The document outlines the implementation of a binary tree using a recursive approach, requiring specific Java files and folders. It details the programming structure, including classes for nodes and binary trees, with instructions to read and build a binary expression tree from an infix expression stored in a file. Additionally, it specifies testing methods for displaying and evaluating the constructed binary tree.
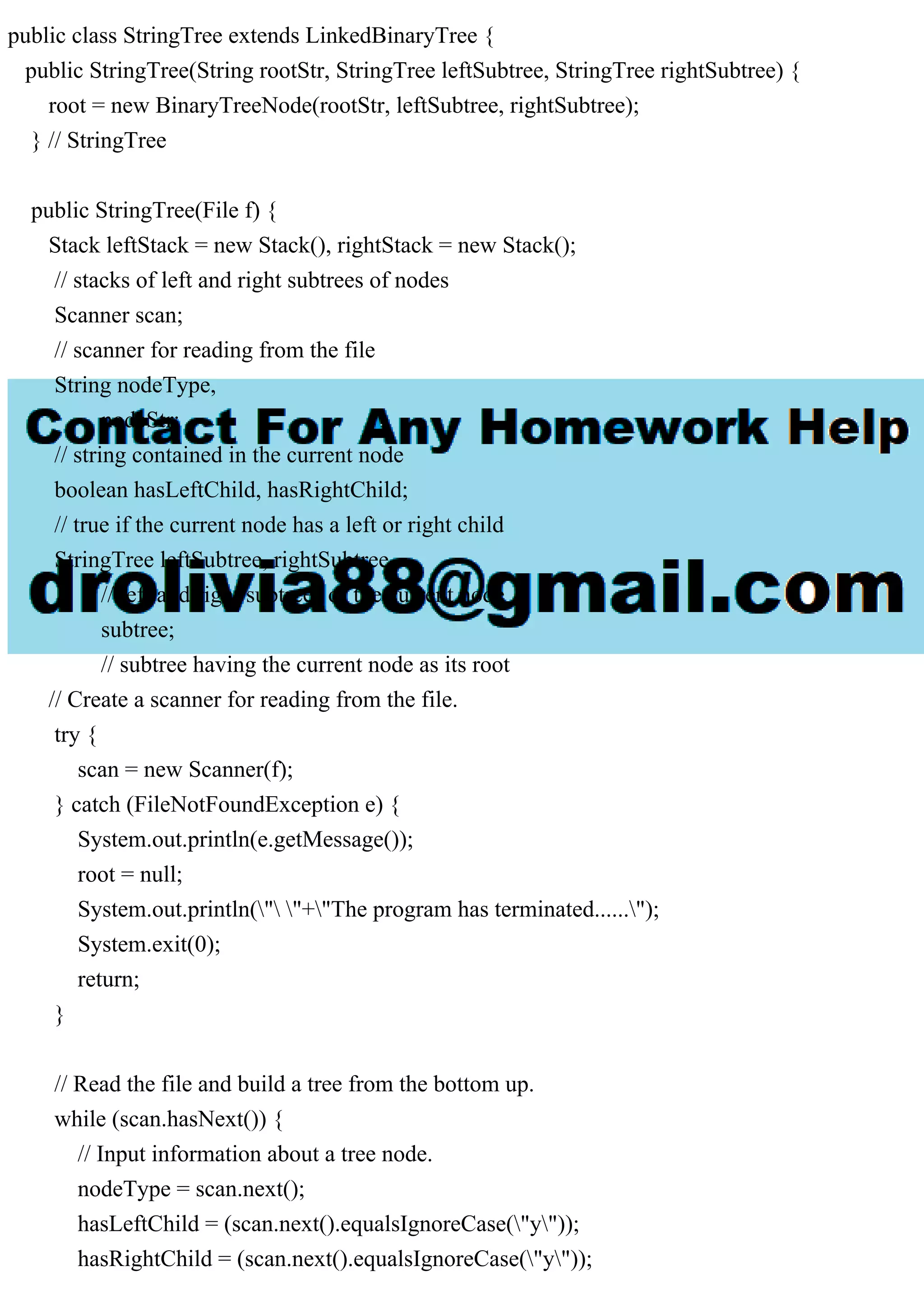
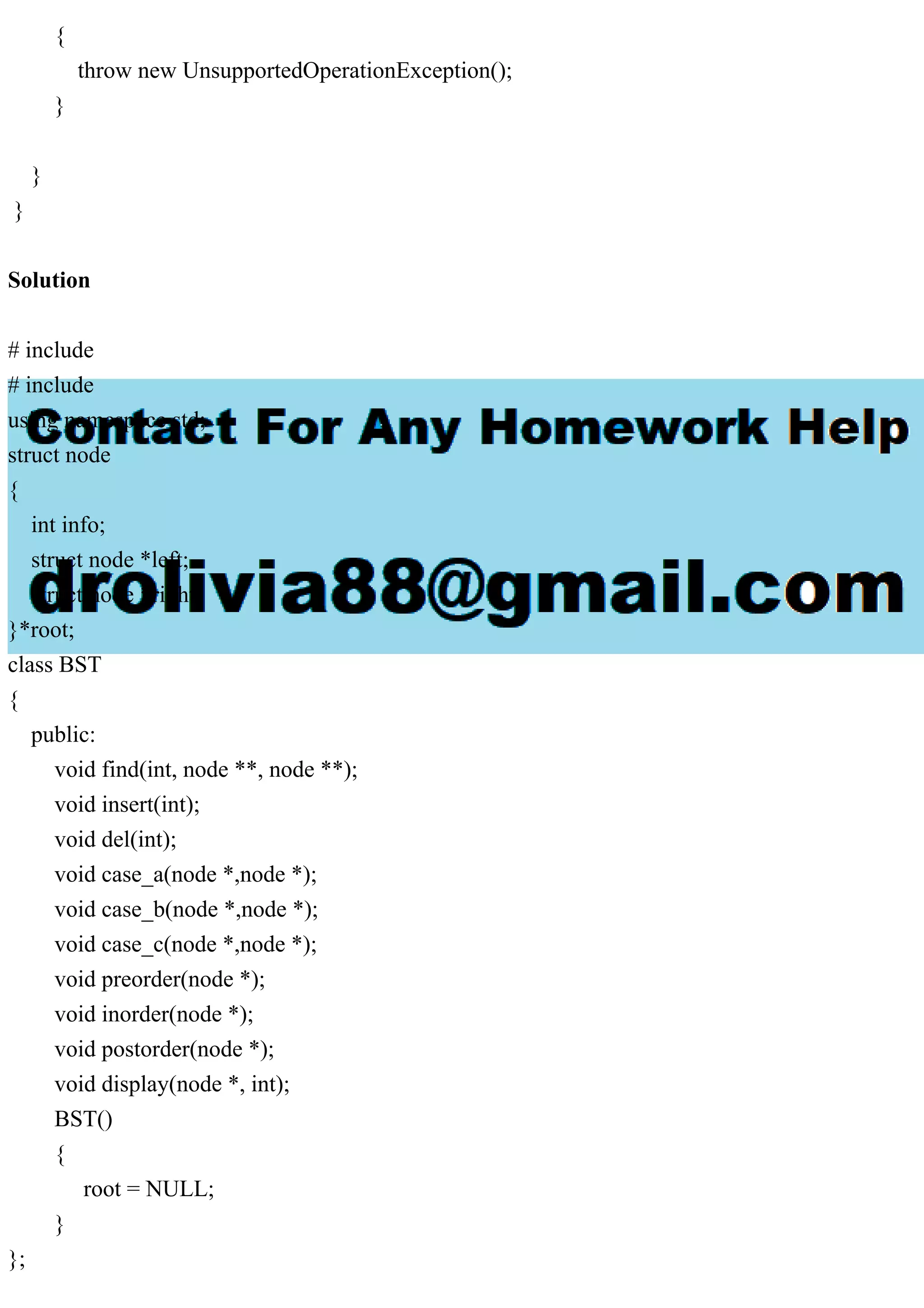
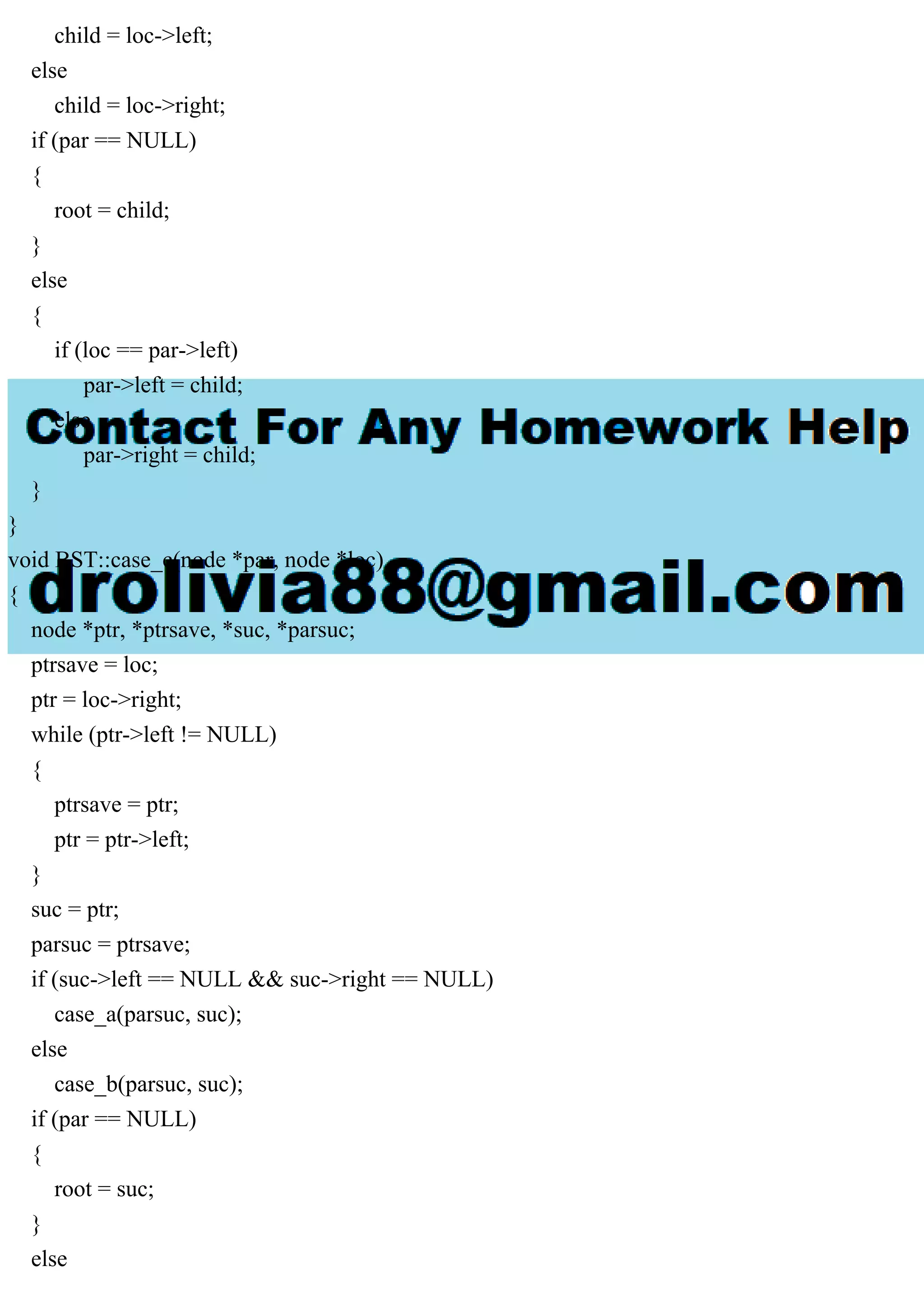
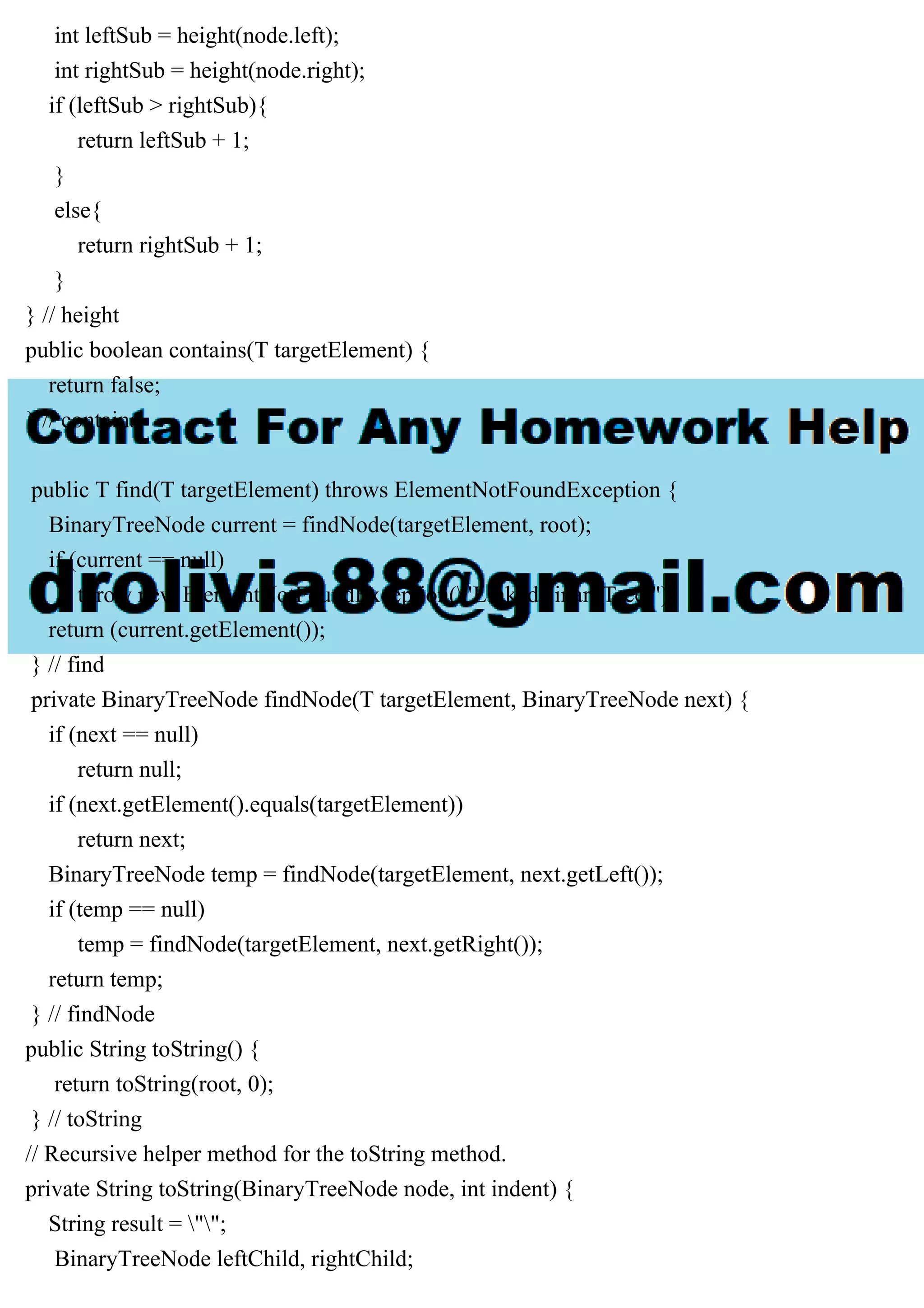
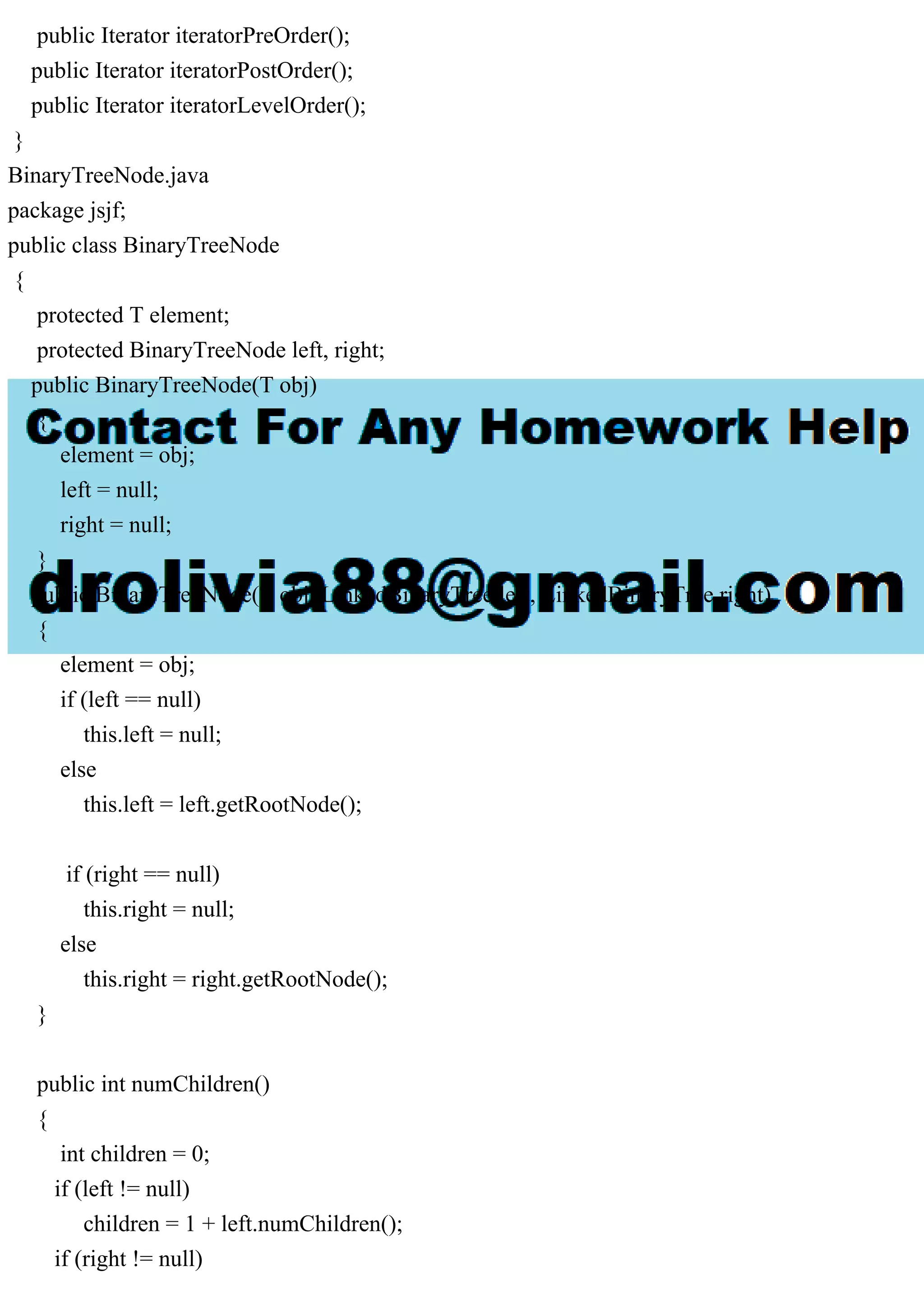
![nodeStr = scan.next();
// Determine the left and right subtrees of the subtree
// having the node as its root.
