Report
Share
Download to read offline
Recommended
SDPS Cert

The document contains a single name - "EricMaury". In 3 sentences or less, this document is about an individual named Eric Maury. The short document focuses on identifying the person named but provides no other context or information about Eric Maury.
Information security trends and steps for (OSAC) Middle East divsion 

Cyber trends in 2021 and what you can do: Presented for the State Department's Diplomatic Security Service - Overseas Security Advisory Council (OSAC)
Tsc2021 cyber-issues

This document provides guidance on cybersecurity best practices for organizations. It notes that no network is completely secure and individuals often enable hacking through mistakes. It recommends establishing an incident response plan, purchasing cyber insurance, developing security policies and procedures, considering outsourcing security monitoring, regularly backing up data in multiple secure locations, and using a password manager. The document also warns against common pitfalls like not sustaining long-term security resources and provides links to additional cybersecurity resources.
IT Staff NDA Template Employee Confidentiality Agreement

This is a sample IT Staff NDA or "Employee Confidentiality Agreement" It has more power to educate staff on what they should or should not do with their power & Access.
A guide to Sustainable Cyber Security

The document provides legal disclaimers and information about sustainable cybersecurity practices. It discusses starting cybersecurity at the administration level by making it cultural rather than technical, based on needs rather than vendor features, iterative and continuous. It also discusses establishing a data protection steering committee and reducing reliance on people by ensuring responsibilities are understood and policies and processes are documented. The document provides recommendations on cybersecurity frameworks, controls, and best practices.
Cy safe 2.0_workbook

This document provides guidelines for implementing IT security controls based on the SANS Critical Controls, ISO, and NIST frameworks. It defines 35 key control areas and lists expected controls and examples of roles and responsibilities (RACI matrix) for each. The purpose is to help organizations assess, understand, and prioritize basic IT security needs, then establish controls and accountabilities. It also provides templates for documenting controls, future plans, and evidence of compliance.
Privacies are Coming

How do we separate hype from useful information in Cyber Security? As Congress is debating a National privacy law, and several states have privacy and breach reporting laws, how will that impact our workload? Privacy starts with good cyber-hygiene. We will look at how we can leverage the focus on Privacy to address standards for:
Firewall and network Configs,
Cloud security
Protocols and ports that need attention
Authentication best practices
Server and network rights
Password rules
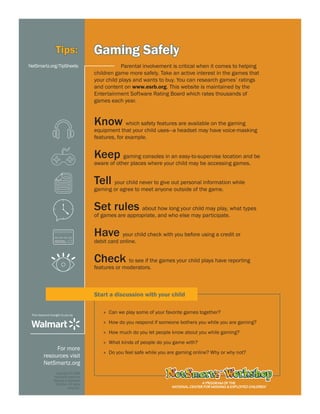
Parenting and the media challenge

What does the current research say about the positive and negative influence of emerging technologies on our ministries, our families, and ourselves? It's imperative we comprehend how media impacts our mental and spiritual health. Technology is changing our lives, how we relate to and understand each other.
Recommended
SDPS Cert

The document contains a single name - "EricMaury". In 3 sentences or less, this document is about an individual named Eric Maury. The short document focuses on identifying the person named but provides no other context or information about Eric Maury.
Information security trends and steps for (OSAC) Middle East divsion 

Cyber trends in 2021 and what you can do: Presented for the State Department's Diplomatic Security Service - Overseas Security Advisory Council (OSAC)
Tsc2021 cyber-issues

This document provides guidance on cybersecurity best practices for organizations. It notes that no network is completely secure and individuals often enable hacking through mistakes. It recommends establishing an incident response plan, purchasing cyber insurance, developing security policies and procedures, considering outsourcing security monitoring, regularly backing up data in multiple secure locations, and using a password manager. The document also warns against common pitfalls like not sustaining long-term security resources and provides links to additional cybersecurity resources.
IT Staff NDA Template Employee Confidentiality Agreement

This is a sample IT Staff NDA or "Employee Confidentiality Agreement" It has more power to educate staff on what they should or should not do with their power & Access.
A guide to Sustainable Cyber Security

