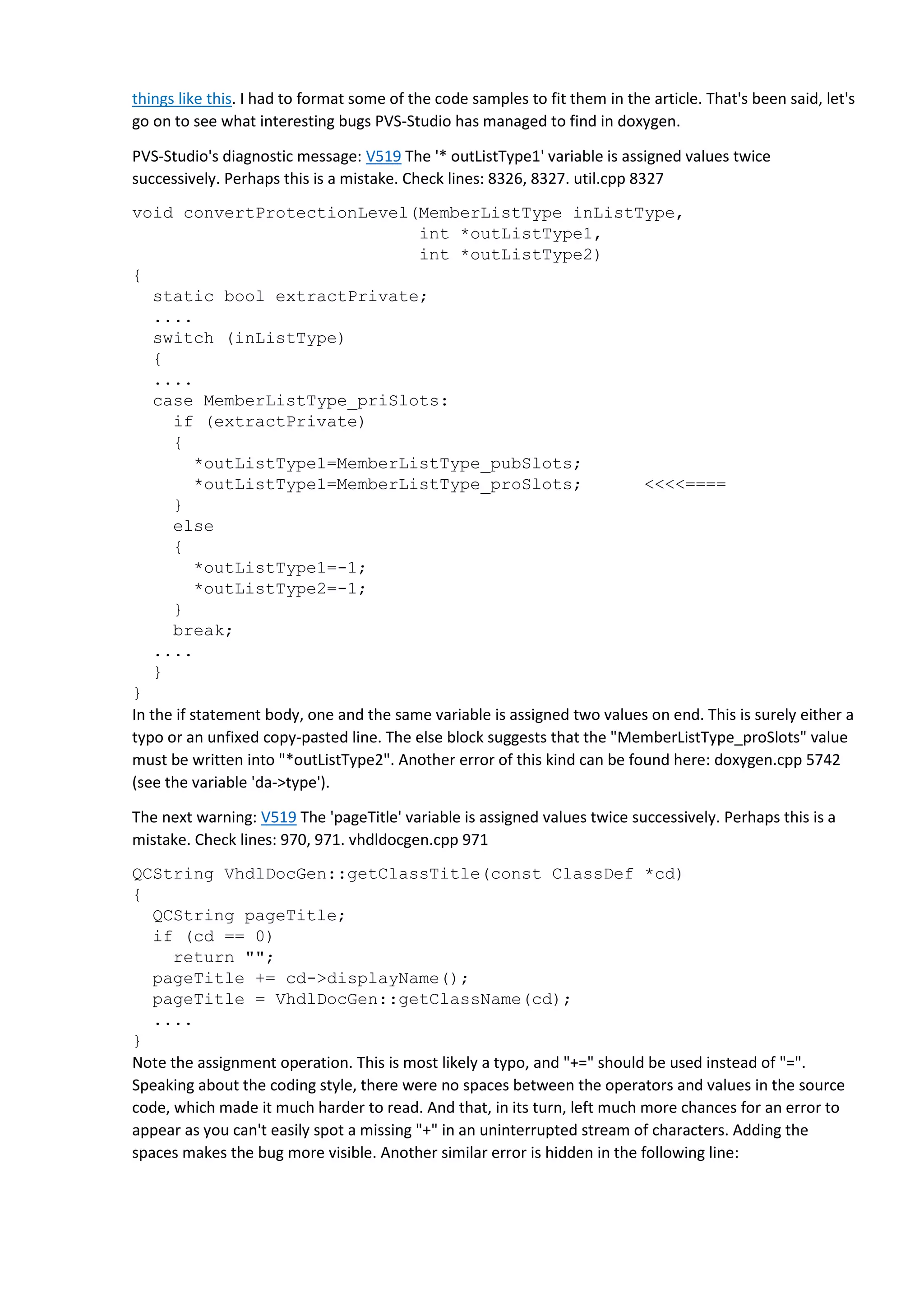
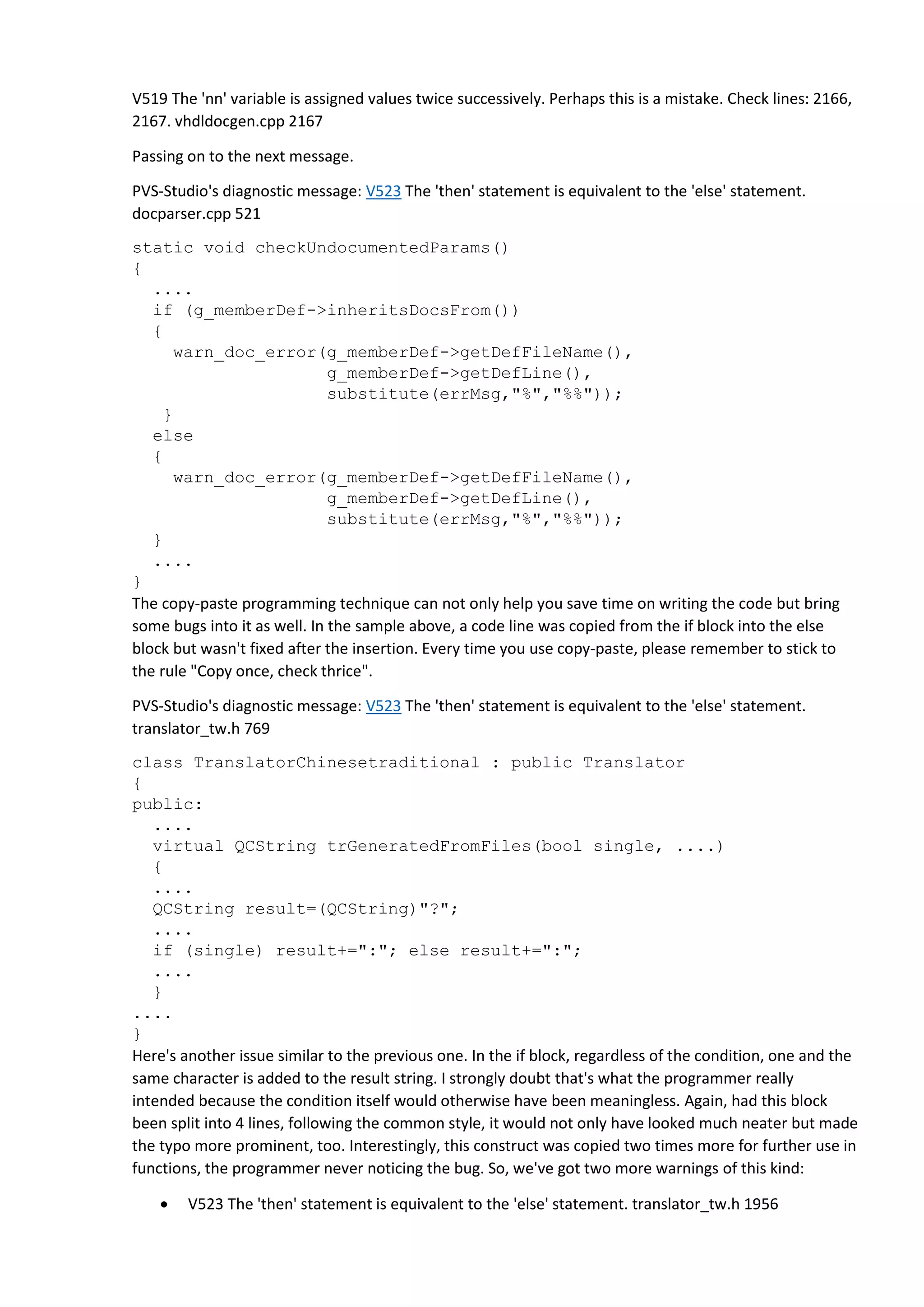
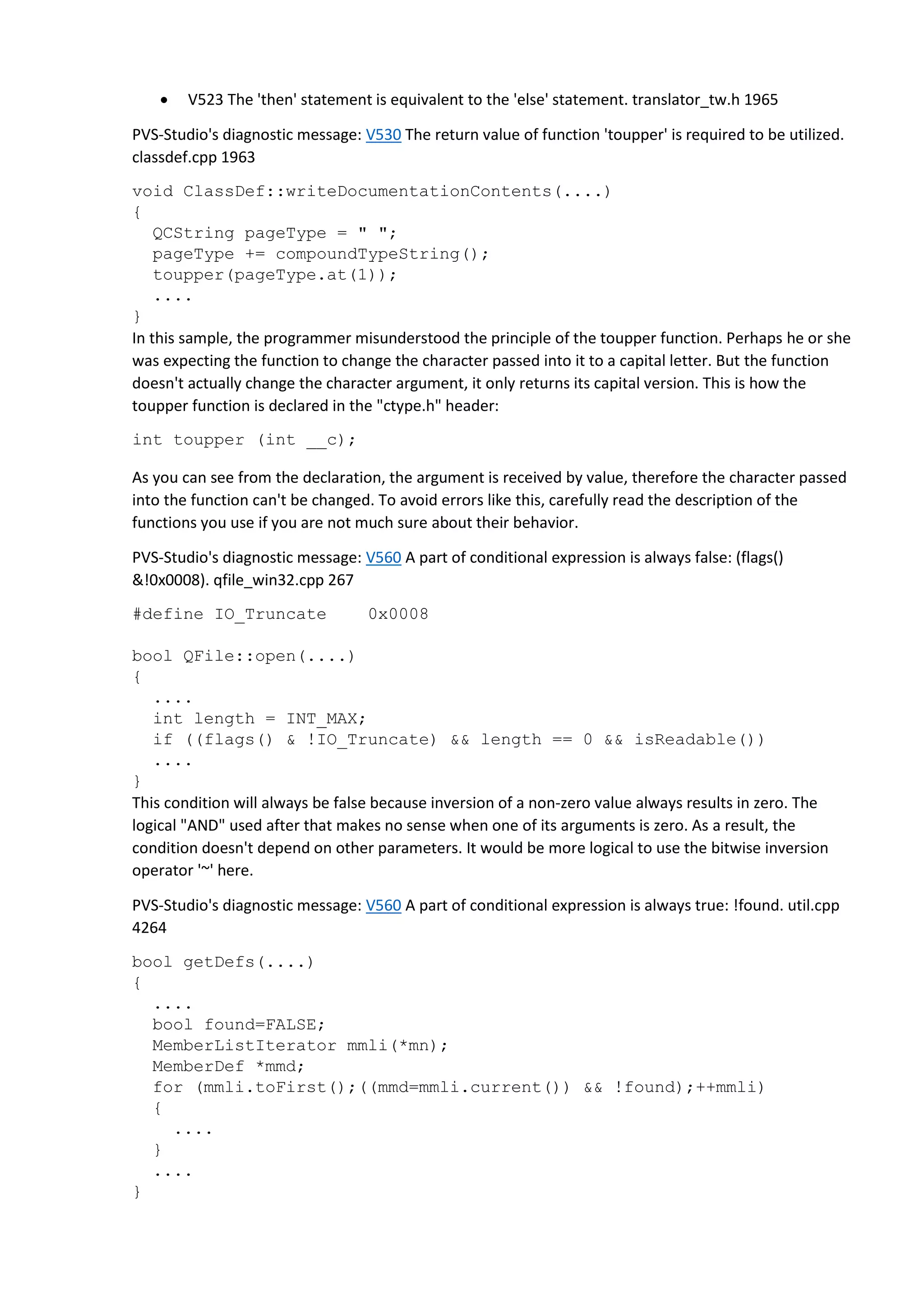