if (hasLeftChild)
leftSubtree = leftStack.pop();
else
leftSubtree = null;
if (hasRightChild)
rightSubtree = rightStack.pop();
else
rightSubtree = null;
// Create the subtree having the node as its root.
subtree = new StringTree(nodeStr, leftSubtree, rightSubtree);
// Push the subtree onto the appropriate stack or finish
// construction of the whole tree.
if (nodeType.equalsIgnoreCase("L"))
leftStack.push(subtree);
else if (nodeType.equalsIgnoreCase("R"))
rightStack.push(subtree);
else {
root = subtree.root;
break;
}
} // while
} // StringTree
public static void main(String[] args) {
Scanner scan = new Scanner(System.in);
// scanner to read keyboard input
String name;
// name of a tree description file
File f;
// the corresponding file object
StringTree tree;
// tree constructed from the file
// Input a tree description file name and create a
// corresponding file object.](https://image.slidesharecdn.com/createanimplementationofabinarytreeusingtherecursiveappr-230709065226-3ee8c2d3/75/Create-an-implementation-of-a-binary-tree-using-the-recursive-appr-pdf-3-2048.jpg)
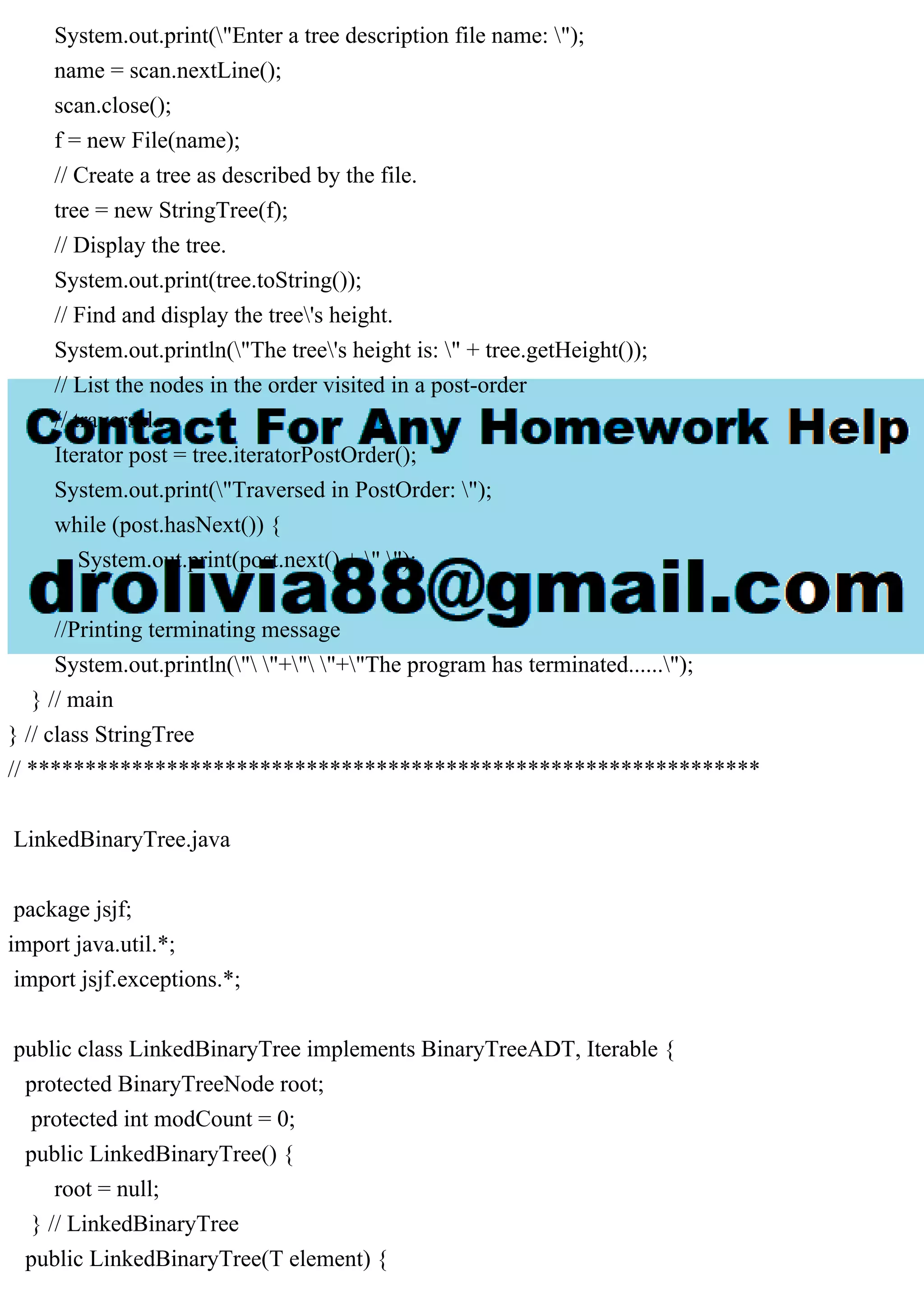
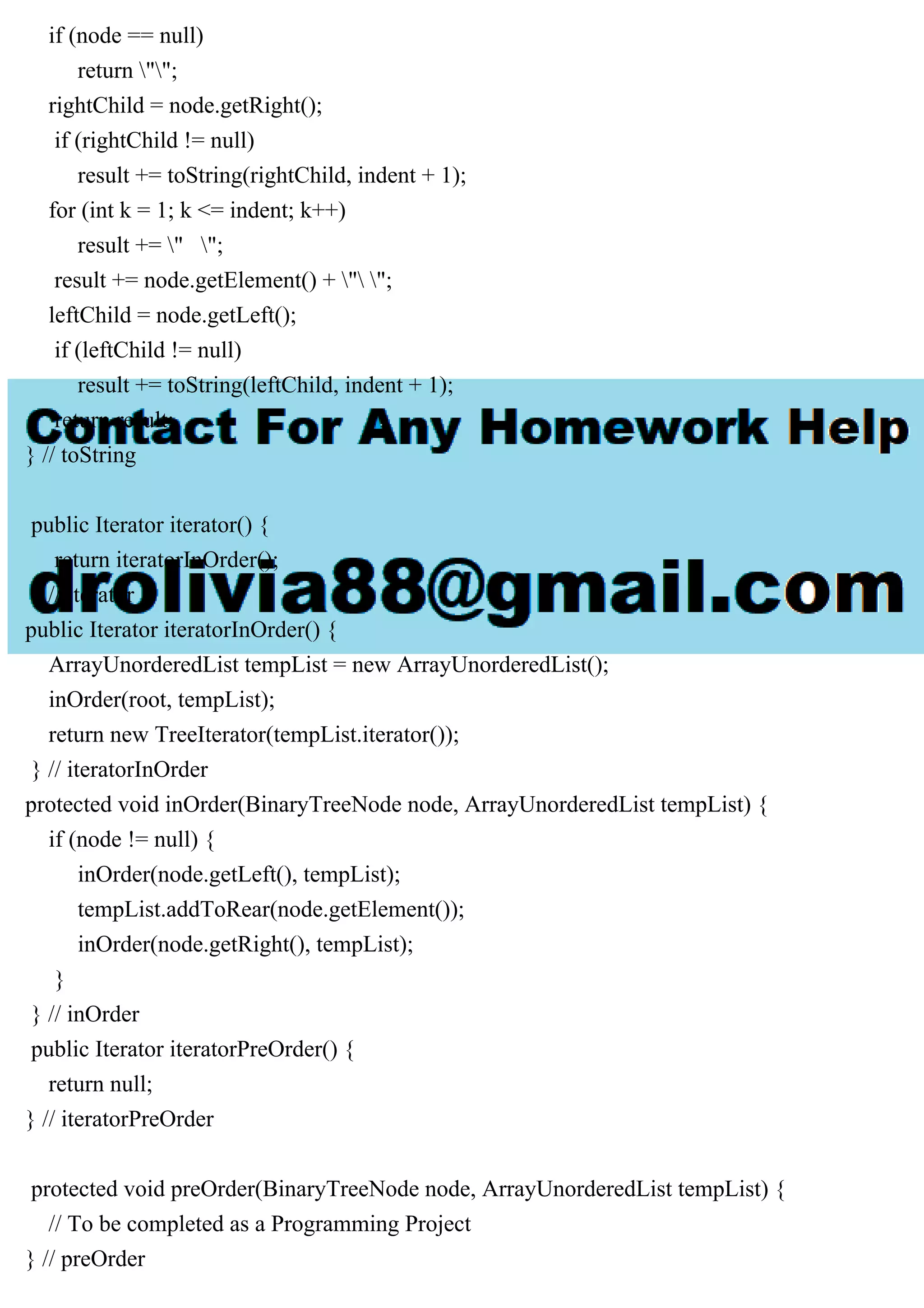
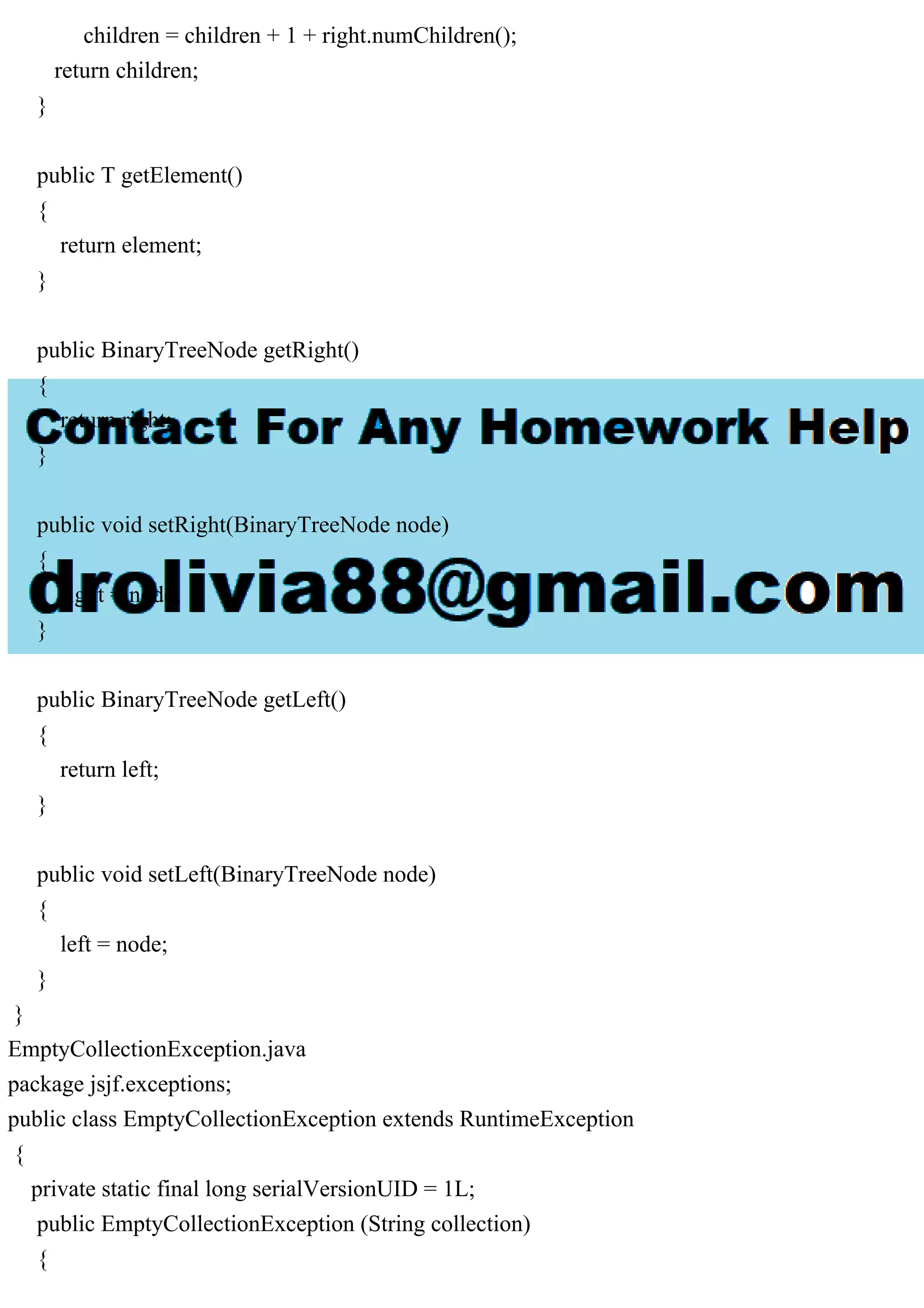
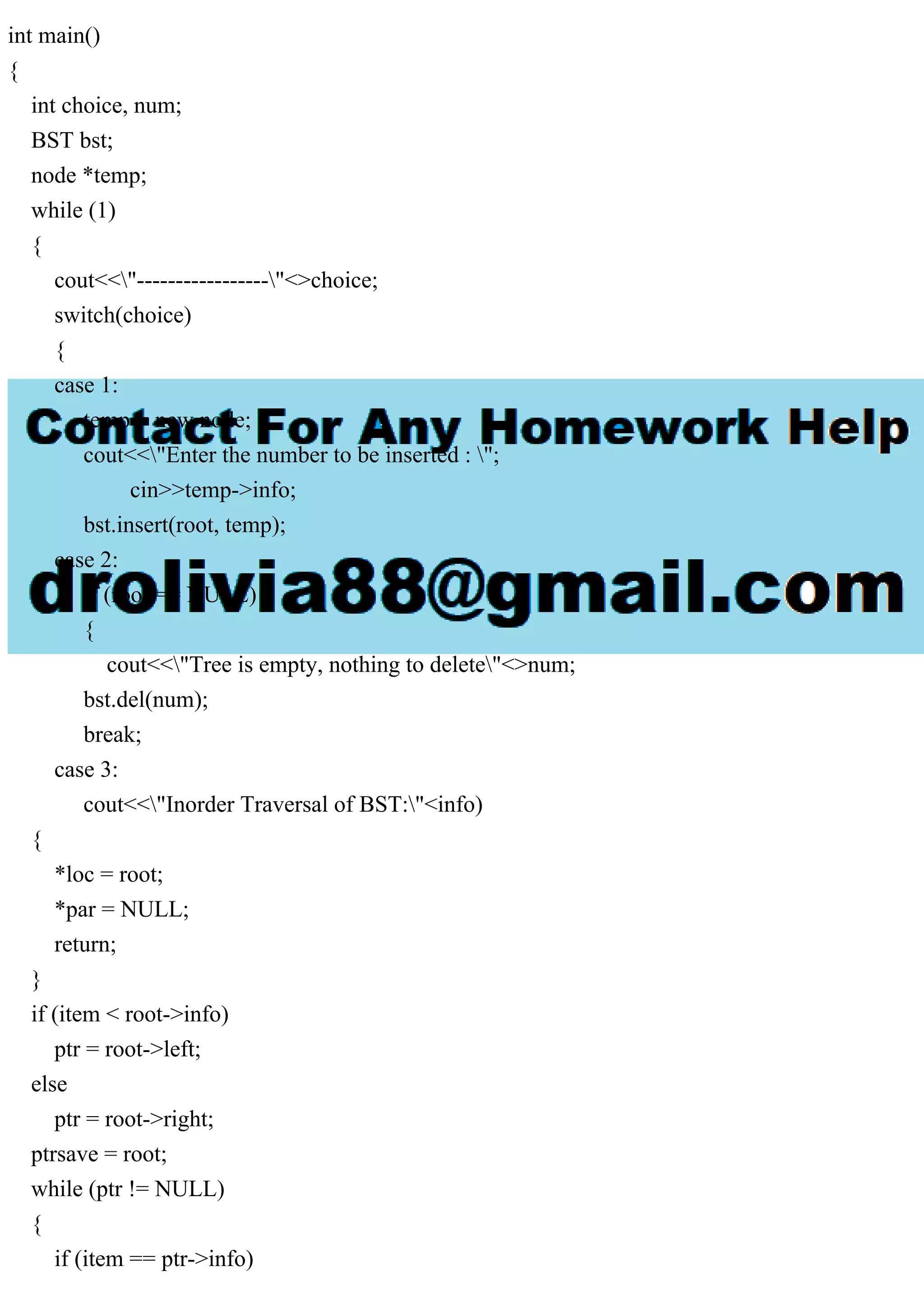
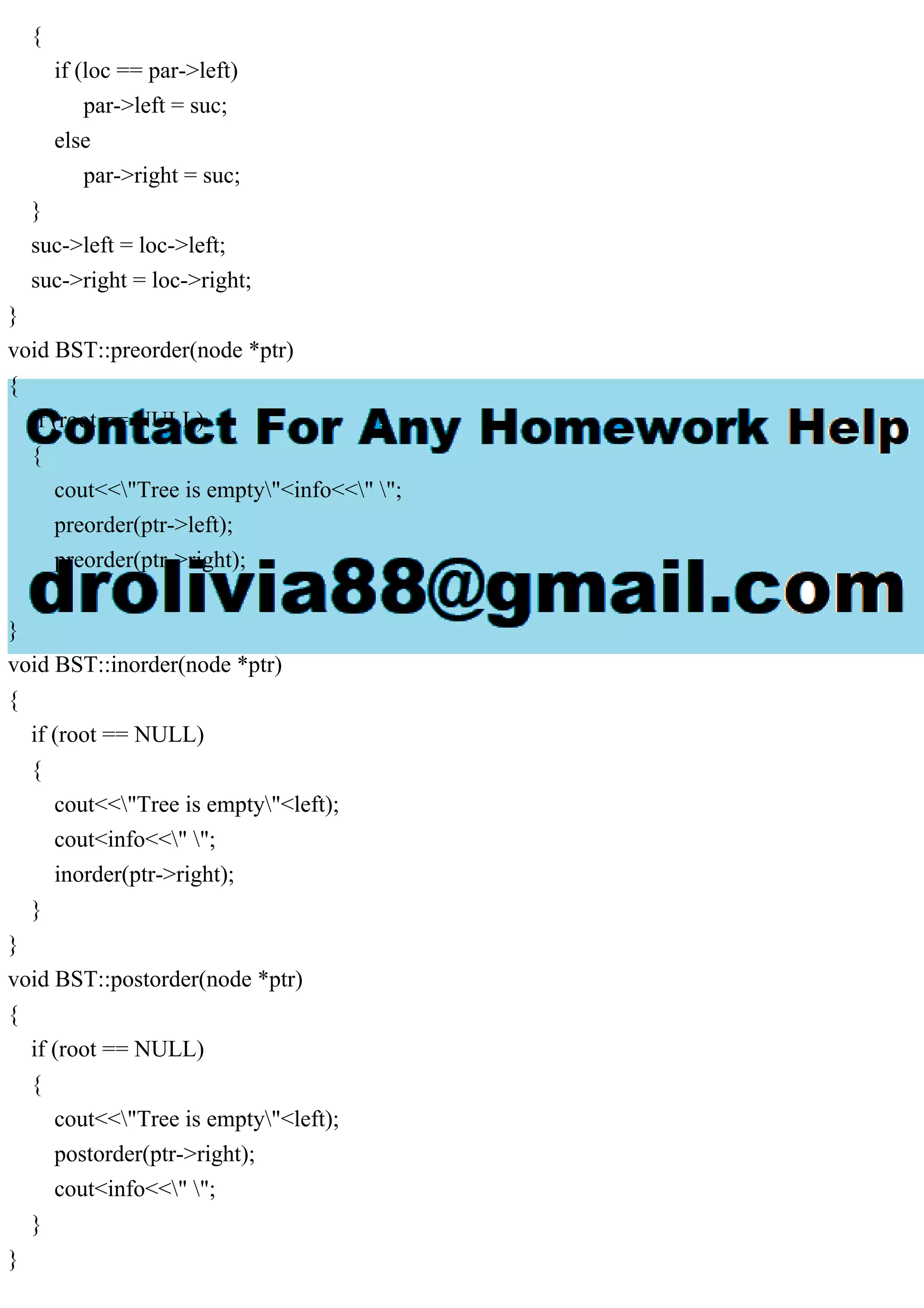
