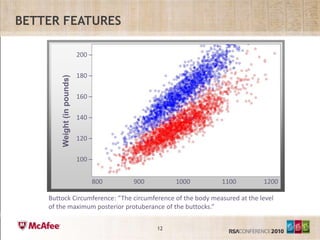
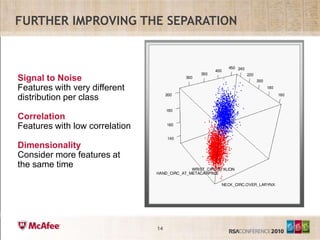
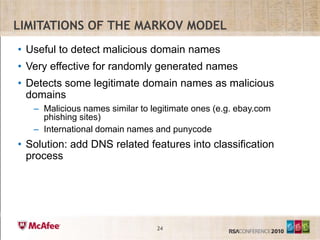
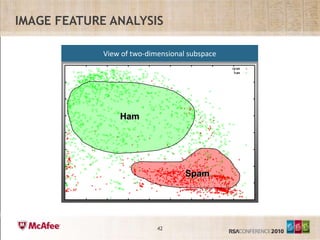
The document discusses using data mining techniques to analyze email data and identify patterns that can help determine characteristics of users like gender. It describes exploring different features of email data like weight, height, and buttock circumference as proxies for actual user data. Dimensionality reduction techniques are used to visualize email data in fewer dimensions to better identify patterns and natural separations between classes of users. The goal is to improve techniques for determining properties of users from sparse, anonymized data.