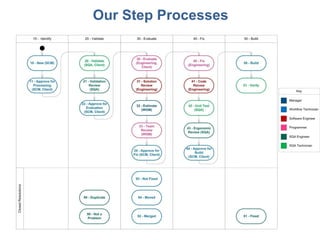
Essential Software, Inc. Step Process
•
0 likes•311 views
We have established step-by-step processes. These processes guide our work to ensure quality and efficiency. By following our processes, we aim to consistently deliver excellent results for our customers.
Report
Share
Report
Share
Recommended
XSS Without Browser

The document summarizes a talk given at Toorcon Seattle 2011 about cross-site scripting (XSS) vulnerabilities in desktop applications that use HTML, JavaScript and CSS for their user interfaces. The speaker demonstrates how XSS payloads can exploit Skype to inject content from other sites and access local files, since desktop apps do not enforce the same origin policy in the same way web browsers do. He urges testing applications like Skype, Adium and iChat that embed web technologies for similar vulnerabilities.
The project gutenberg e book, fairy tales every child should know

This document is the introduction to a collection of fairy tales edited by Hamilton Wright Mabie. It discusses how fairy tales provide a poetic interpretation of life that reconciles the imagination with reality. The introduction notes that early fairy tales predicted many scientific discoveries by envisioning powers over nature. It argues that fairy tales develop the same faculties as modern science and that their worlds are becoming reality. The introduction aims to encourage reading fairy tales to nourish the imagination.
The project gutenberg e book of welsh fairy tales, by william elliot griffis

This document summarizes a Welsh fairy tale about a monster named Afang that lived in a bog and terrorized the local community by eating people and flooding farms. A brave maiden and her lover devised a plan to lure the monster out of its lair using the maiden's beauty and perfumes, while the lover gathered farmers and blacksmiths to forge heavy chains to capture the monster. The summary captures the key details about the monster, its threatening behavior, and the plan developed by the maiden and her lover to defeat it.
Usability Testing Fundamentals

The document provides guidance on planning and conducting usability tests, including how to create test objectives and tasks, recruit participants, moderate the test, and analyze results, with the goal of helping readers learn how to effectively test the usability of a product or design.
Hacking Google Chrome OS

Hacking Google Chrome OS presentation slides, given at BlackHat USA 2011, BSidesLV 2011, and Defcon 19 (2011).
Check http://kyleosborn.org for more
Motivational Maps explained

Motivational Maps Ltd provides online personality assessments called Motivational Maps that are based on theories of human motivation. Their assessments can be used individually, with teams, and organizationally to understand people's energies, emotions, and how they are motivated. Motivational Maps has over 100 practitioners worldwide and offers their assessments and related services to charities, education, public sector, and corporate clients. Their assessments draw from theories of Maslow's hierarchy of needs, career anchors, and the Enneagram to provide accurate insights into motivation.
A / B Testing 

An introduction to A/B Testing !! How you can increase the sales by simple techniques :) Do contact us for more details : support@swaam.com.
Power Over Vs. Power With !!

Power Over Vs. Power With !! The document is not written by Swaam Tech. Its by Workplace solutions Inc.
Recommended
XSS Without Browser

The document summarizes a talk given at Toorcon Seattle 2011 about cross-site scripting (XSS) vulnerabilities in desktop applications that use HTML, JavaScript and CSS for their user interfaces. The speaker demonstrates how XSS payloads can exploit Skype to inject content from other sites and access local files, since desktop apps do not enforce the same origin policy in the same way web browsers do. He urges testing applications like Skype, Adium and iChat that embed web technologies for similar vulnerabilities.
The project gutenberg e book, fairy tales every child should know

This document is the introduction to a collection of fairy tales edited by Hamilton Wright Mabie. It discusses how fairy tales provide a poetic interpretation of life that reconciles the imagination with reality. The introduction notes that early fairy tales predicted many scientific discoveries by envisioning powers over nature. It argues that fairy tales develop the same faculties as modern science and that their worlds are becoming reality. The introduction aims to encourage reading fairy tales to nourish the imagination.
The project gutenberg e book of welsh fairy tales, by william elliot griffis

This document summarizes a Welsh fairy tale about a monster named Afang that lived in a bog and terrorized the local community by eating people and flooding farms. A brave maiden and her lover devised a plan to lure the monster out of its lair using the maiden's beauty and perfumes, while the lover gathered farmers and blacksmiths to forge heavy chains to capture the monster. The summary captures the key details about the monster, its threatening behavior, and the plan developed by the maiden and her lover to defeat it.
Usability Testing Fundamentals

The document provides guidance on planning and conducting usability tests, including how to create test objectives and tasks, recruit participants, moderate the test, and analyze results, with the goal of helping readers learn how to effectively test the usability of a product or design.
Hacking Google Chrome OS

