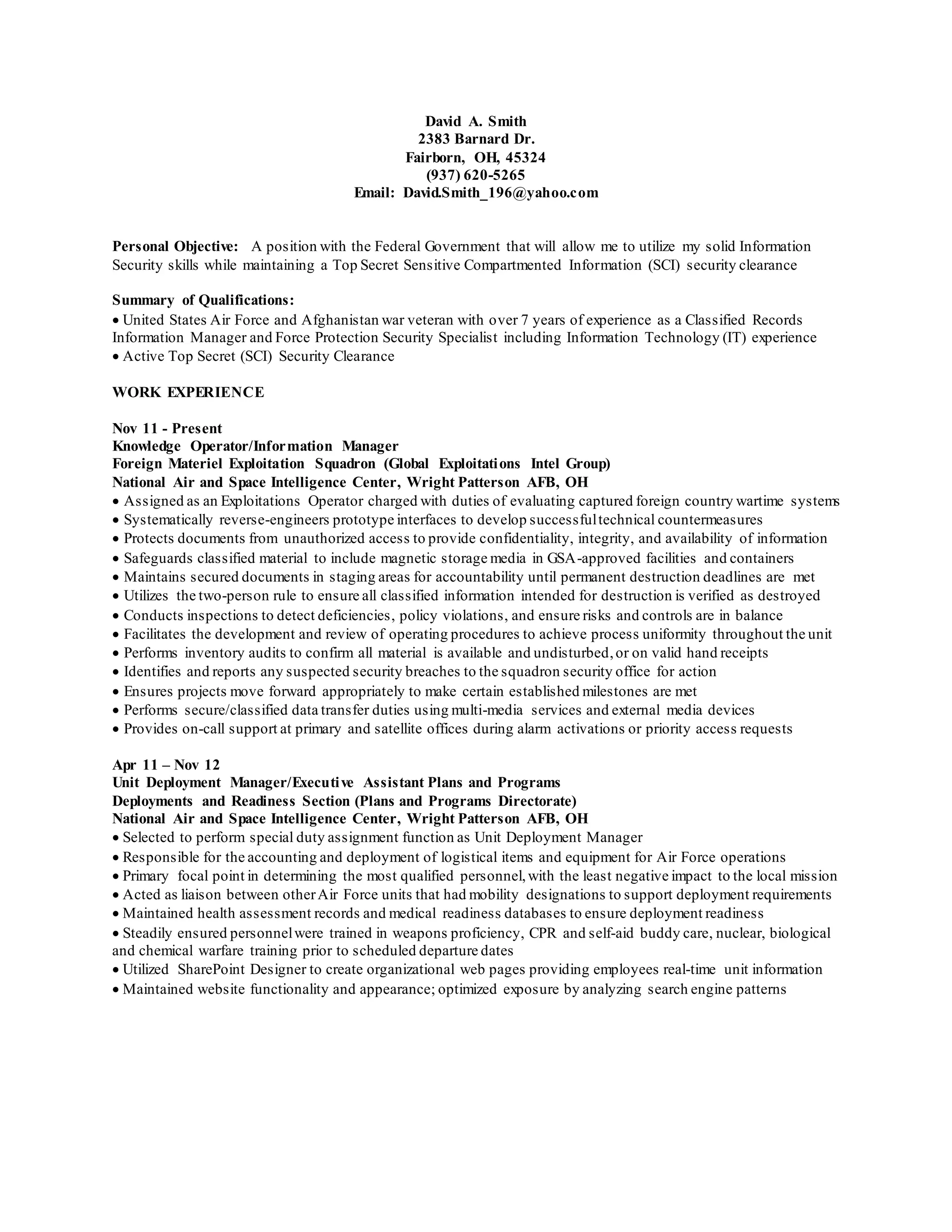
David Smith is seeking a position with the Federal Government utilizing his Information Security skills and Top Secret SCI clearance. He has over 7 years of experience managing classified records and providing force protection as a US Air Force veteran. His experience includes evaluating captured foreign systems, safeguarding classified materials, and ensuring projects meet milestones. He is proficient in Windows, Office, and security protocols.