The document discusses the necessity of parallel processing in programming due to limitations in raising CPU clock speeds and the trend towards multi-core processors. It introduces Erlang, a programming language designed for concurrency, distribution, and robustness, including its features like the actor model and immutable data types. The document outlines different sessions on Erlang concepts, data types, I/O operations, modules, and recursion, emphasizing the advantages of using Erlang over traditional programming languages.
![Data types
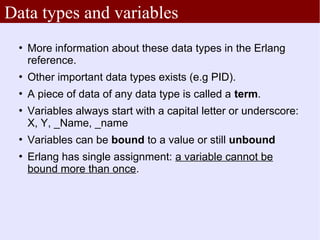
Numbers: 12, -100, 15.55, $a
Atoms: x, ayman, faculty_of_law
Simple atoms cannot begin with a capital letter or have spaces,
but single quotes can be used to bypass those rules: 'Samy',
'calculus book'
Tuples: { samy, 1979, cairo }, {13, 28}
Lists: [ ], [1, 2, 3], [a, [b, c], {1, 2} ]
Strings: "Hello world"
This actually is the list [$H, $e, $l, $l, $o, $ ,$w, $o, $r, $l, $d ]
All these data types are immutable](https://image.slidesharecdn.com/erlang-session1-110831184700-phpapp02/85/Erlang-session1-11-320.jpg)
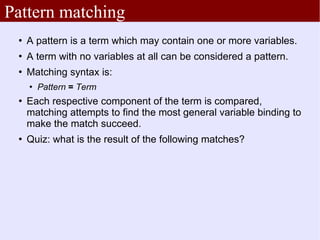
![Pattern matching
5=5.
{Name, Age, _} = {“Osama”, 28, cairo }.
[1,2] = {1, 2}.
"hello" = "hello".
"ABC" = [65, 66, 67].
$a = a.](https://image.slidesharecdn.com/erlang-session1-110831184700-phpapp02/85/Erlang-session1-14-320.jpg)
![Pattern matching on lists
[ H | T ] = [1, 2, 3].
[ H | T ] = [ ].
[ H | T ] = [1, 2].
[ H1, H2 | T ] = [1, 2, 3].
[ H1, H2 | T ] = [1, 2].
[A, B] ++ [ H| T] = "faculty".
"Mustafa" ++ X = "Mustafa Kamel".](https://image.slidesharecdn.com/erlang-session1-110831184700-phpapp02/85/Erlang-session1-16-320.jpg)
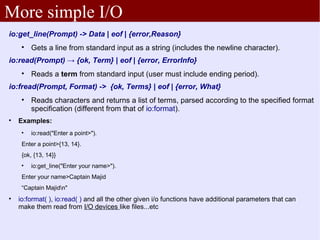
![Some simple I/O
io:format(fmt_str, [arg0,arg1... ])
Examples:
io:format("The results are ~p and ~p", [15, 16]).
io:format("Hello world ~n", [ ]).
io:format("Hello world ~n").
Codes:
~~ : The '~' mark (needs no argument)
~f : Format argument as floating point
~c : Format argument as a character.
~w : Format argument in standard syntax (i.e like terms in the language)
~p : Standard syntax for printing (e.g turns lists of printable characters into strings)
~n : newline character (doesn't need an argument).
Much more detail in the documentation. Erlang has very rich formatting
features.](https://image.slidesharecdn.com/erlang-session1-110831184700-phpapp02/85/Erlang-session1-17-320.jpg)
![Modules
-module(addition).
-export([add/2, add/3]).
add(X, Y) -> X+Y.
add(X, Y, Z) -> X+Y+Z.
unused_func( ) -> io:format("unused!").
% End of module definition.
Erlang code is divided into modules.
A module has attributes at the top (the begin with the dash character '-') and is followed by
function declarations. Both attributes and declaration end with a dot '.'
Exported function names must include its artiy (number of parameters).
Two functions with the same name but different arities are different functions!](https://image.slidesharecdn.com/erlang-session1-110831184700-phpapp02/85/Erlang-session1-19-320.jpg)
![Functions
add(A, B) → A+B.
− Return value is the function's expression
add(A, B) →
io:format(“now adding ~p and ~p~n", [A, B]),
A+B.
− In case of multiple expressions, return value is the last
one](https://image.slidesharecdn.com/erlang-session1-110831184700-phpapp02/85/Erlang-session1-20-320.jpg)