The document provides legal disclaimers and information about sustainable cybersecurity practices. It discusses starting cybersecurity at the administration level by making it cultural rather than technical, based on needs rather than vendor features, iterative and continuous. It also discusses establishing a data protection steering committee and reducing reliance on people by ensuring responsibilities are understood and policies and processes are documented. The document provides recommendations on cybersecurity frameworks, controls, and best practices.
Cy safe 2.0_workbook

This document provides guidelines for implementing IT security controls based on the SANS Critical Controls, ISO, and NIST frameworks. It defines 35 key control areas and lists expected controls and examples of roles and responsibilities (RACI matrix) for each. The purpose is to help organizations assess, understand, and prioritize basic IT security needs, then establish controls and accountabilities. It also provides templates for documenting controls, future plans, and evidence of compliance.
Privacies are Coming

How do we separate hype from useful information in Cyber Security? As Congress is debating a National privacy law, and several states have privacy and breach reporting laws, how will that impact our workload? Privacy starts with good cyber-hygiene. We will look at how we can leverage the focus on Privacy to address standards for:
Firewall and network Configs,
Cloud security
Protocols and ports that need attention
Authentication best practices
Server and network rights
Password rules
Parenting and the media challenge

What does the current research say about the positive and negative influence of emerging technologies on our ministries, our families, and ourselves? It's imperative we comprehend how media impacts our mental and spiritual health. Technology is changing our lives, how we relate to and understand each other.
How to use technology in ministry & parenting

Engaging with technology beyond the level of experience. We need to understand how technology is changing us so we can ensure we are modeling wise habits. There are some good ways we can use technology to understand and shape its use. Suggestions will be given for what we can start doing today that will make positive impacts on our lives and ministries.
Privacies are coming

How do we separate hype from useful information in Cyber Security? As Congress is debating a National privacy law, and several states have their own privacy and breach reporting laws including Georgia, how will that impact our workload? Privacy starts with good cyber-hygiene. We will look at how we can leverage the focus on Privacy to address standards for:
Firewall and network setups
Cloud security
Protocols and ports that need attention
Authentication best practices
Server and network rights
Password rules
Idwg bimonthly security exchange cyber only section

Had a great time sharing with OSAC today on Cyber Security trends, We went over some practical steps organizations, and their staff can take to secure their information and privacy better.
Data Detox Kit Optimized 

The document discusses the benefits of meditation for reducing stress and anxiety. Regular meditation practice can help calm the mind and body by lowering heart rate and blood pressure. Studies have shown that meditating for just 10-20 minutes per day can have significant positive impacts on both mental and physical health over time.
GDPR Benefits and a Technical Overview

This document provides an overview of the General Data Protection Regulation (GDPR) and outlines steps for compliance. It begins with a disclaimer about the information provided. It then lists resources for learning more about the GDPR and its 99 articles and 173 recitals. The rest of the document outlines key aspects of GDPR compliance, including identifying high and critical risk data, privacy notices, individual rights and redress, lawful and fair processing, privacy by design, data security, and data transfers.
Compter Forensics Intro for Students 

Computer forensics is the process of applying scientific and analytical techniques to digital systems and file structures to determine potential legal evidence. It involves preserving the computer as a crime scene by powering off and copying the memory and system. Various types of forensic requests include intrusion analysis, damage assessment, suspect examination, and log file analysis to search for evidence such as image files, apps, and deleted or hidden files. The computer forensics process involves preparation, protection and preservation of evidence, imaging systems, examination of operating systems, applications, log files, and file systems, and thorough documentation.
Risk Management Approach to Cyber Security 

The document discusses implementing a risk management approach to cyber security. It emphasizes that security can no longer be outsourced and instead the security team should help others become more self-sufficient. It then discusses various cyber risks like the growing attack surface and risks to health care as a target. Finally, it discusses strategies to implement an enterprise risk management approach like determining how information flows and conducting risk analysis interviews.
Why security is the kidney not the tail of the dog v3

