Fall 2009 closed memo assignment no. 1 lara jade coton misappropriation of likeness - florida statute
•
1 like•691 views
Report
Share
Report
Share
Download to read offline
Recommended
Support Gay Marriage

This is a project related to the book Maus. I had to create a representation on an issue dealing with hate toward a certain group, and what side I took.
Sex, Love, Social Media

Social Media Week London Event 2012
http://socialmediaweek.org/event/?event_id=2318
For full information about the talk including links to stats, livestream/YouTube and Storify - please visit http://trust2point0.posterous.com/love-sex-social-media
Recommended
Support Gay Marriage

This is a project related to the book Maus. I had to create a representation on an issue dealing with hate toward a certain group, and what side I took.
Sex, Love, Social Media

Social Media Week London Event 2012
http://socialmediaweek.org/event/?event_id=2318
For full information about the talk including links to stats, livestream/YouTube and Storify - please visit http://trust2point0.posterous.com/love-sex-social-media
2010-07-28 Can You See Me Now?

Subtitle: "The Growing Problem of Sexting Among School-Age Children." A presentation delivered to the Catawba County School District on July 28, 2010, in Conover, NC.
How i stole someone's identity scientific american

https://www.scientificamerican.com/article/anatomy-of-a-social-hack/
Republicans who don’t protect Trump’s corruption will pay a very steep price

Republicans who don’t protect Trump’s corruption will pay a very steep priceLUMINATIVE MEDIA/PROJECT COUNSEL MEDIA GROUP
The White House is taking yet another big step to declare any and all oversight conducted by the House of Representatives fundamentally illegitimate, placing President Trump above accountability entirely.PIPA and SOPA

PIPA and SOPA are both U.S. Government Law’s for stopping the Online Piracy which
includes, Software, Music, Movies, anything.. The big companies like Google and Mozilla once supported this ACT's.. But now they are standing against them.... They want that this
Bills never get passed...
Getty images extortion letter

Here is a very easy and simple way to understand, ignore and possibly defend yourself via a letter back to Getty Images and a Cease / Desist request. Which can obviously be followed by reporting to FTC commission for them continuing to hound you.
GEORGE ZIMMERMAN & EBOLA CRISIS (When Will These RACIST Attacks STOP)

What is the CONNECTION between George Zimmerman and the EBOLA Outbreak/Crisis in AFRICA? It appears MORE RACIST ATTACKS by the United States of America's DESPOTISM Regime that is CONTROLLED by the JEWS and WHITE SUPREMACIST!
Social Media and Litigation Nov 2011

Continuing Legal Education from LexisNexis on the use of Social Media as an informal discovery tool
Social Media And Litigation Nov 2011

Overview of the impact of social media on litigation, focusing on ethics and informal discovery. November 2011.
Mba Admission Essay Writing Services Onlin

Professional Writing Service
http://HelpWriting.net/Mba-Admission-Essay-Writing-Services-On 👈
This is an essay assignment and will require a series of expository .docx

This is an essay assignment and will require a series of expository responses.
You are permitted to use only your notes from class and your textbook in answering these questions, and you are forbidden from consulting outside sources and reference materials – including the Internet and your classmates.
The first section of the assignment comprises (short) essay questions in the traditional sense; each question will require answers ranging in length, but certainly not to exceed a single typewritten page. Be sure to address the call of the question, and to answer each part of the question(s) asked.
The second section of the exam (the last two questions) is contains narrative fact patterns (law-school style questions), and requires lengthier answers. Read each question carefully and submit your answers in the order in which the questions appear on the examination. As each question progresses, it will implicate multiple areas of tort law (civil -- not criminal) claims arising from the fact pattern. Your job is to identify every possible legal issue and apply the law (spotting each issue, articulating the rule of law by discussing the elements of each claim in the context of burdens of proof, provide thoughtful analysis of the applicable facts to the rule of law, raising any legal defenses that might exist, and suggesting a likely outcome).
Note, this implicates the so-called "IRAC" method that we have discussed several times now -- I(ssue)-R(ule)-A(nalysis)-C(onclusion). For each part of each question, you should note the facts in the question that apply to the legal issue and rule of law implicated, break it down to the elements, apply the relevant facts to the rule of law, and draw a legal conclusion (essentially, who wins and why?). It's not uncommon to have multiple IRAC-style analyses in the same answer where the fact pattern triggers multiple legal questions/issues.
To the extent that a question implicates one of the statutes or cases that we have studied (in class, or from the text) cite the relevant sources and explain how each applies to the facts of the question. (An answer that fails to cite and analyze relevant sources, as well as highlight the elements of any common-law or statutory claim is incomplete and will not receive full credit.) If you believe that additional facts are needed to answer a question fully, note exactly what additional facts/information you need and how they would affect your answer; if you observe that a question is ambiguous, it likely is drafted that way intentionally and you should note the ambiguity and how it affects your answer, addressing multiple possible solutions to the question where appropriate. Good luck!
QUESTION 1
* Identify and explain each of the four primary sources of modern United States law. What role does precedent (and/or stare decisis) play? (Chapters 1,4)
QUESTION 2
* Various agencies have great effects on global business, and operate under the umbrella of the United Nation.
MGMT 597 Education Organization - snaptutorial.com

