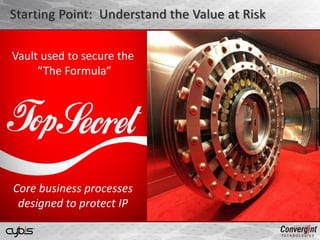
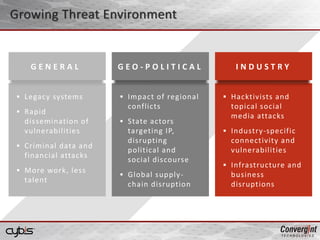
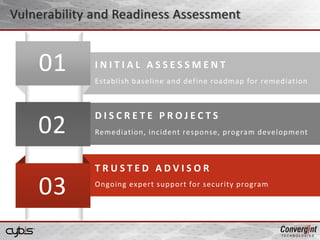
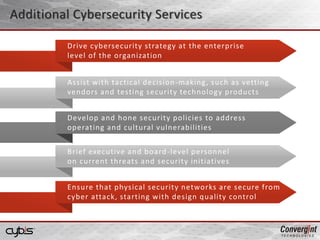
Agency GradeTM Cybersecurity Consulting provides cybersecurity consulting services from former NSA, CIA, DOD cybersecurity operators to help organizations assess vulnerabilities, design security programs, and respond to threats. They serve national security agencies and large companies. Their services include vulnerability assessments, insider threat program design, security program consulting, training, and incident response. They help clients think like attackers and provide vendor-agnostic recommendations and long-term support.