Edva horng 0
•
0 likes•12 views
criminal case ini dia biang dari sipelaku teroris beacukai federau , 284 people masuk indo melewati selangor dari negar luar
Report
Share
Report
Share
Download to read offline
Recommended
Electronic fraud by prof godwin oyedokun (1)

Electronic fraud by prof godwin oyedokun (1)Godwin Emmanuel Oyedokun MBA MSc PhD FCA FCTI FCNA CFE FFAR
Fraud InvestigationWhat You Need to Know to Avoid Identity Theft

company names mentioned herein are for identification and educational purposes only and are the property of, and may be trademarks of, their respective owners.
Recommended
Electronic fraud by prof godwin oyedokun (1)

Electronic fraud by prof godwin oyedokun (1)Godwin Emmanuel Oyedokun MBA MSc PhD FCA FCTI FCNA CFE FFAR
Fraud InvestigationWhat You Need to Know to Avoid Identity Theft

company names mentioned herein are for identification and educational purposes only and are the property of, and may be trademarks of, their respective owners.
25 Internet Crimes

It is an authentic study. ( ISBN 978-969-23197-2-0 )
Internet Crime Complaint Center (www.ic3.gov) and PISA must give award to writer.
How to Protect Yourself From Identity Theft

Join our #CreditChat every Wednesday at 3 p.m. ET on Twitter and YouTube. This week, we discussed the very important topic of identity theft and learned tips about how we can protect ourselves. This deck features highlights from our chat with tips from: @LeslieHTayneEsq, @NatlJumpStart, @Frostbe, @DebbiKing, @RAHomes, @SouthStateBank, @BahiyahShabazz, @WelshKristy, @yesiamcheap and @FacingFinances.
Identity Theft: How to Avoid It

This was a presentation by Hewie Poplock on Tuesday, November 15th, 2016 in the Goodwill Manasota (FL) Ranch Lake Community Room, "How to Avoid Identity Theft".
A victim of identity theft himself, Hewie will provide examples of how ID theft can happen as well as suggestions and precautions on how to prevent you and your family from becoming victims of identity theft yourselves. Topics covered included:
• What is Identity Theft
• How ID Theft Happens
• How to Protect Yourself
• Phishing
• Data Breaches
• Facebook Spoofing
• Skimmers
• Security Freeze
• On Line Shopping Safety
• Credit Card Chips
• What to Do If You are a Victim
Hewie is a former teacher, college instructor, business owner and manager, IT Manager, and web designer. He is currently semi-retired, but is active in technology user groups and frequently speaks to and teaches groups who are mostly seniors. He holds a monthly Windows Special Interest Group for a group in Orlando and has several videos on YouTube. He is an active member of The Sarasota Technology User Group.
Identity Theft: How to Reduce Your Risk

Dr. Barbara O'Neill and Carol Kando-Pineda, of the Federal Trade Commission, will present this 90-minute webinar on behalf of the Military Families Learning Network. This 90-minute webinar will include two sections: a general overview of identity theft and discussion about military-specific scams. Topics covered during the first section, presented by Dr. O’Neill, include a definition of identity theft, signs of identity theft, an identity theft risk assessment quiz, types of identity theft, how identity theft occurs, ways to reduce identity theft risk, phishing scams, proactive and reactive identity theft actions, and identity theft resources. Ms. Kando-Pineda plans to discuss getting help for identity theft victims, including the steps they need to take immediately, walking through the new features for consumers on Identitytheft.gov and how they help victims develop a recovery plan, get a heads-up on the latest “imposter” scams, and an update on the Military Consumer campaign and new resources on the way for the military community.
Senior Citizen Crime Prevention

A presentation for Senior Citizens about common scams used to get your money
How Credit Card Fraud Happens and How You Can Protect Yourself

Often a simple transaction is responsible for a crime that can potentially turn a credit card holder’s life completely upside down. Learn how to protect yourself from identity theft.
New Utility Scam: Alert from David Lerner Associates

Be alert for two recent scams revolving around the payment of utility bills. This alert from David Lerner Associates has the details of what to watch for.
Common Consumer Frauds & How to Avoid Them

Dr. Barbara O'Neill of Rutgers University and Carol Kando-Pineda of the Federal Trade Commission will present this 90-minute session on behalf of the Military Families Learning Network on March 20 at 11 a.m. ET. More info: https://learn.extension.org/events/1500/
Identity Theft: Protecting Our Seniors

