Dataveillance
•Download as PPTX, PDF•
1 like•523 views
The following presentation took place at the 2012 World Game Protection Conference in Las Vegas http://www.worldgameprotection.com/conference/speakers/
Report
Share
Report
Share
Recommended
More Related Content
Similar to Dataveillance
Similar to Dataveillance (20)
The Benefits of Having Nerds On Site Monitoring Your Technology

The Benefits of Having Nerds On Site Monitoring Your Technology
The Benefits of Having Nerds On Site Monitoring Your Technology

The Benefits of Having Nerds On Site Monitoring Your Technology
Threat Hunting by Falgun Rathod - Cyber Octet Private Limited

Threat Hunting by Falgun Rathod - Cyber Octet Private Limited
Social Distance Your IBM i from Cybersecurity Risk

Social Distance Your IBM i from Cybersecurity Risk
Recently uploaded
Recently uploaded (20)
The 7 Things I Know About Cyber Security After 25 Years | April 2024

The 7 Things I Know About Cyber Security After 25 Years | April 2024
Beyond Boundaries: Leveraging No-Code Solutions for Industry Innovation

Beyond Boundaries: Leveraging No-Code Solutions for Industry Innovation
Unblocking The Main Thread Solving ANRs and Frozen Frames

Unblocking The Main Thread Solving ANRs and Frozen Frames
SQL Database Design For Developers at php[tek] 2024![SQL Database Design For Developers at php[tek] 2024](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![SQL Database Design For Developers at php[tek] 2024](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
SQL Database Design For Developers at php[tek] 2024
Swan(sea) Song – personal research during my six years at Swansea ... and bey...

Swan(sea) Song – personal research during my six years at Swansea ... and bey...
08448380779 Call Girls In Civil Lines Women Seeking Men

08448380779 Call Girls In Civil Lines Women Seeking Men
From Event to Action: Accelerate Your Decision Making with Real-Time Automation

From Event to Action: Accelerate Your Decision Making with Real-Time Automation
08448380779 Call Girls In Friends Colony Women Seeking Men

08448380779 Call Girls In Friends Colony Women Seeking Men
Integration and Automation in Practice: CI/CD in Mule Integration and Automat...

Integration and Automation in Practice: CI/CD in Mule Integration and Automat...
FULL ENJOY 🔝 8264348440 🔝 Call Girls in Diplomatic Enclave | Delhi

FULL ENJOY 🔝 8264348440 🔝 Call Girls in Diplomatic Enclave | Delhi
Injustice - Developers Among Us (SciFiDevCon 2024)

Injustice - Developers Among Us (SciFiDevCon 2024)
Transcript: #StandardsGoals for 2024: What’s new for BISAC - Tech Forum 2024

Transcript: #StandardsGoals for 2024: What’s new for BISAC - Tech Forum 2024
Dataveillance
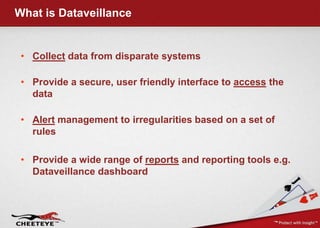
- 1. What is Dataveillance • Collect data from disparate systems • Provide a secure, user friendly interface to access the data • Alert management to irregularities based on a set of rules • Provide a wide range of reports and reporting tools e.g. Dataveillance dashboard
- 2. Collect Occurrence Book
- 3. Collect & Access Collusion Overview Collusion Report Break List
- 4. Access Collusion Detail Transaction List Tips Detailed Player Profile Video Click through
- 5. Access Debarments
- 6. Alert Biggest Winner Alerts
- 7. Alert Biggest Winner Detail Title 31 Inputs Big Winning Patterns
- 8. Alert Standard Deviation • The objective is to identify players with a history of consistently beating the casino. If a player wins over a long period of time while playing at a disadvantage to the house, something is usually up. Analysis is typically on a player with more than 300 hours’ worth of playing time • Standard deviations are calculated by using the underlying odds of the type of bet being placed and the type of game being played
- 9. Report Compliance Dashboard
- 10. Report Card Control Dashboard
- 11. Report Card Control
- 12. Report Slots Review
- 13. Report Slots Graphical Review
- 14. Report Fills & Credits Audit