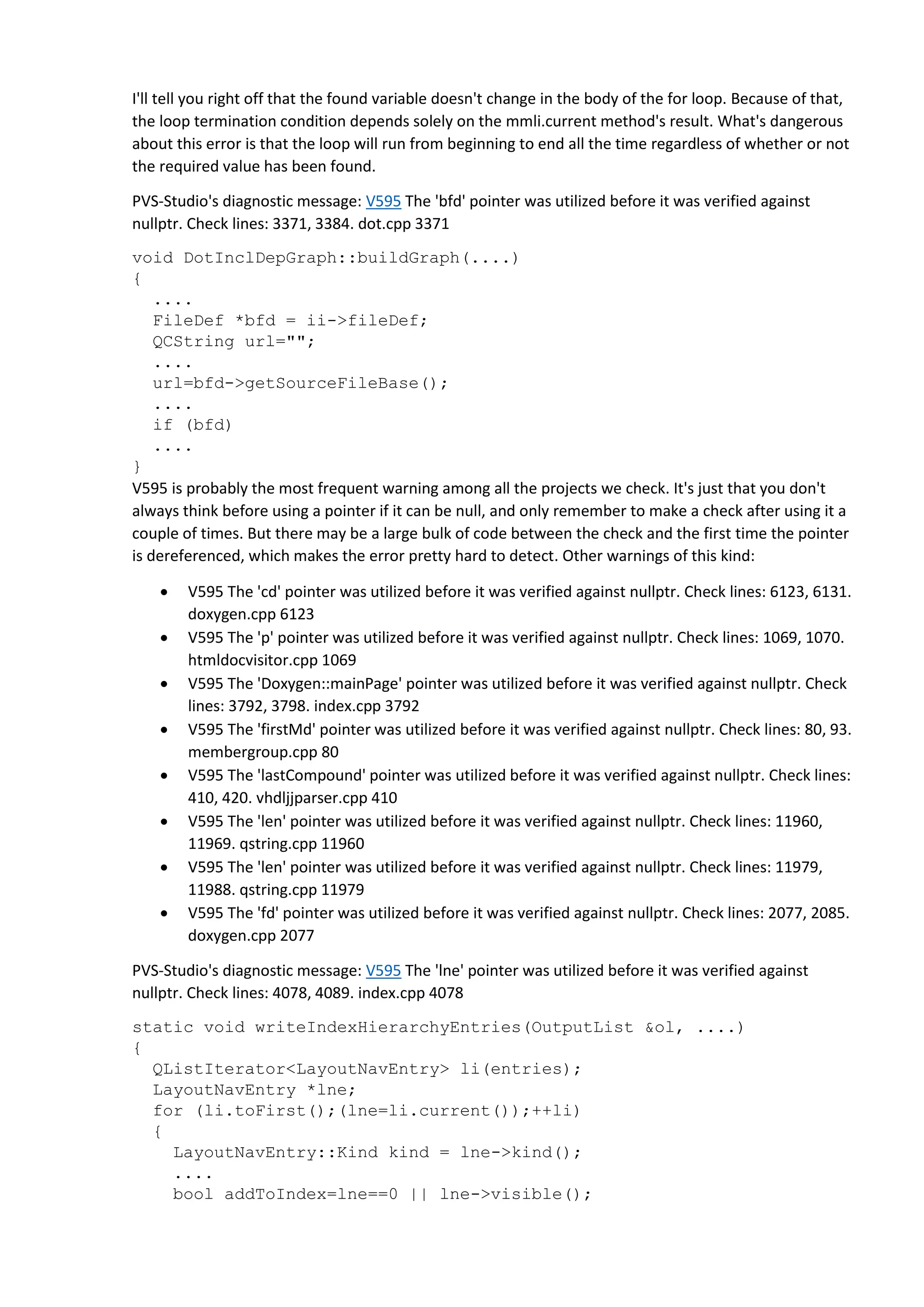
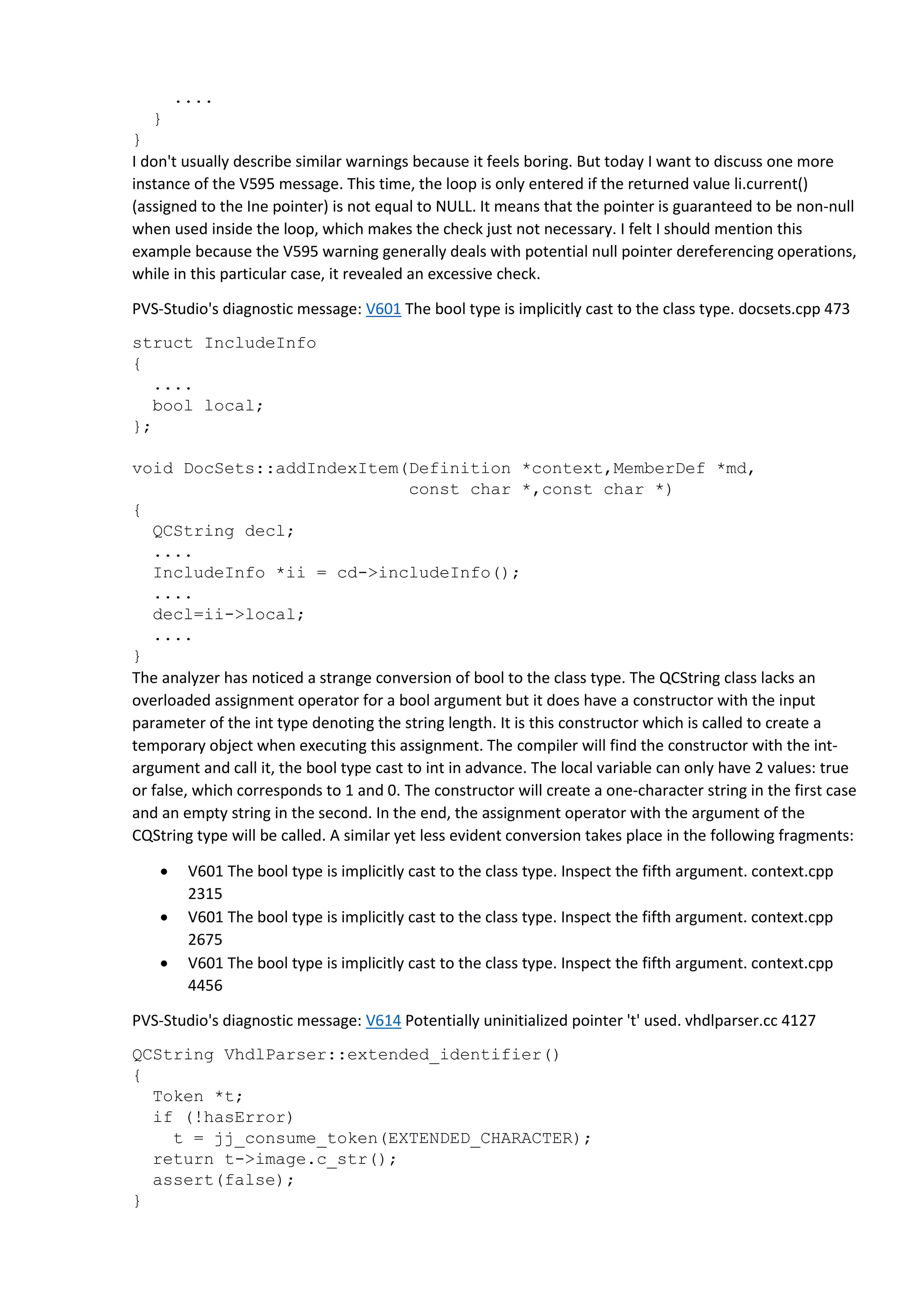