Security is sometimes thought of being the tail that wags the Dog. A better analogy is that Cyber Security should be the Kidneys of the organization taking out the waste while allowing the useful information to pass.
FBI & Secret Service- Business Email Compromise Workshop

This document provides information on various open source and low-cost security tools and solutions, including test email servers, phishing training modules, phishing frameworks, password checking tools, email alerts, network mapping tools, and more. It also lists free business intelligence software, and resources on avoiding business email compromise scams.
FBI & Secret Service- Business Email Compromise Workshop

Compiled some Open source and other tools that I that I have used for BEC/EAC protection, security, & training. I had a great time sitting on the panel with other members.
Harbin clinic iot-mobile-no-vid

The document provides tips for securing your digital footprint and privacy online. It discusses securing social media accounts, using strong and unique passwords, deleting personal information from search engines, enabling two-factor authentication, using secure browsers and VPNs, being wary of sharing personal information publicly, and understanding the risks of a large digital shadow and footprint online. It also covers tips for securing mobile devices, IoT devices, and protecting privacy when traveling across borders.
Securely Erase your Device

This document provides instructions for securely erasing personal information from various devices before donating or replacing them. It outlines steps to back up data, sign out of accounts, encrypt devices where possible, and perform factory resets. For Android and iOS devices, it recommends backing up data, signing out of accounts, encrypting the device, and performing a factory reset. For computers, it suggests backing up data, using encryption and secure erasing software like CCleaner to overwrite free space before performing a factory reset. Drilling holes in hard drives is presented as the most secure but less usable method for computers.
Border crossing mobile social media life-saving security tips

This practical talk focused on steps one can take which could save them or someone else while traveling internationally or even around town. The focus was on the information that is “leaked” by mobile devices and social media, along with some of the most-overlooked steps that could lower risk.
Social & mobile security

This document discusses social and mobile security issues. It covers topics like the psychological impact of social media, internet addiction among college students, privacy concerns with sharing information and photos online, and tips for safe social media and mobile device use. Specific recommendations include educating yourself and loved ones on online risks, setting guidelines for internet and phone use, installing parental control software, using strong passwords, and being aware of location data and metadata attached to photos.
Social mobile safety

This document provides a summary of research on the psychological and physical impacts of media and technology use among students. It finds that social media can foster shallow relationships and an inflated sense of self. Excessive internet and smartphone use has been linked to increased feelings of anxiety, addiction and depression in students. The document also warns that oversharing private details online can have long term consequences and that geotagging photos can reveal more personal information than intended.
Using social media to boost your ministrys online presence 

The document provides tips and best practices for using social media for organizations. It discusses establishing goals and measuring success, types of social media messages to share, optimal posting times and frequencies, using hashtags and photos/videos, promoting events locally, common mistakes to avoid like not engaging audiences or diversifying networks, and tools for automation and management like HootSuite, Google Alerts, and Addictomatic.
Social media How to Step by Step

The document provides instructions for setting up accounts and using popular social media and social media management platforms including Facebook, Pinterest, Google+, Twitter, and Hootsuite. It describes the sign-up processes for each platform and basic functions for posting, sharing content, and analyzing engagement. Hootsuite allows users to connect multiple social accounts to schedule and analyze posts in one place.
Gcc social media presentation

This document provides tips and advice for using social media effectively. It discusses how social media can be used to engage people where they are online and promote conversation. Some key points include using hashtags to promote local events, diversifying your social media networks beyond just one platform, using photos and videos to engage audiences, and taking advantage of automation tools and teams to manage social media presence. Mistakes to avoid include not engaging audiences, relying on just one network, failing to use visual content, and not promoting your social media channels or taking a hands-off approach.
Social networking tips_parents_wmart_es

Este documento proporciona una guía para padres sobre cómo proteger a sus hijos en sitios de redes sociales. Explica que los sitios de redes sociales son lugares donde los jóvenes socializan con amigos pero también pueden publicar contenido inapropiado o conocer gente peligrosa. Recomienda que los padres participen regularmente revisando el perfil de sus hijos, la configuración de privacidad y los amigos para asegurarse de que todo sea apropiado. También ofrece consejos sobre cómo los hijos pueden usar positivamente las redes social
Smartphone safety