For more classes visit
www.snaptutorial.com
Contract law may seem simple on its surface. At its base you need an offer plus acceptance supported by consideration. That seems easy enough.
From Boss Partner To Newbie Date 0104YR01 .docx

From: Boss Partner
To: Newbie
Date: 01/04/YR01
Re: Smith v. Johnson
Hi. I hope you’re settled in and that you like the office we've assigned to you.
Listen, about the Johnson case that I wrote you about the other day…
I had a very interesting conversation with a friend of mine who also practices law
here in Fresno. I told her all about the Johnson case and she told me that she heard that
there was a case in the federal district court for the Eastern District of California that had
many similar facts to our case. She tells me she thinks it discussed jurisdiction,
intellectual property issues and defamation which are all seemingly relevant to our case.
Unfortunately, my friend forgot the name of the case although she thinks it was
also about the publication of a website called something-“exposed” and a movie that was
made about some high-profile murders. In any case, I'd love to go search for it but I have
to prepare for my court hearing next Wednesday and I just don't have the time.
Please do me a favor and:
- Find the case that my friend was talking about; and
- Brief it formally in a way that will allow me to refer to it in the most useful
manner.
I know you've been given a copy of “Legal Research, Analysis and Writing” by
Hames and Ekern and I certainly expect that you will refer to their method in most
effectively briefing this case for me.
Thank you very much.
B. Partner
From: Boss Partner
To: Newbie
Date: 01/02/YR01
Re: Welcome!
Dear Newbie:
First, welcome to the firm of Aberdeen, Bernanke and Claustrophobic, situated
here in lovely downtown Fresno, California. I understand that you’re going to spend your
first day filling out forms and getting acclimated and settled in, but when you’re ready to
start working, take a look at the rest of this letter, which will introduce you to our client,
Jane Johnson.
Jane Johnson lives in Portland, Oregon. A few years back, Jane used to sell stuff
on ebay for a living. But she got a bad online reputation because of a few bad reviews
that were posted online about her by her disgruntled customers. After these reviews
steadily decreased her customer base, she was eventually forced to go out of business.
Based on this experience and her bitterness against online websites that are
devoted to allowing consumers who are upset to anonymously and maliciously post
reviews about producers, Jane came up with a new idea for how to make money. She
decided to create a new website that would be the devoted to allowing service providers
and other sellers to complain about customers that they didn't like.
Because Jane knew of a popular website devoted to allowing customers to
complain about service providers called “pissedconsumer.com” she decided to call her
own site “pissedproducer.com.” On April 14, YR-02, Jane registered the domain name
www. pissedproducer.com through godaddy.com. On April 15 .
English Paper Writing - The Writing Center.

Essay Writing Service
http://HelpWriting.net/English-Paper-Writing---The-Writing-Cen 👈
MGMT 597 Great Stories /newtonhelp.com

For more course tutorials visit
www.newtonhelp.com
Contract law may seem simple on its surface. At its base you need an offer plus acceptance supported by
More Related Content
What's hot
2010-07-28 Can You See Me Now?

Subtitle: "The Growing Problem of Sexting Among School-Age Children." A presentation delivered to the Catawba County School District on July 28, 2010, in Conover, NC.
How i stole someone's identity scientific american

https://www.scientificamerican.com/article/anatomy-of-a-social-hack/
Republicans who don’t protect Trump’s corruption will pay a very steep price

Republicans who don’t protect Trump’s corruption will pay a very steep priceLUMINATIVE MEDIA/PROJECT COUNSEL MEDIA GROUP
The White House is taking yet another big step to declare any and all oversight conducted by the House of Representatives fundamentally illegitimate, placing President Trump above accountability entirely.PIPA and SOPA

PIPA and SOPA are both U.S. Government Law’s for stopping the Online Piracy which
includes, Software, Music, Movies, anything.. The big companies like Google and Mozilla once supported this ACT's.. But now they are standing against them.... They want that this
Bills never get passed...
Getty images extortion letter

Here is a very easy and simple way to understand, ignore and possibly defend yourself via a letter back to Getty Images and a Cease / Desist request. Which can obviously be followed by reporting to FTC commission for them continuing to hound you.
GEORGE ZIMMERMAN & EBOLA CRISIS (When Will These RACIST Attacks STOP)

What is the CONNECTION between George Zimmerman and the EBOLA Outbreak/Crisis in AFRICA? It appears MORE RACIST ATTACKS by the United States of America's DESPOTISM Regime that is CONTROLLED by the JEWS and WHITE SUPREMACIST!
What's hot (9)
How i stole someone's identity scientific american