Hacking Google Chrome OS presentation slides, given at BlackHat USA 2011, BSidesLV 2011, and Defcon 19 (2011).
Check http://kyleosborn.org for more
Motivational Maps explained

Motivational Maps Ltd provides online personality assessments called Motivational Maps that are based on theories of human motivation. Their assessments can be used individually, with teams, and organizationally to understand people's energies, emotions, and how they are motivated. Motivational Maps has over 100 practitioners worldwide and offers their assessments and related services to charities, education, public sector, and corporate clients. Their assessments draw from theories of Maslow's hierarchy of needs, career anchors, and the Enneagram to provide accurate insights into motivation.
A / B Testing 

An introduction to A/B Testing !! How you can increase the sales by simple techniques :) Do contact us for more details : support@swaam.com.
Power Over Vs. Power With !!

Power Over Vs. Power With !! The document is not written by Swaam Tech. Its by Workplace solutions Inc.
Kids Can Code - an interactive IT workshop

Presentation from Goran Velkoski & Ivana Nizamovska on SkopjeTechMeetup 7.
Every child should have the opportunity to learn computer science. It helps nurture problem-solving skills, logic and creativity. By starting early, kids will have the capability to shape the future. This are the main reasons why Goran and Ivana decided to organize “Kids can Code”, an introduction to computer science designed for 7-9 year olds to discover coding and show them that anybody can learn the basics.
Tricode = Career + Fun

Everyone is aware of the importance of life/work balance. It's a known fact that people are happier and more productive when rested and relaxed. Fun at work is what makes a difference in the long run.
Here at Tricode we give equal attention to both "soft" and technical skills, pleasant workdays and the actualization of our employees personal career and life goals. It's synced into our mission.
Understanding the Dalvik bytecode with the Dedexer tool

This document discusses the Dalvik virtual machine used in Android and how to decompile Dalvik bytecode using the Dedexer tool. It provides background on Android's use of Java and the Dalvik VM. Key points include: Dalvik uses its own bytecode format rather than Java bytecode and executes applications; the Dedexer tool can be used to disassemble DEX files back into Dalvik bytecode; and differences in Dalvik like its register-based rather than stack-based design are explained. Examples of Dalvik bytecode instructions and register usage are also provided.
How Technology is Affecting Society - STM 6

SkopjeTechMeetup is an initiative by Tricode for supporting and strengthening the Macedonian IT community. The meetups have the goal of establishing a networking platform for the IT crowd where they can share their know-how, best practices, as well as mutual inspiration.
The 6th STM installment took place at Piazza Liberta, Skopje last Thursday, the 29th of September. This meetup hosted 3 seasoned speakers, each accomplished in their own way.
Here's the presentation of Ermal Sadiku.
In a world where society is moved by science and technology more than anything, scientists and engineers have the power to change the world for better or worse. How should we look at and understand this in order to make the right choices?
12 hot features to engage and save time with aem 6.2

Adobe Experience Manager 6.2 is out now! Those slides shows the hottest new features of AEM 6.2. Now is the time to migrate to AEM 6.2 or to consider buying Adobe Experience Manager to target your audience in the most advanced way possible.
Usability Testing Fundamentals

The document provides an overview of how to plan and conduct usability testing, including how to determine objectives and target users, create scenarios and tasks, recruit participants, moderate a test by briefing users and having them complete tasks while thinking aloud, and analyze the results to identify areas for improvement. The level of detail covers everything from creating a test plan and protocol to practical tips for interacting with users and taking observational notes during a test. The goal is to educate readers on how to perform low-cost, low-effort usability testing to diagnose usability issues early in the design process.
Distributed deadlock

Distributed deadlock occurs when processes are blocked while waiting for resources held by other processes in a distributed system without a central coordinator. There are four conditions for deadlock: mutual exclusion, hold and wait, non-preemption, and circular wait. Deadlock can be addressed by ignoring it, detecting and resolving occurrences, preventing conditions through constraints, or avoiding it through careful resource allocation. Detection methods include centralized coordination of resource graphs or distributed probe messages to identify resource waiting cycles. Prevention strategies impose timestamp or age-based priority to resource requests to eliminate cycles.
Monkey runner & Monkey testing

MonkeyRunner an API for writing programs that control an android device or emulator for automation testing. An intro to Monkey testing too. In next slide we will be sharing how to run the tool with an example too.
Android & iPhone App Testing

SwaamTech, is an independent QA and Software Testing company helping clients to bring quality in there products. Contact us for testing of your SmartPhone App testing: support@swaam.com
Quality For Service Organizations