![super ("The " + collection + " is empty.");
}
}
ElementNotFoundException.java
package jsjf.exceptions;
public class ElementNotFoundException extends RuntimeException
{
private static final long serialVersionUID = 1L;
public ElementNotFoundException (String collection)
{
super ("The target element is not in this " + collection);
}
}
ArrayUnorderedList.java
package jsjf;
import jsjf.exceptions.*;
public class ArrayUnorderedList extends ArrayList
implements UnorderedListADT
{
public ArrayUnorderedList()
{
super();
}
public ArrayUnorderedList(int initialCapacity)
{
super(initialCapacity);
}
public void addToFront(T element)
{
if (size() == list.length)
expandCapacity();
// shift elements up one
for (int scan=rear; scan > 0; scan--)
list[scan] = list[scan-1];](https://image.slidesharecdn.com/createanimplementationofabinarytreeusingtherecursiveappr-230709065226-3ee8c2d3/75/Create-an-implementation-of-a-binary-tree-using-the-recursive-appr-pdf-13-2048.jpg)
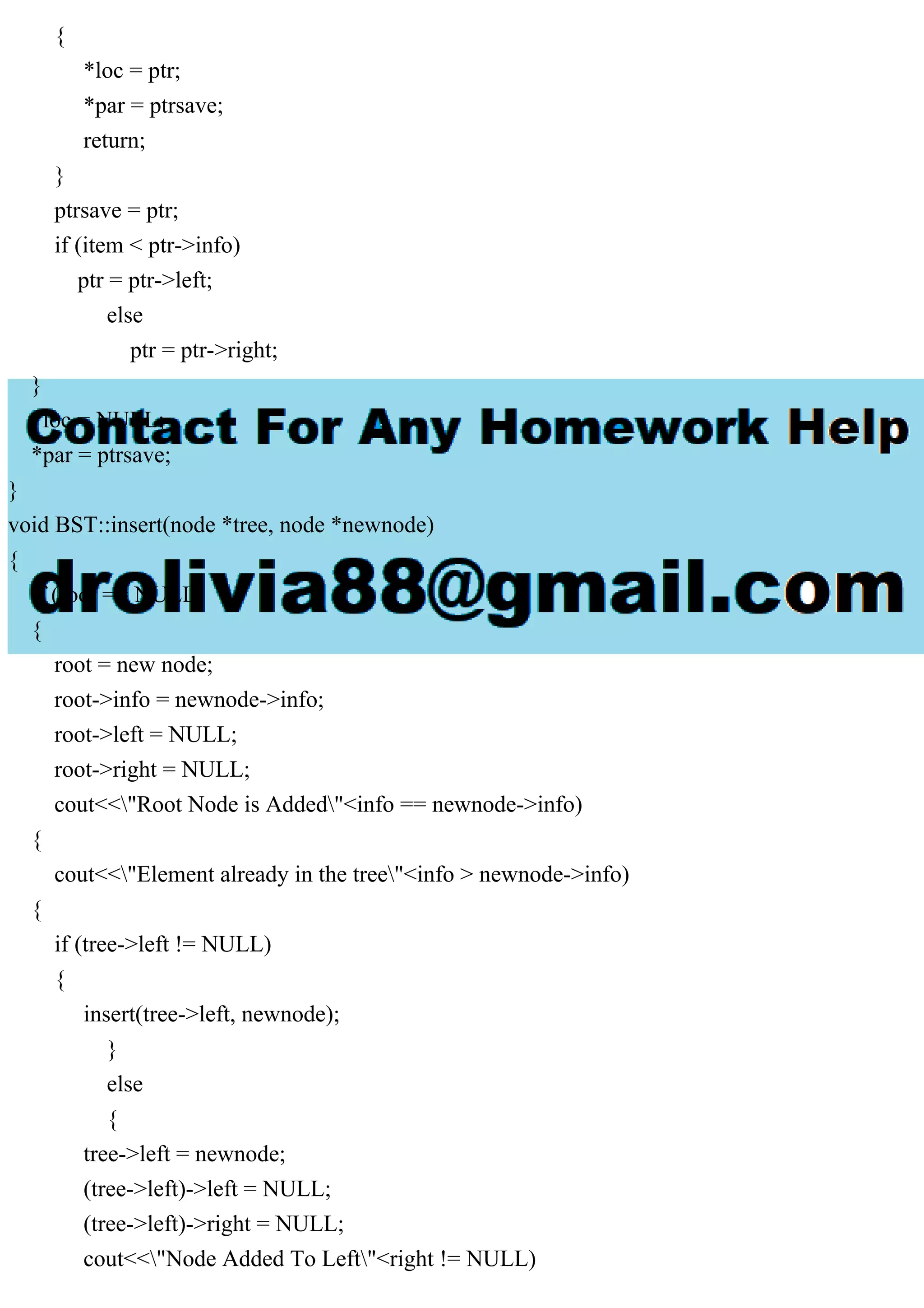
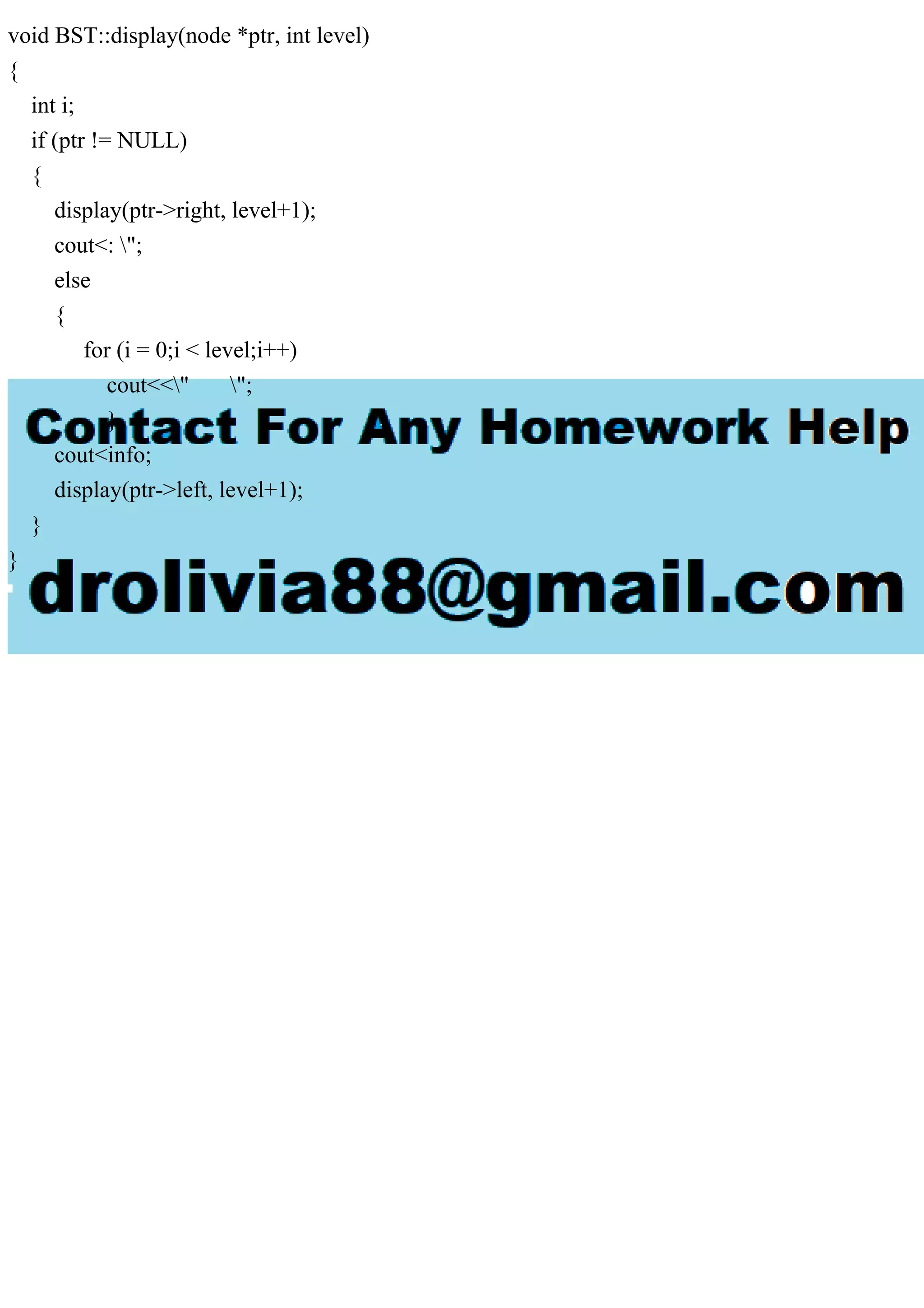
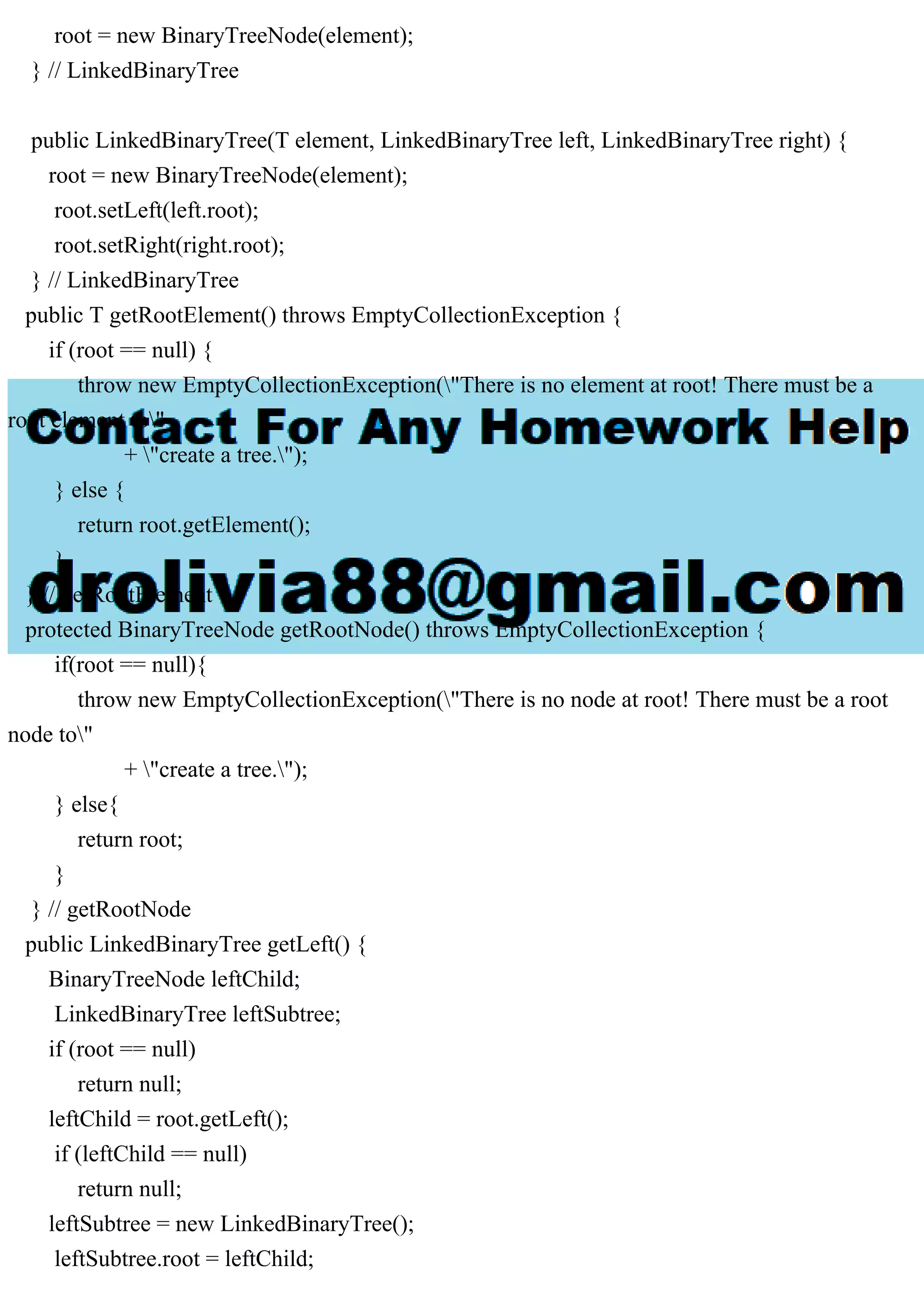
![list[0] = element;
rear++;
modCount++;
}
public void addToRear(T element)
{
if (size() == list.length)
expandCapacity();
list[rear] = element;
rear++;
modCount++;
}
