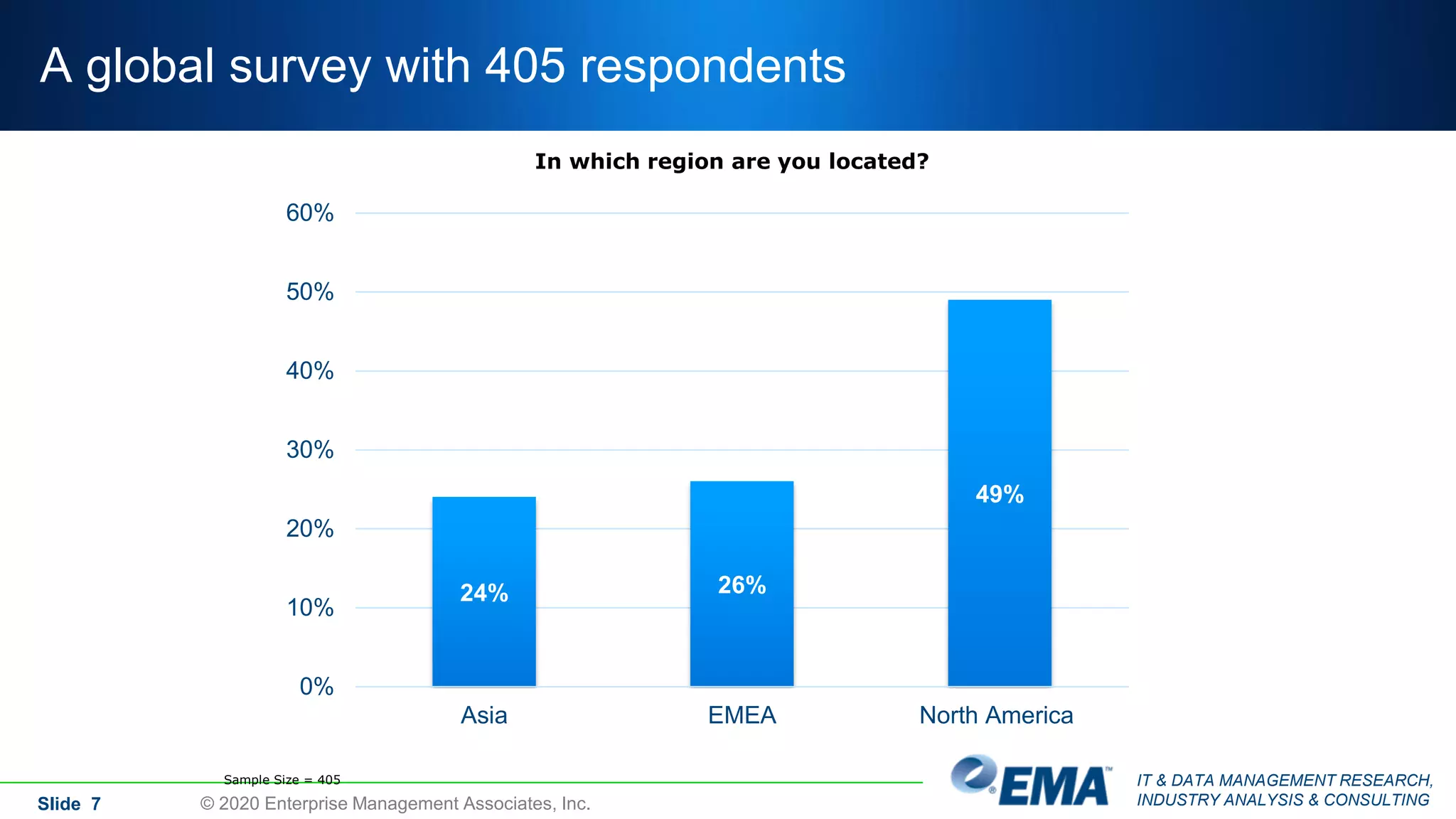
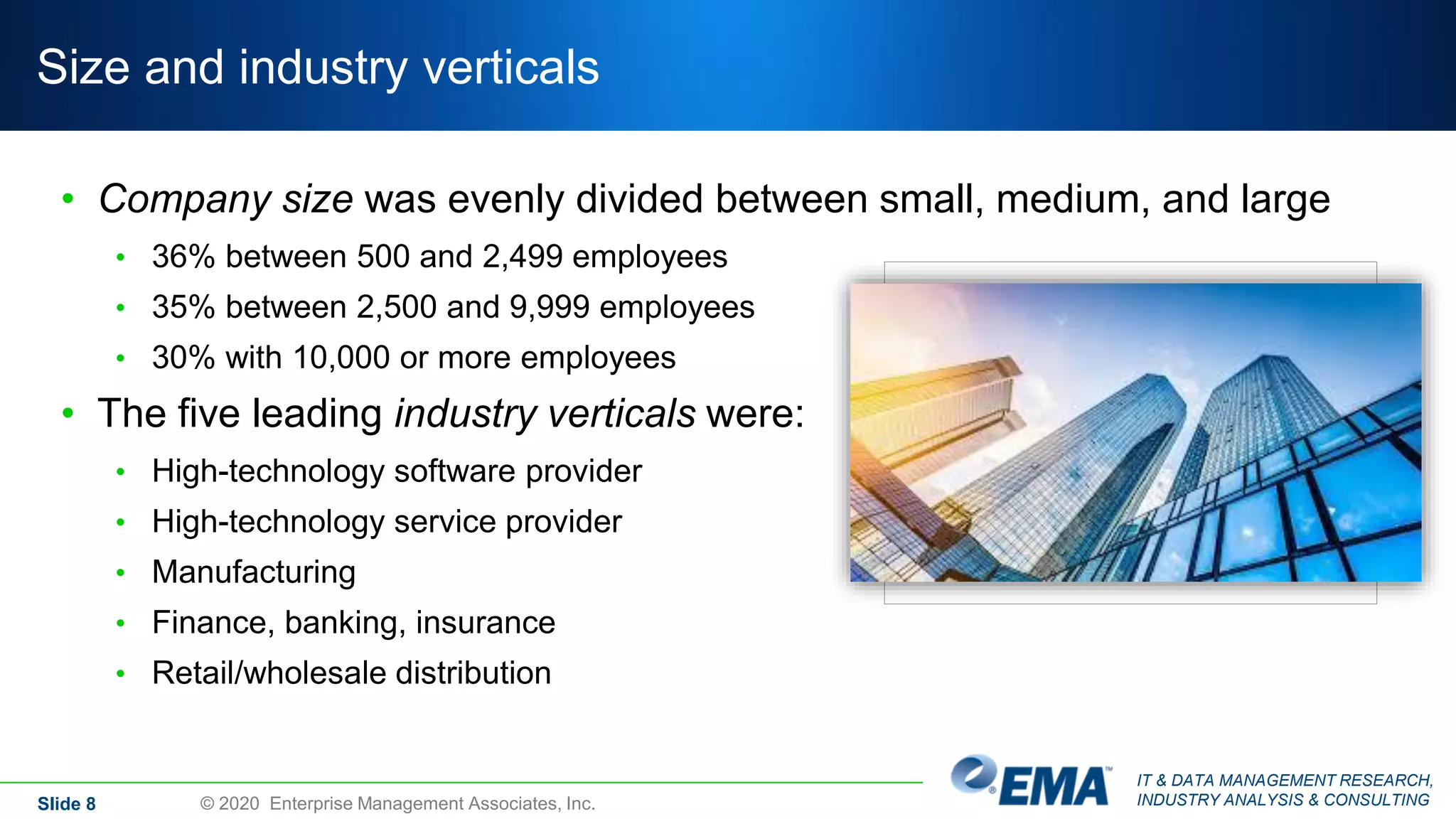
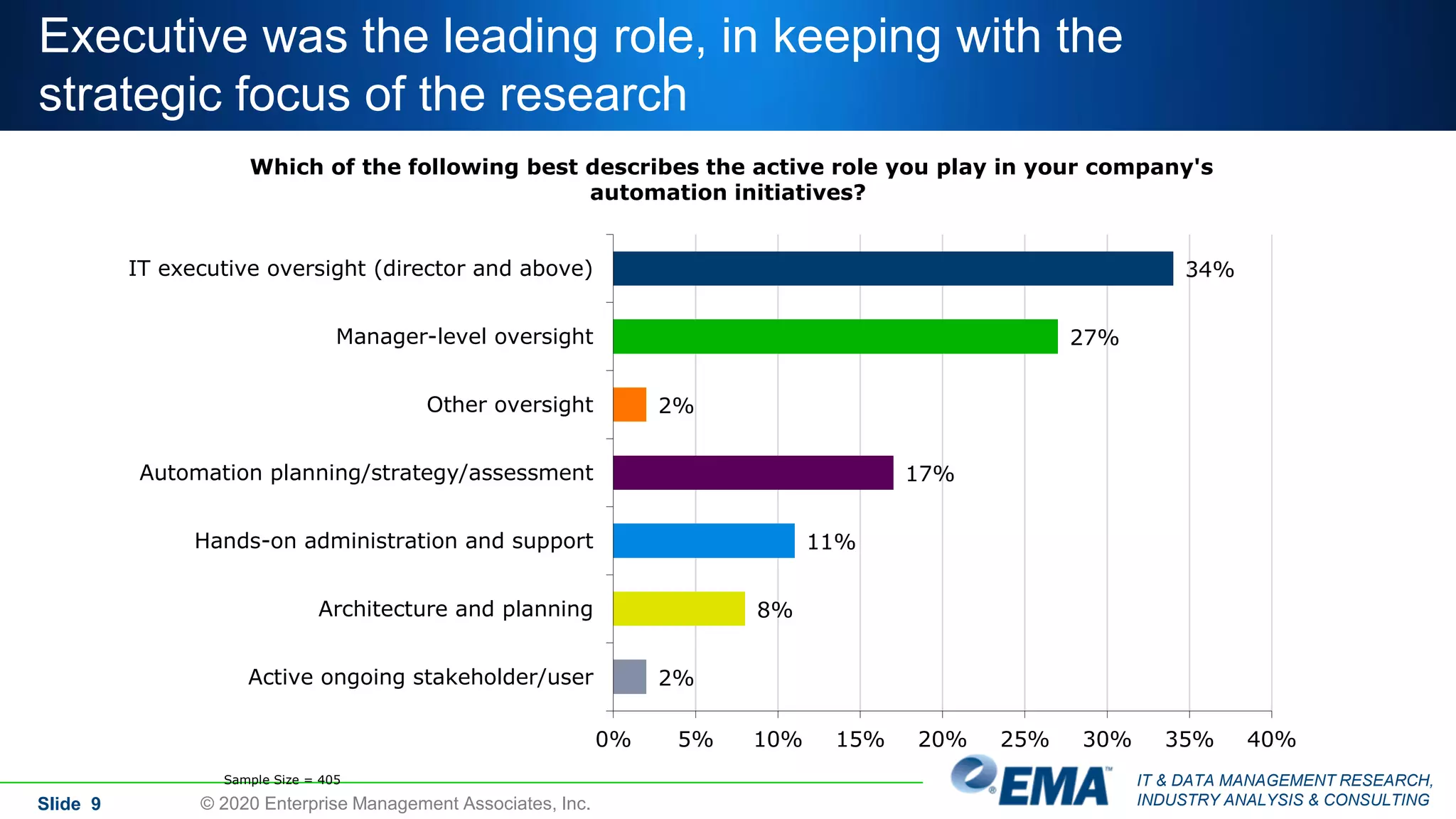
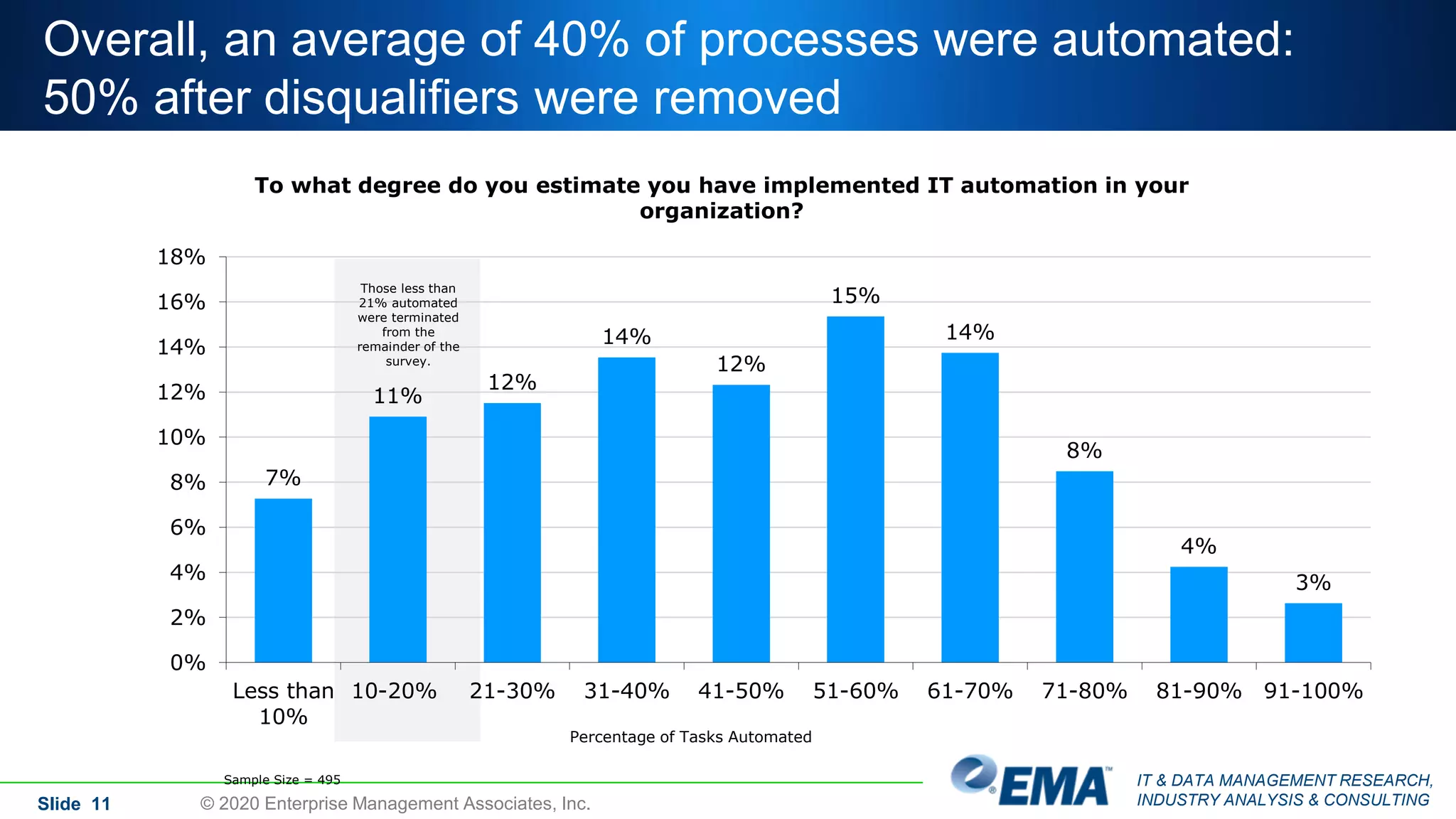
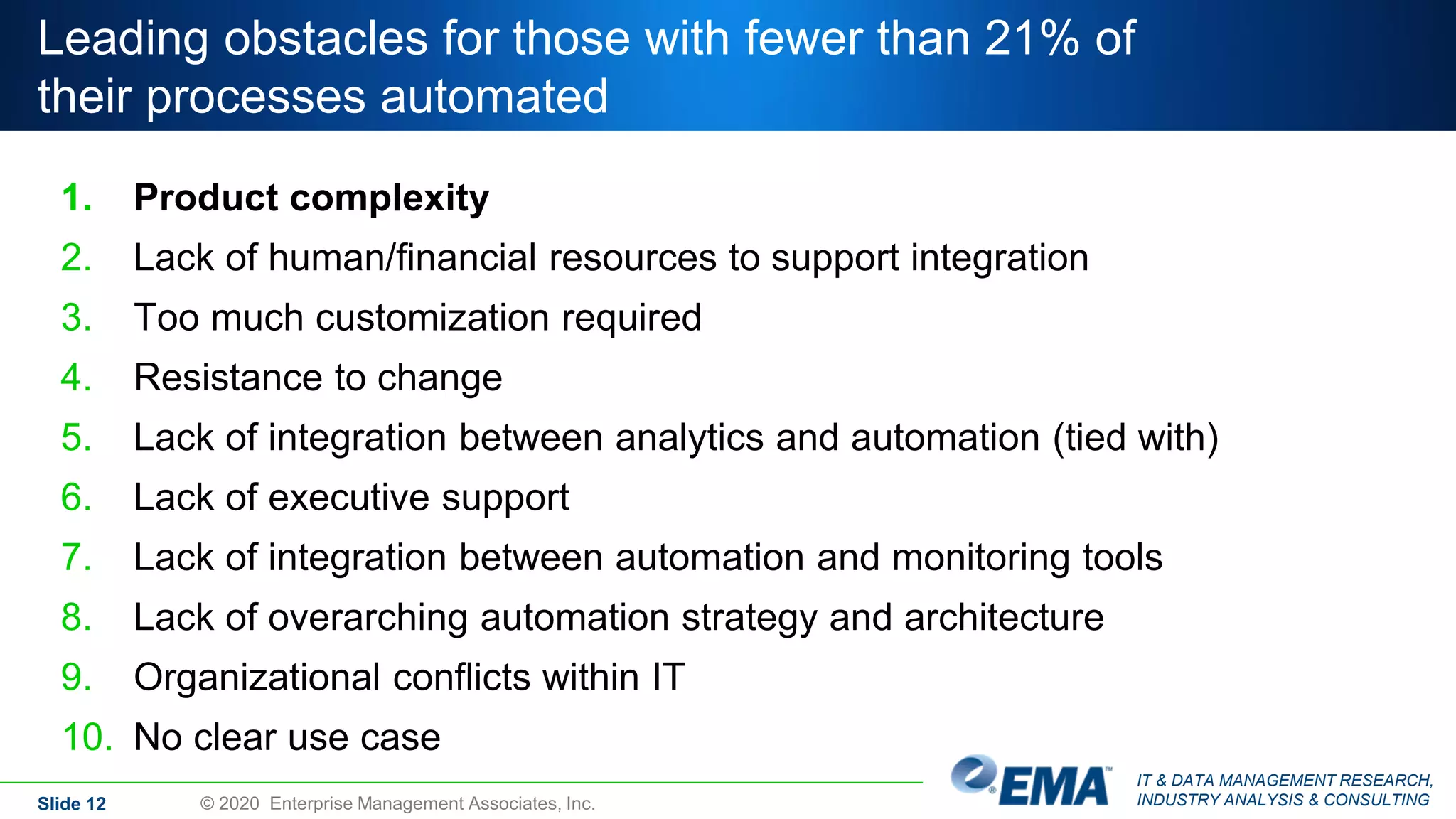