This document provides parents with information about potential risks and safety tips for children using smartphones. The risks discussed include cyberbullying, revealing a child's location through geolocation and photos, exposure to inappropriate content, sexting, and viruses/malware. The document recommends that parents establish clear guidelines, set up password protection, update the operating system, approve apps before downloading, and understand location services settings to help children use smartphones safely.
More Related Content
More from Ernest Staats
How to use technology in ministry & parenting

Engaging with technology beyond the level of experience. We need to understand how technology is changing us so we can ensure we are modeling wise habits. There are some good ways we can use technology to understand and shape its use. Suggestions will be given for what we can start doing today that will make positive impacts on our lives and ministries.
Privacies are coming

How do we separate hype from useful information in Cyber Security? As Congress is debating a National privacy law, and several states have their own privacy and breach reporting laws including Georgia, how will that impact our workload? Privacy starts with good cyber-hygiene. We will look at how we can leverage the focus on Privacy to address standards for:
Firewall and network setups
Cloud security
Protocols and ports that need attention
Authentication best practices
Server and network rights
Password rules
Idwg bimonthly security exchange cyber only section

Had a great time sharing with OSAC today on Cyber Security trends, We went over some practical steps organizations, and their staff can take to secure their information and privacy better.
Data Detox Kit Optimized 

The document discusses the benefits of meditation for reducing stress and anxiety. Regular meditation practice can help calm the mind and body by lowering heart rate and blood pressure. Studies have shown that meditating for just 10-20 minutes per day can have significant positive impacts on both mental and physical health over time.
GDPR Benefits and a Technical Overview

This document provides an overview of the General Data Protection Regulation (GDPR) and outlines steps for compliance. It begins with a disclaimer about the information provided. It then lists resources for learning more about the GDPR and its 99 articles and 173 recitals. The rest of the document outlines key aspects of GDPR compliance, including identifying high and critical risk data, privacy notices, individual rights and redress, lawful and fair processing, privacy by design, data security, and data transfers.
Compter Forensics Intro for Students 

Computer forensics is the process of applying scientific and analytical techniques to digital systems and file structures to determine potential legal evidence. It involves preserving the computer as a crime scene by powering off and copying the memory and system. Various types of forensic requests include intrusion analysis, damage assessment, suspect examination, and log file analysis to search for evidence such as image files, apps, and deleted or hidden files. The computer forensics process involves preparation, protection and preservation of evidence, imaging systems, examination of operating systems, applications, log files, and file systems, and thorough documentation.
Risk Management Approach to Cyber Security 

The document discusses implementing a risk management approach to cyber security. It emphasizes that security can no longer be outsourced and instead the security team should help others become more self-sufficient. It then discusses various cyber risks like the growing attack surface and risks to health care as a target. Finally, it discusses strategies to implement an enterprise risk management approach like determining how information flows and conducting risk analysis interviews.
Why security is the kidney not the tail of the dog v3

Security is sometimes thought of being the tail that wags the Dog. A better analogy is that Cyber Security should be the Kidneys of the organization taking out the waste while allowing the useful information to pass.
FBI & Secret Service- Business Email Compromise Workshop

This document provides information on various open source and low-cost security tools and solutions, including test email servers, phishing training modules, phishing frameworks, password checking tools, email alerts, network mapping tools, and more. It also lists free business intelligence software, and resources on avoiding business email compromise scams.
FBI & Secret Service- Business Email Compromise Workshop

Compiled some Open source and other tools that I that I have used for BEC/EAC protection, security, & training. I had a great time sitting on the panel with other members.
Harbin clinic iot-mobile-no-vid

The document provides tips for securing your digital footprint and privacy online. It discusses securing social media accounts, using strong and unique passwords, deleting personal information from search engines, enabling two-factor authentication, using secure browsers and VPNs, being wary of sharing personal information publicly, and understanding the risks of a large digital shadow and footprint online. It also covers tips for securing mobile devices, IoT devices, and protecting privacy when traveling across borders.
Securely Erase your Device