public void addAfter(T element, T target)
{
if (size() == list.length)
expandCapacity();
int scan = 0;
// find the insertion point
while (scan < rear && !target.equals(list[scan]))
scan++;
if (scan == rear)
throw new ElementNotFoundException("UnorderedList");
scan++;
// shift elements up one
for (int shift=rear; shift > scan; shift--)
list[shift] = list[shift-1];
// insert element
list[scan] = element;
rear++;
modCount++;
}
}](https://image.slidesharecdn.com/createanimplementationofabinarytreeusingtherecursiveappr-230709065226-3ee8c2d3/75/Create-an-implementation-of-a-binary-tree-using-the-recursive-appr-pdf-14-2048.jpg)
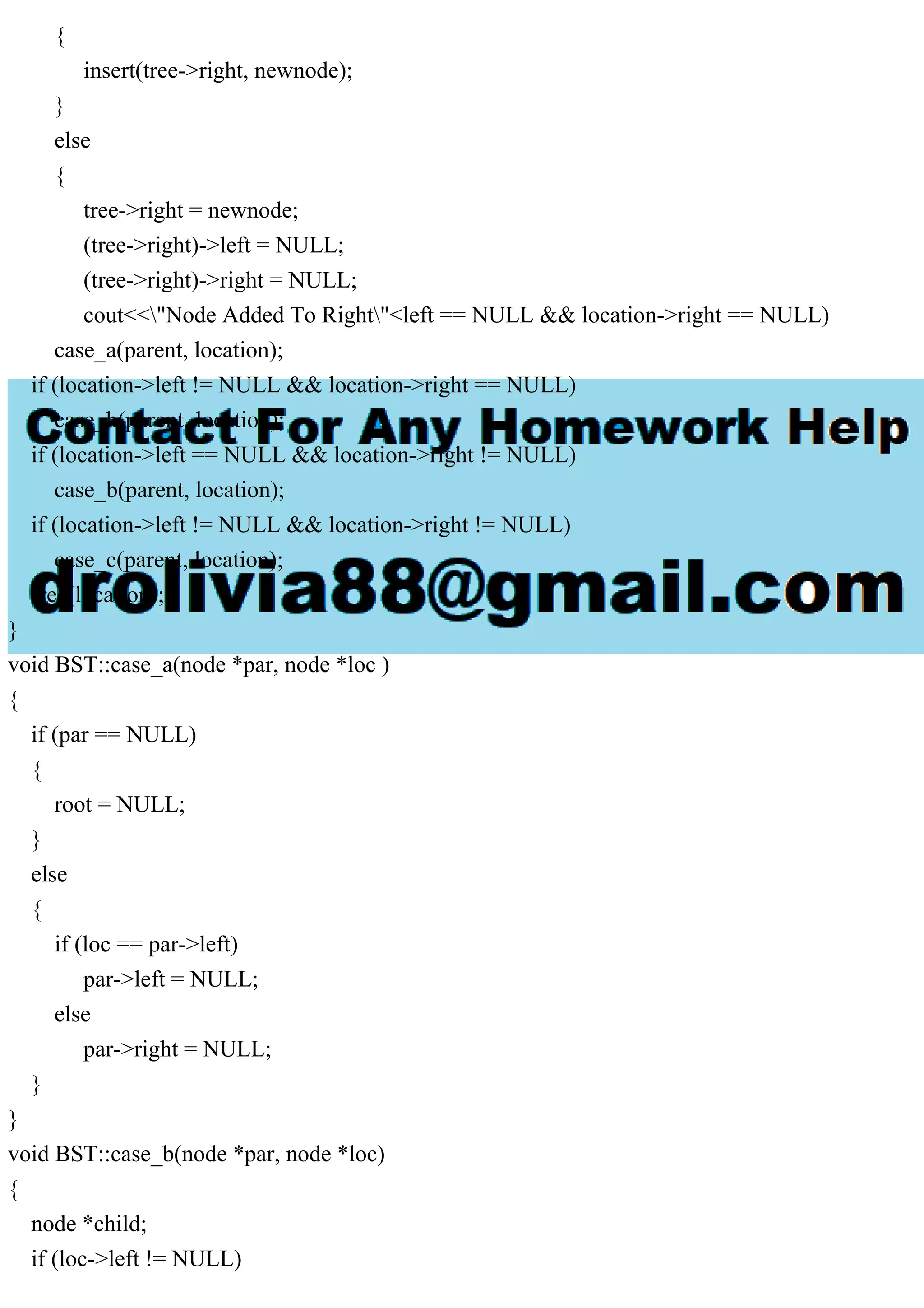
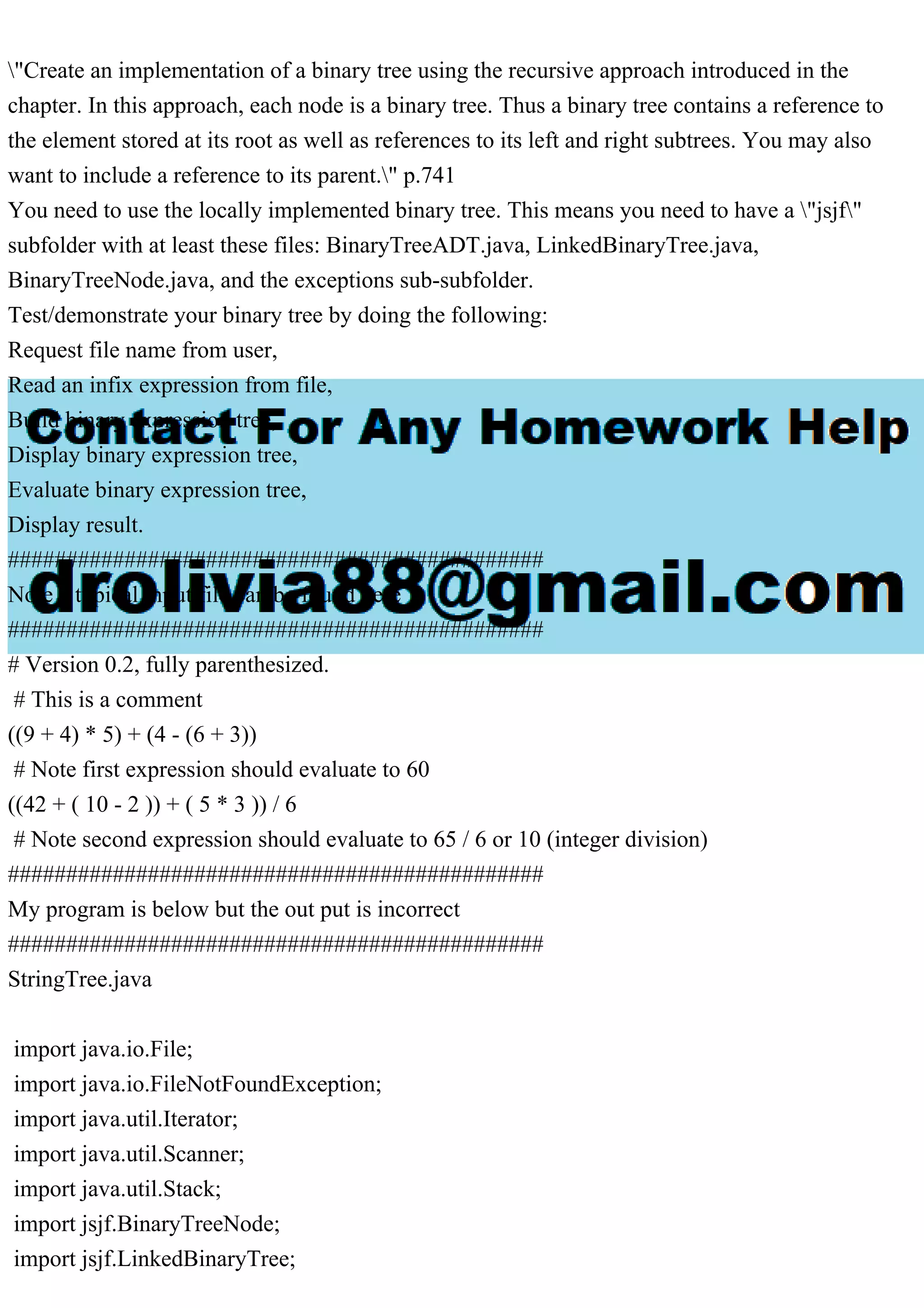
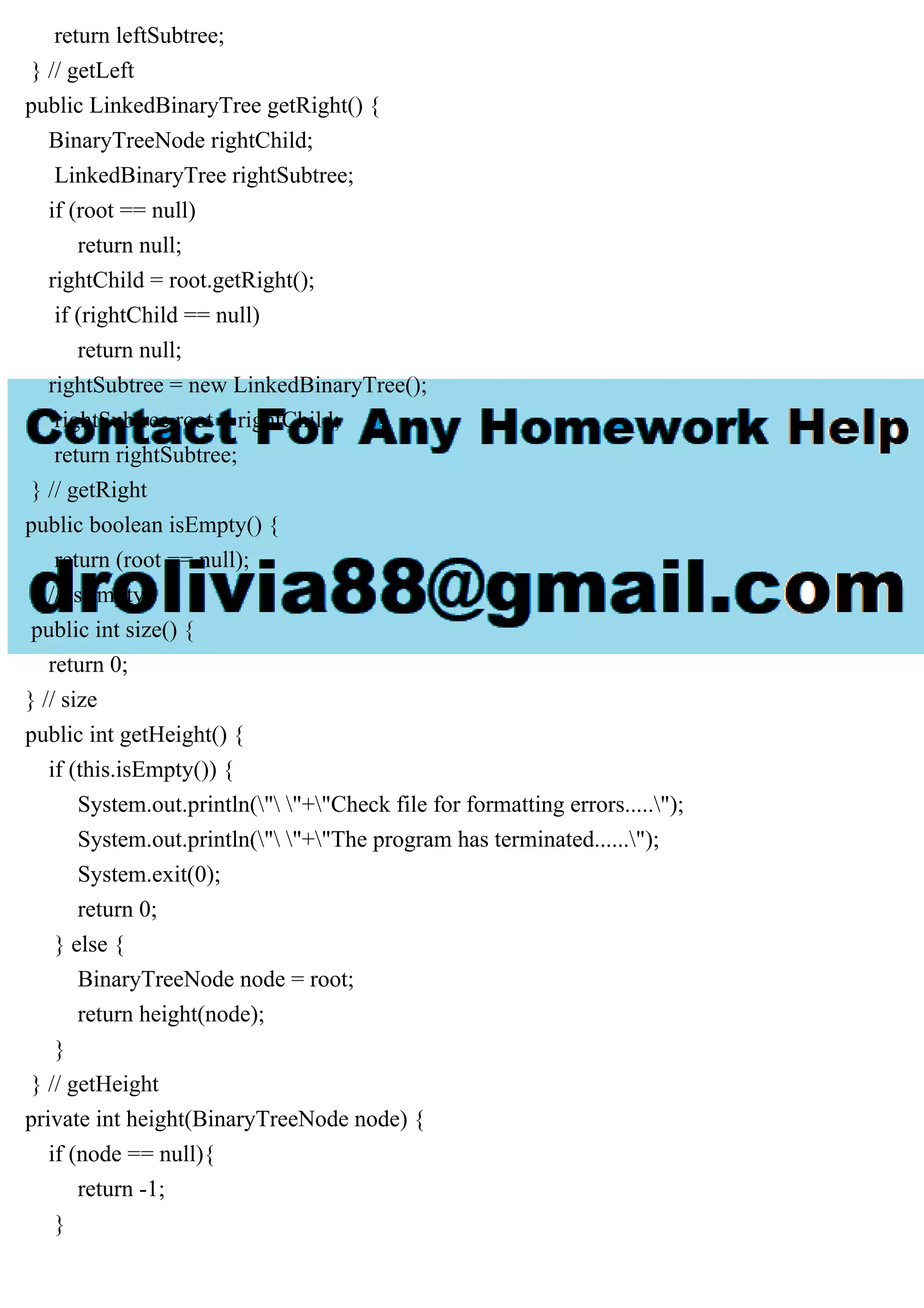
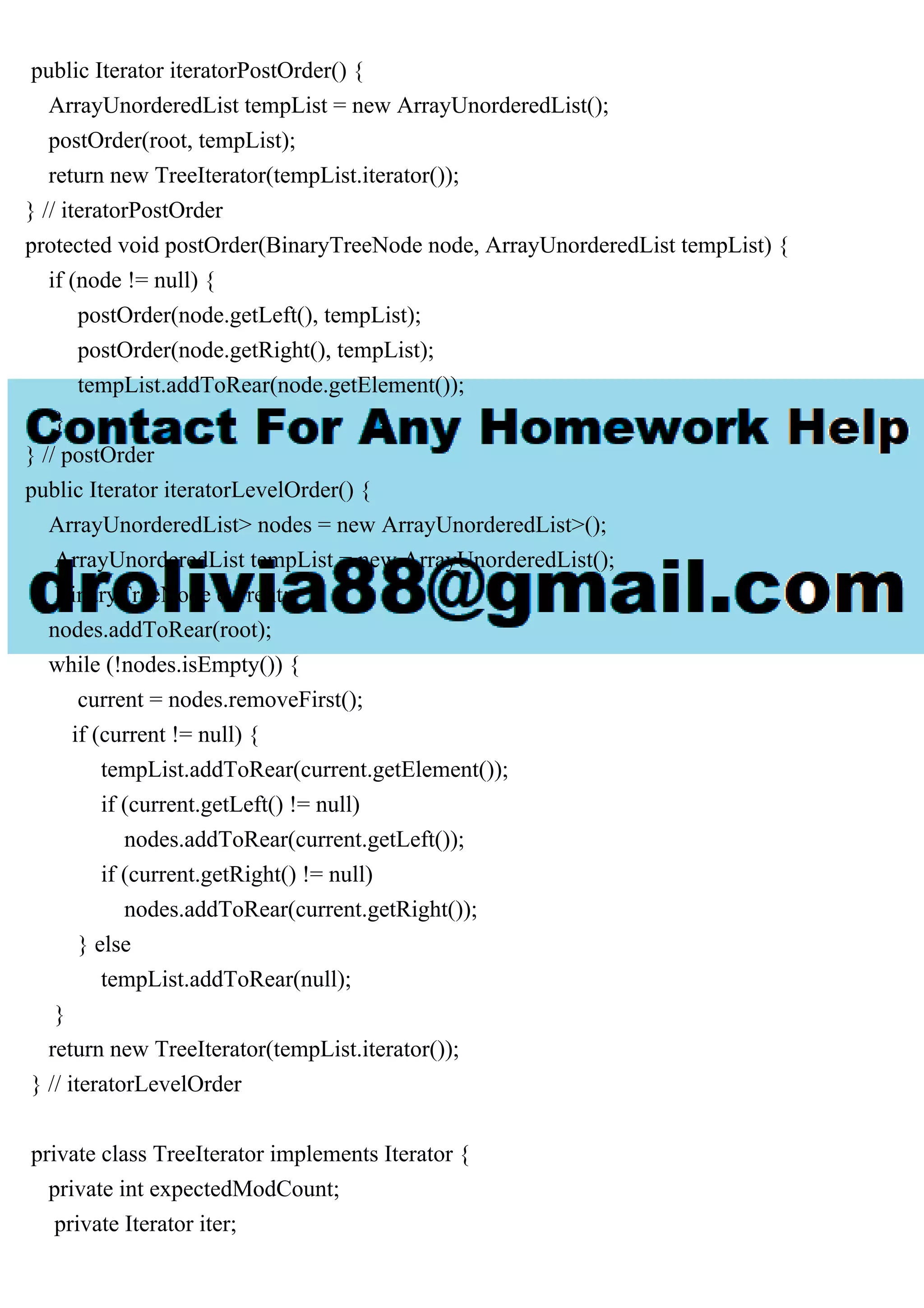
![UnorderedListADT.java
package jsjf;
public interface UnorderedListADT extends ListADT
{
public void addToFront(T element);
public void addToRear(T element);
public void addAfter(T element, T target);
}
ListADT.java
package jsjf;
import java.util.Iterator;
public interface ListADT extends Iterable
{
public T removeFirst();
public T removeLast();
public T remove(T element);
public T first();
public T last();
public boolean contains(T target);
public boolean isEmpty();
public int size();