How i stole someone's identity scientific american
Confronting social media at depositions and discovery njaj

Confronting social media at depositions and discovery njaj
Republicans who don’t protect Trump’s corruption will pay a very steep price

Republicans who don’t protect Trump’s corruption will pay a very steep price
GEORGE ZIMMERMAN & EBOLA CRISIS (When Will These RACIST Attacks STOP)

GEORGE ZIMMERMAN & EBOLA CRISIS (When Will These RACIST Attacks STOP)
Similar to Fall 2009 closed memo assignment no. 1 lara jade coton misappropriation of likeness - florida statute
Social Media and Litigation Nov 2011

Continuing Legal Education from LexisNexis on the use of Social Media as an informal discovery tool
Social Media And Litigation Nov 2011

Overview of the impact of social media on litigation, focusing on ethics and informal discovery. November 2011.
Mba Admission Essay Writing Services Onlin

Professional Writing Service
http://HelpWriting.net/Mba-Admission-Essay-Writing-Services-On 👈
This is an essay assignment and will require a series of expository .docx

This is an essay assignment and will require a series of expository responses.
You are permitted to use only your notes from class and your textbook in answering these questions, and you are forbidden from consulting outside sources and reference materials – including the Internet and your classmates.
The first section of the assignment comprises (short) essay questions in the traditional sense; each question will require answers ranging in length, but certainly not to exceed a single typewritten page. Be sure to address the call of the question, and to answer each part of the question(s) asked.
The second section of the exam (the last two questions) is contains narrative fact patterns (law-school style questions), and requires lengthier answers. Read each question carefully and submit your answers in the order in which the questions appear on the examination. As each question progresses, it will implicate multiple areas of tort law (civil -- not criminal) claims arising from the fact pattern. Your job is to identify every possible legal issue and apply the law (spotting each issue, articulating the rule of law by discussing the elements of each claim in the context of burdens of proof, provide thoughtful analysis of the applicable facts to the rule of law, raising any legal defenses that might exist, and suggesting a likely outcome).
Note, this implicates the so-called "IRAC" method that we have discussed several times now -- I(ssue)-R(ule)-A(nalysis)-C(onclusion). For each part of each question, you should note the facts in the question that apply to the legal issue and rule of law implicated, break it down to the elements, apply the relevant facts to the rule of law, and draw a legal conclusion (essentially, who wins and why?). It's not uncommon to have multiple IRAC-style analyses in the same answer where the fact pattern triggers multiple legal questions/issues.
To the extent that a question implicates one of the statutes or cases that we have studied (in class, or from the text) cite the relevant sources and explain how each applies to the facts of the question. (An answer that fails to cite and analyze relevant sources, as well as highlight the elements of any common-law or statutory claim is incomplete and will not receive full credit.) If you believe that additional facts are needed to answer a question fully, note exactly what additional facts/information you need and how they would affect your answer; if you observe that a question is ambiguous, it likely is drafted that way intentionally and you should note the ambiguity and how it affects your answer, addressing multiple possible solutions to the question where appropriate. Good luck!
QUESTION 1
* Identify and explain each of the four primary sources of modern United States law. What role does precedent (and/or stare decisis) play? (Chapters 1,4)
QUESTION 2
* Various agencies have great effects on global business, and operate under the umbrella of the United Nation.
MGMT 597 Education Organization - snaptutorial.com

For more classes visit
www.snaptutorial.com
Contract law may seem simple on its surface. At its base you need an offer plus acceptance supported by consideration. That seems easy enough.
From Boss Partner To Newbie Date 0104YR01 .docx

From: Boss Partner
To: Newbie
Date: 01/04/YR01
Re: Smith v. Johnson
Hi. I hope you’re settled in and that you like the office we've assigned to you.
Listen, about the Johnson case that I wrote you about the other day…
I had a very interesting conversation with a friend of mine who also practices law
here in Fresno. I told her all about the Johnson case and she told me that she heard that
there was a case in the federal district court for the Eastern District of California that had
many similar facts to our case. She tells me she thinks it discussed jurisdiction,
intellectual property issues and defamation which are all seemingly relevant to our case.
Unfortunately, my friend forgot the name of the case although she thinks it was
also about the publication of a website called something-“exposed” and a movie that was
made about some high-profile murders. In any case, I'd love to go search for it but I have
to prepare for my court hearing next Wednesday and I just don't have the time.
Please do me a favor and:
- Find the case that my friend was talking about; and
- Brief it formally in a way that will allow me to refer to it in the most useful
manner.
I know you've been given a copy of “Legal Research, Analysis and Writing” by
Hames and Ekern and I certainly expect that you will refer to their method in most
effectively briefing this case for me.
Thank you very much.
B. Partner
From: Boss Partner
To: Newbie
Date: 01/02/YR01
Re: Welcome!
Dear Newbie:
First, welcome to the firm of Aberdeen, Bernanke and Claustrophobic, situated
here in lovely downtown Fresno, California. I understand that you’re going to spend your
first day filling out forms and getting acclimated and settled in, but when you’re ready to
start working, take a look at the rest of this letter, which will introduce you to our client,
Jane Johnson.
Jane Johnson lives in Portland, Oregon. A few years back, Jane used to sell stuff
on ebay for a living. But she got a bad online reputation because of a few bad reviews
that were posted online about her by her disgruntled customers. After these reviews
steadily decreased her customer base, she was eventually forced to go out of business.
Based on this experience and her bitterness against online websites that are
devoted to allowing consumers who are upset to anonymously and maliciously post
reviews about producers, Jane came up with a new idea for how to make money. She
decided to create a new website that would be the devoted to allowing service providers
and other sellers to complain about customers that they didn't like.
Because Jane knew of a popular website devoted to allowing customers to
complain about service providers called “pissedconsumer.com” she decided to call her
own site “pissedproducer.com.” On April 14, YR-02, Jane registered the domain name
www. pissedproducer.com through godaddy.com. On April 15 .
English Paper Writing - The Writing Center.