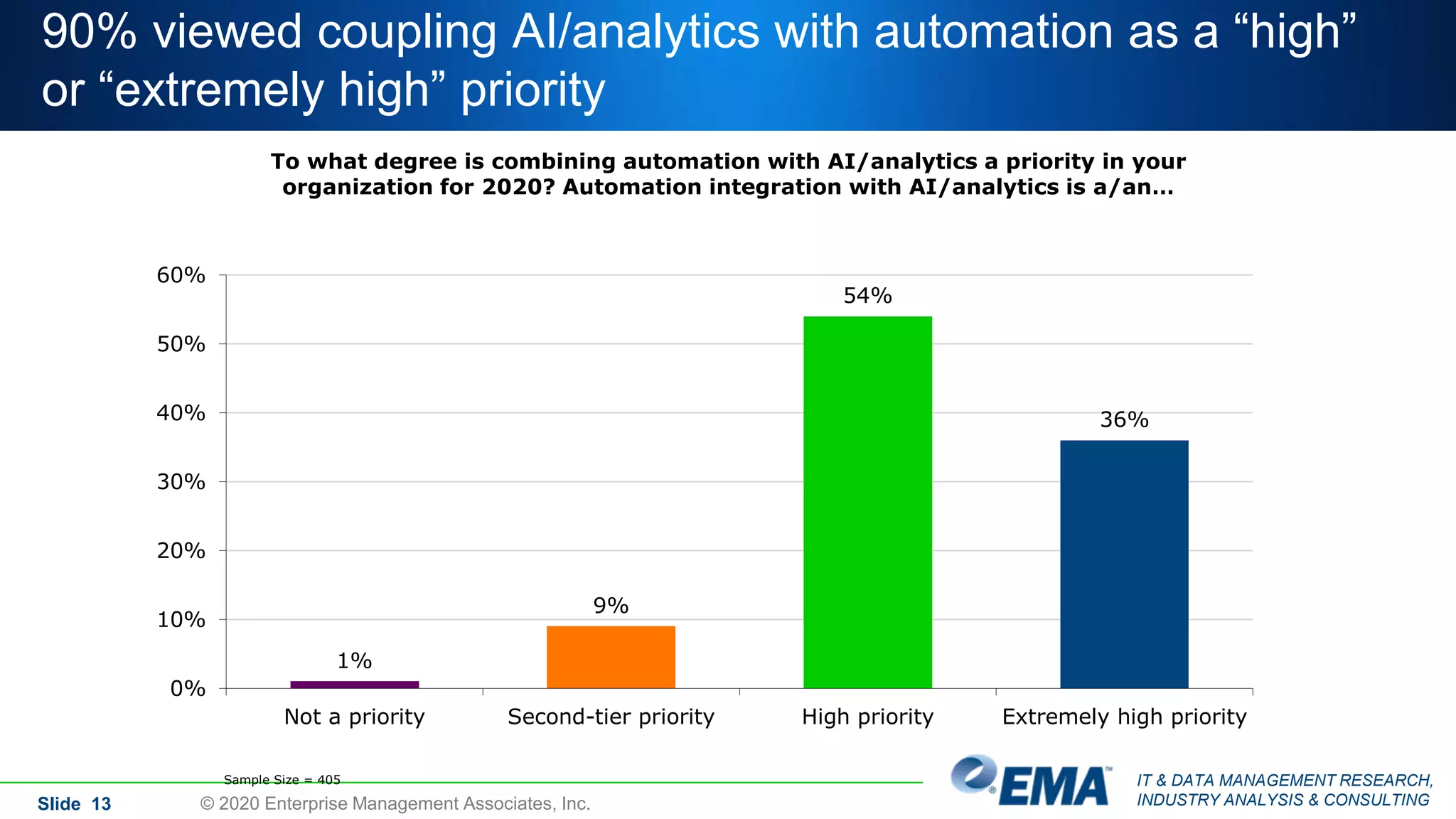
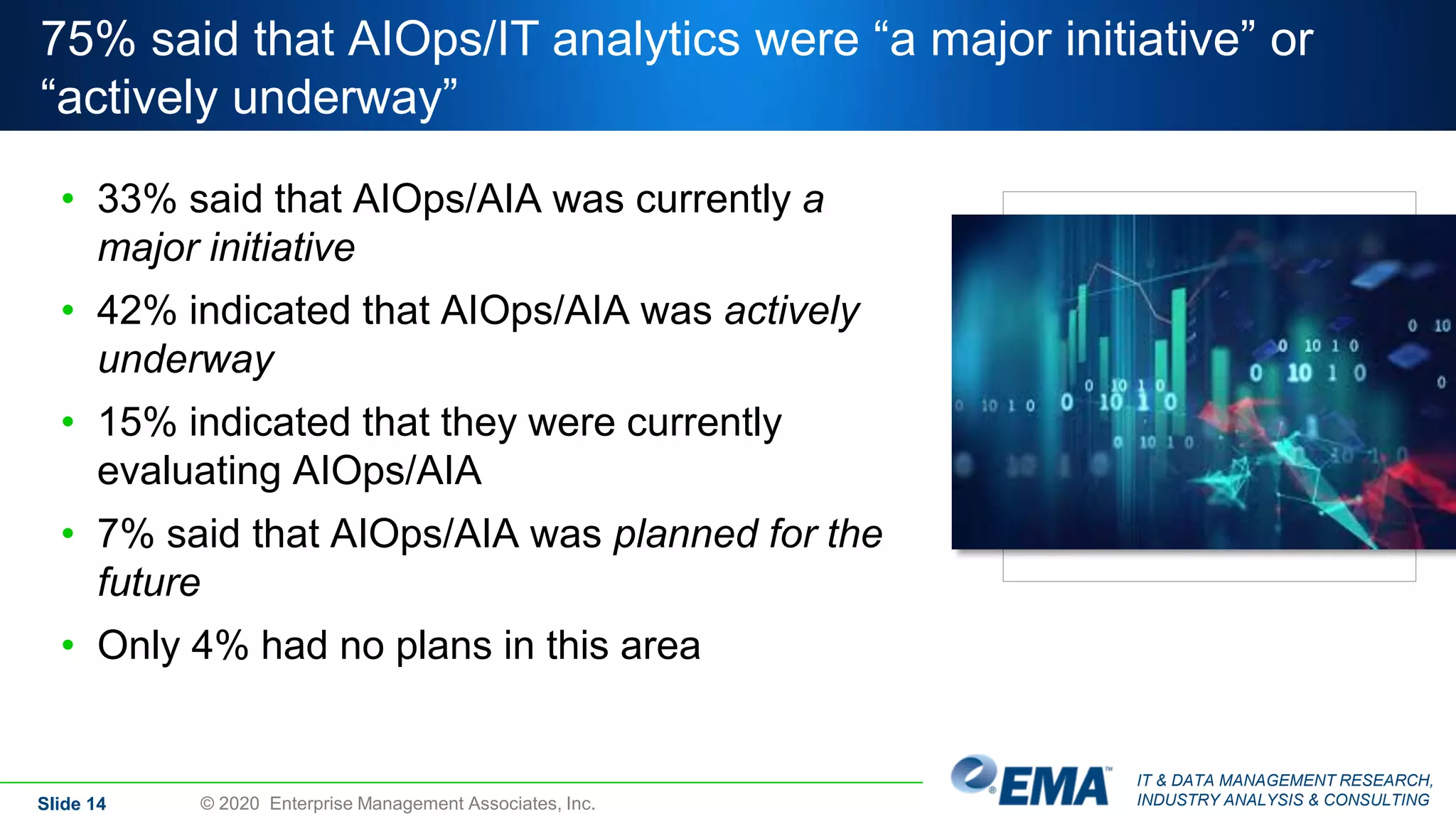
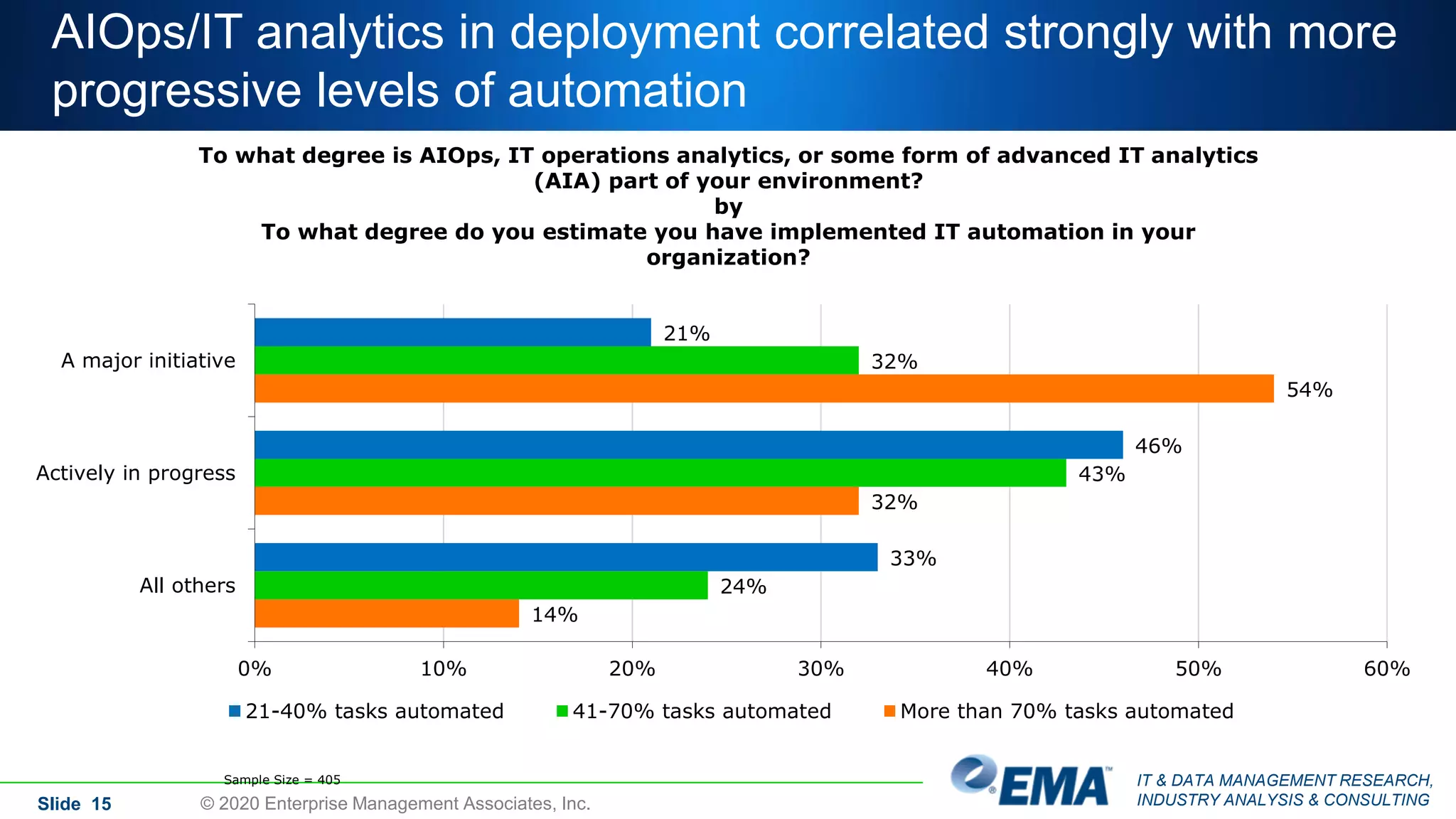
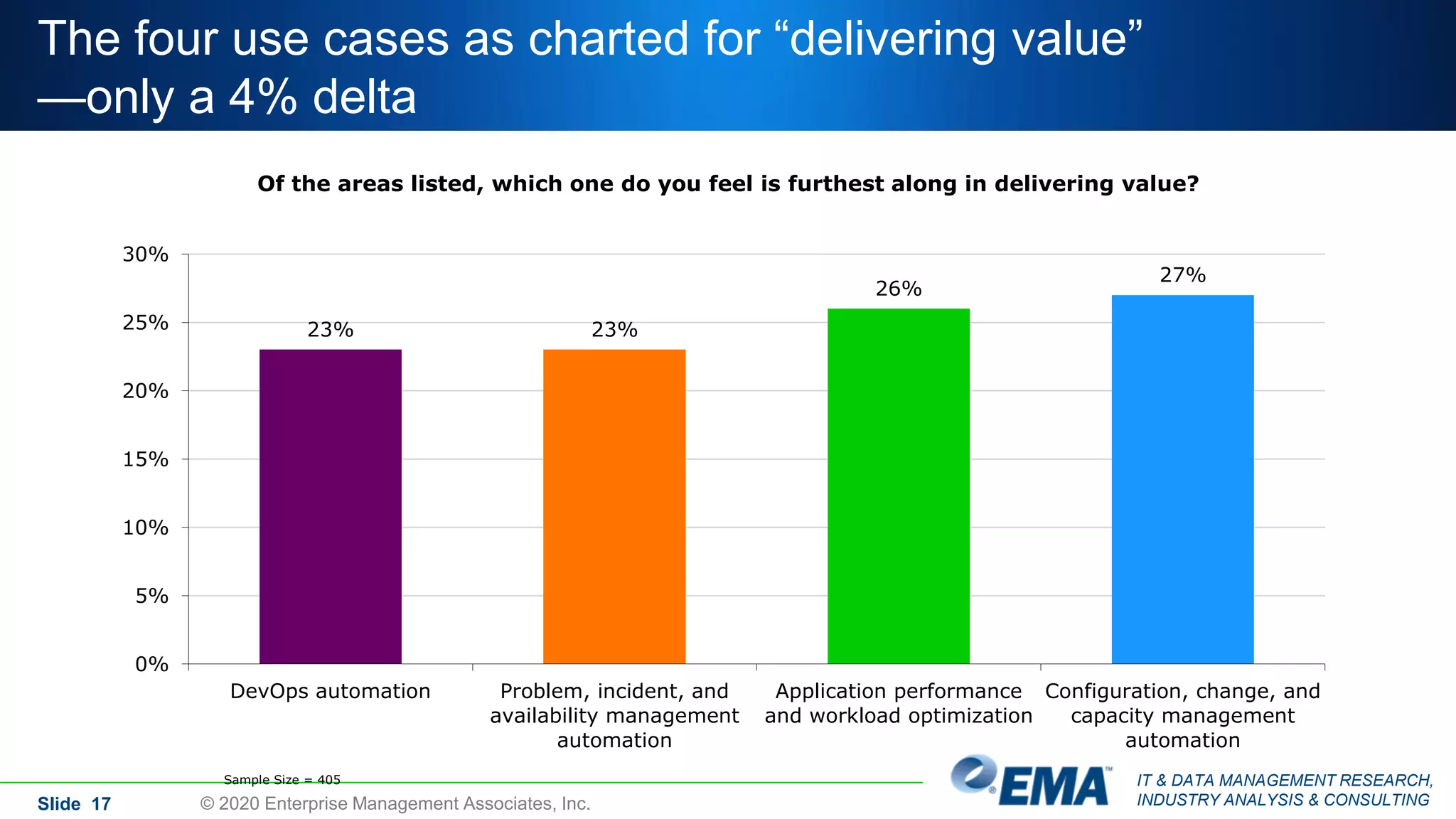
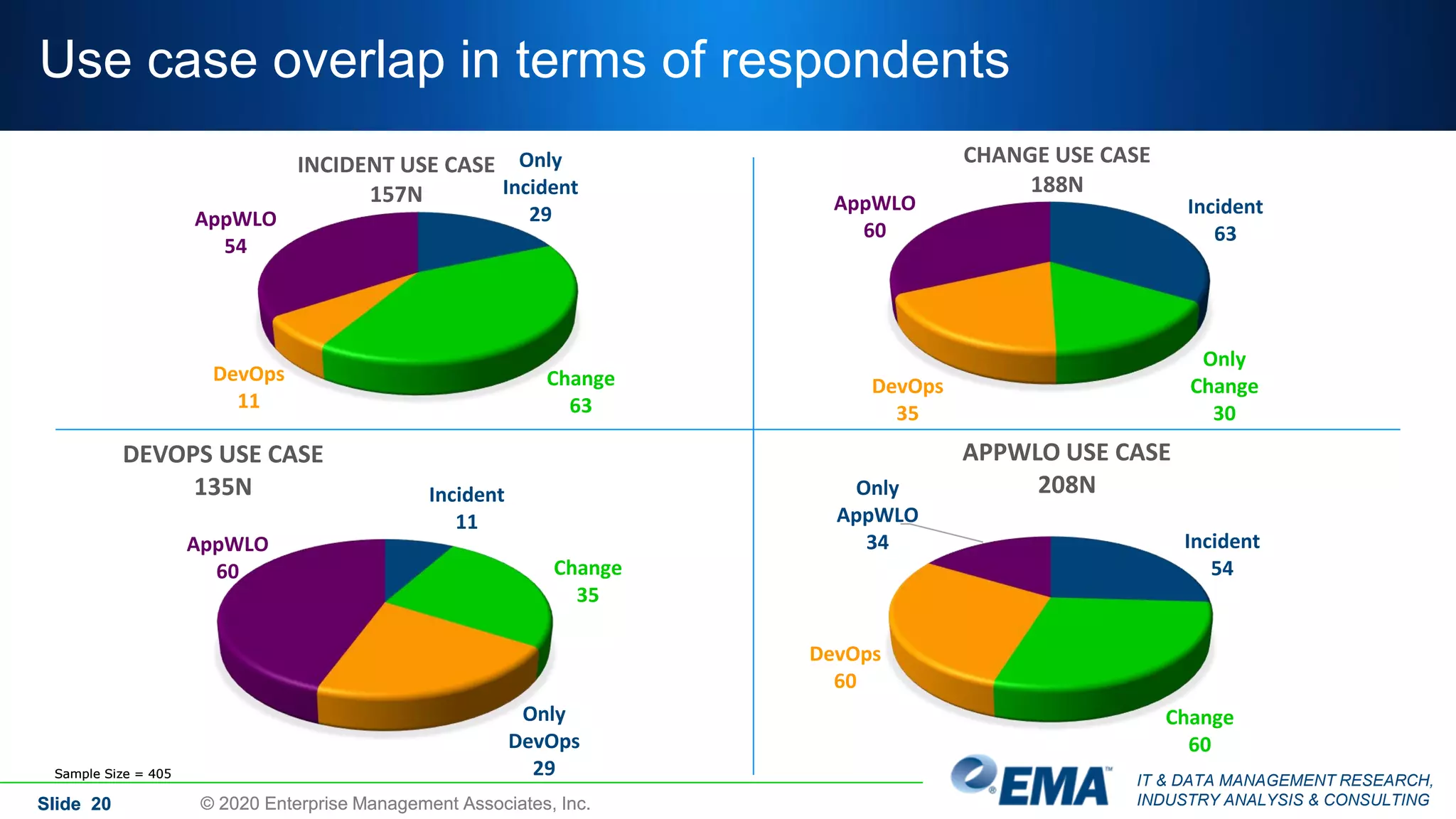