ISO 9001 provides standards for quality management systems that can be applied to service organizations. It aims to achieve customer satisfaction by meeting requirements and continually improving processes. Key aspects of a quality management system include management responsibility, resource management, developing and delivering services, and monitoring and improving processes. Implementing such a system helps organizations improve quality, consistency and customer satisfaction.
All About Bug

An error is a mistake in code, a bug is an error found before production, and a defect is an error found after production. Defects can arise from product specifications or customer expectations. Defects should be named, have their severity and type classified, and priorities assigned. Examples of different types of defects include user interface bugs, calculation bugs, and improper alignments. Components of a bug report include the title, severity, priority, type, steps to reproduce, actual/expected outputs, attachments, comments, and test environment details. Guidelines for writing effective bug reports include being precise, clear, and providing all necessary reproduction details.
Ielts handbook 2007

This document provides an overview of the International English Language Testing System (IELTS) exam, including information about its format, scoring, and administration. IELTS tests candidates' English abilities in listening, reading, writing, and speaking. It is jointly managed by Cambridge ESOL, the British Council, and IDP Australia. Test results are reported on a band scale of 1 to 9 and are recognized by universities, employers, and professional organizations around the world.
Essential Software, Inc. Support

ESW provides support for teams. The document discusses how ESW supports teams. It aims to help teams by offering support services.
Presentation of the OECD Artificial Intelligence Review of Germany

Consult the full report at https://www.oecd.org/digital/oecd-artificial-intelligence-review-of-germany-609808d6-en.htm
GNSS spoofing via SDR (Criptored Talks 2024)

In the realm of cybersecurity, offensive security practices act as a critical shield. By simulating real-world attacks in a controlled environment, these techniques expose vulnerabilities before malicious actors can exploit them. This proactive approach allows manufacturers to identify and fix weaknesses, significantly enhancing system security.
This presentation delves into the development of a system designed to mimic Galileo's Open Service signal using software-defined radio (SDR) technology. We'll begin with a foundational overview of both Global Navigation Satellite Systems (GNSS) and the intricacies of digital signal processing.
The presentation culminates in a live demonstration. We'll showcase the manipulation of Galileo's Open Service pilot signal, simulating an attack on various software and hardware systems. This practical demonstration serves to highlight the potential consequences of unaddressed vulnerabilities, emphasizing the importance of offensive security practices in safeguarding critical infrastructure.
HCL Notes and Domino License Cost Reduction in the World of DLAU

Webinar Recording: https://www.panagenda.com/webinars/hcl-notes-and-domino-license-cost-reduction-in-the-world-of-dlau/
The introduction of DLAU and the CCB & CCX licensing model caused quite a stir in the HCL community. As a Notes and Domino customer, you may have faced challenges with unexpected user counts and license costs. You probably have questions on how this new licensing approach works and how to benefit from it. Most importantly, you likely have budget constraints and want to save money where possible. Don’t worry, we can help with all of this!
We’ll show you how to fix common misconfigurations that cause higher-than-expected user counts, and how to identify accounts which you can deactivate to save money. There are also frequent patterns that can cause unnecessary cost, like using a person document instead of a mail-in for shared mailboxes. We’ll provide examples and solutions for those as well. And naturally we’ll explain the new licensing model.
Join HCL Ambassador Marc Thomas in this webinar with a special guest appearance from Franz Walder. It will give you the tools and know-how to stay on top of what is going on with Domino licensing. You will be able lower your cost through an optimized configuration and keep it low going forward.
These topics will be covered
- Reducing license cost by finding and fixing misconfigurations and superfluous accounts
- How do CCB and CCX licenses really work?
- Understanding the DLAU tool and how to best utilize it
- Tips for common problem areas, like team mailboxes, functional/test users, etc
- Practical examples and best practices to implement right away
Your One-Stop Shop for Python Success: Top 10 US Python Development Providers

Simplify your search for a reliable Python development partner! This list presents the top 10 trusted US providers offering comprehensive Python development services, ensuring your project's success from conception to completion.
Generating privacy-protected synthetic data using Secludy and Milvus

During this demo, the founders of Secludy will demonstrate how their system utilizes Milvus to store and manipulate embeddings for generating privacy-protected synthetic data. Their approach not only maintains the confidentiality of the original data but also enhances the utility and scalability of LLMs under privacy constraints. Attendees, including machine learning engineers, data scientists, and data managers, will witness first-hand how Secludy's integration with Milvus empowers organizations to harness the power of LLMs securely and efficiently.
“How Axelera AI Uses Digital Compute-in-memory to Deliver Fast and Energy-eff...

