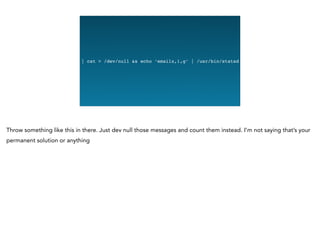
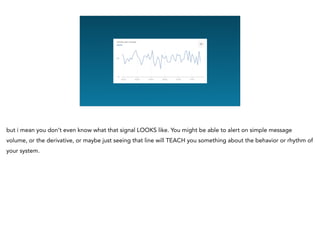
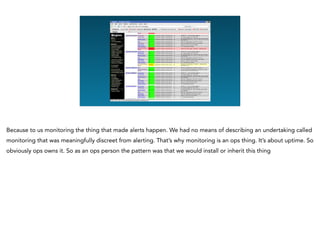
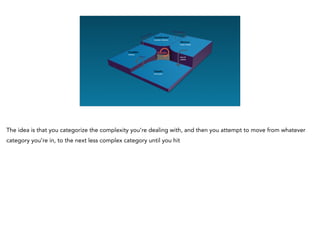
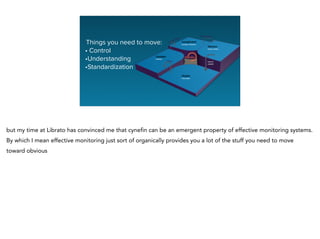
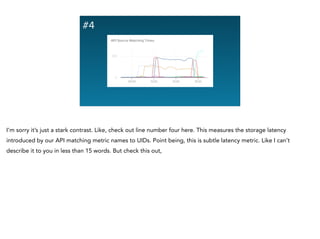
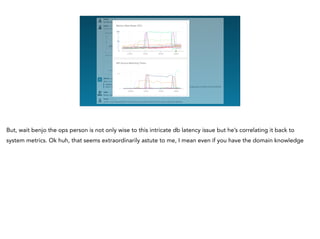
Dave, who recently transitioned back to the ops team at Librato from a developer evangelist role, reflects on his experiences at conferences and the misunderstandings about monitoring and alerting. He emphasizes that monitoring should not just be about alerting but is a shared responsibility among all engineers, aiming for understanding system behavior, rather than becoming isolated in complexity. Through anecdotes, he illustrates how effective monitoring and collaboration can lead to simplification and better communication among teams.