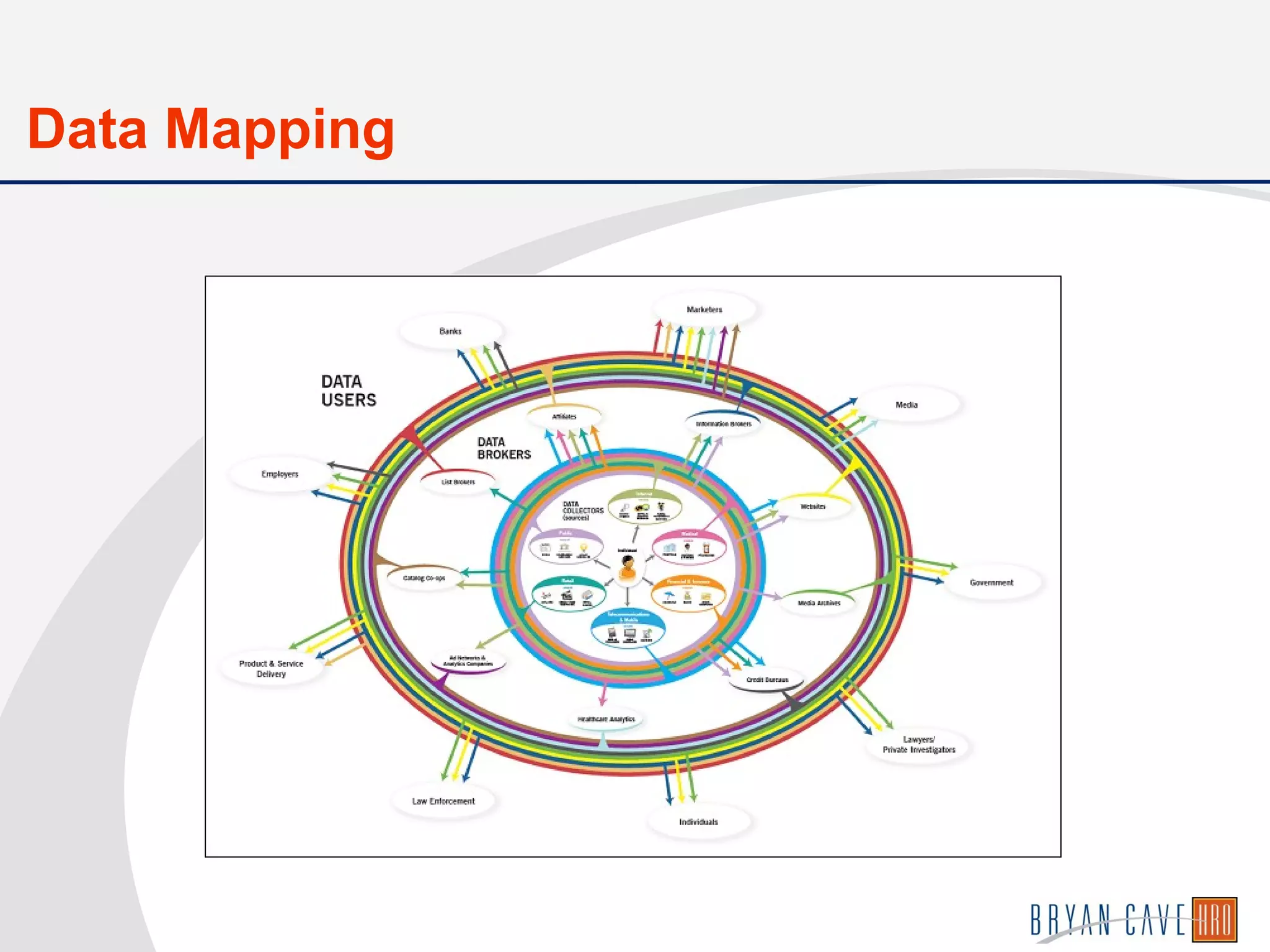
