Discovery and investigation
•Download as PPTX, PDF•
0 likes•197 views
This document discusses various methods used in archaeological research, including desk-based research of existing records, maps, and photographs; aerial photography; field walking; field work such as landscape and building surveys; geophysical prospection techniques like resistivity and magnetometry; and geochemical analysis. It provides examples of the types of documents that may be used in desk-based research, such as maps from 1792 and 1840, as well as paintings and photographs. The document also presents a case study of a tileworks that previously occupied the site of some houses in Strathbungo in the late 1850s, explaining how brick fragments are still found in gardens today from this former industrial site.
Report
Share
Report
Share
Recommended
From Bad to Worse: How to Stay Protected from a Mega Data Breach

Data breaches are hitting the news now more than ever before and the trend is getting nothing but worse. View our presentation to learn how deep a breach can go, common misconceptions and best practice solutions to keep your SAP-based business protected.
ZEYTİNBURNU DEMİRDÖKÜM KOMBİ SERVİSİ_0212 472 72 23_0541 872 72 23

ZEYTİNBURNU DEMİRDÖKÜM KOMBİ SERVİSİ_0212 472 72 23_0541 872 72 23ZEYTİNBURNU DEMİRDÖKÜM KOMBİ SERVİSİ_0212 472 72 23_0541 872 72 23
Recommended
From Bad to Worse: How to Stay Protected from a Mega Data Breach

Data breaches are hitting the news now more than ever before and the trend is getting nothing but worse. View our presentation to learn how deep a breach can go, common misconceptions and best practice solutions to keep your SAP-based business protected.
ZEYTİNBURNU DEMİRDÖKÜM KOMBİ SERVİSİ_0212 472 72 23_0541 872 72 23

ZEYTİNBURNU DEMİRDÖKÜM KOMBİ SERVİSİ_0212 472 72 23_0541 872 72 23ZEYTİNBURNU DEMİRDÖKÜM KOMBİ SERVİSİ_0212 472 72 23_0541 872 72 23
Ancient Egyptian Materials And Technology

Professional Writing Service
http://StudyHub.vip/Ancient-Egyptian-Materials-And-Technolo 👈
Timberlake y craddock_45-1-2013

Prehistoric Metal Mining in Britain: The Study of Cobble Stone Mining Tools Based on Artefact Study, Ethnography and Experimentation
Minería Prehistórica en Gran Bretaña: El Estudio de Herramientas Mineras Líticas a Partir de Estudios Artefactuales, Etnografía y Experimentación 33
Simon Timberlake and Brenda Craddock
Chronology of the Great Pyramid.pdf

The Great Pyramid is a book in stone, a book in which knowledge of mathematics, knowledge of architecture and knowledge of astronomy are stored. This is the knowledge of the Pyramid about our physical world and it is told in the first part of this book. The Great Pyramid also tells the history of human time and human spiritual life, because in the measures of the Pyramid it leaves coded testimonies about biblical events, biblical codes and about the end of time of the Earth in the days of the transformation of this world into a higher existential level between 2035-2070 AD. In the second part of this book, Pyramid's story about our spiritual world is told. The book is intended for a wide readership, especially lovers of mysticism and esotericism, Freemasons, architects and students.
Vertical ground: making geology graham icus 2016

Key note presentation at the Island Cities and Urban Archipelagos 2016. 07-12 March 2016, Hong Kong, University of Hong Kong
See http://www.islandcities.org/icua2016.html
Archaeology of the East Midlands: Class 3. Radcliffe Autumn 2014

Archaeology of the East Midlands: Class 3. Radcliffe Autumn 2014
An Archaeology of the East Midlands. Class 6 Radcliffe, Autumn 2014

An Archaeology of the East Midlands. Class 6 Radcliffe, Autumn 2014
Transbay Terminal Archaeology

At the October 2009 AC Transit Transbay Taskforce meeting, attendees were treated to a great historical presentation. Heather Price from William Self Associates presented facts and findings from the excavation process related to the construction of San Francisco's Temporary Transbay Terminal. She was followed with a presentation by Joyce Oishi on the salvage and historical preservation efforts within the existing Transbay Terminal.
Several smaller items salvaged from the Terminal will be on display in an interpretive exhibit at the new Transbay Transit Center (not the Temporary Terminal), while larger items not taken by local museums will be properly recycled.
More Related Content
Viewers also liked
Viewers also liked (10)
To rs & new advertisment consultancy environment tourism projects

To rs & new advertisment consultancy environment tourism projects
Similar to Discovery and investigation
Ancient Egyptian Materials And Technology