Scott Tolstad of the Escondido Police Department explains different ways senior citizens are scammed out of their money, particularly by thieves who steal identities. It's a valuable lesson for all of us, regardless of age, to know. Scott spoke during the June 7, 2013 Glenner Symposium on Elder Abuse.
Social networking and identity theft 

Presentation my daughter drafted for a class assignment; discusses social networking and risks of identity theft
Implied representation

AQA A-Level Law U4 requires you to know the offence of fraud by false representation, implied representations are a part of this.
More Related Content
What's hot
25 Internet Crimes

It is an authentic study. ( ISBN 978-969-23197-2-0 )
Internet Crime Complaint Center (www.ic3.gov) and PISA must give award to writer.
How to Protect Yourself From Identity Theft

Join our #CreditChat every Wednesday at 3 p.m. ET on Twitter and YouTube. This week, we discussed the very important topic of identity theft and learned tips about how we can protect ourselves. This deck features highlights from our chat with tips from: @LeslieHTayneEsq, @NatlJumpStart, @Frostbe, @DebbiKing, @RAHomes, @SouthStateBank, @BahiyahShabazz, @WelshKristy, @yesiamcheap and @FacingFinances.
Identity Theft: How to Avoid It

This was a presentation by Hewie Poplock on Tuesday, November 15th, 2016 in the Goodwill Manasota (FL) Ranch Lake Community Room, "How to Avoid Identity Theft".
A victim of identity theft himself, Hewie will provide examples of how ID theft can happen as well as suggestions and precautions on how to prevent you and your family from becoming victims of identity theft yourselves. Topics covered included:
• What is Identity Theft
• How ID Theft Happens
• How to Protect Yourself
• Phishing
• Data Breaches
• Facebook Spoofing
• Skimmers
• Security Freeze
• On Line Shopping Safety
• Credit Card Chips
• What to Do If You are a Victim
Hewie is a former teacher, college instructor, business owner and manager, IT Manager, and web designer. He is currently semi-retired, but is active in technology user groups and frequently speaks to and teaches groups who are mostly seniors. He holds a monthly Windows Special Interest Group for a group in Orlando and has several videos on YouTube. He is an active member of The Sarasota Technology User Group.
Identity Theft: How to Reduce Your Risk

Dr. Barbara O'Neill and Carol Kando-Pineda, of the Federal Trade Commission, will present this 90-minute webinar on behalf of the Military Families Learning Network. This 90-minute webinar will include two sections: a general overview of identity theft and discussion about military-specific scams. Topics covered during the first section, presented by Dr. O’Neill, include a definition of identity theft, signs of identity theft, an identity theft risk assessment quiz, types of identity theft, how identity theft occurs, ways to reduce identity theft risk, phishing scams, proactive and reactive identity theft actions, and identity theft resources. Ms. Kando-Pineda plans to discuss getting help for identity theft victims, including the steps they need to take immediately, walking through the new features for consumers on Identitytheft.gov and how they help victims develop a recovery plan, get a heads-up on the latest “imposter” scams, and an update on the Military Consumer campaign and new resources on the way for the military community.
Senior Citizen Crime Prevention

A presentation for Senior Citizens about common scams used to get your money
How Credit Card Fraud Happens and How You Can Protect Yourself

Often a simple transaction is responsible for a crime that can potentially turn a credit card holder’s life completely upside down. Learn how to protect yourself from identity theft.
New Utility Scam: Alert from David Lerner Associates

Be alert for two recent scams revolving around the payment of utility bills. This alert from David Lerner Associates has the details of what to watch for.
Common Consumer Frauds & How to Avoid Them

Dr. Barbara O'Neill of Rutgers University and Carol Kando-Pineda of the Federal Trade Commission will present this 90-minute session on behalf of the Military Families Learning Network on March 20 at 11 a.m. ET. More info: https://learn.extension.org/events/1500/
Identity Theft: Protecting Our Seniors

Scott Tolstad of the Escondido Police Department explains different ways senior citizens are scammed out of their money, particularly by thieves who steal identities. It's a valuable lesson for all of us, regardless of age, to know. Scott spoke during the June 7, 2013 Glenner Symposium on Elder Abuse.
Social networking and identity theft 

Presentation my daughter drafted for a class assignment; discusses social networking and risks of identity theft
What's hot (20)
How Credit Card Fraud Happens and How You Can Protect Yourself

