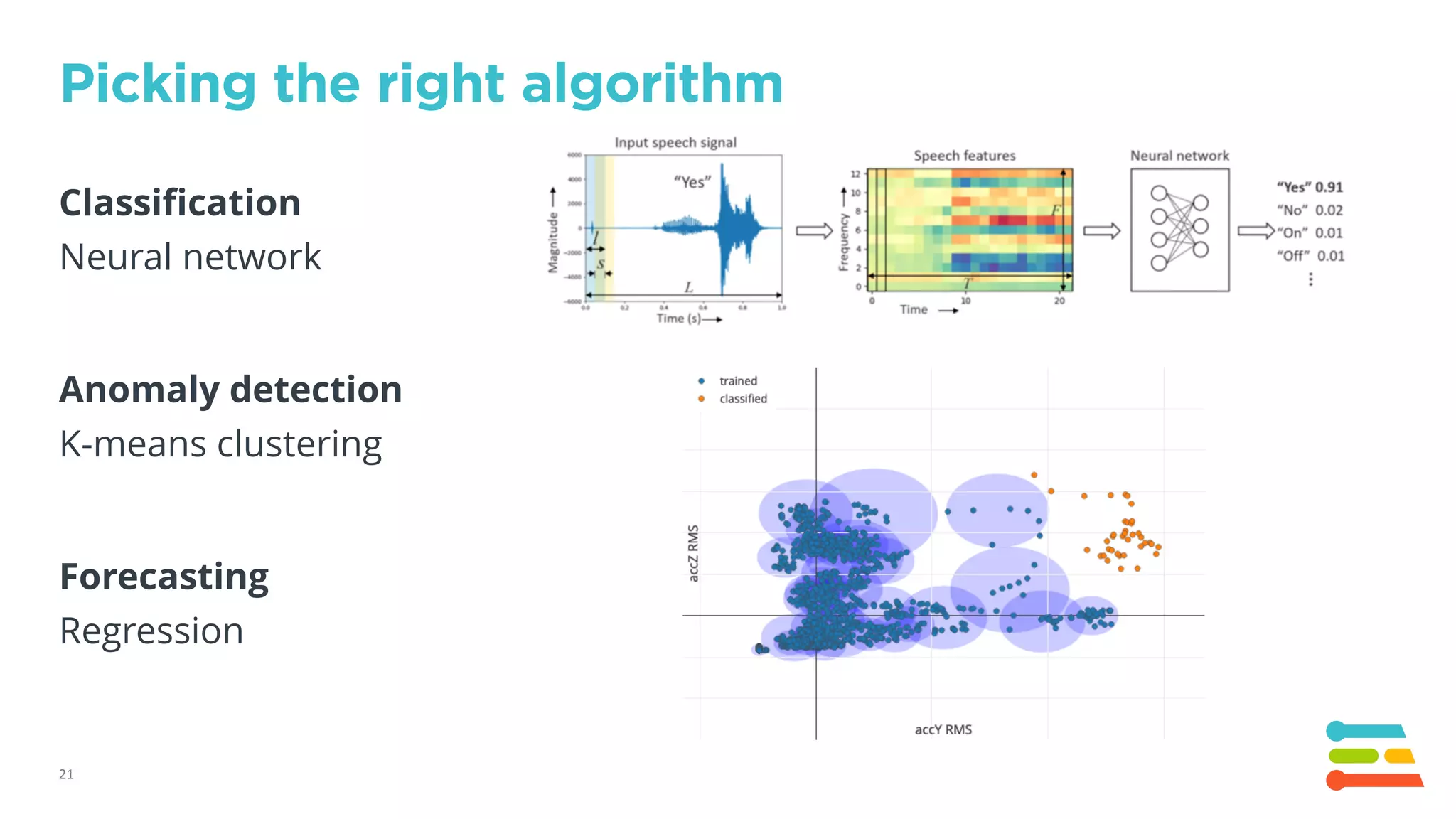
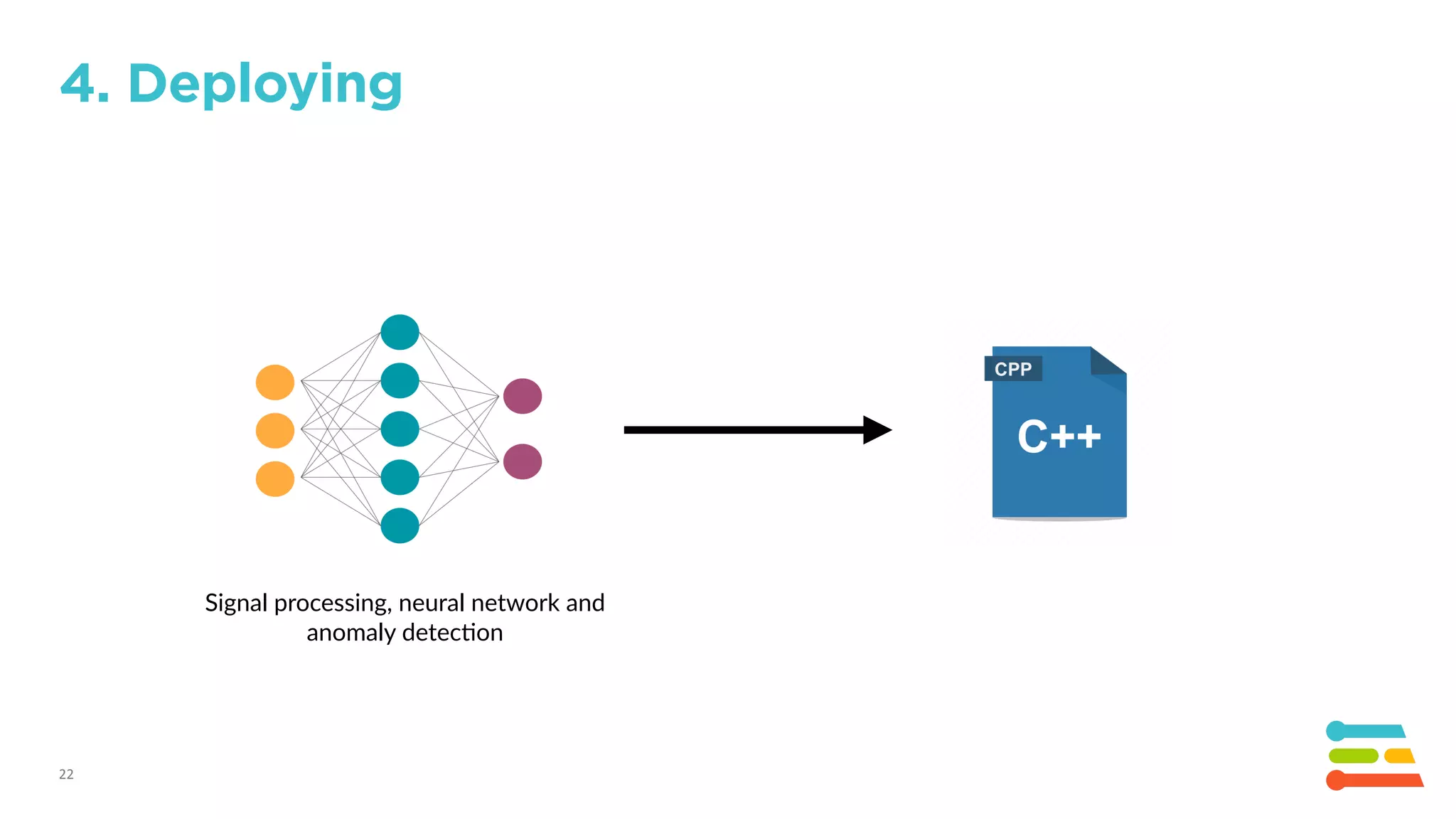
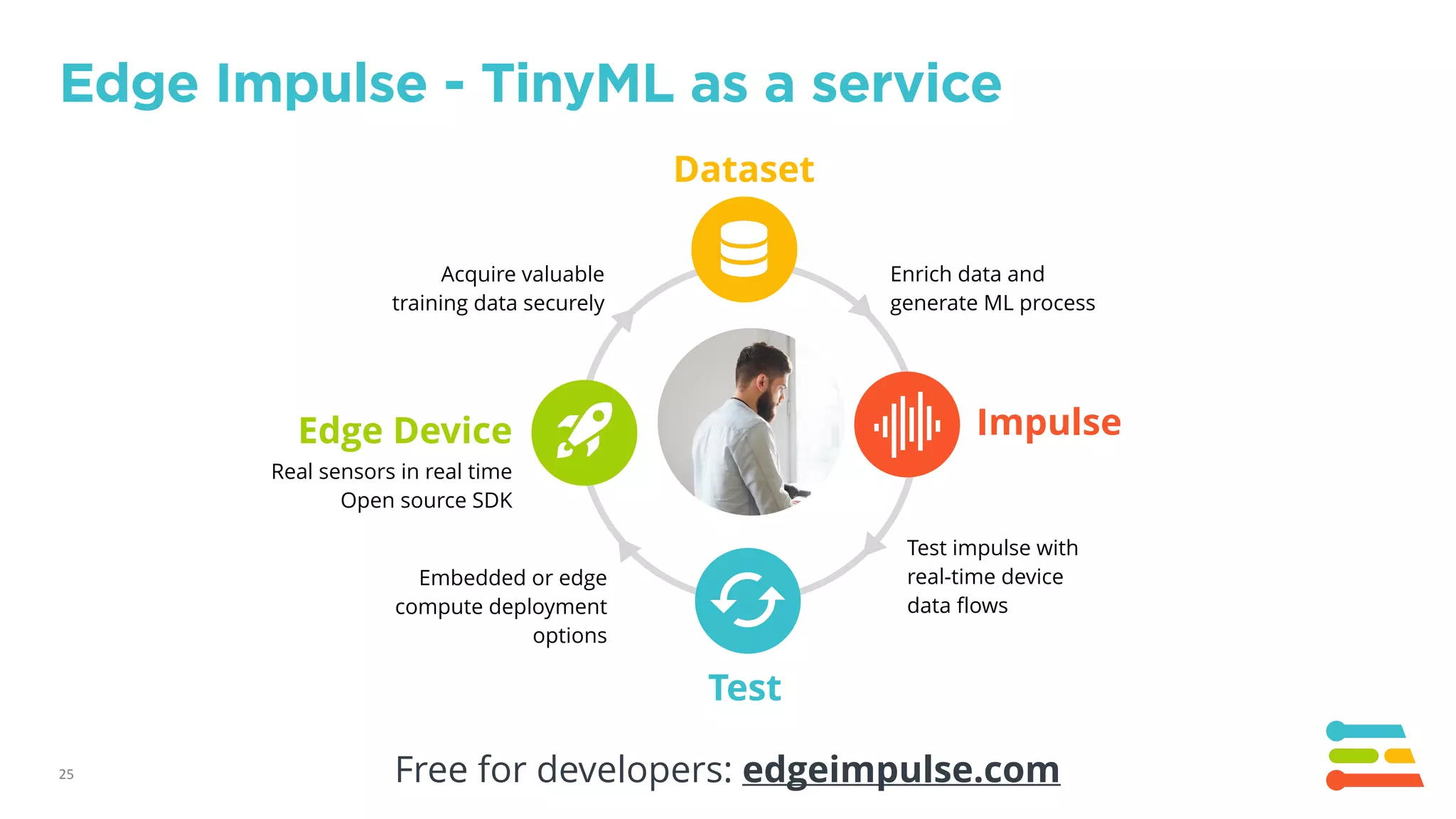
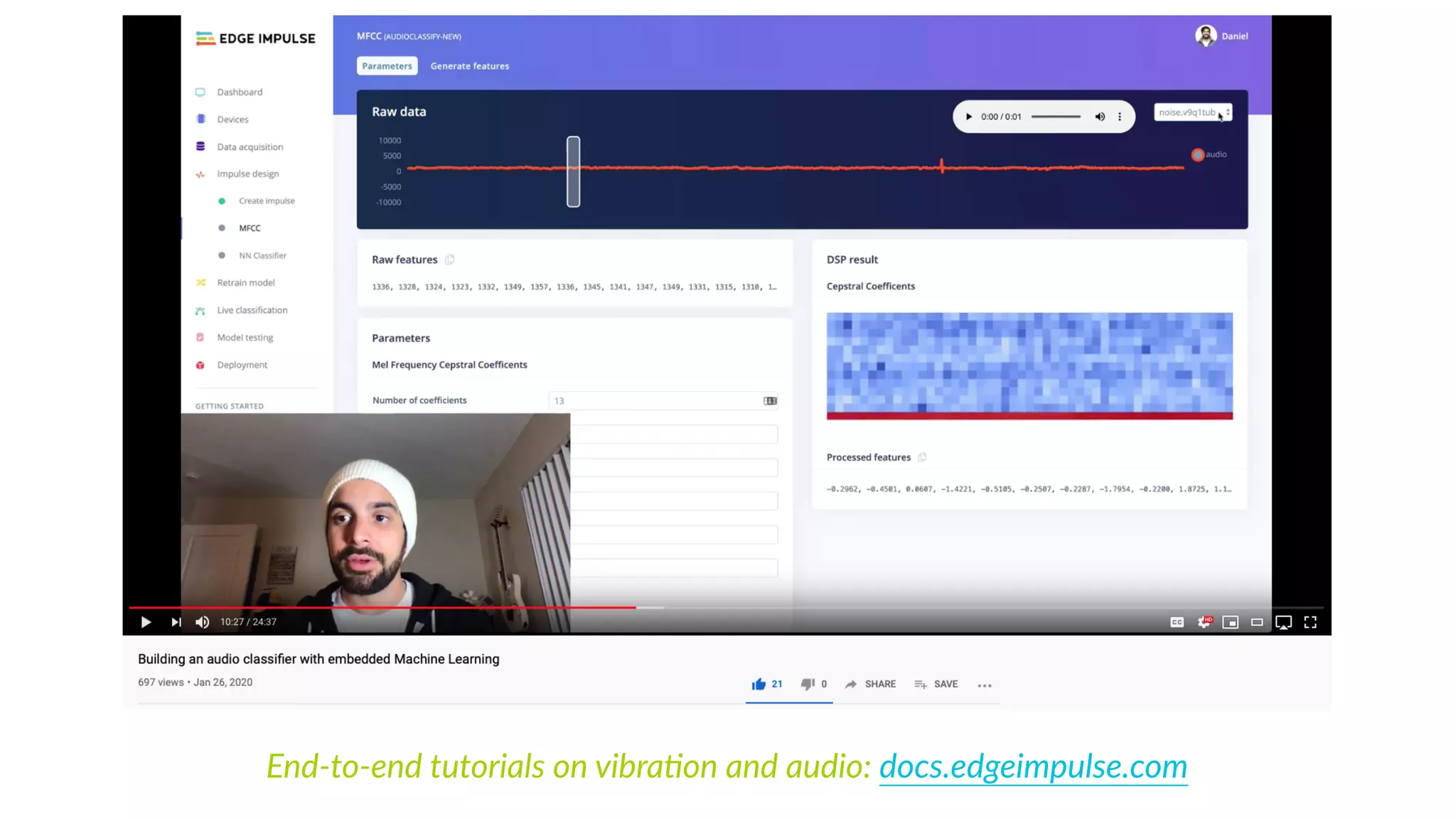
The document discusses the advancements and applications of TinyML in industrial sensors, highlighting the importance of on-device intelligence for processing data efficiently. It emphasizes that much of the sensor data is wasted due to constraints and aims to harness machine learning to identify patterns in complex data. By extracting meaningful features from high-resolution raw data, TinyML enables new use cases such as recognizing sounds and detecting abnormal vibrations.