Professional Writing Service
http://StudyHub.vip/Ancient-Egyptian-Materials-And-Technolo 👈
Timberlake y craddock_45-1-2013

Prehistoric Metal Mining in Britain: The Study of Cobble Stone Mining Tools Based on Artefact Study, Ethnography and Experimentation
Minería Prehistórica en Gran Bretaña: El Estudio de Herramientas Mineras Líticas a Partir de Estudios Artefactuales, Etnografía y Experimentación 33
Simon Timberlake and Brenda Craddock
Chronology of the Great Pyramid.pdf

The Great Pyramid is a book in stone, a book in which knowledge of mathematics, knowledge of architecture and knowledge of astronomy are stored. This is the knowledge of the Pyramid about our physical world and it is told in the first part of this book. The Great Pyramid also tells the history of human time and human spiritual life, because in the measures of the Pyramid it leaves coded testimonies about biblical events, biblical codes and about the end of time of the Earth in the days of the transformation of this world into a higher existential level between 2035-2070 AD. In the second part of this book, Pyramid's story about our spiritual world is told. The book is intended for a wide readership, especially lovers of mysticism and esotericism, Freemasons, architects and students.
Vertical ground: making geology graham icus 2016

Key note presentation at the Island Cities and Urban Archipelagos 2016. 07-12 March 2016, Hong Kong, University of Hong Kong
See http://www.islandcities.org/icua2016.html
Archaeology of the East Midlands: Class 3. Radcliffe Autumn 2014

Archaeology of the East Midlands: Class 3. Radcliffe Autumn 2014
An Archaeology of the East Midlands. Class 6 Radcliffe, Autumn 2014

An Archaeology of the East Midlands. Class 6 Radcliffe, Autumn 2014
Transbay Terminal Archaeology

At the October 2009 AC Transit Transbay Taskforce meeting, attendees were treated to a great historical presentation. Heather Price from William Self Associates presented facts and findings from the excavation process related to the construction of San Francisco's Temporary Transbay Terminal. She was followed with a presentation by Joyce Oishi on the salvage and historical preservation efforts within the existing Transbay Terminal.
Several smaller items salvaged from the Terminal will be on display in an interpretive exhibit at the new Transbay Transit Center (not the Temporary Terminal), while larger items not taken by local museums will be properly recycled.
An Archaeology of the East Midlands Class 8. Radcliffe Autumn 2014

An Archaeology of the East Midlands Class 8. Radcliffe Autumn 2014
Detailed Slope Stability Analysis and Assessment of the Original Carsington E...

A 1225 m long, 35 m high zone earth filled embankment was being constructed from 1981 to 1984 from a British Regional Water Authority to regulate flows in the River Derwent in England. The Carsington Dam was planned to be one of the largest earth filled dams in Britain. Its reservoir capacity was 35 million m3 and the watertight element was Rolled Clay Core with an upstream extension of boot shaped and shoulders of compacted mudstone with horizontal drainage layers of crushed limestone about 4 metres apart and a cut-off grout curtain (Davey and Eccles, 1983).
The downstream slope was 1:2.5 and the upstream slope 1:3. Fill placing began in May 1982 and took three summers, with winter shutdowns. In August 1983 a small berm was placed at the upstream toe to compensate for a faster rate of construction. Earth filling restarted in April 1984 and was one metre below the final crest level on 4 June 1984 when the upstream slope slipped (Skempton, 1985). Observations of pore pressure and settlement were made during construction at four sections and horizontal displacements were observed from August 1983. The Carsington Dam was almost completed on 1984.
However, at the beginning of June 1984, a 400-m length of the upstream shoulder of the embankment dam slipped some 11 m and failed. At the time of the failure, embankment construction was virtually complete with the dam approaching its maximum height of 35 m. Horizontal drainage blankets were incorporated in both the upstream and the downstream shale fill shoulders. Piezometers had been installed and pore pressures were being monitored in the foundation, in the clay core, and in the shoulder fill. The failure surface passed through the boot shaped rolled clay core and a relatively thin layer of surface clay in the foundation of the dam. Investigation of the events at Carsington has made important contributions to the fundamental understanding of the behaviour of large earthworks of this type (Vaughan et al., 1989; Dounias et al., 1996).
The objective of this research is to evaluate a detailed slope stability assessment of the Carsington Earth Embankment Dam in the UK used to retain mine tailings.
By using and applying advanced geotechnical engineering analysis tools and modelling techniques the Carsington Earth Embankment Dam, which is considered a particular geotechnical structure, is analysed.
In the current detailed slope stability analyses the total and effective stress state soil properties / parameters were used, and the most critical slip circle centre according to Fellenius - Jumikis method was initially determined. Subsequently, the Carsington Earth Embankment Dam and its foundation was analysed and examined against failure by slope instability. Considerations of loading conditions which may result to instability for all likely combinations of reservoir and tailwater levels, seepage conditions, both after and during construction were made, and hence three construction and / or loading condit
A Short History Of Engineering Geology And Geophysics At The British Geologic...