public Iterator iterator();
public String toString();
}
ArrayList.java
package jsjf;
import jsjf.exceptions.*;
import java.util.*;
public abstract class ArrayList implements ListADT, Iterable
{
private final static int DEFAULT_CAPACITY = 100;
private final static int NOT_FOUND = -1;
protected int rear;
protected T[] list;](https://image.slidesharecdn.com/createanimplementationofabinarytreeusingtherecursiveappr-230709065226-3ee8c2d3/75/Create-an-implementation-of-a-binary-tree-using-the-recursive-appr-pdf-15-2048.jpg)
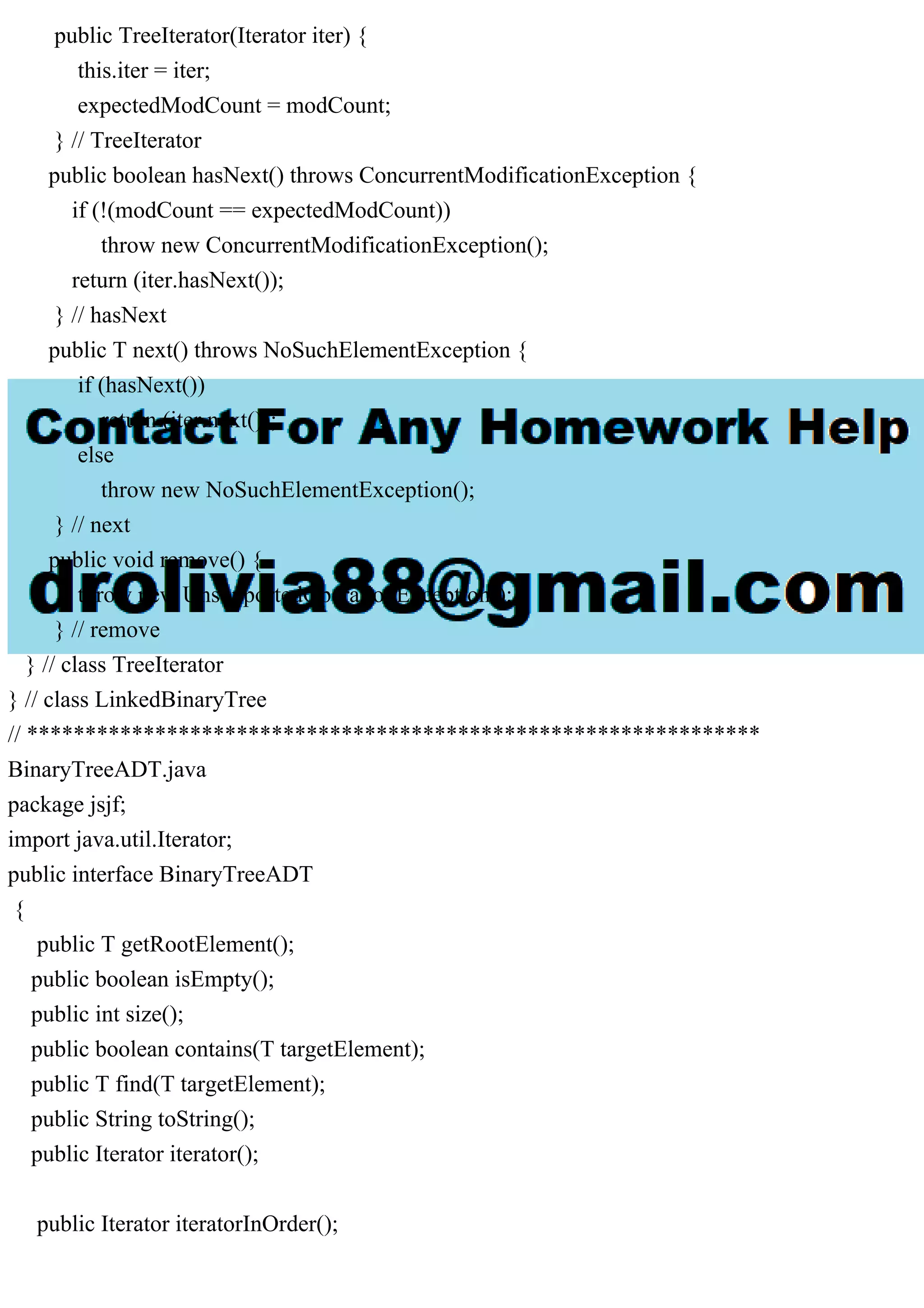
![protected int modCount;
public ArrayList()
{
this(DEFAULT_CAPACITY);
}
// Added.
@SuppressWarnings("unchecked")
public ArrayList(int initialCapacity)
{
rear = 0;
list = (T[])(new Object[initialCapacity]);
modCount = 0;
}
protected void expandCapacity()
{
list = Arrays.copyOf(list, list.length*2);
}
public T removeLast() throws EmptyCollectionException
{
if (isEmpty())
throw new EmptyCollectionException("ArrayList");
T result;
rear--;
result = list[rear];
list[rear] = null;
modCount++;
return result;
}
public T removeFirst() throws EmptyCollectionException
{
if (isEmpty())
throw new EmptyCollectionException("ArrayList");