How Credit Card Fraud Happens and How You Can Protect Yourself
New Utility Scam: Alert from David Lerner Associates

New Utility Scam: Alert from David Lerner Associates
Similar to Edva horng 0
Implied representation

AQA A-Level Law U4 requires you to know the offence of fraud by false representation, implied representations are a part of this.
Of all the forms of finance finance crimes discussed, which do you c.pdf

Of all the forms of finance finance crimes discussed, which do you consider the most serious,
and why? Are there any forms of finance crime that you do not think should be considered a
crime? If so, why?
Solution
Fraud and financial crimes are a form of theft/larceny that occur when a person or entity takes
money or property, or uses them in an illicit manner, with the intent to gain a benefit from it.
These crimes typically involve some form of deceit, subterfuge or the abuse of a position of trust,
which distinguishes them from common theft or robbery. In today\'s complex economy, fraud
and financial crimes can take many forms. The resources below will introduce you to the more
common forms of financial crimes, such as forgery, credit card fraud, embezzlement and money
laundering.« Show Less
Debit/Credit Card Fraud
Debit and credit card fraud also occurs when an individual has an intent to fraudulently obtain
money, goods, or services by using the access card of a cardholder who has not authorized its
use. Common examples of credit or debit card fraud include using someone else\'s credit or debit
card without that person\'s consent, using your own credit or debit card knowing that it has been
revoked or expired or that your available balance is less than the purchase price, and using a
stolen or fraudulent credit or debit card to receive money, goods or services.
Forgery
The crime of forgery occurs when, with the intent to defraud, a person executes, alters or
publishes a writing without the owner\'s knowledge or consent. This can also happen if s/he
fraudulently makes a writing and holds it out to be the work of another. A \"writing\" can include
money, coins, credit cards, checks, bank drafts, stock certificates, bonds, wills and deeds.
Wire Fraud
The crime of wire fraud occurs when someone voluntarily and intentionally uses an interstate
communications device (such as a telephone or the internet) as a part of any scheme to defraud
another of property, or anything else of value. For example, if you try to sell property you do not
own, and in your attempt you use a your smartphone to send an email to someone trying to
convince that person to purchase the land, you commit wire fraud. Wire fraud is a federal crime
with serious potential consequences.
Types of Insurance Fraud
Insurance fraud is stealing. Simply put, insurance fraud is lying for the purpose of getting more
money from an insurance company, whether it is auto insurance, life insurance, or any other kind
of insurance. There are two types of insurance fraud: soft and hard fraud. An example of soft
fraud is getting into a motorcycle accident and claiming your injuries are worse than they really
are for financial gain. An example of hard fraud would be getting into that same motorcycle
accident on purpose so that you can claim the insurance money..
Assignment 5 consumer fraud protection

A slide show that I compiled for my post master's certificate program, through Northcentral University, in Business Administration, with a specialization on Advanced Accounting. This is assignment 5 Consumer Fraud Prevention.
Citizenfour producers-face-legal-challenges-over-edward-snowden-leaks

A lawsuit has been filed against The Weinstein Co., Participant Media and others for aiding and abetting Edward Snowden, the American whistleblower, according to hackread.com.
The internet prospects 

Presentation on the good and bad of the internet. What it's here to give us and what it takes from us
Celestin_et_al_v_Martelly_et_al__nyedce-18-07340__0158.0 (1).pdf

Celestin_et_al_v_Martelly_et_al__nyedce-18-07340__0158.0 (1).pdf
Два федеральных агента, которые вели дело Silk Road, обвиняются в краже битко...

Два федеральных агента, которые вели дело Silk Road, обвиняются в краже биткоинов
White collar crime by waseem i. khan

Waseem I. Khan
Assistant Professor, Shri Shivaji Law College, Parbhani, Maharashtra, India
Defendants google, microsoft and yahoo bring their own judge

When becoming defendants in the Marshall Islands with overwhelming evidence for torts, corporations GOOGLE, MICROSOFT, YAHOO et al elected to make sure they got off the hook: they brought their own bribed judge to "work" with their own unauthorized attorneys to defeat due course of law. Are these mega corporations above the law?
Madhavi Vuppalapati and Prithvi Information Solutions Involved in Million Fraud

Plot: Madhavi Vuppalapati’s company Prithvi Information Solutions and all its affiliates had created fictitious, counterfeit customers to get an advance payment of $17 million from Kyko Global Inc.
Torts, Crimes and BusinessChapter 7 & 8Intent vs.docx