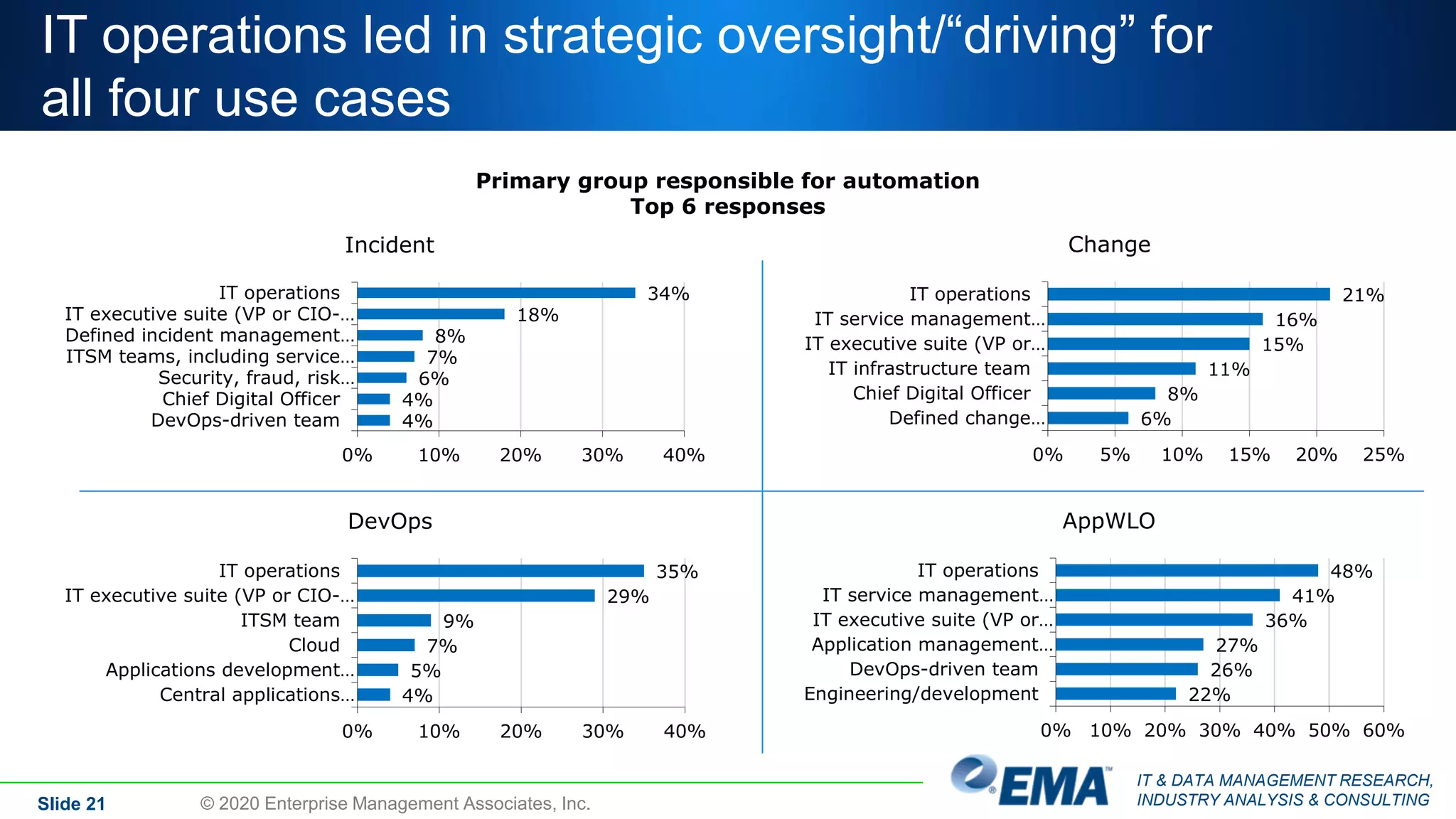
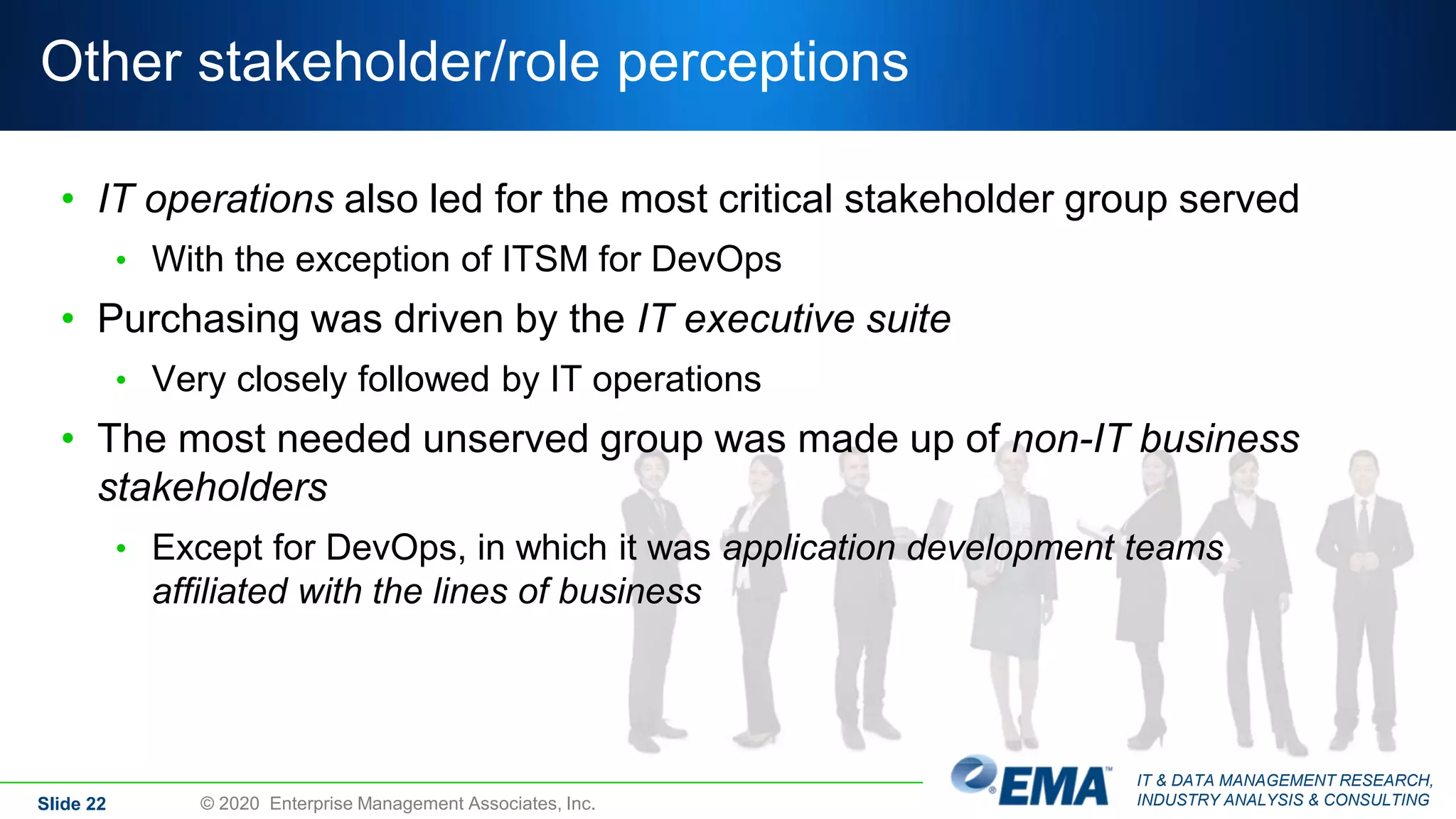
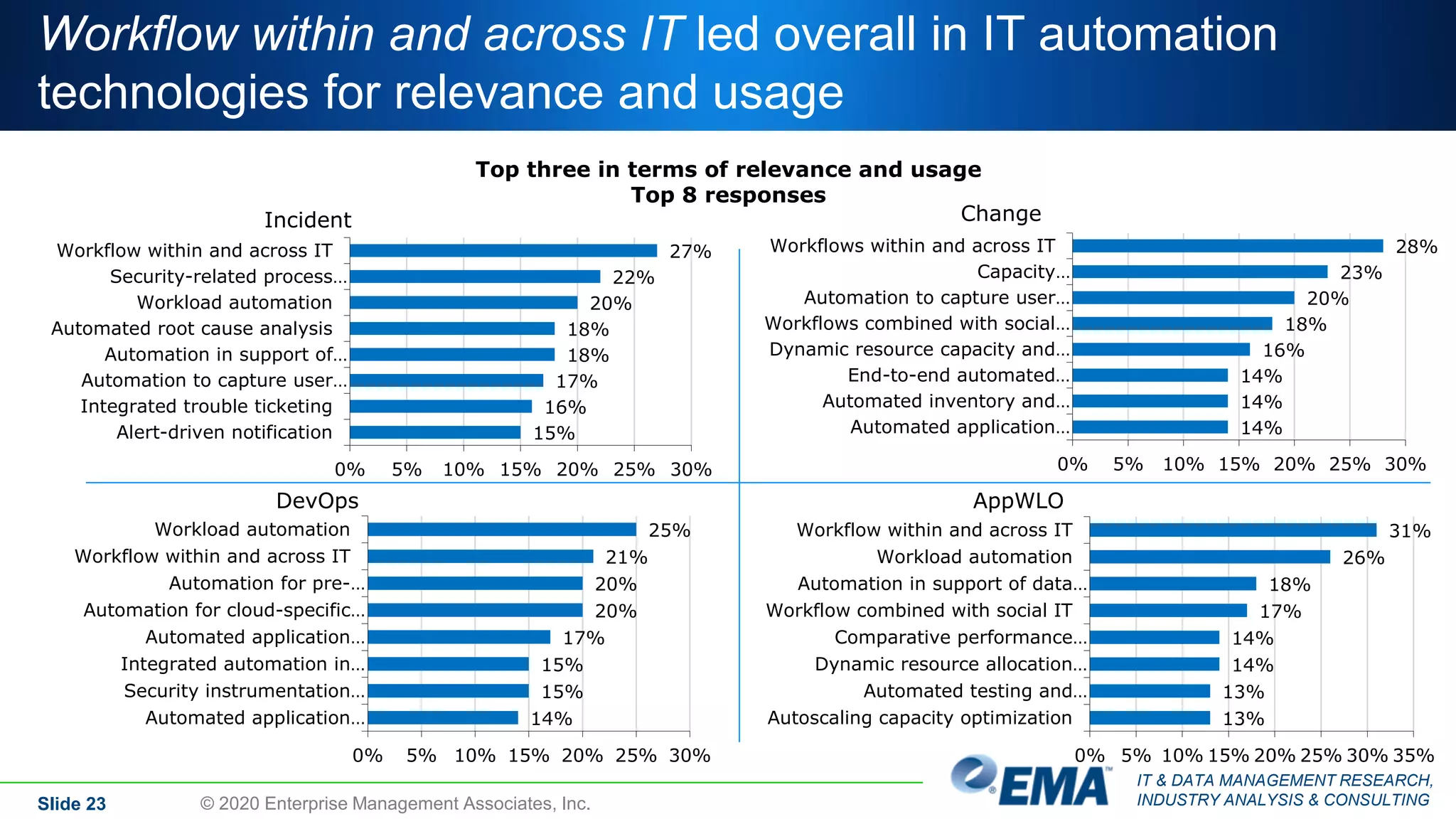
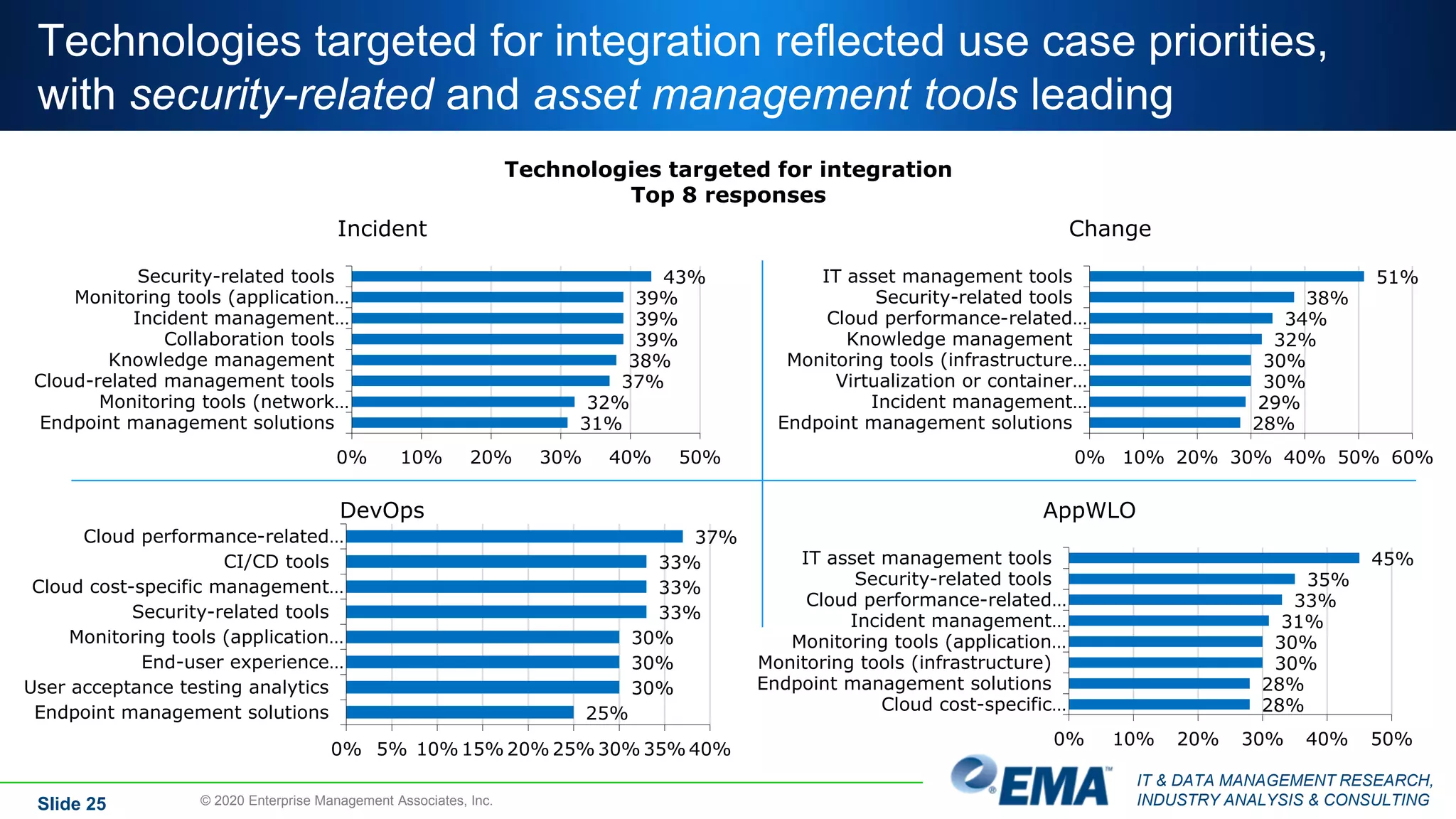
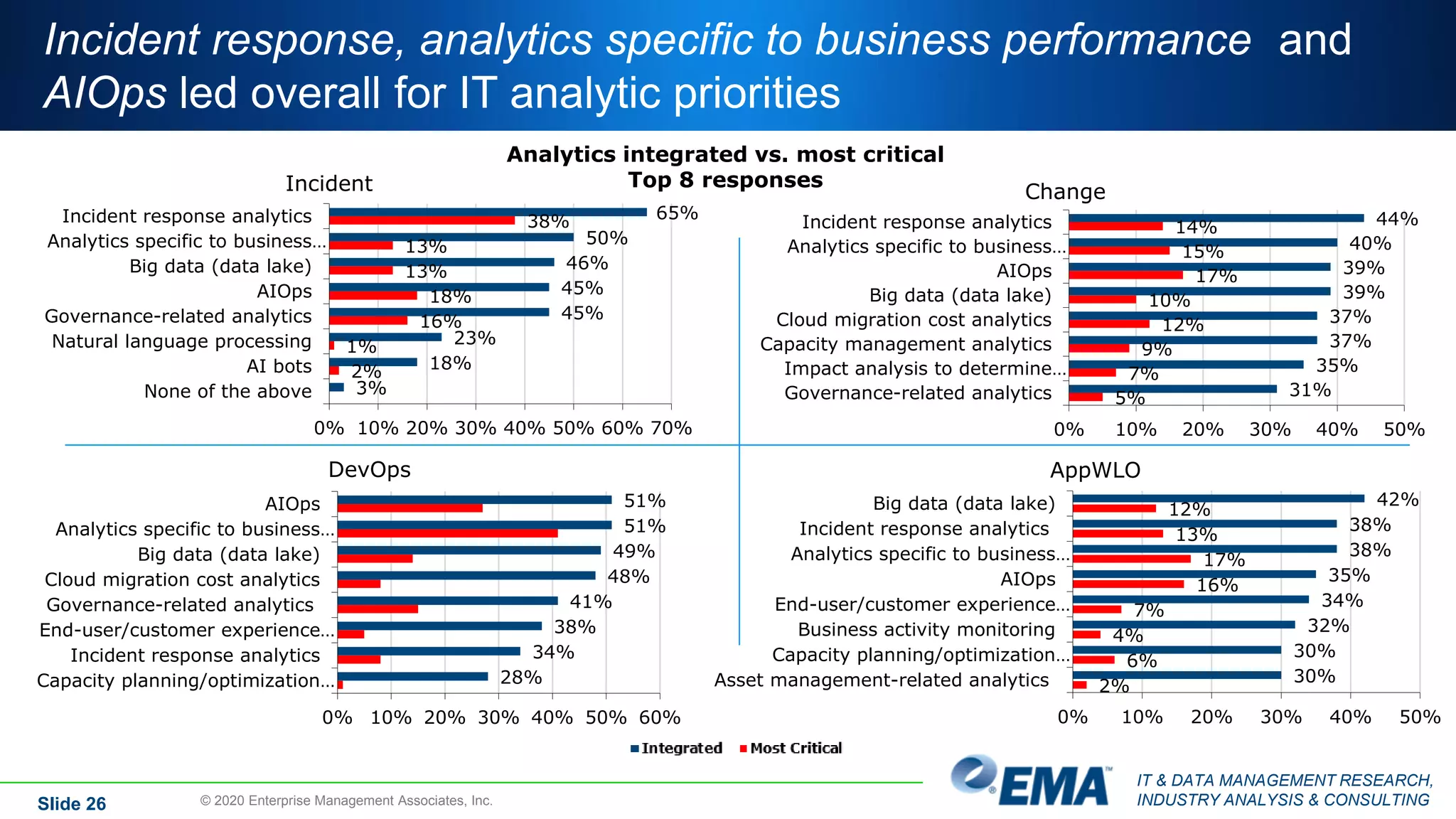
