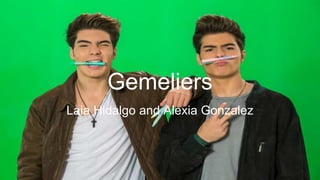
The document provides a history and description of the musical duo Gemeliers. It discusses that Jesus and Daniel Oviedo Morilla have been dedicated to music since age 4. It notes some of their early performances and appearances on television shows in Spain. Their big break came in 2014 on the television show The Voice Kids. The document describes their popular songs and sound as pop and Latino-inspired music. It mentions some of their album releases and awards they have received.