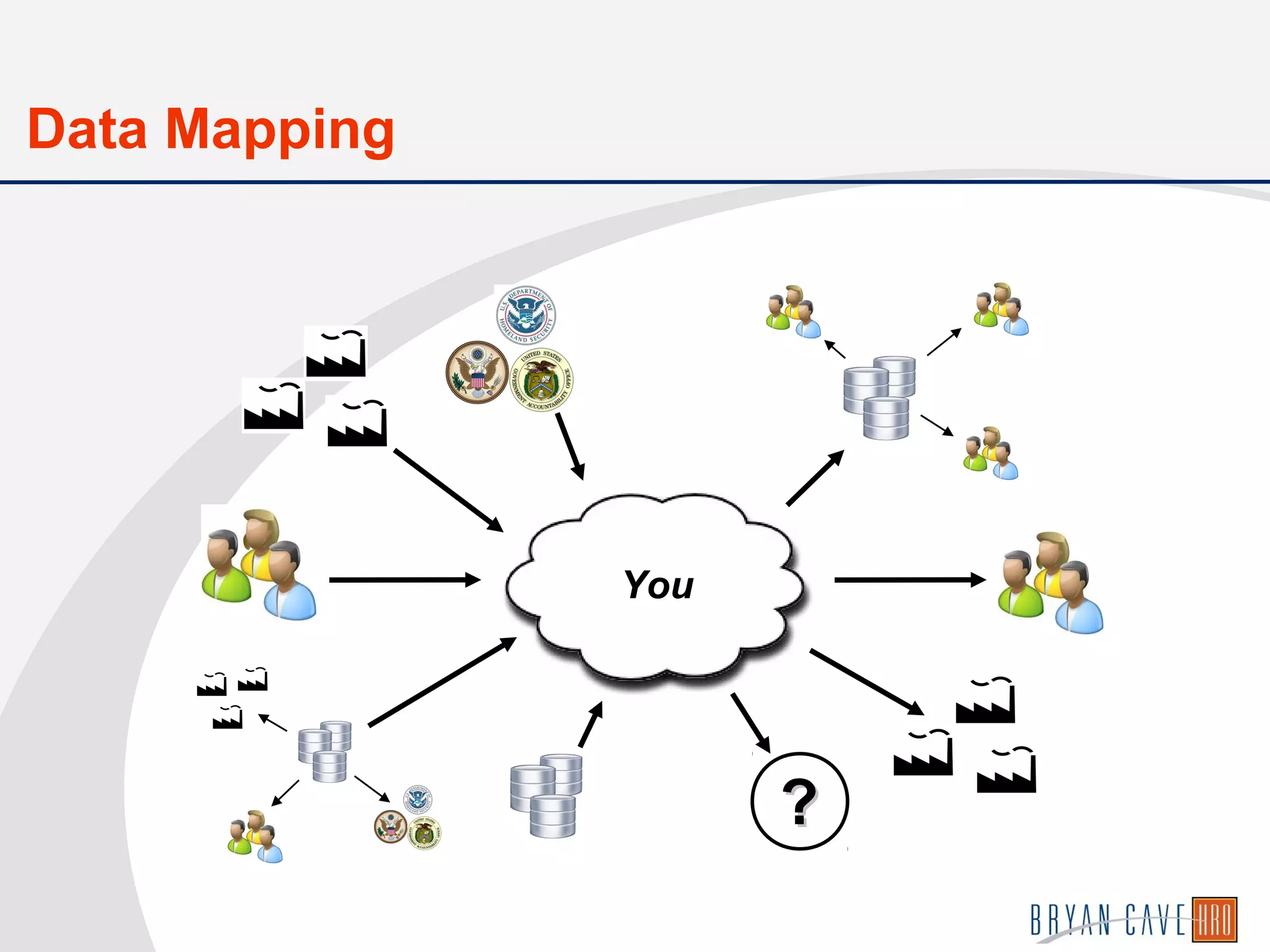