Torts, Crimes and Business
Chapter 7 & 8
Intent vs. AccidentIntent: b. The state of mind with which an act is done. 2a: clearly formulated or planned intention.Accident: 1a: an event occurring by chance or arising from unknown cause. b. Lack of intention or necessity. c: an unexpected happening causing loss or injury which is not due to any fault or misconduct on the part of the person injured but from the consequences of which he may be entitled to some legal relief. Webster’s New Collegiate Dictionary
Intent DefinedMens rea: A guilty mind. The mental state accompanying a forbidden act. For an act to constitute a criminal offense, the act usually must be illegal and accompanied by a requisite mental state.Scienter: Previous knowledge of an operative state of fact. Knowingly or with guilty knowledge. Making false statements intentionally to deceive or with what is recognized as the legal equivalent to a deliberately fraudulent intent to deceive. Blacks Law Dictionary
Tort: Twisted Behavior
“n. from French for "wrong," a civil wrong or wrongful act, whether intentional or accidental, from which injury occurs to another. Torts include all negligence cases as well as intentional wrongs which result in harm.”
http://dictionary.law.com/default2.asp?selected=2137&bold=||||
See Video on Twisted Behavior
Intentional Torts
Intentional torts against personsAssaultBatteryFalse imprisonmentDefamation of characterInvasion of the right to privacyIntentional infliction of emotional distressMalicious prosecution
Intentional torts against propertyTrespass to landTrespass to and conversion of personal property
Trespass
Business TortsEntering certain businesses and professions without a license(Conducting Business with a license)Intentional misrepresentation (fraud)Civil RICO – Racketeering Influenced and Corrupt Organization Act
Elements of Unintentional Torts (Negligence)
To be successful in a negligence lawsuit, the plaintiff must prove:the defendant owed a duty of care to the plaintiffthe defendant breached this duty of carethe plaintiff suffered injurythe defendant’s negligent act caused the plaintiff’s injury
Special Negligence DoctrinesNegligence per seRes ipsa loquiturDram shop actsSocial host liabilityGuest statutesGood Samaritan lawsFireman’s rule“Danger invites rescue” doctrineLiability of common carriers and innkeepersLiability of landowners
Defenses Against NegligenceAssumption of the riskContributory negligenceComparative negligenceSuperseding event
Crimes and Business
Classification of CrimesFelonies – Major offences punishable by jail time from one year - to life sentences. Crimes include arson, burglary, grand theft, murder, rape…
Misdemeanors – Minor offenses that are punishable by confinement up to one year, a fine or both. Misdemeanors include: public intoxication, speeding, vandalism.
Violations – Infractions. Generally in fines only. Examples include disturbing the peace, illegal g ...
Short Answer41) Sally operates a large manufacturing firm near.docx

Short Answer
41) Sally operates a large manufacturing firm near a federal land preserve known for its waterfowl and fauna. The federal government has just filed suit against Sally and her corporation, charging them with criminal violations of various environmental protection statutes. What rights do Sally and her corporation have that are guaranteed under the United States Constitution?
42) John was driving his car in a careless way, failing to drive as a reasonably prudent person would under the driving conditions. Ramona was crossing the street in a careless way, failing to cross as a reasonably prudent person would. John struck and injured Ramona with the car John was driving. At trial, it was determined that John was 80 percent at fault and that Ramona was 20 percent at fault. The injuries sustained amounted to $100,000. Explain how much, if any, recovery Ramona would receive in a state that applies the contributory negligence rule. Do the same thing for a state that applies the comparative negligence rule.
43) Herman Corporation is engaged in preparing a marketing campaign consisting of electronic and print images. Drawings and photographs for the campaign are coming from a variety of sources, including popular magazines, international newspapers, and web sources. The marketing vice president asserts that the company may use the images under the fair use doctrine. What factors should be considered in the application of the fair use doctrine?
44) Louise owned a house next to Robert's house. Robert made a contract with Midcity Painters to paint his house. The painters arrived to paint Robert's house, but mistakenly painted Louise's house. She saw the painters at work and made no comment. Later, Midcity Painters sent Louise a bill for painting her house. She claimed that she was not liable because she had not made any contract with them. Is this a valid defense?
45) Mary offered to sell Mike several pieces of rare Chinese art at a very good price because they were duplicates in her own collection. Mike could not accept the offer at that time, but he did give Mary $500 in return for her promise to keep her offer open for three (3) weeks. Mike returned with the agreed-upon balance two weeks later to find that Mary already had sold the pieces she had offered to sell to him. Mary explained that she had been able to get a better price from another buyer. She offered to return Mike's $500 and insisted that this was all she was obligated to do. Is Mary right?
46) John received a promotion at work and felt new clothes would be necessary in the new position. John went to a local store and charged three ties on his charge account at a cost of $60 each. Bill, a friend of John's, saw a sidewalk vendor selling ties at a cost of three for $10 and bought three at that price. The friends compared purchases that night and found that they had purchased identical ties. John became enraged and said that he would not pay the charge-account bill because the t.
New Kmart Data Breach lawsuit spotlights PCI DSS