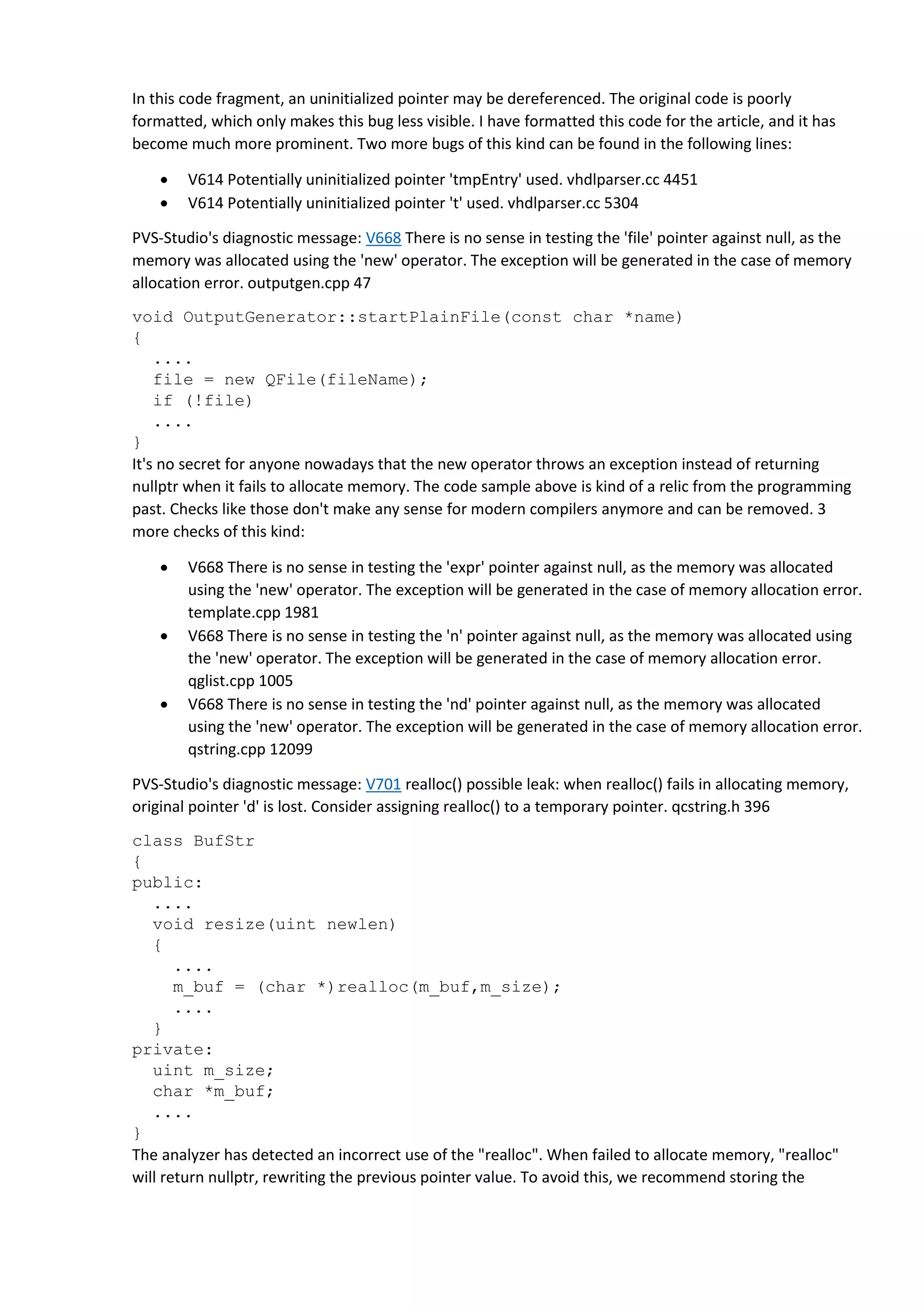
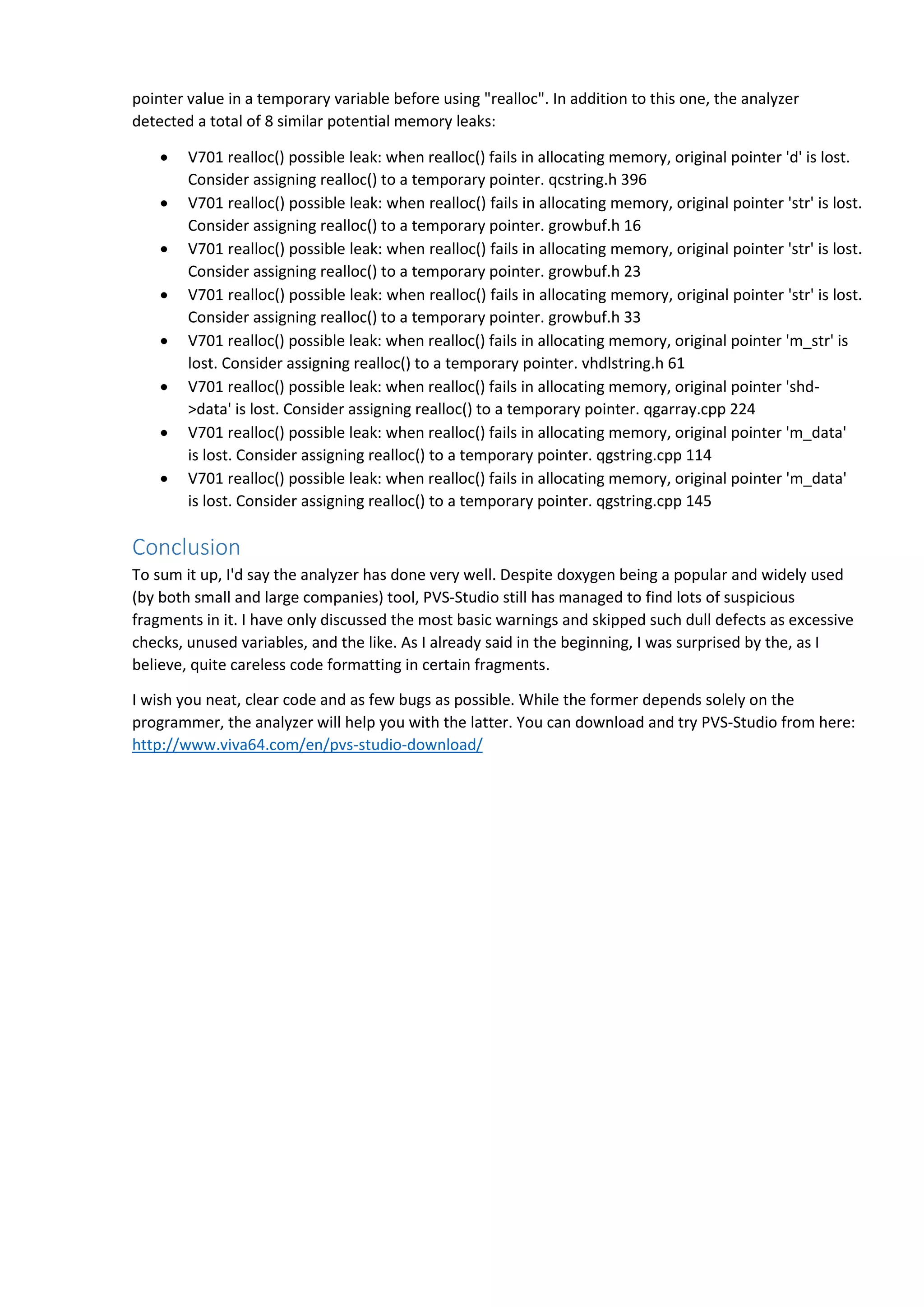
The article discusses a static analysis of the Doxygen documentation generator tool, highlighting various coding errors identified by PVS-Studio, including improper variable assignments, redundant conditions, and potential null pointer dereferences. It emphasizes the importance of code readability and correct coding practices to avoid bugs. The findings suggest that even widely used tools like Doxygen can benefit from enhanced code scrutiny and formatting.