Essay Writing Service
http://HelpWriting.net/English-Paper-Writing---The-Writing-Cen 👈
MGMT 597 Great Stories /newtonhelp.com

For more course tutorials visit
www.newtonhelp.com
Contract law may seem simple on its surface. At its base you need an offer plus acceptance supported by
From Boss Partner To Newbie Date 0102YR01 Re.docx

From: Boss Partner
To: Newbie
Date: 01/02/YR01
Re: Welcome!
Dear Newbie:
First, welcome to the firm of Aberdeen, Bernanke and Claustrophobic, situated
here in lovely downtown Fresno, California. I understand that you’re going to spend your
first day filling out forms and getting acclimated and settled in, but when you’re ready to
start working, take a look at the rest of this letter, which will introduce you to our client,
Jane Johnson.
Jane Johnson lives in Portland, Oregon. A few years back, Jane used to sell stuff
on ebay for a living. But she got a bad online reputation because of a few bad reviews
that were posted online about her by her disgruntled customers. After these reviews
steadily decreased her customer base, she was eventually forced to go out of business.
Based on this experience and her bitterness against online websites that are
devoted to allowing consumers who are upset to anonymously and maliciously post
reviews about producers, Jane came up with a new idea for how to make money. She
decided to create a new website that would be the devoted to allowing service providers
and other sellers to complain about customers that they didn't like.
Because Jane knew of a popular website devoted to allowing customers to
complain about service providers called “pissedconsumer.com” she decided to call her
own site “pissedproducer.com.” On April 14, YR-02, Jane registered the domain name
www. pissedproducer.com through godaddy.com. On April 15 she posted her homepage
which contained the following message:
This website is devoted to allowing the producer to fight back. While there are
myriads of websites out there devoted to allowing malicious crybaby consumers
to launch cowardly attacks against hard-working producers behind the safety and
anonymity of their own computers, this website levels the playing field.
Producers are encouraged to post feedback about consumers that other producers
should be wary of. Producers may post stories about deadbeat buyers, customers
who leave unwarranted negative reviews or anything else that other producers
might want to be aware of. Consumers have many outlets to complain about us
hard-working producers and so it's only fair that they be subject to the same kind
of public scrutiny for their wrongful actions.
However, false information of any sort may not be posted on this website.
Moreover, pissedproducer.com does not warrant that any information posted by
any third party on this website is true. The posted content is solely the
responsibility of the party who posted it and in no way will pissedproducer.com
assume any responsibility for any negative review posted by any person on this
site.
This site was an instant hit as, within months, thousands of companies posted
reviews about customers who had failed to pay their bills, made false and malicious
complaints against them and committed other malfeasance.
Similar to Fall 2009 closed memo assignment no. 1 lara jade coton misappropriation of likeness - florida statute (15)
Fall 2010 open memo assignment no doubt v. activision right of publicity cali...

Fall 2010 open memo assignment no doubt v. activision right of publicity cali...
Informal Discovery - Simple Strategies for Cost-Effective Litigation

Informal Discovery - Simple Strategies for Cost-Effective Litigation
This is an essay assignment and will require a series of expository .docx

This is an essay assignment and will require a series of expository .docx
MGMT 597 Education Organization - snaptutorial.com

MGMT 597 Education Organization - snaptutorial.com
More from Lyn Goering
More from Lyn Goering (20)
Spring 2009 appellate brief assignment u.s. v. apollo energies (defendants)

Spring 2009 appellate brief assignment u.s. v. apollo energies (defendants)
Spring 2009 appellate brief assignment u.s. v. apollo energies (prosecution)

Spring 2009 appellate brief assignment u.s. v. apollo energies (prosecution)
Spring 2010 closed memo assignment jellyvision v. aflac lanham act trademar...