“How Axelera AI Uses Digital Compute-in-memory to Deliver Fast and Energy-eff...Edge AI and Vision Alliance
For the full video of this presentation, please visit: https://www.edge-ai-vision.com/2024/06/how-axelera-ai-uses-digital-compute-in-memory-to-deliver-fast-and-energy-efficient-computer-vision-a-presentation-from-axelera-ai/
Bram Verhoef, Head of Machine Learning at Axelera AI, presents the “How Axelera AI Uses Digital Compute-in-memory to Deliver Fast and Energy-efficient Computer Vision” tutorial at the May 2024 Embedded Vision Summit.
As artificial intelligence inference transitions from cloud environments to edge locations, computer vision applications achieve heightened responsiveness, reliability and privacy. This migration, however, introduces the challenge of operating within the stringent confines of resource constraints typical at the edge, including small form factors, low energy budgets and diminished memory and computational capacities. Axelera AI addresses these challenges through an innovative approach of performing digital computations within memory itself. This technique facilitates the realization of high-performance, energy-efficient and cost-effective computer vision capabilities at the thin and thick edge, extending the frontier of what is achievable with current technologies.
In this presentation, Verhoef unveils his company’s pioneering chip technology and demonstrates its capacity to deliver exceptional frames-per-second performance across a range of standard computer vision networks typical of applications in security, surveillance and the industrial sector. This shows that advanced computer vision can be accessible and efficient, even at the very edge of our technological ecosystem.Connector Corner: Seamlessly power UiPath Apps, GenAI with prebuilt connectors

Join us to learn how UiPath Apps can directly and easily interact with prebuilt connectors via Integration Service--including Salesforce, ServiceNow, Open GenAI, and more.
The best part is you can achieve this without building a custom workflow! Say goodbye to the hassle of using separate automations to call APIs. By seamlessly integrating within App Studio, you can now easily streamline your workflow, while gaining direct access to our Connector Catalog of popular applications.
We’ll discuss and demo the benefits of UiPath Apps and connectors including:
Creating a compelling user experience for any software, without the limitations of APIs.
Accelerating the app creation process, saving time and effort
Enjoying high-performance CRUD (create, read, update, delete) operations, for
seamless data management.
Speakers:
Russell Alfeche, Technology Leader, RPA at qBotic and UiPath MVP
Charlie Greenberg, host
Taking AI to the Next Level in Manufacturing.pdf

Read Taking AI to the Next Level in Manufacturing to gain insights on AI adoption in the manufacturing industry, such as:
1. How quickly AI is being implemented in manufacturing.
2. Which barriers stand in the way of AI adoption.
3. How data quality and governance form the backbone of AI.
4. Organizational processes and structures that may inhibit effective AI adoption.
6. Ideas and approaches to help build your organization's AI strategy.
Columbus Data & Analytics Wednesdays - June 2024

Columbus Data & Analytics Wednesdays, June 2024 with Maria Copot 20
More Related Content
Viewers also liked
Kids Can Code - an interactive IT workshop

Presentation from Goran Velkoski & Ivana Nizamovska on SkopjeTechMeetup 7.
Every child should have the opportunity to learn computer science. It helps nurture problem-solving skills, logic and creativity. By starting early, kids will have the capability to shape the future. This are the main reasons why Goran and Ivana decided to organize “Kids can Code”, an introduction to computer science designed for 7-9 year olds to discover coding and show them that anybody can learn the basics.
Tricode = Career + Fun

Everyone is aware of the importance of life/work balance. It's a known fact that people are happier and more productive when rested and relaxed. Fun at work is what makes a difference in the long run.
Here at Tricode we give equal attention to both "soft" and technical skills, pleasant workdays and the actualization of our employees personal career and life goals. It's synced into our mission.
Understanding the Dalvik bytecode with the Dedexer tool

This document discusses the Dalvik virtual machine used in Android and how to decompile Dalvik bytecode using the Dedexer tool. It provides background on Android's use of Java and the Dalvik VM. Key points include: Dalvik uses its own bytecode format rather than Java bytecode and executes applications; the Dedexer tool can be used to disassemble DEX files back into Dalvik bytecode; and differences in Dalvik like its register-based rather than stack-based design are explained. Examples of Dalvik bytecode instructions and register usage are also provided.
How Technology is Affecting Society - STM 6

SkopjeTechMeetup is an initiative by Tricode for supporting and strengthening the Macedonian IT community. The meetups have the goal of establishing a networking platform for the IT crowd where they can share their know-how, best practices, as well as mutual inspiration.
The 6th STM installment took place at Piazza Liberta, Skopje last Thursday, the 29th of September. This meetup hosted 3 seasoned speakers, each accomplished in their own way.
Here's the presentation of Ermal Sadiku.
In a world where society is moved by science and technology more than anything, scientists and engineers have the power to change the world for better or worse. How should we look at and understand this in order to make the right choices?
12 hot features to engage and save time with aem 6.2

