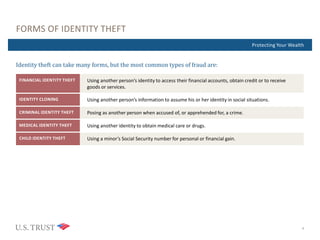
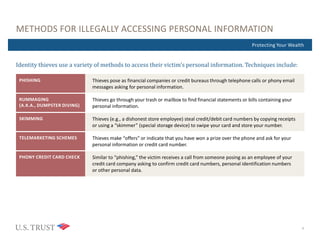
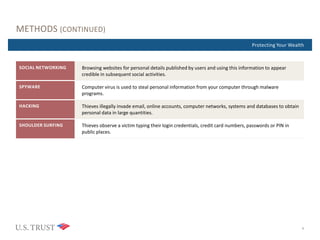
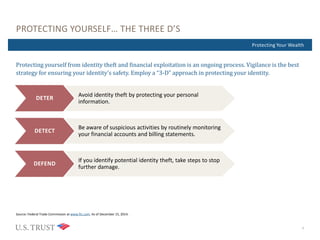
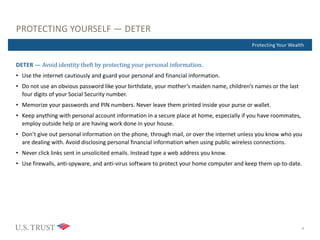
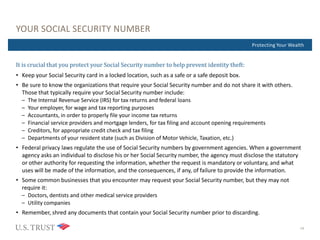
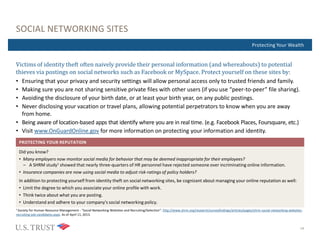
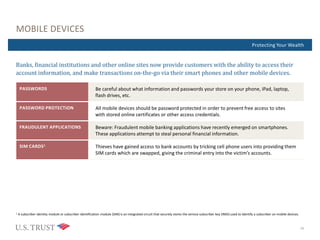
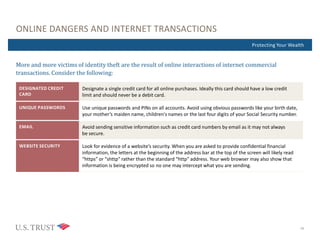
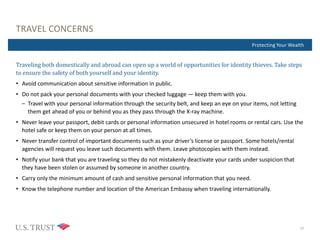
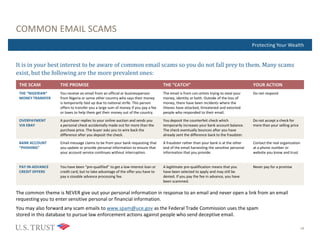
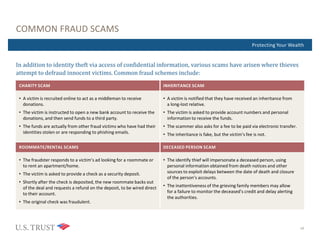
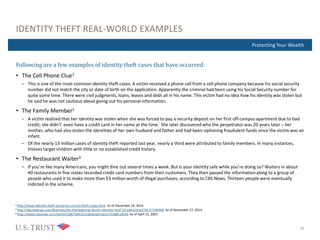
This document provides information on identity theft and how to protect yourself. It discusses common forms of identity theft, methods thieves use to access personal information, and a three step approach ("Deter, Detect, Defend") to protection. Readers are advised to protect passwords and documents with personal data, monitor accounts, and take steps like filing police reports if identity theft is suspected.