Spring 2010 closed memo assignment jellyvision v. aflac lanham act trademar...
Spring 2010 closed memo assignment jellyvision v. aflac complaint pdf

Spring 2010 closed memo assignment jellyvision v. aflac complaint pdf
Spring 2010 closed memo jellyvision v. aflac trademark infringement researc...

Spring 2010 closed memo jellyvision v. aflac trademark infringement researc...
Spring 2010 closed memo assignment jellyvision v. aflac lanham act trademar...

Spring 2010 closed memo assignment jellyvision v. aflac lanham act trademar...
Spring 2007 appellate brief assignment u.s. v. belfast (prosecution)

Spring 2007 appellate brief assignment u.s. v. belfast (prosecution)
Spring 2007 appellate brief assignment u.s. v. belfast (public defender's off...

Spring 2007 appellate brief assignment u.s. v. belfast (public defender's off...
Spring 2010 closed memo jellyvision v. aflac trademark infringement researc...

Spring 2010 closed memo jellyvision v. aflac trademark infringement researc...
Spring 2010 closed memo assignment jellyvision v. aflac complaint pdf

Spring 2010 closed memo assignment jellyvision v. aflac complaint pdf
Spring 2010 closed memo assignment jellyvision v. aflac lanham act trademar...

Spring 2010 closed memo assignment jellyvision v. aflac lanham act trademar...
Spring 2007 appellate brief assignment u.s. v. belfast (public defender's off...

Spring 2007 appellate brief assignment u.s. v. belfast (public defender's off...
Spring 2007 appellate brief assignment u.s. v. belfast (prosecutor)

Spring 2007 appellate brief assignment u.s. v. belfast (prosecutor)
Spring 2007 appellate brief assignment u.s. v. belfast (prosecution)

Spring 2007 appellate brief assignment u.s. v. belfast (prosecution)
Spring 2006 appellate brief assignment west v. mercy hospital (defendant)

Spring 2006 appellate brief assignment west v. mercy hospital (defendant)
Spring 2006 appellate brief assignment west v. mercy hospital (plaintiff)

Spring 2006 appellate brief assignment west v. mercy hospital (plaintiff)
Spring 2006 appellate brief assignment west v. mercy hospital - timeline of...

Spring 2006 appellate brief assignment west v. mercy hospital - timeline of...
Spring 2006 appellate brief assignment west v. mercy hospital - appendix

Spring 2006 appellate brief assignment west v. mercy hospital - appendix
Fall 2006 closed memo assignment workers' comp. horseplay rule a z doc

Fall 2006 closed memo assignment workers' comp. horseplay rule a z doc
Fall 2011 closed memo no. 2 assignment cooper v. stockett appropriation of ...

Fall 2011 closed memo no. 2 assignment cooper v. stockett appropriation of ...
Recently uploaded
Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf

91mobiles recently conducted a Smart TV Buyer Insights Survey in which we asked over 3,000 respondents about the TV they own, aspects they look at on a new TV, and their TV buying preferences.
SAP Sapphire 2024 - ASUG301 building better apps with SAP Fiori.pdf

Building better applications for business users with SAP Fiori.
• What is SAP Fiori and why it matters to you
• How a better user experience drives measurable business benefits
• How to get started with SAP Fiori today
• How SAP Fiori elements accelerates application development
• How SAP Build Code includes SAP Fiori tools and other generative artificial intelligence capabilities
• How SAP Fiori paves the way for using AI in SAP apps
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

Effective Application Security in Software Delivery lifecycle using Deployment Firewall and DBOM
The modern software delivery process (or the CI/CD process) includes many tools, distributed teams, open-source code, and cloud platforms. Constant focus on speed to release software to market, along with the traditional slow and manual security checks has caused gaps in continuous security as an important piece in the software supply chain. Today organizations feel more susceptible to external and internal cyber threats due to the vast attack surface in their applications supply chain and the lack of end-to-end governance and risk management.
The software team must secure its software delivery process to avoid vulnerability and security breaches. This needs to be achieved with existing tool chains and without extensive rework of the delivery processes. This talk will present strategies and techniques for providing visibility into the true risk of the existing vulnerabilities, preventing the introduction of security issues in the software, resolving vulnerabilities in production environments quickly, and capturing the deployment bill of materials (DBOM).
Speakers:
Bob Boule
Robert Boule is a technology enthusiast with PASSION for technology and making things work along with a knack for helping others understand how things work. He comes with around 20 years of solution engineering experience in application security, software continuous delivery, and SaaS platforms. He is known for his dynamic presentations in CI/CD and application security integrated in software delivery lifecycle.
Gopinath Rebala
Gopinath Rebala is the CTO of OpsMx, where he has overall responsibility for the machine learning and data processing architectures for Secure Software Delivery. Gopi also has a strong connection with our customers, leading design and architecture for strategic implementations. Gopi is a frequent speaker and well-known leader in continuous delivery and integrating security into software delivery.
Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...