Adobe Experience Manager 6.2 is out now! Those slides shows the hottest new features of AEM 6.2. Now is the time to migrate to AEM 6.2 or to consider buying Adobe Experience Manager to target your audience in the most advanced way possible.
Usability Testing Fundamentals

The document provides an overview of how to plan and conduct usability testing, including how to determine objectives and target users, create scenarios and tasks, recruit participants, moderate a test by briefing users and having them complete tasks while thinking aloud, and analyze the results to identify areas for improvement. The level of detail covers everything from creating a test plan and protocol to practical tips for interacting with users and taking observational notes during a test. The goal is to educate readers on how to perform low-cost, low-effort usability testing to diagnose usability issues early in the design process.
Distributed deadlock

Distributed deadlock occurs when processes are blocked while waiting for resources held by other processes in a distributed system without a central coordinator. There are four conditions for deadlock: mutual exclusion, hold and wait, non-preemption, and circular wait. Deadlock can be addressed by ignoring it, detecting and resolving occurrences, preventing conditions through constraints, or avoiding it through careful resource allocation. Detection methods include centralized coordination of resource graphs or distributed probe messages to identify resource waiting cycles. Prevention strategies impose timestamp or age-based priority to resource requests to eliminate cycles.
Monkey runner & Monkey testing

MonkeyRunner an API for writing programs that control an android device or emulator for automation testing. An intro to Monkey testing too. In next slide we will be sharing how to run the tool with an example too.
Android & iPhone App Testing

SwaamTech, is an independent QA and Software Testing company helping clients to bring quality in there products. Contact us for testing of your SmartPhone App testing: support@swaam.com
Quality For Service Organizations

ISO 9001 provides standards for quality management systems that can be applied to service organizations. It aims to achieve customer satisfaction by meeting requirements and continually improving processes. Key aspects of a quality management system include management responsibility, resource management, developing and delivering services, and monitoring and improving processes. Implementing such a system helps organizations improve quality, consistency and customer satisfaction.
All About Bug

An error is a mistake in code, a bug is an error found before production, and a defect is an error found after production. Defects can arise from product specifications or customer expectations. Defects should be named, have their severity and type classified, and priorities assigned. Examples of different types of defects include user interface bugs, calculation bugs, and improper alignments. Components of a bug report include the title, severity, priority, type, steps to reproduce, actual/expected outputs, attachments, comments, and test environment details. Guidelines for writing effective bug reports include being precise, clear, and providing all necessary reproduction details.
Ielts handbook 2007

This document provides an overview of the International English Language Testing System (IELTS) exam, including information about its format, scoring, and administration. IELTS tests candidates' English abilities in listening, reading, writing, and speaking. It is jointly managed by Cambridge ESOL, the British Council, and IDP Australia. Test results are reported on a band scale of 1 to 9 and are recognized by universities, employers, and professional organizations around the world.
Essential Software, Inc. Support

ESW provides support for teams. The document discusses how ESW supports teams. It aims to help teams by offering support services.
Viewers also liked (13)
Understanding the Dalvik bytecode with the Dedexer tool

Understanding the Dalvik bytecode with the Dedexer tool
12 hot features to engage and save time with aem 6.2

12 hot features to engage and save time with aem 6.2
Recently uploaded
Presentation of the OECD Artificial Intelligence Review of Germany

Consult the full report at https://www.oecd.org/digital/oecd-artificial-intelligence-review-of-germany-609808d6-en.htm
GNSS spoofing via SDR (Criptored Talks 2024)

In the realm of cybersecurity, offensive security practices act as a critical shield. By simulating real-world attacks in a controlled environment, these techniques expose vulnerabilities before malicious actors can exploit them. This proactive approach allows manufacturers to identify and fix weaknesses, significantly enhancing system security.
This presentation delves into the development of a system designed to mimic Galileo's Open Service signal using software-defined radio (SDR) technology. We'll begin with a foundational overview of both Global Navigation Satellite Systems (GNSS) and the intricacies of digital signal processing.
The presentation culminates in a live demonstration. We'll showcase the manipulation of Galileo's Open Service pilot signal, simulating an attack on various software and hardware systems. This practical demonstration serves to highlight the potential consequences of unaddressed vulnerabilities, emphasizing the importance of offensive security practices in safeguarding critical infrastructure.
HCL Notes and Domino License Cost Reduction in the World of DLAU