Posted as a courtesy by:
Dave Sweigert
CISA, CISSP, HCISPP, PMP, SEC+
Similar to Edva horng 0 (20)
Of all the forms of finance finance crimes discussed, which do you c.pdf

Of all the forms of finance finance crimes discussed, which do you c.pdf
Citizenfour producers-face-legal-challenges-over-edward-snowden-leaks

Citizenfour producers-face-legal-challenges-over-edward-snowden-leaks
Citizenfour producers-face-legal-challenges-over-edward-snowden-leaks

Citizenfour producers-face-legal-challenges-over-edward-snowden-leaks
Dossier diaspora 1,50 $ Gov.uscourts.nyed.427196.1.0

Dossier diaspora 1,50 $ Gov.uscourts.nyed.427196.1.0
Celestin_et_al_v_Martelly_et_al__nyedce-18-07340__0158.0 (1).pdf

Celestin_et_al_v_Martelly_et_al__nyedce-18-07340__0158.0 (1).pdf
Два федеральных агента, которые вели дело Silk Road, обвиняются в краже битко...

Два федеральных агента, которые вели дело Silk Road, обвиняются в краже битко...
Defendants google, microsoft and yahoo bring their own judge

Defendants google, microsoft and yahoo bring their own judge
Madhavi Vuppalapati and Prithvi Information Solutions Involved in Million Fraud

Madhavi Vuppalapati and Prithvi Information Solutions Involved in Million Fraud
Torts, Crimes and BusinessChapter 7 & 8Intent vs.docx

Torts, Crimes and BusinessChapter 7 & 8Intent vs.docx
Short Answer41) Sally operates a large manufacturing firm near.docx

Short Answer41) Sally operates a large manufacturing firm near.docx
More from fadliwiryawirawan
KEAMANAN WEBISTE 

SECURE LINE BUAT KALIAN ,
KEAMANAN JARINGAN BANYAK SEKALINYA JENISNYA ANTIVIRUS ,
membuat viruses melawan dengan viruses
Australia professional-membership-application frm-eng_0720

download here ISACA ,
isikan form karena dapat foundation free , ini masih sisa waktu kok sampai 2021 , hanya memiliki vissa platinum ,
dan sebagainya ,
kontak fadliwirya@webnull.com & friendly melindagates@foundations.org/
Gov belgium id

indonesia bekerjasama dengan bebearapa negara dari berbagai economic , 2020 , 2021 mendatang
More from fadliwiryawirawan (10)
Australia professional-membership-application frm-eng_0720

Australia professional-membership-application frm-eng_0720
Recently uploaded
Media as a Mind Controlling Strategy In Old and Modern Era

This presentation, created by Syed Faiz ul Hassan, explores the profound influence of media on public perception and behavior. It delves into the evolution of media from oral traditions to modern digital and social media platforms. Key topics include the role of media in information propagation, socialization, crisis awareness, globalization, and education. The presentation also examines media influence through agenda setting, propaganda, and manipulative techniques used by advertisers and marketers. Furthermore, it highlights the impact of surveillance enabled by media technologies on personal behavior and preferences. Through this comprehensive overview, the presentation aims to shed light on how media shapes collective consciousness and public opinion.
Supercharge your AI - SSP Industry Breakout Session 2024-v2_1.pdf

During the May 2024 SSP Conference in Boston, MA, Margie Hlava gave this presentation during the Industry Breakout Session on May 29, 2024.
María Carolina Martínez - eCommerce Day Colombia 2024

María Carolina Martínez - eCommerce Day Colombia 2024
AWANG ANIQKMALBIN AWANG TAJUDIN B22080004 ASSIGNMENT 2 MPU3193 PHILOSOPHY AND...