💥 Speed, accuracy, and scaling – discover the superpowers of GenAI in action with UiPath Document Understanding and Communications Mining™:
See how to accelerate model training and optimize model performance with active learning
Learn about the latest enhancements to out-of-the-box document processing – with little to no training required
Get an exclusive demo of the new family of UiPath LLMs – GenAI models specialized for processing different types of documents and messages
This is a hands-on session specifically designed for automation developers and AI enthusiasts seeking to enhance their knowledge in leveraging the latest intelligent document processing capabilities offered by UiPath.
Speakers:
👨🏫 Andras Palfi, Senior Product Manager, UiPath
👩🏫 Lenka Dulovicova, Product Program Manager, UiPath
Key Trends Shaping the Future of Infrastructure.pdf

Keynote at DIGIT West Expo, Glasgow on 29 May 2024.
Cheryl Hung, ochery.com
Sr Director, Infrastructure Ecosystem, Arm.
The key trends across hardware, cloud and open-source; exploring how these areas are likely to mature and develop over the short and long-term, and then considering how organisations can position themselves to adapt and thrive.
Quantum Computing: Current Landscape and the Future Role of APIs

The current state of quantum computing and the role of APIs to take it mainstream.
A tale of scale & speed: How the US Navy is enabling software delivery from l...

Rapid and secure feature delivery is a goal across every application team and every branch of the DoD. The Navy’s DevSecOps platform, Party Barge, has achieved:
- Reduction in onboarding time from 5 weeks to 1 day
- Improved developer experience and productivity through actionable findings and reduction of false positives
- Maintenance of superior security standards and inherent policy enforcement with Authorization to Operate (ATO)
Development teams can ship efficiently and ensure applications are cyber ready for Navy Authorizing Officials (AOs). In this webinar, Sigma Defense and Anchore will give attendees a look behind the scenes and demo secure pipeline automation and security artifacts that speed up application ATO and time to production.
We will cover:
- How to remove silos in DevSecOps
- How to build efficient development pipeline roles and component templates
- How to deliver security artifacts that matter for ATO’s (SBOMs, vulnerability reports, and policy evidence)
- How to streamline operations with automated policy checks on container images
UiPath Test Automation using UiPath Test Suite series, part 4

Welcome to UiPath Test Automation using UiPath Test Suite series part 4. In this session, we will cover Test Manager overview along with SAP heatmap.
The UiPath Test Manager overview with SAP heatmap webinar offers a concise yet comprehensive exploration of the role of a Test Manager within SAP environments, coupled with the utilization of heatmaps for effective testing strategies.
Participants will gain insights into the responsibilities, challenges, and best practices associated with test management in SAP projects. Additionally, the webinar delves into the significance of heatmaps as a visual aid for identifying testing priorities, areas of risk, and resource allocation within SAP landscapes. Through this session, attendees can expect to enhance their understanding of test management principles while learning practical approaches to optimize testing processes in SAP environments using heatmap visualization techniques
What will you get from this session?
1. Insights into SAP testing best practices
2. Heatmap utilization for testing
3. Optimization of testing processes
4. Demo
Topics covered:
Execution from the test manager
Orchestrator execution result
Defect reporting
SAP heatmap example with demo
Speaker:
Deepak Rai, Automation Practice Lead, Boundaryless Group and UiPath MVP
UiPath Test Automation using UiPath Test Suite series, part 3

Welcome to UiPath Test Automation using UiPath Test Suite series part 3. In this session, we will cover desktop automation along with UI automation.
Topics covered:
UI automation Introduction,
UI automation Sample
Desktop automation flow
Pradeep Chinnala, Senior Consultant Automation Developer @WonderBotz and UiPath MVP
Deepak Rai, Automation Practice Lead, Boundaryless Group and UiPath MVP
Securing your Kubernetes cluster_ a step-by-step guide to success !

Today, after several years of existence, an extremely active community and an ultra-dynamic ecosystem, Kubernetes has established itself as the de facto standard in container orchestration. Thanks to a wide range of managed services, it has never been so easy to set up a ready-to-use Kubernetes cluster.
However, this ease of use means that the subject of security in Kubernetes is often left for later, or even neglected. This exposes companies to significant risks.
In this talk, I'll show you step-by-step how to secure your Kubernetes cluster for greater peace of mind and reliability.
Transcript: Selling digital books in 2024: Insights from industry leaders - T...