Webinar Recording: https://www.panagenda.com/webinars/hcl-notes-and-domino-license-cost-reduction-in-the-world-of-dlau/
The introduction of DLAU and the CCB & CCX licensing model caused quite a stir in the HCL community. As a Notes and Domino customer, you may have faced challenges with unexpected user counts and license costs. You probably have questions on how this new licensing approach works and how to benefit from it. Most importantly, you likely have budget constraints and want to save money where possible. Don’t worry, we can help with all of this!
We’ll show you how to fix common misconfigurations that cause higher-than-expected user counts, and how to identify accounts which you can deactivate to save money. There are also frequent patterns that can cause unnecessary cost, like using a person document instead of a mail-in for shared mailboxes. We’ll provide examples and solutions for those as well. And naturally we’ll explain the new licensing model.
Join HCL Ambassador Marc Thomas in this webinar with a special guest appearance from Franz Walder. It will give you the tools and know-how to stay on top of what is going on with Domino licensing. You will be able lower your cost through an optimized configuration and keep it low going forward.
These topics will be covered
- Reducing license cost by finding and fixing misconfigurations and superfluous accounts
- How do CCB and CCX licenses really work?
- Understanding the DLAU tool and how to best utilize it
- Tips for common problem areas, like team mailboxes, functional/test users, etc
- Practical examples and best practices to implement right away
Your One-Stop Shop for Python Success: Top 10 US Python Development Providers

Simplify your search for a reliable Python development partner! This list presents the top 10 trusted US providers offering comprehensive Python development services, ensuring your project's success from conception to completion.
Generating privacy-protected synthetic data using Secludy and Milvus

During this demo, the founders of Secludy will demonstrate how their system utilizes Milvus to store and manipulate embeddings for generating privacy-protected synthetic data. Their approach not only maintains the confidentiality of the original data but also enhances the utility and scalability of LLMs under privacy constraints. Attendees, including machine learning engineers, data scientists, and data managers, will witness first-hand how Secludy's integration with Milvus empowers organizations to harness the power of LLMs securely and efficiently.
“How Axelera AI Uses Digital Compute-in-memory to Deliver Fast and Energy-eff...

“How Axelera AI Uses Digital Compute-in-memory to Deliver Fast and Energy-eff...Edge AI and Vision Alliance
For the full video of this presentation, please visit: https://www.edge-ai-vision.com/2024/06/how-axelera-ai-uses-digital-compute-in-memory-to-deliver-fast-and-energy-efficient-computer-vision-a-presentation-from-axelera-ai/
Bram Verhoef, Head of Machine Learning at Axelera AI, presents the “How Axelera AI Uses Digital Compute-in-memory to Deliver Fast and Energy-efficient Computer Vision” tutorial at the May 2024 Embedded Vision Summit.
As artificial intelligence inference transitions from cloud environments to edge locations, computer vision applications achieve heightened responsiveness, reliability and privacy. This migration, however, introduces the challenge of operating within the stringent confines of resource constraints typical at the edge, including small form factors, low energy budgets and diminished memory and computational capacities. Axelera AI addresses these challenges through an innovative approach of performing digital computations within memory itself. This technique facilitates the realization of high-performance, energy-efficient and cost-effective computer vision capabilities at the thin and thick edge, extending the frontier of what is achievable with current technologies.
In this presentation, Verhoef unveils his company’s pioneering chip technology and demonstrates its capacity to deliver exceptional frames-per-second performance across a range of standard computer vision networks typical of applications in security, surveillance and the industrial sector. This shows that advanced computer vision can be accessible and efficient, even at the very edge of our technological ecosystem.Connector Corner: Seamlessly power UiPath Apps, GenAI with prebuilt connectors

Join us to learn how UiPath Apps can directly and easily interact with prebuilt connectors via Integration Service--including Salesforce, ServiceNow, Open GenAI, and more.
The best part is you can achieve this without building a custom workflow! Say goodbye to the hassle of using separate automations to call APIs. By seamlessly integrating within App Studio, you can now easily streamline your workflow, while gaining direct access to our Connector Catalog of popular applications.
We’ll discuss and demo the benefits of UiPath Apps and connectors including:
Creating a compelling user experience for any software, without the limitations of APIs.
Accelerating the app creation process, saving time and effort
Enjoying high-performance CRUD (create, read, update, delete) operations, for
seamless data management.
Speakers:
Russell Alfeche, Technology Leader, RPA at qBotic and UiPath MVP
Charlie Greenberg, host
Taking AI to the Next Level in Manufacturing.pdf

Read Taking AI to the Next Level in Manufacturing to gain insights on AI adoption in the manufacturing industry, such as:
1. How quickly AI is being implemented in manufacturing.
2. Which barriers stand in the way of AI adoption.
3. How data quality and governance form the backbone of AI.
4. Organizational processes and structures that may inhibit effective AI adoption.
6. Ideas and approaches to help build your organization's AI strategy.
Columbus Data & Analytics Wednesdays - June 2024