T result = list[0];](https://image.slidesharecdn.com/createanimplementationofabinarytreeusingtherecursiveappr-230709065226-3ee8c2d3/75/Create-an-implementation-of-a-binary-tree-using-the-recursive-appr-pdf-16-2048.jpg)
![rear--;
/** shift the elements */
for (int scan=0; scan < rear; scan++)
list[scan] = list[scan+1];
list[rear] = null;
modCount++;
return result;
}
public T remove(T element)
{
T result;
int index = find(element);
if (index == NOT_FOUND)
throw new ElementNotFoundException("ArrayList");
result = list[index];
rear--;
// shift the appropriate elements
for (int scan=index; scan < rear; scan++)
list[scan] = list[scan+1];
list[rear] = null;
modCount++;
return result;
}
public T first() throws EmptyCollectionException
{
if (isEmpty())
throw new EmptyCollectionException("ArrayList");
return list[0];
}
public T last() throws EmptyCollectionException
{](https://image.slidesharecdn.com/createanimplementationofabinarytreeusingtherecursiveappr-230709065226-3ee8c2d3/75/Create-an-implementation-of-a-binary-tree-using-the-recursive-appr-pdf-17-2048.jpg)
![if (isEmpty())
throw new EmptyCollectionException("ArrayList");
return list[rear-1];
}
public boolean contains(T target)
{
return (find(target) != NOT_FOUND);
}
private int find(T target)
{
int scan = 0;
int result = NOT_FOUND;
if (!isEmpty())
while (result == NOT_FOUND && scan < rear)
if (target.equals(list[scan]))