The publishing industry has been selling digital audiobooks and ebooks for over a decade and has found its groove. What’s changed? What has stayed the same? Where do we go from here? Join a group of leading sales peers from across the industry for a conversation about the lessons learned since the popularization of digital books, best practices, digital book supply chain management, and more.
Link to video recording: https://bnctechforum.ca/sessions/selling-digital-books-in-2024-insights-from-industry-leaders/
Presented by BookNet Canada on May 28, 2024, with support from the Department of Canadian Heritage.
Generative AI Deep Dive: Advancing from Proof of Concept to Production

Join Maher Hanafi, VP of Engineering at Betterworks, in this new session where he'll share a practical framework to transform Gen AI prototypes into impactful products! He'll delve into the complexities of data collection and management, model selection and optimization, and ensuring security, scalability, and responsible use.
Accelerate your Kubernetes clusters with Varnish Caching

A presentation about the usage and availability of Varnish on Kubernetes. This talk explores the capabilities of Varnish caching and shows how to use the Varnish Helm chart to deploy it to Kubernetes.
This presentation was delivered at K8SUG Singapore. See https://feryn.eu/presentations/accelerate-your-kubernetes-clusters-with-varnish-caching-k8sug-singapore-28-2024 for more details.
Bits & Pixels using AI for Good.........

A whirlwind tour of tech & AI for socio-environmental impact.
How world-class product teams are winning in the AI era by CEO and Founder, P...

How world-class product teams are winning in the AI era by CEO and Founder, Product School
Recently uploaded (20)
Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf

Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf
Monitoring Java Application Security with JDK Tools and JFR Events

Monitoring Java Application Security with JDK Tools and JFR Events
SAP Sapphire 2024 - ASUG301 building better apps with SAP Fiori.pdf

SAP Sapphire 2024 - ASUG301 building better apps with SAP Fiori.pdf
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...
Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...

Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...
Key Trends Shaping the Future of Infrastructure.pdf

Key Trends Shaping the Future of Infrastructure.pdf
Quantum Computing: Current Landscape and the Future Role of APIs

Quantum Computing: Current Landscape and the Future Role of APIs
Free Complete Python - A step towards Data Science

Free Complete Python - A step towards Data Science
A tale of scale & speed: How the US Navy is enabling software delivery from l...

A tale of scale & speed: How the US Navy is enabling software delivery from l...
UiPath Test Automation using UiPath Test Suite series, part 4

UiPath Test Automation using UiPath Test Suite series, part 4
UiPath Test Automation using UiPath Test Suite series, part 3

UiPath Test Automation using UiPath Test Suite series, part 3
Securing your Kubernetes cluster_ a step-by-step guide to success !

Securing your Kubernetes cluster_ a step-by-step guide to success !
Transcript: Selling digital books in 2024: Insights from industry leaders - T...

Transcript: Selling digital books in 2024: Insights from industry leaders - T...
Generative AI Deep Dive: Advancing from Proof of Concept to Production

Generative AI Deep Dive: Advancing from Proof of Concept to Production
Accelerate your Kubernetes clusters with Varnish Caching

Accelerate your Kubernetes clusters with Varnish Caching
FIDO Alliance Osaka Seminar: FIDO Security Aspects.pdf

FIDO Alliance Osaka Seminar: FIDO Security Aspects.pdf
How world-class product teams are winning in the AI era by CEO and Founder, P...