National education philosophy ( N.E.P)
Presentatie 8. Joost van der Linde & Daniel Anderton - Eliq 28 mei 2024

Dutch Power Event
“AI – Navigeren naar de toekomst?”
Op 28 mei 2024 bij Info Support.
Collapsing Narratives: Exploring Non-Linearity • a micro report by Rosie Wells

Insight: In a landscape where traditional narrative structures are giving way to fragmented and non-linear forms of storytelling, there lies immense potential for creativity and exploration.
'Collapsing Narratives: Exploring Non-Linearity' is a micro report from Rosie Wells.
Rosie Wells is an Arts & Cultural Strategist uniquely positioned at the intersection of grassroots and mainstream storytelling.
Their work is focused on developing meaningful and lasting connections that can drive social change.
Please download this presentation to enjoy the hyperlinks!
2024-05-30_meetup_devops_aix-marseille.pdf

Slides de notre meetup DevOps AixMarseille du 30 mai 2024 chez SmarTribune
Sujets: platform engineering / terragrunt / test containers
Tom tresser burning issue.pptx My Burning issue

Addressing the status of black home ownership in America. and what actions are taken to impact these trends.
somanykidsbutsofewfathers-140705000023-phpapp02.pptx

Reminiscing on my Father and what he meant in my life, and regretting that so many children suffer and have no family in their home or lives...
Presentatie 4. Jochen Cremer - TU Delft 28 mei 2024

Dutch Power Event
“AI – Navigeren naar de toekomst?”
Op 28 mei 2024 bij Info Support.
Obesity causes and management and associated medical conditions

Obesity causes and management and associated medical conditionsFaculty of Medicine And Health Sciences
Causes and management of obesity and associated medical conditions Doctoral Symposium at the 17th IEEE International Conference on Software Test...

Doctoral Symposium at the 17th IEEE International Conference on Software Test...Sebastiano Panichella
Doctoral Symposium at the
17th IEEE International Conference on Software Testing, Verification and Validation
(ICST 2024)Mastering the Concepts Tested in the Databricks Certified Data Engineer Assoc...

• For a full set of 760+ questions. Go to
https://skillcertpro.com/product/databricks-certified-data-engineer-associate-exam-questions/
• SkillCertPro offers detailed explanations to each question which helps to understand the concepts better.
• It is recommended to score above 85% in SkillCertPro exams before attempting a real exam.
• SkillCertPro updates exam questions every 2 weeks.
• You will get life time access and life time free updates
• SkillCertPro assures 100% pass guarantee in first attempt.
Announcement of 18th IEEE International Conference on Software Testing, Verif...

Announcement of 18th IEEE International Conference on Software Testing, Verif...Sebastiano Panichella
Announcement of 18th IEEE International Conference on Software Testing, Verification and Validation (ICST) 2025, Napoli, ItalyInternational Workshop on Artificial Intelligence in Software Testing

International Workshop on Artificial Intelligence in
Software Testing
Recently uploaded (19)
Media as a Mind Controlling Strategy In Old and Modern Era

Media as a Mind Controlling Strategy In Old and Modern Era
Supercharge your AI - SSP Industry Breakout Session 2024-v2_1.pdf

Supercharge your AI - SSP Industry Breakout Session 2024-v2_1.pdf
María Carolina Martínez - eCommerce Day Colombia 2024

María Carolina Martínez - eCommerce Day Colombia 2024
AWANG ANIQKMALBIN AWANG TAJUDIN B22080004 ASSIGNMENT 2 MPU3193 PHILOSOPHY AND...

AWANG ANIQKMALBIN AWANG TAJUDIN B22080004 ASSIGNMENT 2 MPU3193 PHILOSOPHY AND...
Presentatie 8. Joost van der Linde & Daniel Anderton - Eliq 28 mei 2024

Presentatie 8. Joost van der Linde & Daniel Anderton - Eliq 28 mei 2024
Collapsing Narratives: Exploring Non-Linearity • a micro report by Rosie Wells

Collapsing Narratives: Exploring Non-Linearity • a micro report by Rosie Wells
somanykidsbutsofewfathers-140705000023-phpapp02.pptx

somanykidsbutsofewfathers-140705000023-phpapp02.pptx
Presentatie 4. Jochen Cremer - TU Delft 28 mei 2024

Presentatie 4. Jochen Cremer - TU Delft 28 mei 2024
Obesity causes and management and associated medical conditions

Obesity causes and management and associated medical conditions
Doctoral Symposium at the 17th IEEE International Conference on Software Test...