result = scan;
else
scan++;
return result;
}
public boolean isEmpty()
{
return (rear == 0);
}
public int size()
{
return rear;
}
public String toString()
{
String result = "";
for (int scan=0; scan < rear; scan++)
result = result + list[scan] + " ";
return result;](https://image.slidesharecdn.com/createanimplementationofabinarytreeusingtherecursiveappr-230709065226-3ee8c2d3/75/Create-an-implementation-of-a-binary-tree-using-the-recursive-appr-pdf-18-2048.jpg)
![}
public Iterator iterator()
{
return new ArrayListIterator();
}
private class ArrayListIterator implements Iterator
{
int iteratorModCount;
int current;
public ArrayListIterator()
{
iteratorModCount = modCount;
current = 0;
}
public boolean hasNext() throws ConcurrentModificationException
{
if (iteratorModCount != modCount)
throw new ConcurrentModificationException();
return (current < rear);
}
public T next() throws ConcurrentModificationException
{
if (!hasNext())
throw new NoSuchElementException();
current++;
return list[current - 1];
}
public void remove() throws UnsupportedOperationException](https://image.slidesharecdn.com/createanimplementationofabinarytreeusingtherecursiveappr-230709065226-3ee8c2d3/75/Create-an-implementation-of-a-binary-tree-using-the-recursive-appr-pdf-19-2048.jpg)