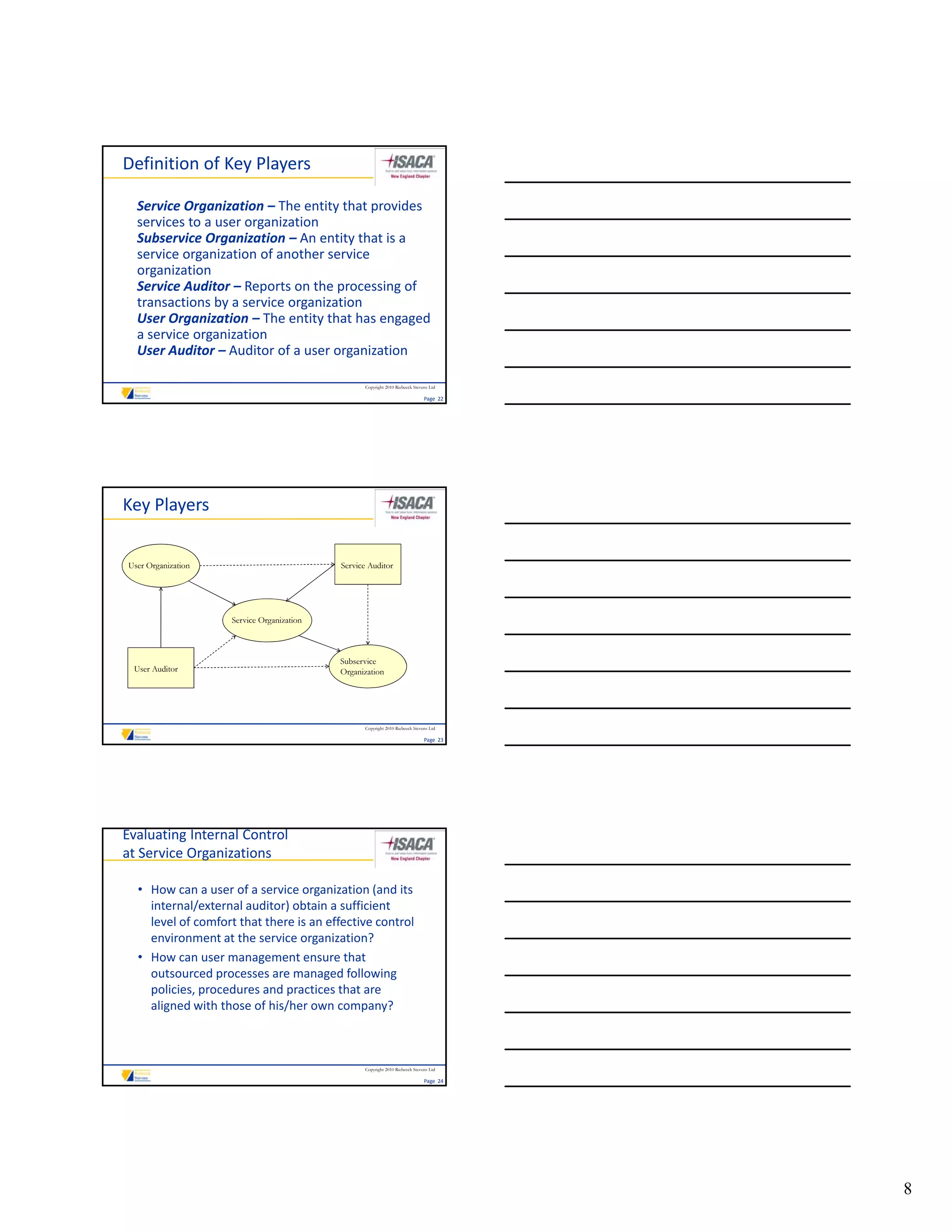
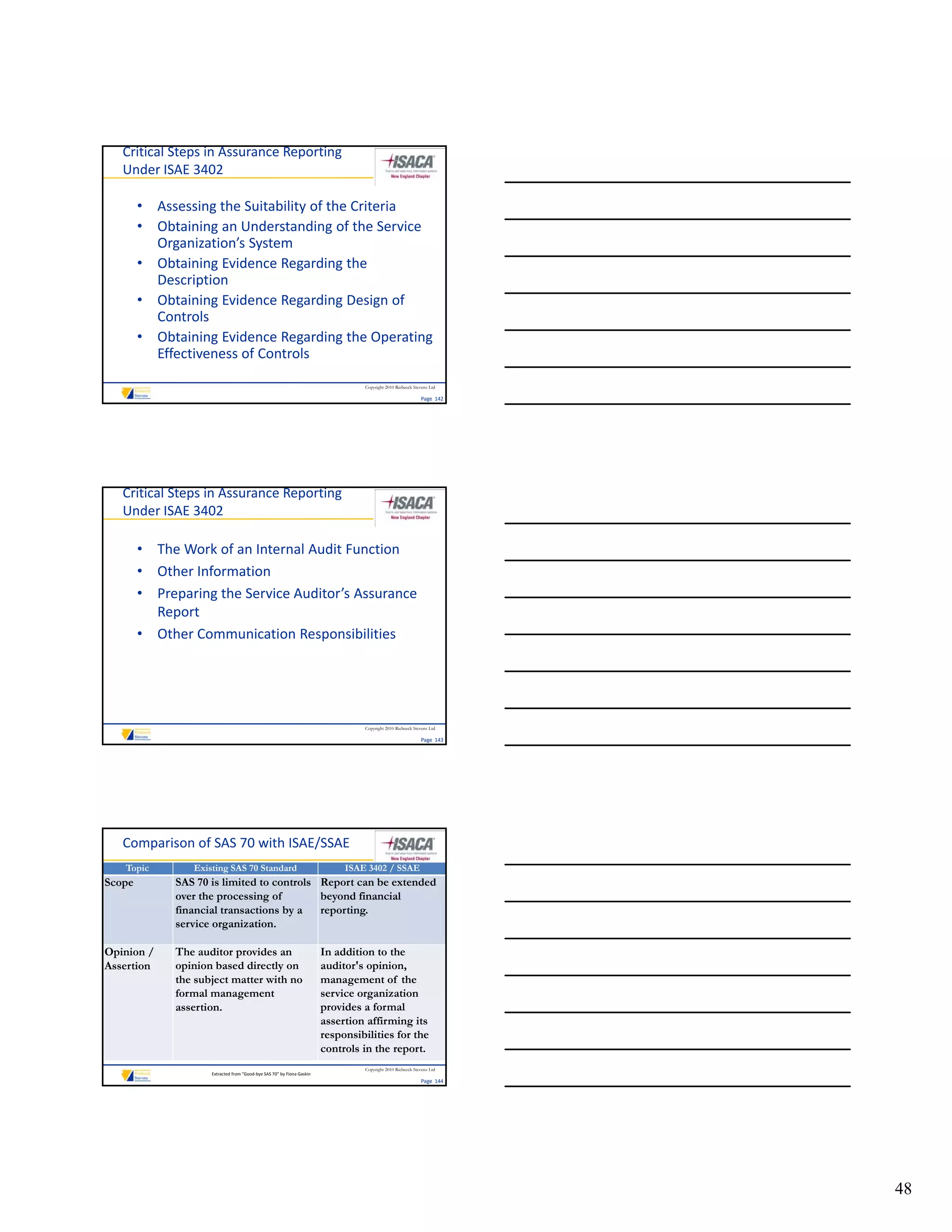
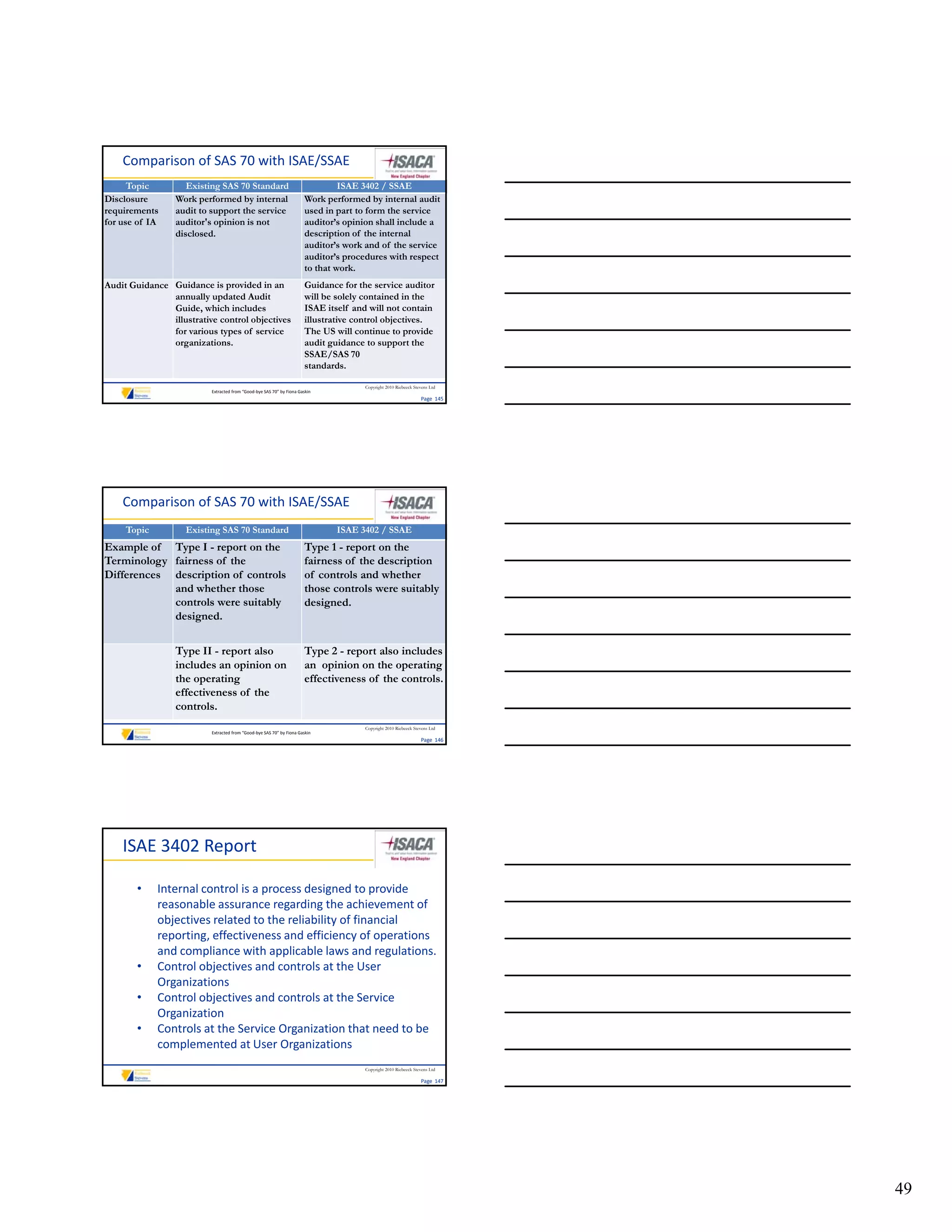
This document provides an overview of evaluating vendor risks at service organizations. It discusses assessing, managing, and controlling risks posed by third party vendors. The document outlines various assessment mechanisms for evaluating internal controls at service organizations, such as SAS 70, Shared Assessments, and ISAE 3402 reports. It also discusses how user organizations can obtain assurance about service organization controls through third party assurance engagements.