Doctoral Symposium at the 17th IEEE International Conference on Software Test...
Mastering the Concepts Tested in the Databricks Certified Data Engineer Assoc...

Mastering the Concepts Tested in the Databricks Certified Data Engineer Assoc...
Announcement of 18th IEEE International Conference on Software Testing, Verif...

Announcement of 18th IEEE International Conference on Software Testing, Verif...
International Workshop on Artificial Intelligence in Software Testing

International Workshop on Artificial Intelligence in Software Testing
Edva horng 0
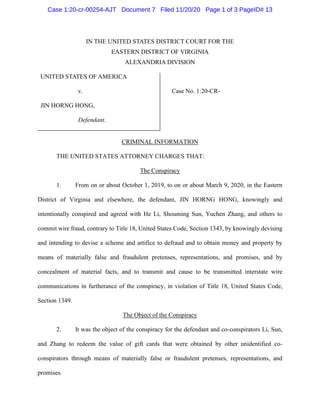
- 1. Case 1:20-cr-00254-AJT Document 7 Filed 11/20/20 Page 1 of 3 PageID# 13 IN THE UNITED STATES DISTRICT COURT FOR THE EASTERN DISTRICT OF VIRGINIA ALEXANDRIA DIVISION UNITED STATES OF AMERICA v. Case No. 1:20-CR- JIN HORNG HONG, Defendant. CRIMINAL INFORMATION THE UNITED STATES ATTORNEY CHARGES THAT: The Conspiracy 1. From on or about October 1, 2019, to on or about March 9, 2020, in the Eastern District of Virginia and elsewhere, the defendant, JIN HORNG HONG, knowingly and intentionally conspired and agreed with He Li, Shouming Sun, Yuchen Zhang, and others to commit wire fraud, contrary to Title 18, United States Code, Section 1343, by knowingly devising and intending to devise a scheme and artifice to defraud and to obtain money and property by means of materially false and fraudulent pretenses, representations, and promises, and by concealment of material facts, and to transmit and cause to be transmitted interstate wire communications in furtherance of the conspiracy, in violation of Title 18, United States Code, Section 1349. The Object of the Conspiracy 2. It was the object of the conspiracy for the defendant and co-conspirators Li, Sun, and Zhang to redeem the value of gift cards that were obtained by other unidentified co- conspirators through means of materially false or fraudulent pretenses, representations, and promises.
- 2. Case 1:20-cr-00254-AJT Document 7 Filed 11/20/20 Page 2 of 3 PageID# 14 Manner and Means of the Conspiracy 3. In order to effect the object of the conspiracy, the defendant and his co-conspirators engaged in the following conduct in the Eastern District of Virginia and elsewhere: a. Unidentified co-conspirators contacted victims by telephone or through social media. b. Unidentified co-conspirators assumed fictitious identities, including falsely claiming to be from the Internal Revenue Service, the Social Security Administration, or employees of businesses or financial institutions known to the victims, and, among others ruses, falsely told victims they were entitled to grants or refunds, or in some cases had their personal identification information compromised. In other cases, unidentified co-conspirators developed on-line relationships with victims as a means to commit the fraud and effect the object of the conspiracy. c. Based on false representations, unidentified co-conspirators fraudulently induced more than 500 victims to purchase gift cards, including gift cards to be redeemed at Walmart and Sam’s Club stores. d. Unidentified co-conspirators then directed the victims to send to members of the conspiracy through wire communications the gift cards’ redemption codes, which are codes used to redeem the value of the gift cards without having the physical cards. e. Defendant HONG and co-conspirators Li, Sun, and Zhang were provided the redemption codes and used the redemption codes obtained by fraud to purchase goods and services for their personal benefit and the benefit of their co-conspirators primarily at Walmart and Sam’s Club locations. These transactions occurred in the Eastern District of Virginia and elsewhere and each transaction transmitted and caused to be transmitted interstate wire
- 3. Case 1:20-cr-00254-AJT Document 7 Filed 11/20/20 Page 3 of 3 PageID# 15 communications in furtherance of the conspiracy. In violation of Title 18, United States Code, Section 1349. Respectfully submitted, G. Zachary Terwilliger United States Attorney By: /s/ William Fitzpatrick Assistant United States Attorney, Viviana Vasiu Special Assistant United States Attorney Date: October 23, 2020