Columbus Data & Analytics Wednesdays, June 2024 with Maria Copot 20
HCL Notes und Domino Lizenzkostenreduzierung in der Welt von DLAU

Webinar Recording: https://www.panagenda.com/webinars/hcl-notes-und-domino-lizenzkostenreduzierung-in-der-welt-von-dlau/
DLAU und die Lizenzen nach dem CCB- und CCX-Modell sind für viele in der HCL-Community seit letztem Jahr ein heißes Thema. Als Notes- oder Domino-Kunde haben Sie vielleicht mit unerwartet hohen Benutzerzahlen und Lizenzgebühren zu kämpfen. Sie fragen sich vielleicht, wie diese neue Art der Lizenzierung funktioniert und welchen Nutzen sie Ihnen bringt. Vor allem wollen Sie sicherlich Ihr Budget einhalten und Kosten sparen, wo immer möglich. Das verstehen wir und wir möchten Ihnen dabei helfen!
Wir erklären Ihnen, wie Sie häufige Konfigurationsprobleme lösen können, die dazu führen können, dass mehr Benutzer gezählt werden als nötig, und wie Sie überflüssige oder ungenutzte Konten identifizieren und entfernen können, um Geld zu sparen. Es gibt auch einige Ansätze, die zu unnötigen Ausgaben führen können, z. B. wenn ein Personendokument anstelle eines Mail-Ins für geteilte Mailboxen verwendet wird. Wir zeigen Ihnen solche Fälle und deren Lösungen. Und natürlich erklären wir Ihnen das neue Lizenzmodell.
Nehmen Sie an diesem Webinar teil, bei dem HCL-Ambassador Marc Thomas und Gastredner Franz Walder Ihnen diese neue Welt näherbringen. Es vermittelt Ihnen die Tools und das Know-how, um den Überblick zu bewahren. Sie werden in der Lage sein, Ihre Kosten durch eine optimierte Domino-Konfiguration zu reduzieren und auch in Zukunft gering zu halten.
Diese Themen werden behandelt
- Reduzierung der Lizenzkosten durch Auffinden und Beheben von Fehlkonfigurationen und überflüssigen Konten
- Wie funktionieren CCB- und CCX-Lizenzen wirklich?
- Verstehen des DLAU-Tools und wie man es am besten nutzt
- Tipps für häufige Problembereiche, wie z. B. Team-Postfächer, Funktions-/Testbenutzer usw.
- Praxisbeispiele und Best Practices zum sofortigen Umsetzen
Astute Business Solutions | Oracle Cloud Partner |

Your goto partner for Oracle Cloud, PeopleSoft, E-Business Suite, and Ellucian Banner. We are a firm specialized in managed services and consulting.
"Choosing proper type of scaling", Olena Syrota

Imagine an IoT processing system that is already quite mature and production-ready and for which client coverage is growing and scaling and performance aspects are life and death questions. The system has Redis, MongoDB, and stream processing based on ksqldb. In this talk, firstly, we will analyze scaling approaches and then select the proper ones for our system.
TrustArc Webinar - 2024 Global Privacy Survey

How does your privacy program stack up against your peers? What challenges are privacy teams tackling and prioritizing in 2024?
In the fifth annual Global Privacy Benchmarks Survey, we asked over 1,800 global privacy professionals and business executives to share their perspectives on the current state of privacy inside and outside of their organizations. This year’s report focused on emerging areas of importance for privacy and compliance professionals, including considerations and implications of Artificial Intelligence (AI) technologies, building brand trust, and different approaches for achieving higher privacy competence scores.
See how organizational priorities and strategic approaches to data security and privacy are evolving around the globe.
This webinar will review:
- The top 10 privacy insights from the fifth annual Global Privacy Benchmarks Survey
- The top challenges for privacy leaders, practitioners, and organizations in 2024
- Key themes to consider in developing and maintaining your privacy program
FREE A4 Cyber Security Awareness Posters-Social Engineering part 3

Free A4 downloadable and printable Cyber Security, Social Engineering Safety and security Training Posters . Promote security awareness in the home or workplace. Lock them Out From training providers datahops.com
zkStudyClub - LatticeFold: A Lattice-based Folding Scheme and its Application...