This document provides instructions for securely erasing personal information from various devices before donating or replacing them. It outlines steps to back up data, sign out of accounts, encrypt devices where possible, and perform factory resets. For Android and iOS devices, it recommends backing up data, signing out of accounts, encrypting the device, and performing a factory reset. For computers, it suggests backing up data, using encryption and secure erasing software like CCleaner to overwrite free space before performing a factory reset. Drilling holes in hard drives is presented as the most secure but less usable method for computers.
Border crossing mobile social media life-saving security tips

This practical talk focused on steps one can take which could save them or someone else while traveling internationally or even around town. The focus was on the information that is “leaked” by mobile devices and social media, along with some of the most-overlooked steps that could lower risk.
Social & mobile security

This document discusses social and mobile security issues. It covers topics like the psychological impact of social media, internet addiction among college students, privacy concerns with sharing information and photos online, and tips for safe social media and mobile device use. Specific recommendations include educating yourself and loved ones on online risks, setting guidelines for internet and phone use, installing parental control software, using strong passwords, and being aware of location data and metadata attached to photos.
Social mobile safety

This document provides a summary of research on the psychological and physical impacts of media and technology use among students. It finds that social media can foster shallow relationships and an inflated sense of self. Excessive internet and smartphone use has been linked to increased feelings of anxiety, addiction and depression in students. The document also warns that oversharing private details online can have long term consequences and that geotagging photos can reveal more personal information than intended.
Using social media to boost your ministrys online presence 

The document provides tips and best practices for using social media for organizations. It discusses establishing goals and measuring success, types of social media messages to share, optimal posting times and frequencies, using hashtags and photos/videos, promoting events locally, common mistakes to avoid like not engaging audiences or diversifying networks, and tools for automation and management like HootSuite, Google Alerts, and Addictomatic.
Social media How to Step by Step

The document provides instructions for setting up accounts and using popular social media and social media management platforms including Facebook, Pinterest, Google+, Twitter, and Hootsuite. It describes the sign-up processes for each platform and basic functions for posting, sharing content, and analyzing engagement. Hootsuite allows users to connect multiple social accounts to schedule and analyze posts in one place.
Gcc social media presentation

This document provides tips and advice for using social media effectively. It discusses how social media can be used to engage people where they are online and promote conversation. Some key points include using hashtags to promote local events, diversifying your social media networks beyond just one platform, using photos and videos to engage audiences, and taking advantage of automation tools and teams to manage social media presence. Mistakes to avoid include not engaging audiences, relying on just one network, failing to use visual content, and not promoting your social media channels or taking a hands-off approach.
Social networking tips_parents_wmart_es

Este documento proporciona una guía para padres sobre cómo proteger a sus hijos en sitios de redes sociales. Explica que los sitios de redes sociales son lugares donde los jóvenes socializan con amigos pero también pueden publicar contenido inapropiado o conocer gente peligrosa. Recomienda que los padres participen regularmente revisando el perfil de sus hijos, la configuración de privacidad y los amigos para asegurarse de que todo sea apropiado. También ofrece consejos sobre cómo los hijos pueden usar positivamente las redes social
Smartphone safety

This document provides parents with information about potential risks and safety tips for children using smartphones. The risks discussed include cyberbullying, revealing a child's location through geolocation and photos, exposure to inappropriate content, sexting, and viruses/malware. The document recommends that parents establish clear guidelines, set up password protection, update the operating system, approve apps before downloading, and understand location services settings to help children use smartphones safely.
More from Ernest Staats (20)
Idwg bimonthly security exchange cyber only section

Idwg bimonthly security exchange cyber only section
Why security is the kidney not the tail of the dog v3

Why security is the kidney not the tail of the dog v3
FBI & Secret Service- Business Email Compromise Workshop

FBI & Secret Service- Business Email Compromise Workshop
FBI & Secret Service- Business Email Compromise Workshop

FBI & Secret Service- Business Email Compromise Workshop
Border crossing mobile social media life-saving security tips

Border crossing mobile social media life-saving security tips
Using social media to boost your ministrys online presence 

Using social media to boost your ministrys online presence
