Crossing the chasm jeoffrey moore powerpoint ppt templates.
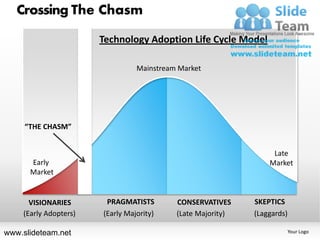
- 1. Crossing The Chasm Technology Adoption Life Cycle Model Mainstream Market “THE CHASM” Late Early Market CHASM Market VISIONARIES PRAGMATISTS CONSERVATIVES SKEPTICS (Early Adopters) (Early Majority) (Late Majority) (Laggards) www.slideteam.net Your Logo
- 2. Crossing The Chasm Technology Adoption Life Cycle Model Crossing The Chasm between Visionaries and Pragmatists “THE CHASM” TECHLES PRAGMATISTS CONSERVATIVES SKEPTICS (Innovators) (Early Majority) (Late Majority) (Laggards) VISIONARIES www.slideteam.net (Early Adopters) Your Logo
- 3. Crossing The Chasm Technology Adoption Life Cycle Model Area under the curve represents No. Of Customers “THE CHASM” TECHLES PRAGMATISTS CONSERVATIVES SKEPTICS (Innovators) (Early Majority) (Late Majority) (Laggards) VISIONARIES www.slideteam.net Adopters) (Early Your Logo
- 4. Crossing The Chasm Technology Adoption Life Cycle Model Mainstream Market Early Market Late Market CONSERVATIVES VISIONARIES Hold on! Get Ahead! PRAGMATISTS “THE CHASM” TECHLES Stick with the SKEPTICS Try it! herd! No way! Innovators Early Majority Laggards 2.5% 34% Late Majority 16% Early Adopters 13.5% 34% www.slideteam.net Your Logo
- 5. MIND MAP - Icons USE THE ICONS TO EVALUATE AND PRIORITIZE THE IDEAS 11 12 1 10 2 9 3 8 4 7 5 6 www.slideteam.net
- 6. Crossing The Chasm Technology Adoption Life Cycle Model Diagnose and Adapt as Markets Evolve Main Street Tornado “THE CHASM” Total Early Assimilation Market Bowling Alley TECHLES PRAGMATISTS CONSERVATIVES SKEPTICS (Innovators) (Early Majority) (Late Majority) (Laggards) VISIONARIES www.slideteam.net (Early Adopters) Your Logo
- 7. Crossing The Chasm Early Majority 34% The Chasm Early Early Adopters Adopters 13.5% 13.5% Innovators 2.5% Innovators 2.5% Innovators 2.5% www.slideteam.net Your Logo
- 8. Crossing The Chasm Technology Adoption Life Cycle Model How do you create a beachhead to the chasm? THE CHASM TECHLES PRAGMATISTS CONSERVATIVES SKEPTICS (Innovators) (Early Majority) (Late Majority) (Laggards) VISIONARIES www.slideteam.net (Early Adopters) Your Logo
- 9. Crossing The Chasm Technology Adoption Life Cycle Model VISIONARIES (Early CONSERVATIVES (Late Majority Adopters) & Laggards) Product Company Mainstream Market Developing The Developing The Early Market Consumer’s Key Focus Market Technology (Early TECHLES (Innovator) PRAGMATISTS Majority) Consumer’s Consumer’s role at Characteristics adapting new technology www.slideteam.net Your Logo
- 10. Crossing The Chasm 100 Market Share % 75 “THE CHASM” 50 25 0 Innovators Early Majority Laggards 2.5% Early 34% Late Majority 16% Adopters 34% www.slideteam.net 13.5% Your Logo
- 11. Crossing The Chasm “THE CHASM” www.slideteam.net Your Logo
- 12. Crossing The Chasm “THE CHASM” www.slideteam.net Your Logo
- 13. Crossing The Chasm “THE CHASM” www.slideteam.net Your Logo
- 14. Crossing The Chasm USE THESE ICONS TO CONVEY IDEAS www.slideteam.net Your Logo
- 15. All images are 100% editable in Powerpoint “Change color, size and orientation of any icon to your liking” www.slideteam.net
- 16. Ungrouping the object 2 1 3 1. Right click the object. 2. Choose Group and then Ungroup. 3. Click beside the object and drag the arrow over it. www.slideteam.net
- 17. Edit Color 2 3 1 1. Select the shape to change the color and Right click the object( click any object which you want to change color) 2. Choose Format Shape in the dialog box. 3. Choose “Fill” in the Format Shape box then “Solid” or “Gradient” depending on the appearance of the object. Change colour as shown in the picture. www.slideteam.net