Folding is a recent technique for building efficient recursive SNARKs. Several elegant folding protocols have been proposed, such as Nova, Supernova, Hypernova, Protostar, and others. However, all of them rely on an additively homomorphic commitment scheme based on discrete log, and are therefore not post-quantum secure. In this work we present LatticeFold, the first lattice-based folding protocol based on the Module SIS problem. This folding protocol naturally leads to an efficient recursive lattice-based SNARK and an efficient PCD scheme. LatticeFold supports folding low-degree relations, such as R1CS, as well as high-degree relations, such as CCS. The key challenge is to construct a secure folding protocol that works with the Ajtai commitment scheme. The difficulty, is ensuring that extracted witnesses are low norm through many rounds of folding. We present a novel technique using the sumcheck protocol to ensure that extracted witnesses are always low norm no matter how many rounds of folding are used. Our evaluation of the final proof system suggests that it is as performant as Hypernova, while providing post-quantum security.
Paper Link: https://eprint.iacr.org/2024/257
5th LF Energy Power Grid Model Meet-up Slides

5th Power Grid Model Meet-up
It is with great pleasure that we extend to you an invitation to the 5th Power Grid Model Meet-up, scheduled for 6th June 2024. This event will adopt a hybrid format, allowing participants to join us either through an online Mircosoft Teams session or in person at TU/e located at Den Dolech 2, Eindhoven, Netherlands. The meet-up will be hosted by Eindhoven University of Technology (TU/e), a research university specializing in engineering science & technology.
Power Grid Model
The global energy transition is placing new and unprecedented demands on Distribution System Operators (DSOs). Alongside upgrades to grid capacity, processes such as digitization, capacity optimization, and congestion management are becoming vital for delivering reliable services.
Power Grid Model is an open source project from Linux Foundation Energy and provides a calculation engine that is increasingly essential for DSOs. It offers a standards-based foundation enabling real-time power systems analysis, simulations of electrical power grids, and sophisticated what-if analysis. In addition, it enables in-depth studies and analysis of the electrical power grid’s behavior and performance. This comprehensive model incorporates essential factors such as power generation capacity, electrical losses, voltage levels, power flows, and system stability.
Power Grid Model is currently being applied in a wide variety of use cases, including grid planning, expansion, reliability, and congestion studies. It can also help in analyzing the impact of renewable energy integration, assessing the effects of disturbances or faults, and developing strategies for grid control and optimization.
What to expect
For the upcoming meetup we are organizing, we have an exciting lineup of activities planned:
-Insightful presentations covering two practical applications of the Power Grid Model.
-An update on the latest advancements in Power Grid -Model technology during the first and second quarters of 2024.
-An interactive brainstorming session to discuss and propose new feature requests.
-An opportunity to connect with fellow Power Grid Model enthusiasts and users.
Freshworks Rethinks NoSQL for Rapid Scaling & Cost-Efficiency

Freshworks creates AI-boosted business software that helps employees work more efficiently and effectively. Managing data across multiple RDBMS and NoSQL databases was already a challenge at their current scale. To prepare for 10X growth, they knew it was time to rethink their database strategy. Learn how they architected a solution that would simplify scaling while keeping costs under control.
June Patch Tuesday

Ivanti’s Patch Tuesday breakdown goes beyond patching your applications and brings you the intelligence and guidance needed to prioritize where to focus your attention first. Catch early analysis on our Ivanti blog, then join industry expert Chris Goettl for the Patch Tuesday Webinar Event. There we’ll do a deep dive into each of the bulletins and give guidance on the risks associated with the newly-identified vulnerabilities.
Recently uploaded (20)
Presentation of the OECD Artificial Intelligence Review of Germany

Presentation of the OECD Artificial Intelligence Review of Germany
HCL Notes and Domino License Cost Reduction in the World of DLAU

HCL Notes and Domino License Cost Reduction in the World of DLAU
Your One-Stop Shop for Python Success: Top 10 US Python Development Providers

Your One-Stop Shop for Python Success: Top 10 US Python Development Providers
Generating privacy-protected synthetic data using Secludy and Milvus

Generating privacy-protected synthetic data using Secludy and Milvus
“How Axelera AI Uses Digital Compute-in-memory to Deliver Fast and Energy-eff...

“How Axelera AI Uses Digital Compute-in-memory to Deliver Fast and Energy-eff...
Connector Corner: Seamlessly power UiPath Apps, GenAI with prebuilt connectors

Connector Corner: Seamlessly power UiPath Apps, GenAI with prebuilt connectors
HCL Notes und Domino Lizenzkostenreduzierung in der Welt von DLAU

HCL Notes und Domino Lizenzkostenreduzierung in der Welt von DLAU
Astute Business Solutions | Oracle Cloud Partner |

Astute Business Solutions | Oracle Cloud Partner |
FREE A4 Cyber Security Awareness Posters-Social Engineering part 3

FREE A4 Cyber Security Awareness Posters-Social Engineering part 3
zkStudyClub - LatticeFold: A Lattice-based Folding Scheme and its Application...

zkStudyClub - LatticeFold: A Lattice-based Folding Scheme and its Application...
Freshworks Rethinks NoSQL for Rapid Scaling & Cost-Efficiency

Freshworks Rethinks NoSQL for Rapid Scaling & Cost-Efficiency