Academic Paper Writing Service
http://StudyHub.vip/A-Short-History-Of-Engineering-Geology- 👈
Similar to Discovery and investigation (20)
Archaeology of the East Midlands: Class 3. Radcliffe Autumn 2014

Archaeology of the East Midlands: Class 3. Radcliffe Autumn 2014
An Archaeology of the East Midlands. Class 6 Radcliffe, Autumn 2014

An Archaeology of the East Midlands. Class 6 Radcliffe, Autumn 2014
An Archaeology of the East Midlands Class 8. Radcliffe Autumn 2014

An Archaeology of the East Midlands Class 8. Radcliffe Autumn 2014
Detailed Slope Stability Analysis and Assessment of the Original Carsington E...

Detailed Slope Stability Analysis and Assessment of the Original Carsington E...
A Short History Of Engineering Geology And Geophysics At The British Geologic...

A Short History Of Engineering Geology And Geophysics At The British Geologic...
More from Hutchesons' Grammar School
Sustainable development

Set of slides intended to stimulate discussion on sustainability; for use with S1 ( Key Stage 3) pupils.
More from Hutchesons' Grammar School (20)
Introduction: some key thinkers in 20th Anthropology

Introduction: some key thinkers in 20th Anthropology
Recently uploaded
LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...

Do you want to learn how to model and simulate an electrical network from scratch in under an hour?
Then welcome to this PowSyBl workshop, hosted by Rte, the French Transmission System Operator (TSO)!
During the webinar, you will discover the PowSyBl ecosystem as well as handle and study an electrical network through an interactive Python notebook.
PowSyBl is an open source project hosted by LF Energy, which offers a comprehensive set of features for electrical grid modelling and simulation. Among other advanced features, PowSyBl provides:
- A fully editable and extendable library for grid component modelling;
- Visualization tools to display your network;
- Grid simulation tools, such as power flows, security analyses (with or without remedial actions) and sensitivity analyses;
The framework is mostly written in Java, with a Python binding so that Python developers can access PowSyBl functionalities as well.
What you will learn during the webinar:
- For beginners: discover PowSyBl's functionalities through a quick general presentation and the notebook, without needing any expert coding skills;
- For advanced developers: master the skills to efficiently apply PowSyBl functionalities to your real-world scenarios.
Encryption in Microsoft 365 - ExpertsLive Netherlands 2024

In this session I delve into the encryption technology used in Microsoft 365 and Microsoft Purview. Including the concepts of Customer Key and Double Key Encryption.
Assuring Contact Center Experiences for Your Customers With ThousandEyes

Presented by Suzanne Phillips and Alex Marcotte
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

Effective Application Security in Software Delivery lifecycle using Deployment Firewall and DBOM
The modern software delivery process (or the CI/CD process) includes many tools, distributed teams, open-source code, and cloud platforms. Constant focus on speed to release software to market, along with the traditional slow and manual security checks has caused gaps in continuous security as an important piece in the software supply chain. Today organizations feel more susceptible to external and internal cyber threats due to the vast attack surface in their applications supply chain and the lack of end-to-end governance and risk management.
The software team must secure its software delivery process to avoid vulnerability and security breaches. This needs to be achieved with existing tool chains and without extensive rework of the delivery processes. This talk will present strategies and techniques for providing visibility into the true risk of the existing vulnerabilities, preventing the introduction of security issues in the software, resolving vulnerabilities in production environments quickly, and capturing the deployment bill of materials (DBOM).
Speakers:
Bob Boule
Robert Boule is a technology enthusiast with PASSION for technology and making things work along with a knack for helping others understand how things work. He comes with around 20 years of solution engineering experience in application security, software continuous delivery, and SaaS platforms. He is known for his dynamic presentations in CI/CD and application security integrated in software delivery lifecycle.
Gopinath Rebala
Gopinath Rebala is the CTO of OpsMx, where he has overall responsibility for the machine learning and data processing architectures for Secure Software Delivery. Gopi also has a strong connection with our customers, leading design and architecture for strategic implementations. Gopi is a frequent speaker and well-known leader in continuous delivery and integrating security into software delivery.
Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf

91mobiles recently conducted a Smart TV Buyer Insights Survey in which we asked over 3,000 respondents about the TV they own, aspects they look at on a new TV, and their TV buying preferences.
Securing your Kubernetes cluster_ a step-by-step guide to success !