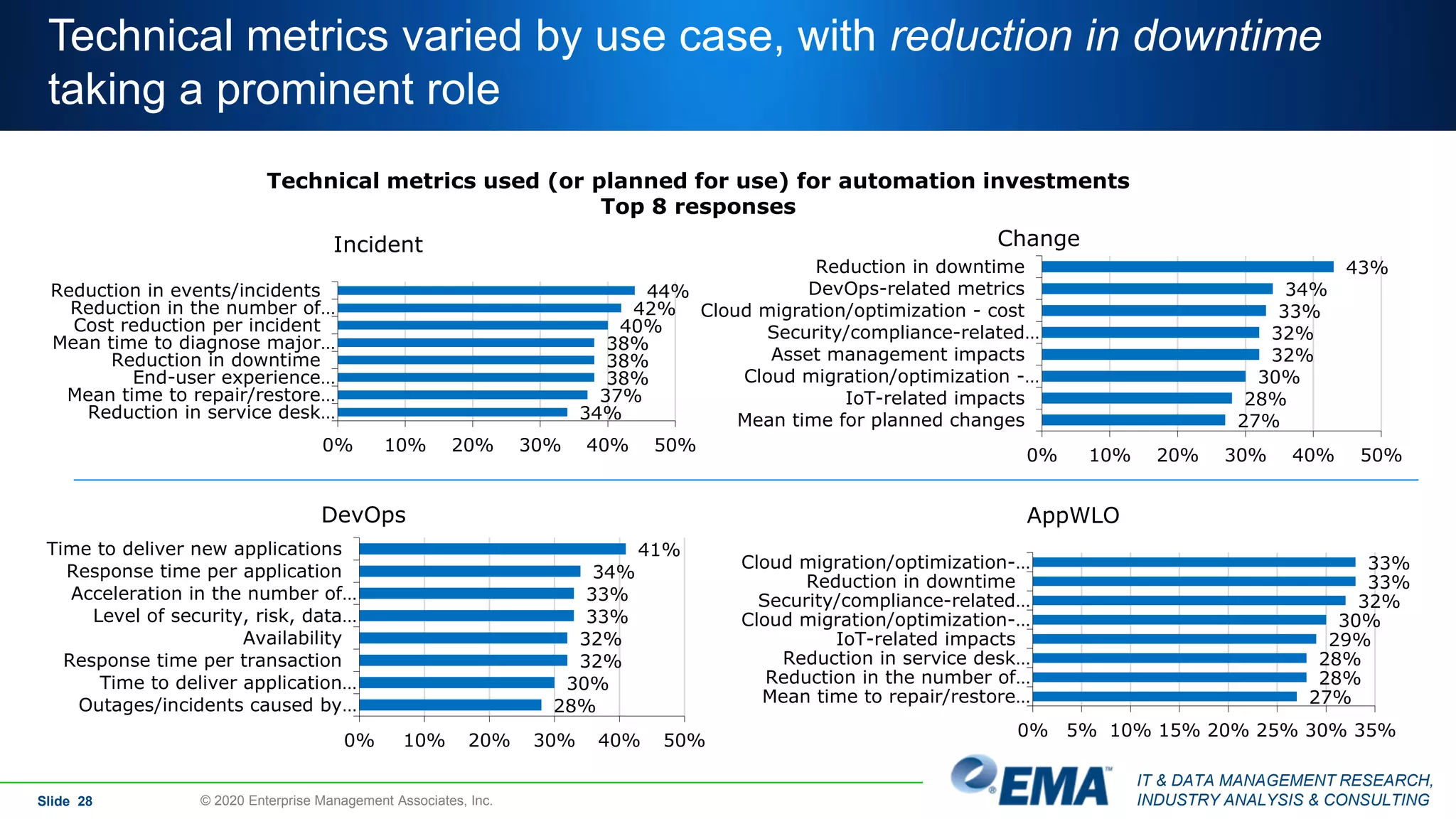
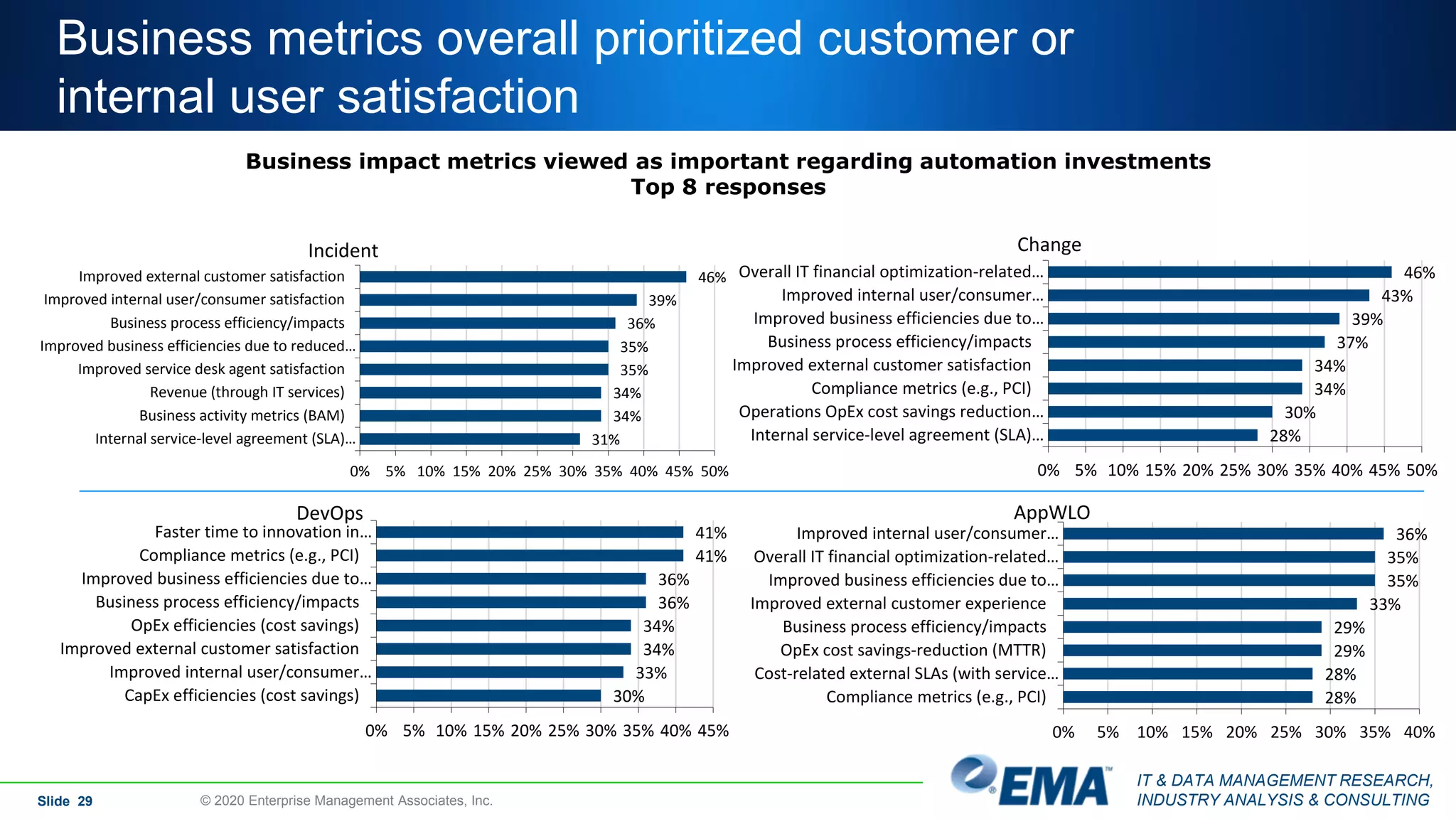
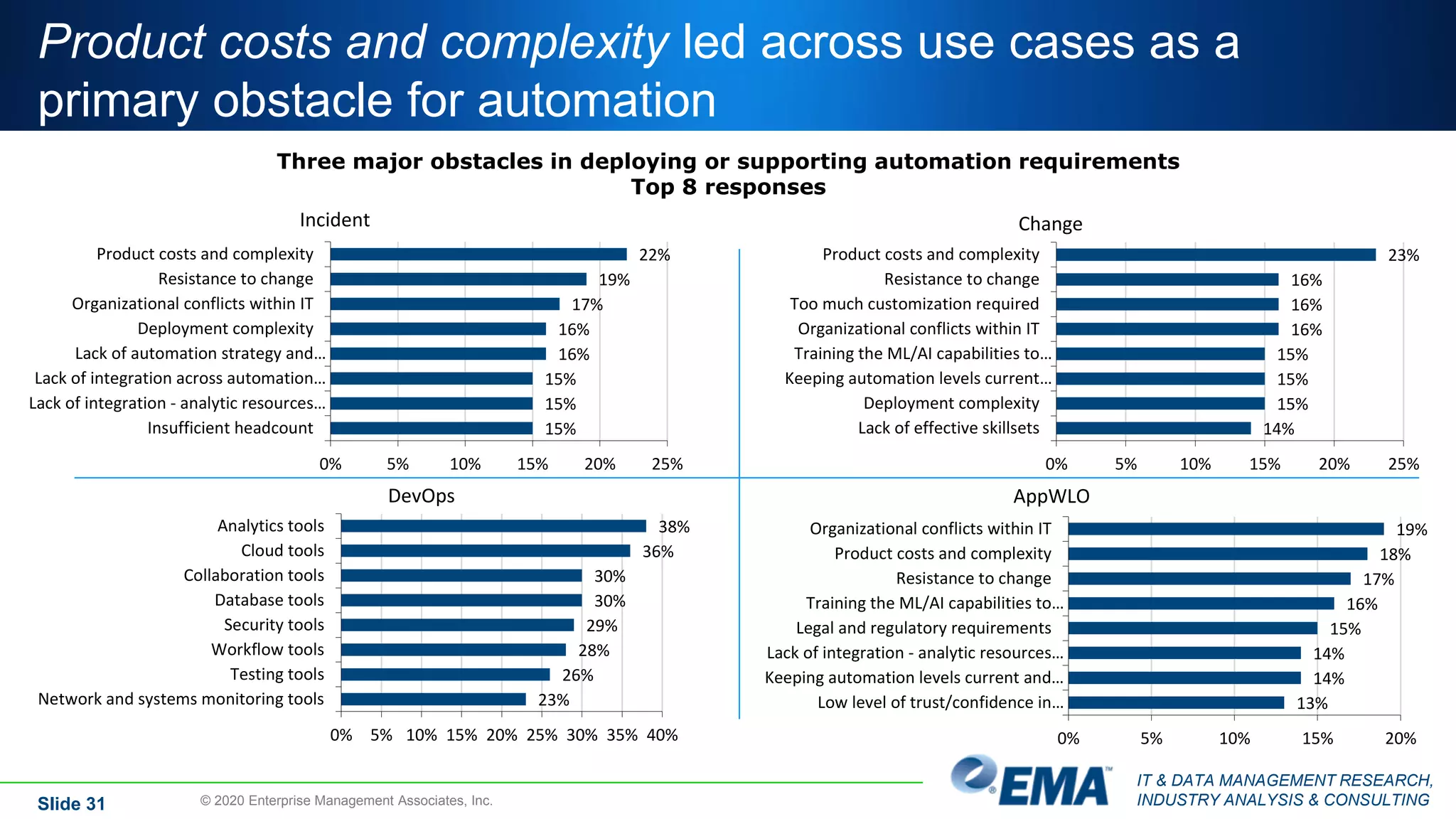
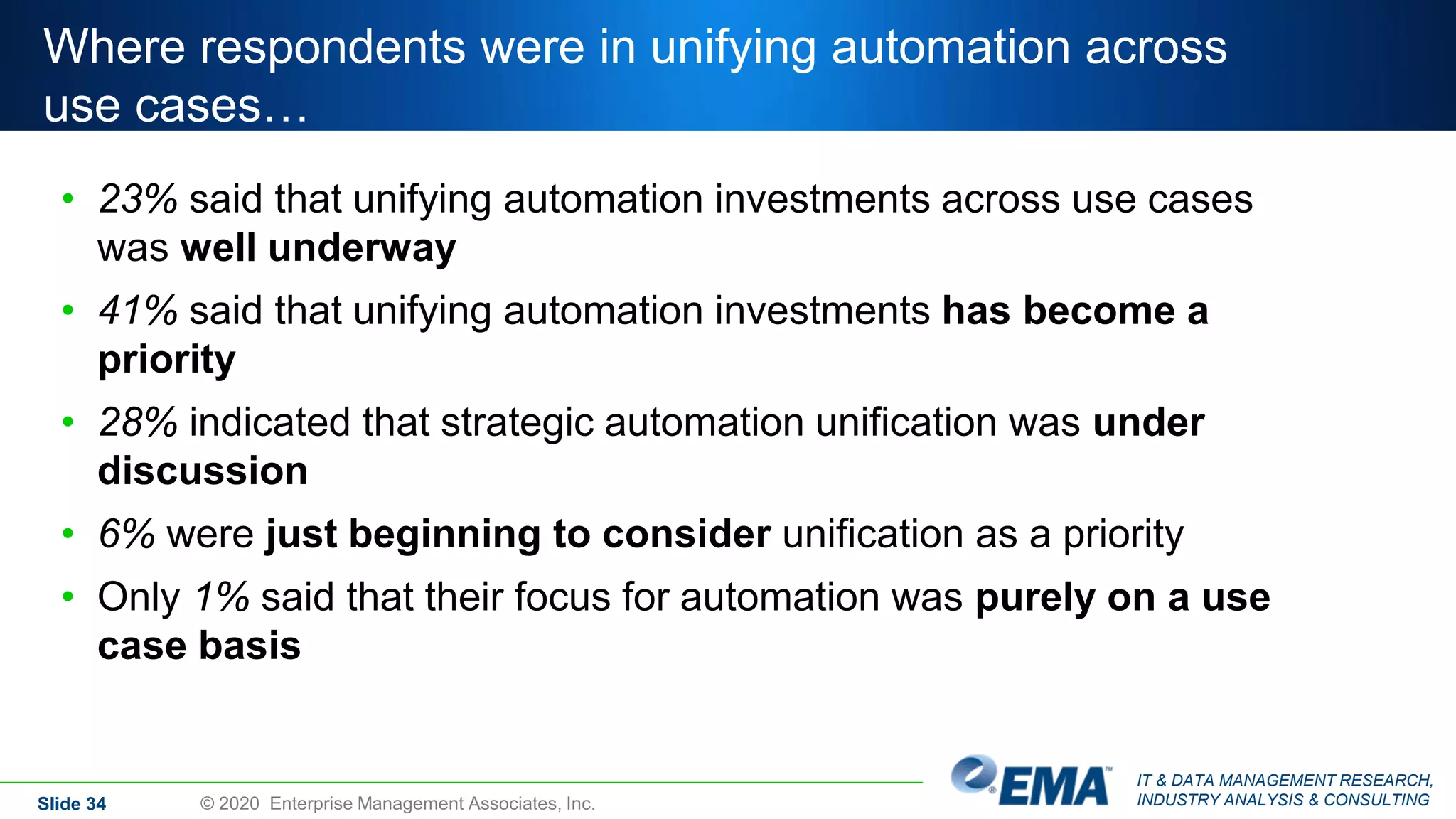
