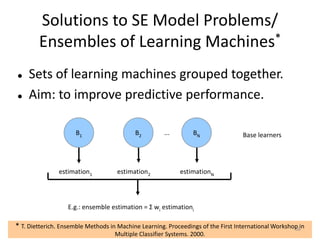
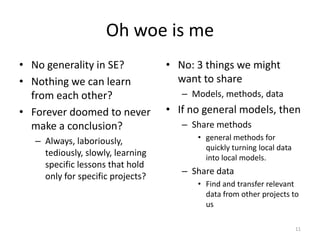
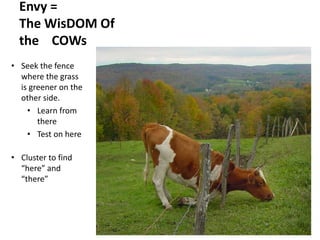
This document summarizes a talk on data science for software engineering. It discusses how data science involves various fields like statistics, machine learning, and data mining. It notes that while "big data" is often discussed, software engineering data is typically small and sparse. Domain knowledge is important for data mining to avoid misinterpreting data. Data science with software engineering data requires understanding organizations and their willingness to share data given privacy concerns. The document outlines sharing data, models, and methods for learning across different organizations and discusses techniques for balancing privacy and utility when sharing data.




















































![Fastmap
56
Fastmap: Faloutsos [1995]
O(2N) generation of axis of large variability
• Pick any point W;
• Find X furthest from W,
• Find Y furthest from Y.
c = dist(X,Y)
All points have distance a,b to (X,Y)
• x = (a2 + c2 − b2)/2c
• y= sqrt(a2 – x2)
Find median(x), median(y)
Recurse on four quadrants](https://image.slidesharecdn.com/dm-sei-tutorial-v7-130815110501-phpapp02/85/Dm-sei-tutorial-v7-57-320.jpg)




![Q: How to learn rules from
neighboring clusters
• A: it doesn’t really matter
– Many competent rule learners
• But to evaluate global vs local rules:
– Use the same rule learner for local vs global rule learning
• This study uses WHICH (Menzies [2010])
– Customizable scoring operator
– Faster termination
– Generates very small rules (good for explanation)
62](https://image.slidesharecdn.com/dm-sei-tutorial-v7-130815110501-phpapp02/85/Dm-sei-tutorial-v7-63-320.jpg)