Today, after several years of existence, an extremely active community and an ultra-dynamic ecosystem, Kubernetes has established itself as the de facto standard in container orchestration. Thanks to a wide range of managed services, it has never been so easy to set up a ready-to-use Kubernetes cluster.
However, this ease of use means that the subject of security in Kubernetes is often left for later, or even neglected. This exposes companies to significant risks.
In this talk, I'll show you step-by-step how to secure your Kubernetes cluster for greater peace of mind and reliability.
Designing Great Products: The Power of Design and Leadership by Chief Designe...

Designing Great Products: The Power of Design and Leadership by Chief Designer, Beats by Dr Dre
Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI): pav...

Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI)
Bits & Pixels using AI for Good.........

A whirlwind tour of tech & AI for socio-environmental impact.
Software Delivery At the Speed of AI: Inflectra Invests In AI-Powered Quality

In this insightful webinar, Inflectra explores how artificial intelligence (AI) is transforming software development and testing. Discover how AI-powered tools are revolutionizing every stage of the software development lifecycle (SDLC), from design and prototyping to testing, deployment, and monitoring.
Learn about:
• The Future of Testing: How AI is shifting testing towards verification, analysis, and higher-level skills, while reducing repetitive tasks.
• Test Automation: How AI-powered test case generation, optimization, and self-healing tests are making testing more efficient and effective.
• Visual Testing: Explore the emerging capabilities of AI in visual testing and how it's set to revolutionize UI verification.
• Inflectra's AI Solutions: See demonstrations of Inflectra's cutting-edge AI tools like the ChatGPT plugin and Azure Open AI platform, designed to streamline your testing process.
Whether you're a developer, tester, or QA professional, this webinar will give you valuable insights into how AI is shaping the future of software delivery.
GenAISummit 2024 May 28 Sri Ambati Keynote: AGI Belongs to The Community in O...

“AGI should be open source and in the public domain at the service of humanity and the planet.”
Elevating Tactical DDD Patterns Through Object Calisthenics

After immersing yourself in the blue book and its red counterpart, attending DDD-focused conferences, and applying tactical patterns, you're left with a crucial question: How do I ensure my design is effective? Tactical patterns within Domain-Driven Design (DDD) serve as guiding principles for creating clear and manageable domain models. However, achieving success with these patterns requires additional guidance. Interestingly, we've observed that a set of constraints initially designed for training purposes remarkably aligns with effective pattern implementation, offering a more ‘mechanical’ approach. Let's explore together how Object Calisthenics can elevate the design of your tactical DDD patterns, offering concrete help for those venturing into DDD for the first time!
JMeter webinar - integration with InfluxDB and Grafana

Watch this recorded webinar about real-time monitoring of application performance. See how to integrate Apache JMeter, the open-source leader in performance testing, with InfluxDB, the open-source time-series database, and Grafana, the open-source analytics and visualization application.
In this webinar, we will review the benefits of leveraging InfluxDB and Grafana when executing load tests and demonstrate how these tools are used to visualize performance metrics.
Length: 30 minutes
Session Overview
-------------------------------------------
During this webinar, we will cover the following topics while demonstrating the integrations of JMeter, InfluxDB and Grafana:
- What out-of-the-box solutions are available for real-time monitoring JMeter tests?
- What are the benefits of integrating InfluxDB and Grafana into the load testing stack?
- Which features are provided by Grafana?
- Demonstration of InfluxDB and Grafana using a practice web application
To view the webinar recording, go to:
https://www.rttsweb.com/jmeter-integration-webinar
UiPath Test Automation using UiPath Test Suite series, part 4

Welcome to UiPath Test Automation using UiPath Test Suite series part 4. In this session, we will cover Test Manager overview along with SAP heatmap.
The UiPath Test Manager overview with SAP heatmap webinar offers a concise yet comprehensive exploration of the role of a Test Manager within SAP environments, coupled with the utilization of heatmaps for effective testing strategies.
Participants will gain insights into the responsibilities, challenges, and best practices associated with test management in SAP projects. Additionally, the webinar delves into the significance of heatmaps as a visual aid for identifying testing priorities, areas of risk, and resource allocation within SAP landscapes. Through this session, attendees can expect to enhance their understanding of test management principles while learning practical approaches to optimize testing processes in SAP environments using heatmap visualization techniques
What will you get from this session?
1. Insights into SAP testing best practices
2. Heatmap utilization for testing
3. Optimization of testing processes
4. Demo
Topics covered:
Execution from the test manager
Orchestrator execution result
Defect reporting
SAP heatmap example with demo
Speaker:
Deepak Rai, Automation Practice Lead, Boundaryless Group and UiPath MVP
Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head...

Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head of Product, Amazon Games
Recently uploaded (20)
LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...

LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...
Encryption in Microsoft 365 - ExpertsLive Netherlands 2024

Encryption in Microsoft 365 - ExpertsLive Netherlands 2024
Assuring Contact Center Experiences for Your Customers With ThousandEyes

Assuring Contact Center Experiences for Your Customers With ThousandEyes
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...
Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf

Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf
FIDO Alliance Osaka Seminar: Passkeys and the Road Ahead.pdf

FIDO Alliance Osaka Seminar: Passkeys and the Road Ahead.pdf
Securing your Kubernetes cluster_ a step-by-step guide to success !

Securing your Kubernetes cluster_ a step-by-step guide to success !
Designing Great Products: The Power of Design and Leadership by Chief Designe...

Designing Great Products: The Power of Design and Leadership by Chief Designe...
FIDO Alliance Osaka Seminar: Passkeys at Amazon.pdf

FIDO Alliance Osaka Seminar: Passkeys at Amazon.pdf
Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI): pav...

Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI): pav...
Software Delivery At the Speed of AI: Inflectra Invests In AI-Powered Quality

Software Delivery At the Speed of AI: Inflectra Invests In AI-Powered Quality
GenAISummit 2024 May 28 Sri Ambati Keynote: AGI Belongs to The Community in O...

GenAISummit 2024 May 28 Sri Ambati Keynote: AGI Belongs to The Community in O...
Elevating Tactical DDD Patterns Through Object Calisthenics

Elevating Tactical DDD Patterns Through Object Calisthenics
JMeter webinar - integration with InfluxDB and Grafana

JMeter webinar - integration with InfluxDB and Grafana
UiPath Test Automation using UiPath Test Suite series, part 4

UiPath Test Automation using UiPath Test Suite series, part 4
Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head...

Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head...
Discovery and investigation
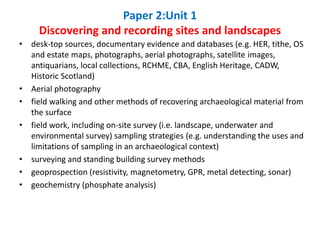
- 1. • desk-top sources, documentary evidence and databases (e.g. HER, tithe, OS and estate maps, photographs, aerial photographs, satellite images, antiquarians, local collections, RCHME, CBA, English Heritage, CADW, Historic Scotland) • Aerial photography • field walking and other methods of recovering archaeological material from the surface • field work, including on-site survey (i.e. landscape, underwater and environmental survey) sampling strategies (e.g. understanding the uses and limitations of sampling in an archaeological context) • surveying and standing building survey methods • geoprospection (resistivity, magnetometry, GPR, metal detecting, sonar) • geochemistry (phosphate analysis) Paper 2:Unit 1 Discovering and recording sites and landscapes
- 3. Tithe map of same area, 1840 Survey of parish by Whyte, 1792
- 8. “....desk-based assessment is a programme of assessment of the known or potential archaeological resource within a specified area or site on land, inter-tidal zone or underwater. It consists of a collation of existing written, graphic, photographic and electronic information in order to identify the likely character, extent, quality and worth of the known or potential archaeological resource in a local, regional, national or international context as appropriate.
- 14. Late 1850s
- 15. painting of the old Strathbungo village in the 1820′s, it is made from 2 viewpoints combined to give an overview Tile works
- 16. “Hi Jim, I got lots of info on the brick works - too much to post on Facebook so I hope you get this message: First, this from Andrew Downie on Marywood Sq: The 1859 Glasgow PO Directory lists the Titwood brickyard of A & T Hamilton, brick and tile makers, that previously occupied the site. The original feu disposition of 1860 between Sir John Maxwell, and William Stevenson & John McIntyre refers to compensation to be paid to Alexander Hamilton, brickmaker in Glasgow and Thomas Hamilton, brick and tile maker, Auchingray Brick and Tile Works, Carnwrath, since they would be required to vacate the site. The map puts the brickworks about half way down Marywood Square, or in the back land between it and Queen Square. It probably explains why whenever I dig my garden I hit brick. There was a small branch line that ran from the brickworks to the railway line (on the map), the railway predating the houses of Strathbungo. The line would have passed roughly under my house [52] at the end of Marywood Square. Case study- A tileworks in the South Side
- 20. 1820