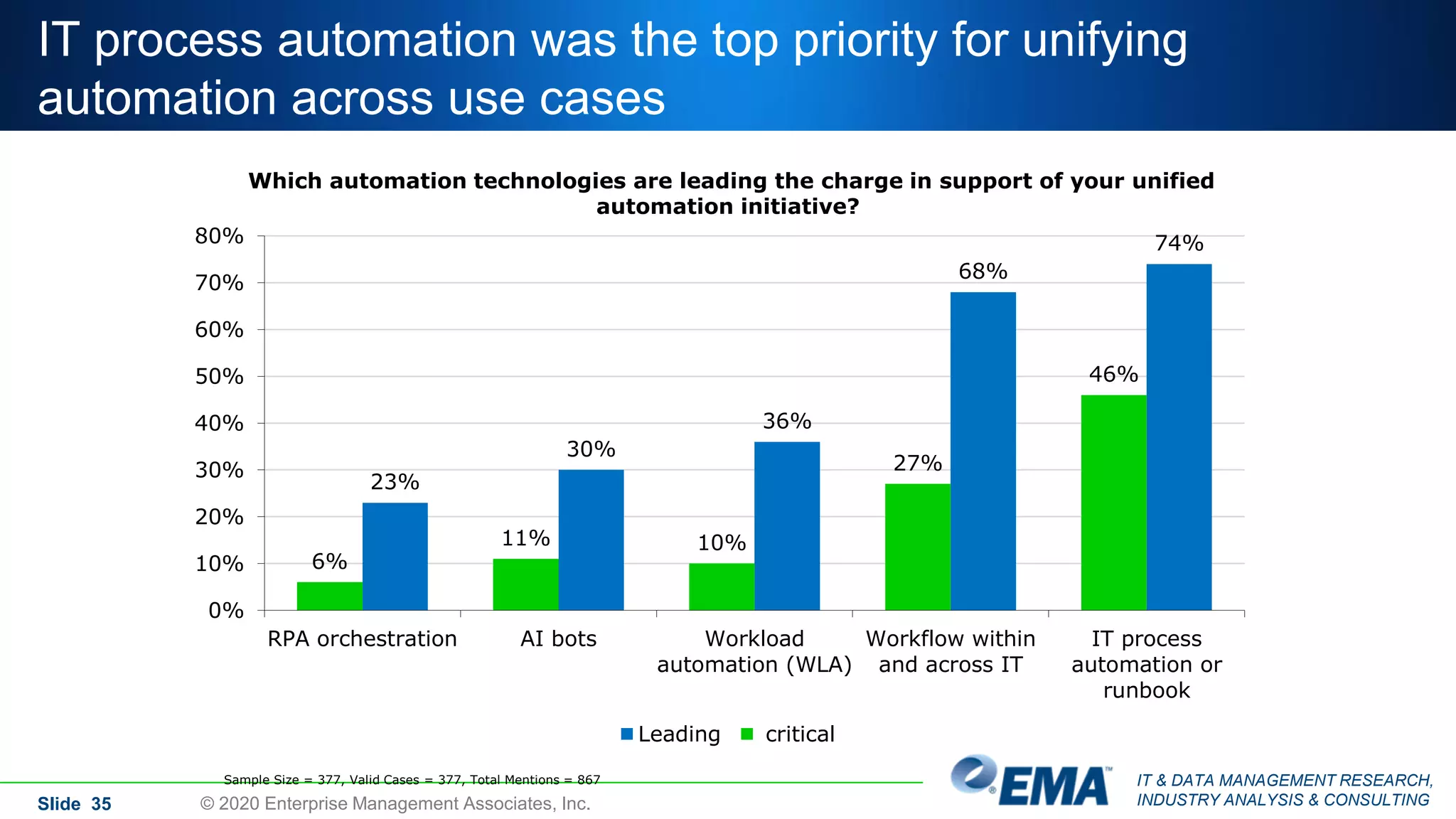
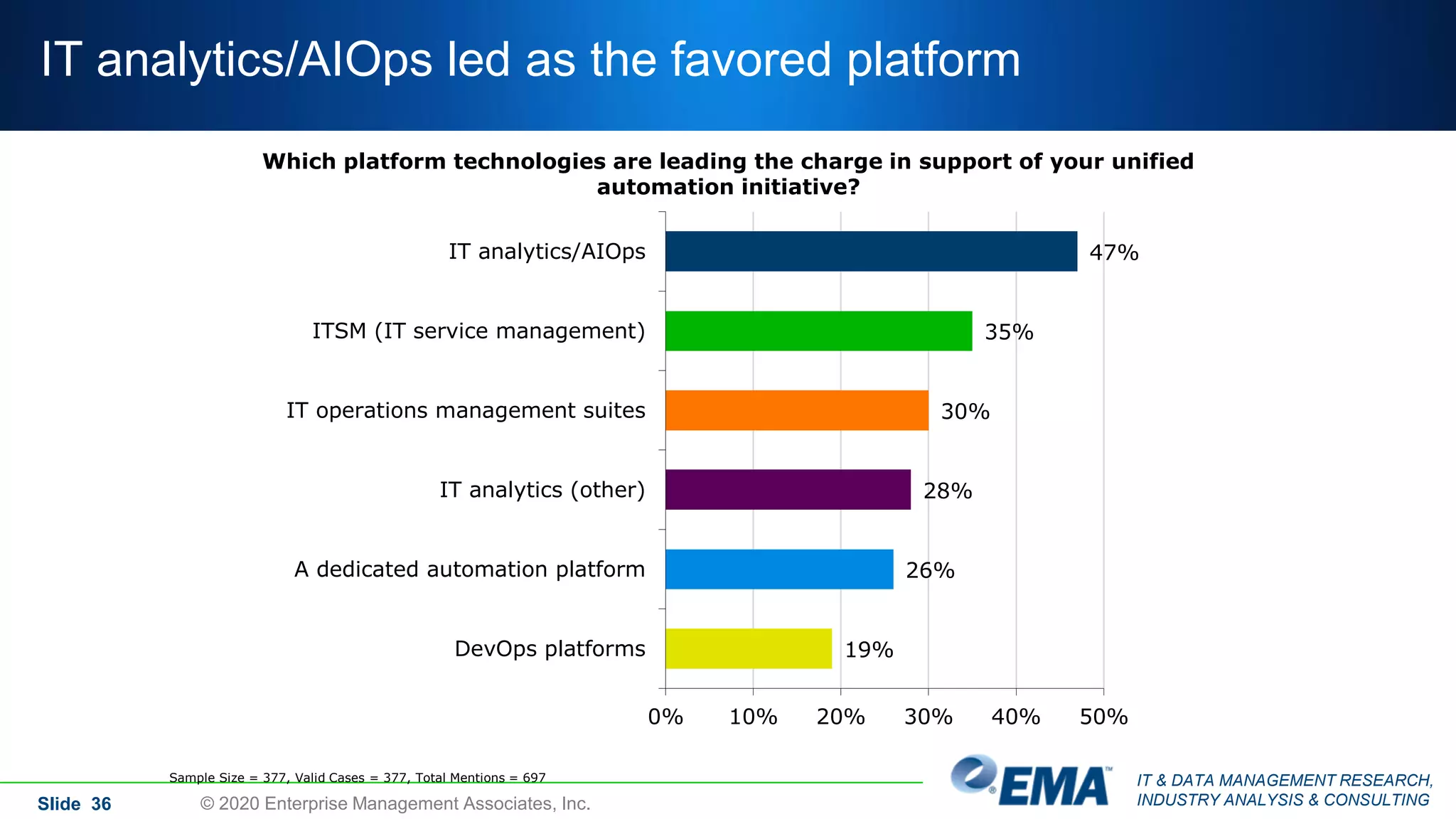
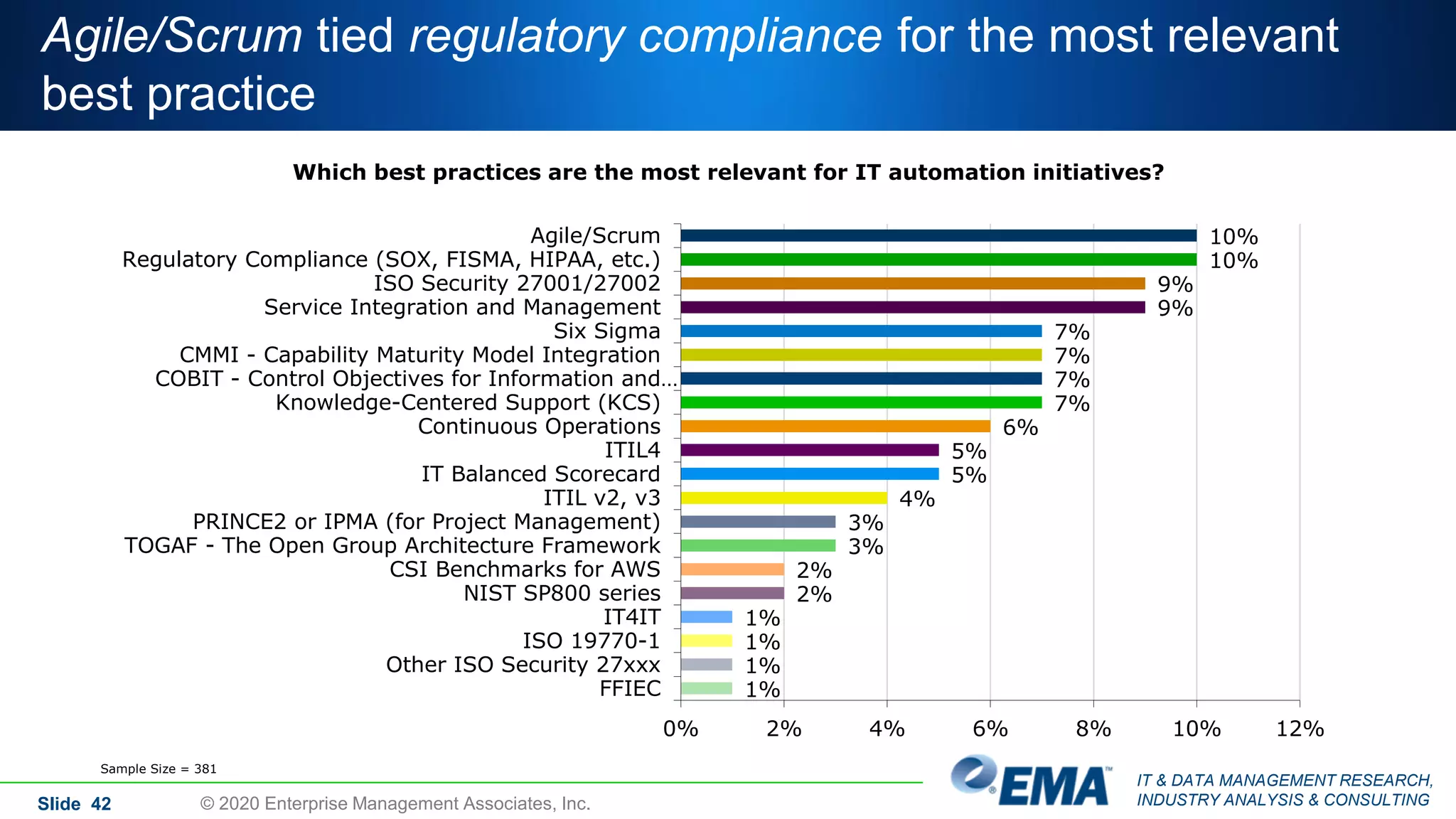
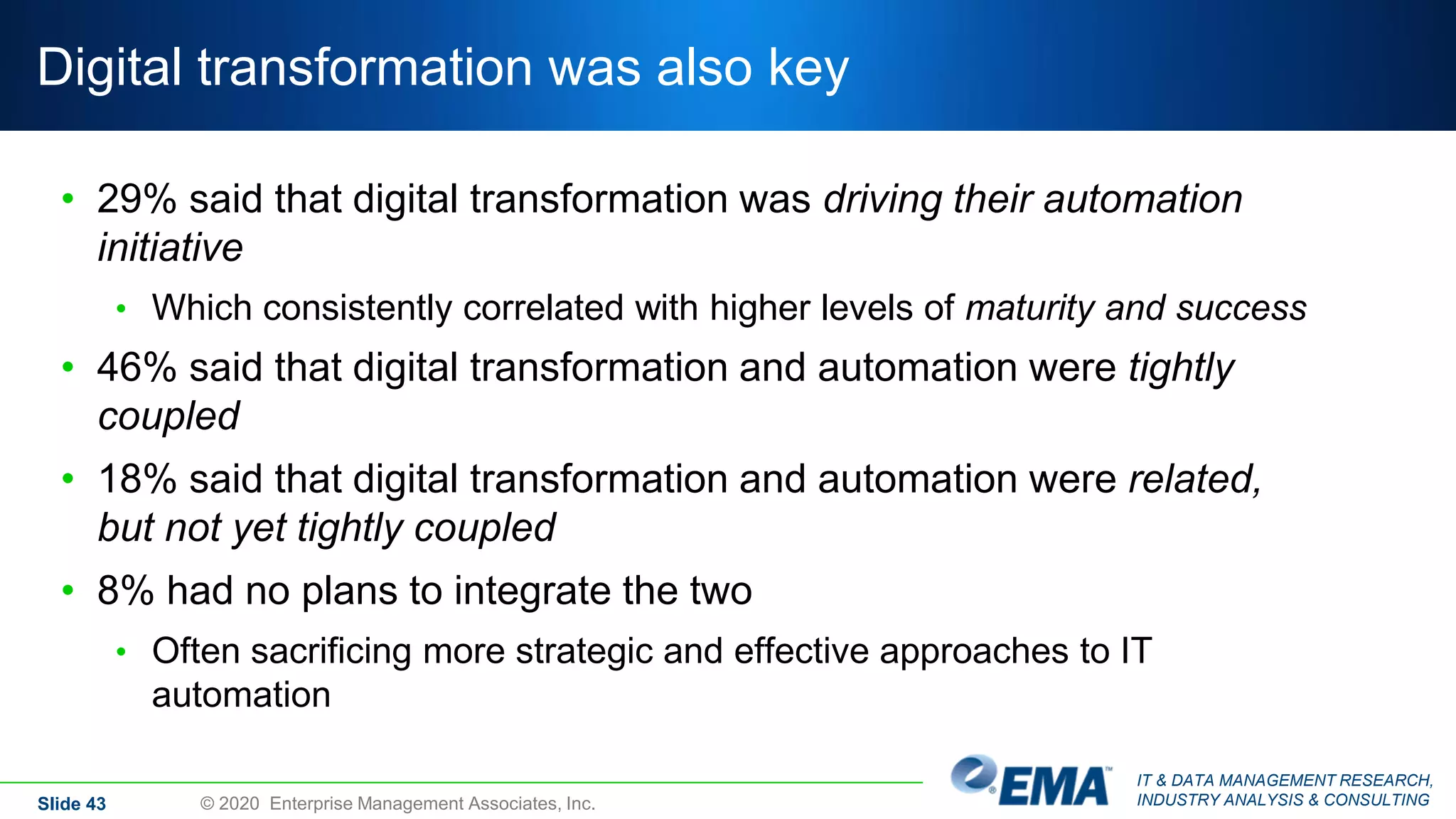
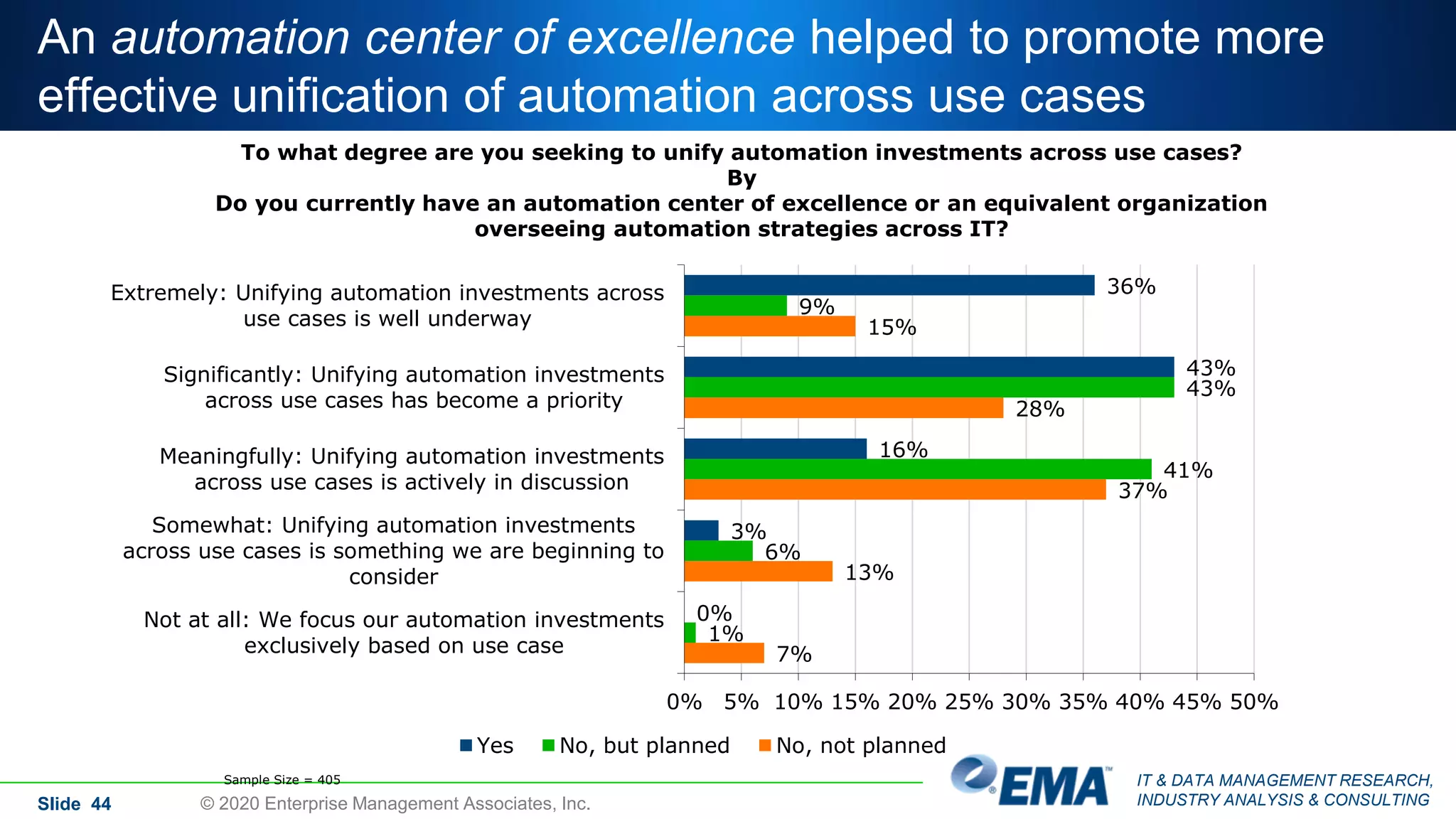