How world-class product teams are winning in the AI era by CEO and Founder, P...
Fall 2009 closed memo assignment no. 1 lara jade coton misappropriation of likeness - florida statute
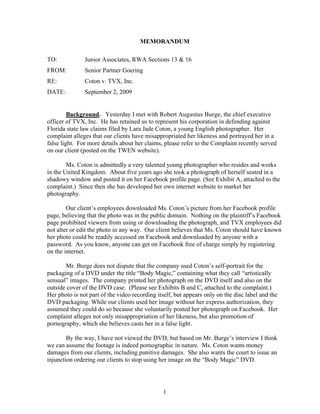
- 1. MEMORANDUM TO: Junior Associates, RWA Sections 13 & 16 FROM: Senior Partner Goering RE: Coton v. TVX, Inc. DATE: September 2, 2009 Background. Yesterday I met with Robert Augustus Burge, the chief executive officer of TVX, Inc. He has retained us to represent his corporation in defending against Florida state law claims filed by Lara Jade Coton, a young English photographer. Her complaint alleges that our clients have misappropriated her likeness and portrayed her in a false light. For more details about her claims, please refer to the Complaint recently served on our client (posted on the TWEN website). Ms. Coton is admittedly a very talented young photographer who resides and works in the United Kingdom. About five years ago she took a photograph of herself seated in a shadowy window and posted it on her Facebook profile page. (See Exhibit A, attached to the complaint.) Since then she has developed her own internet website to market her photography. Our client’s employees downloaded Ms. Coton’s picture from her Facebook profile page, believing that the photo was in the public domain. Nothing on the plaintiff’s Facebook page prohibited viewers from using or downloading the photograph, and TVX employees did not alter or edit the photo in any way. Our client believes that Ms. Coton should have known her photo could be readily accessed on Facebook and downloaded by anyone with a password. As you know, anyone can get on Facebook free of charge simply by registering on the internet. Mr. Burge does not dispute that the company used Coton’s self-portrait for the packaging of a DVD under the title “Body Magic,” containing what they call “artistically sensual” images. The company printed her photograph on the DVD itself and also on the outside cover of the DVD case. (Please see Exhibits B and C, attached to the complaint.) Her photo is not part of the video recording itself, but appears only on the disc label and the DVD packaging. While our clients used her image without her express authorization, they assumed they could do so because she voluntarily posted her photograph on Facebook. Her complaint alleges not only misappropriation of her likeness, but also promotion of pornography, which she believes casts her in a false light. By the way, I have not viewed the DVD, but based on Mr. Burge’s interview I think we can assume the footage is indeed pornographic in nature. Ms. Coton wants money damages from our clients, including punitive damages. She also wants the court to issue an injunction ordering our clients to stop using her image on the “Body Magic” DVD. 1
- 2. Assignment. With your help, we need to immediately assess the likelihood that the plaintiff will prevail in federal district court on either of her claims. If she is likely to win, we may want to consider settlement negotiations to avoid undue litigation expense for our client. At this point, you may assume that the essential facts alleged in her complaint are not in dispute. You may also assume that the federal district court in Florida has proper diversity jurisdiction as well as personal jurisdiction over our client, which markets the DVD nationwide. Depending upon the outcome of your research, we anticipate arguing that the plaintiff cannot prevail because she waived any right to privacy she may have had in the photo. After all, she voluntarily posted her image on Facebook without setting any privacy constraints, so any viewer could download the photo. We also plan to dispute her claim that our client’s use of her photograph depicts her in a false light. Neither the photograph in question nor any other image of her is displayed on the video contents of the DVD itself – only on the label and the packaging. Research Materials. The relevant Florida statute and several cases that appear to be on point are cited below. Copies of these legal authorities are posted on the TWEN page. Please limit your research to these materials. Do not look up any other legal authority or background information, except you may consult a law dictionary to ensure you understand any unfamiliar terms. While not necessary, you may consult the websites identified in the complaint to learn more background information on the plaintiff and her website photography business. However, if you run into any discrepancies, you must assume that the facts are as stated in the complaint and in this memo. You may not look up any other legal authorities, either in print or online, and you may not investigate any other facts regarding the plaintiff or her claims. (1) Alameida v. Amazon.com, Inc., 456 F.3d 1516 (11th Cir. 2006). (2) Cason v. Baskin, 20 So. 2d 243 (Fla. 1945). (3) Cummings v. Sony Music, 2003 WL 2271189 (S.D.N.Y. Sept. 30, 2003). (4) Gill v. Hearst Publg. Co., 253 P.2d 441 (Cal. 1953). (5) Kunz v. Allen, 172 P. 532 (Kan. 1918). (6) Lane v. MRA Holdings, LLC, 242 F. Supp. 2d 1205 (M.D. Fla. 2002). (7) Tyne v. Time Warner Ent. Co., LP, 901 So. 2d 802 (Fla. 2005). (8) Valentine v. CBS, Inc., 698 F.3d 430 (11th Cir. 1983). (9) Fla. Stat. § 540.08 (2008). 2
- 3. Memo Instructions. After carefully reviewing the attached legal authorities, please write the Discussion section of an office memo addressing the appropriate issue or issues of law. Please double-space your memo using 12-point Times New Roman font, and please use at least one-inch margins on all four sides of the page. Include page numbers at the bottom center of each page (except the first), and be sure to include your name and your RWA section number (13 or 16) in your heading. In preparing your office memo, you are expected and required to cite cases and statutes consistent with the ALWD citation manual. You are also expected to demonstrate your understanding of when you should cite legal authority to support a statement in your memo. Finally, you must include accurate pinpoint citations to legal authority to support your analysis. Your completed memo should not exceed five (5) double-spaced pages. I will not read past the fifth page. Your final memo is due in hardcopy on or before Wednesday, September 30, at 5:00 p.m. Please turn in your hardcopy to my mailbox in the copy room on the Fifth Floor, and then upload an identical electronic version to the TWEN Assignment Drop Box. Consultation. You may discuss the research materials and your legal analysis with other students in RWA Sections 13 and 16 who are working on the same memo assignment. However, you may not discuss the assignment or any of the research materials with anyone else, including other law students, other professors, lawyers, parents, siblings, roommates, or significant others. Furthermore, you may not show your written work to anyone, including your classmates. Writing, revising, editing, and proofreading of your memo must be done by you and you alone. Any departure from these requirements, however minor in nature, will be considered a violation of the Honor Code and will be treated accordingly. The only exception is that you may show your written work to me, subject to the 48-hour rule discussed in the syllabus. Honor Code. Before you begin, I expect you to carefully review the Honor Code, available at http://www.law.ualr.edu/academics/pdfs/honorcode.pdf. In particular, read Section III defining infractions of the Code. If at any time you have any questions about what is considered permissible conduct, please contact me immediately by telephone, in person, or by email. It is always better to check in advance to avoid any appearance of impropriety. If anyone asks you for assistance—or offers you assistance—that would violate these restrictions, please contact me immediately. 3