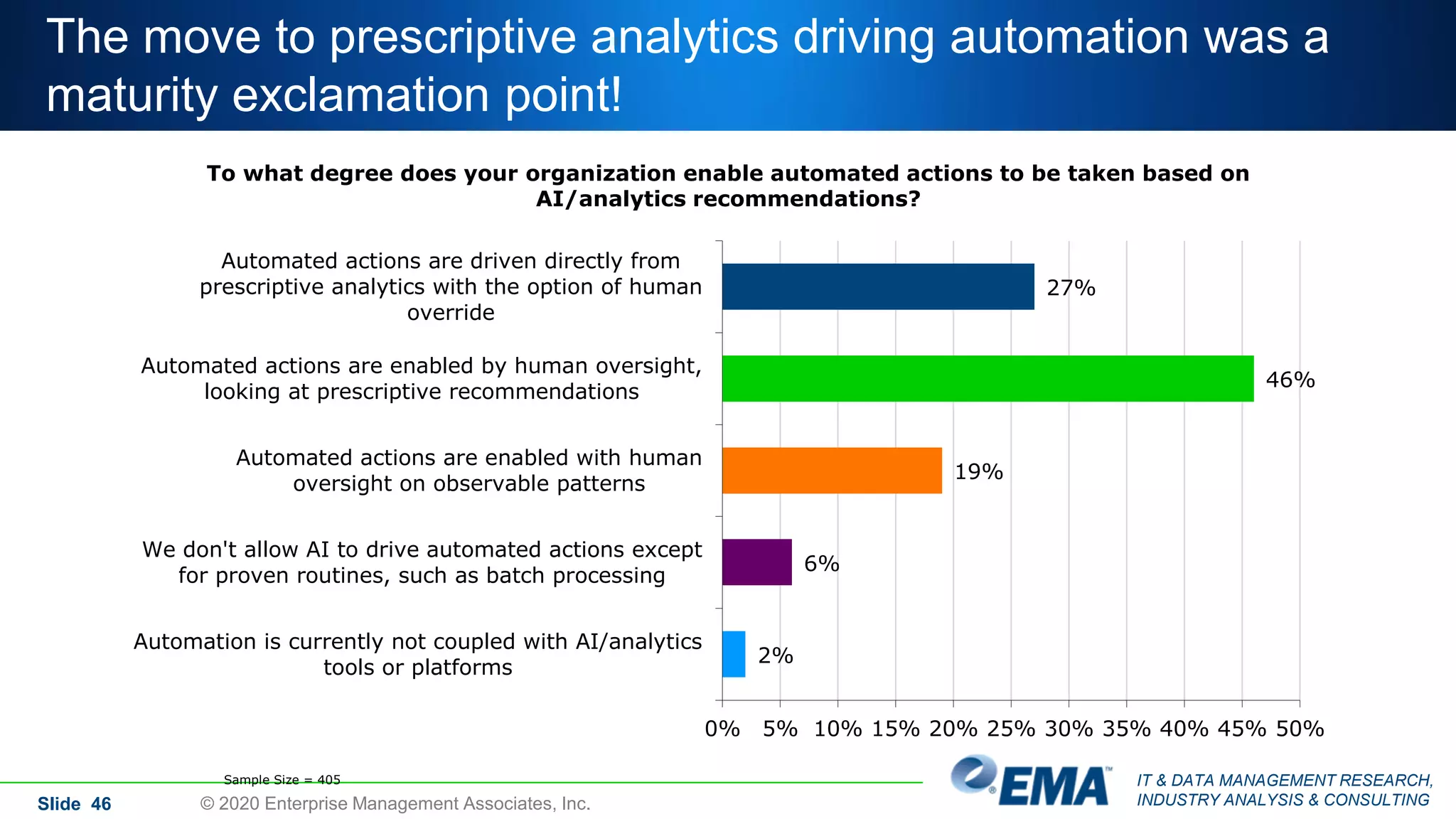
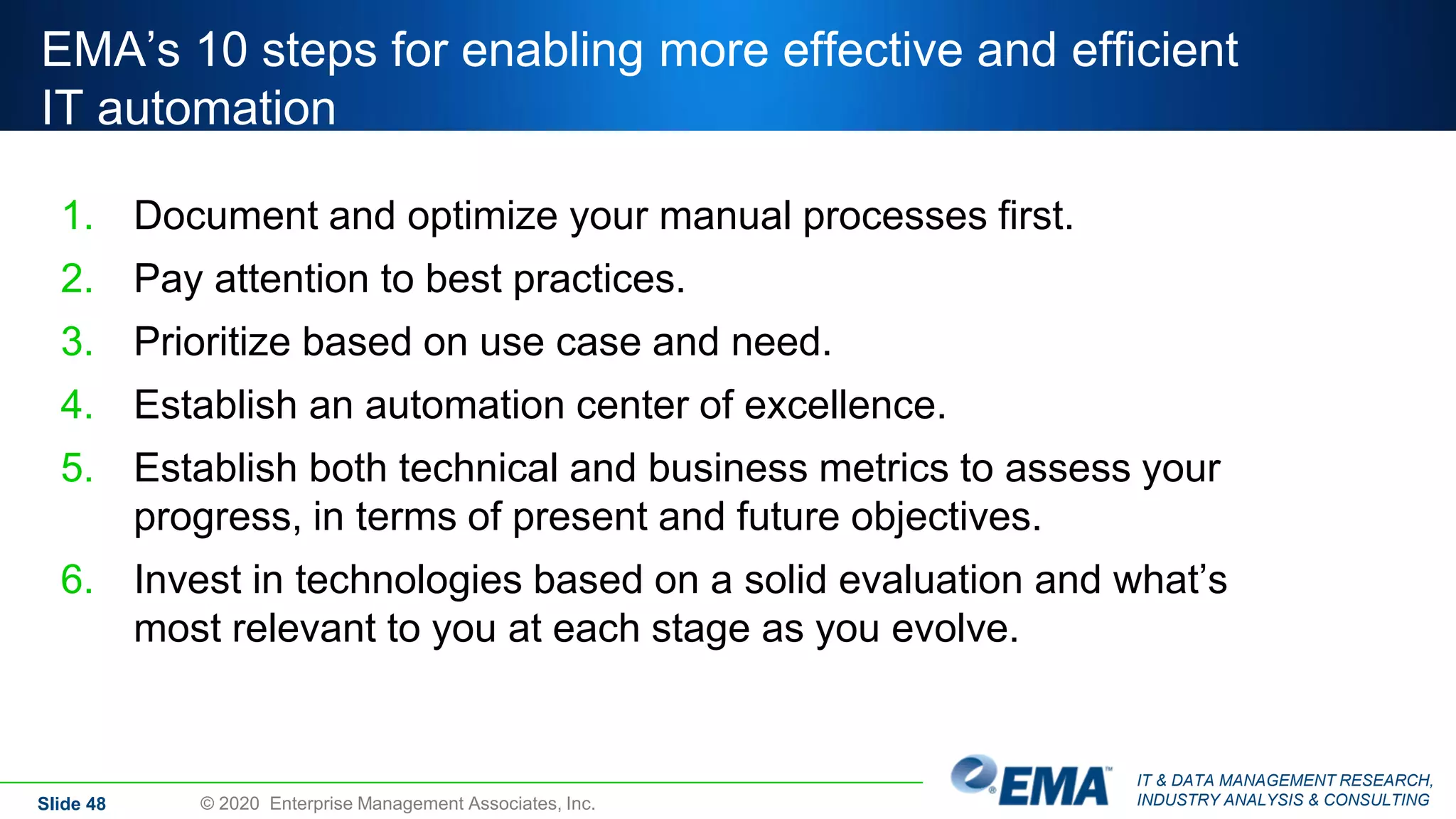
The document presents findings from a global survey analyzing the state of data-driven IT automation among organizations, with 405 respondents participating. Key insights include that 90% of organizations prioritize integrating AI with automation, while common obstacles to automation include product complexity and resistance to change. The report highlights the strategic importance of IT automation in various use cases, underscoring the need for effective integration and management to enhance operational efficiencies.