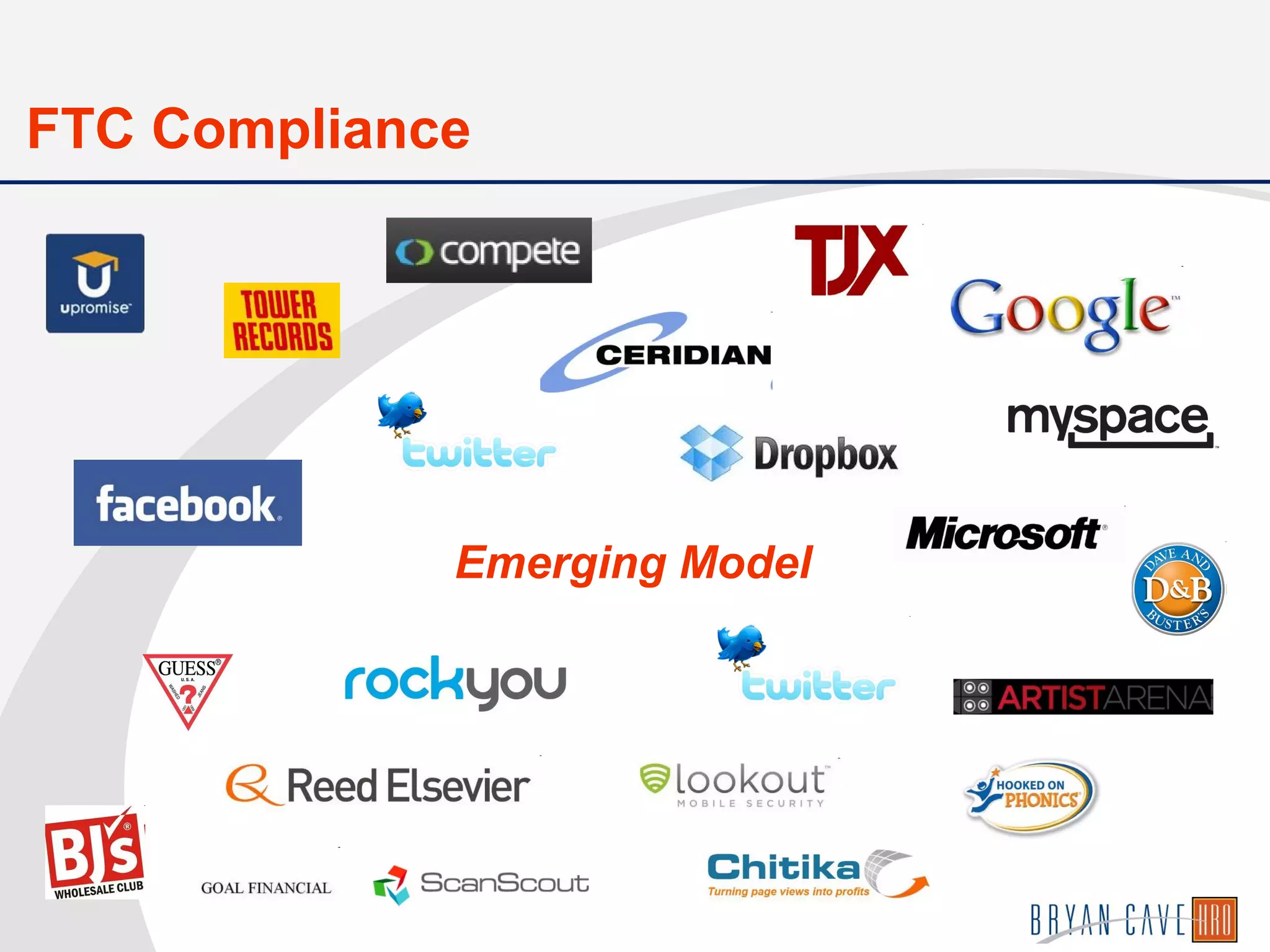
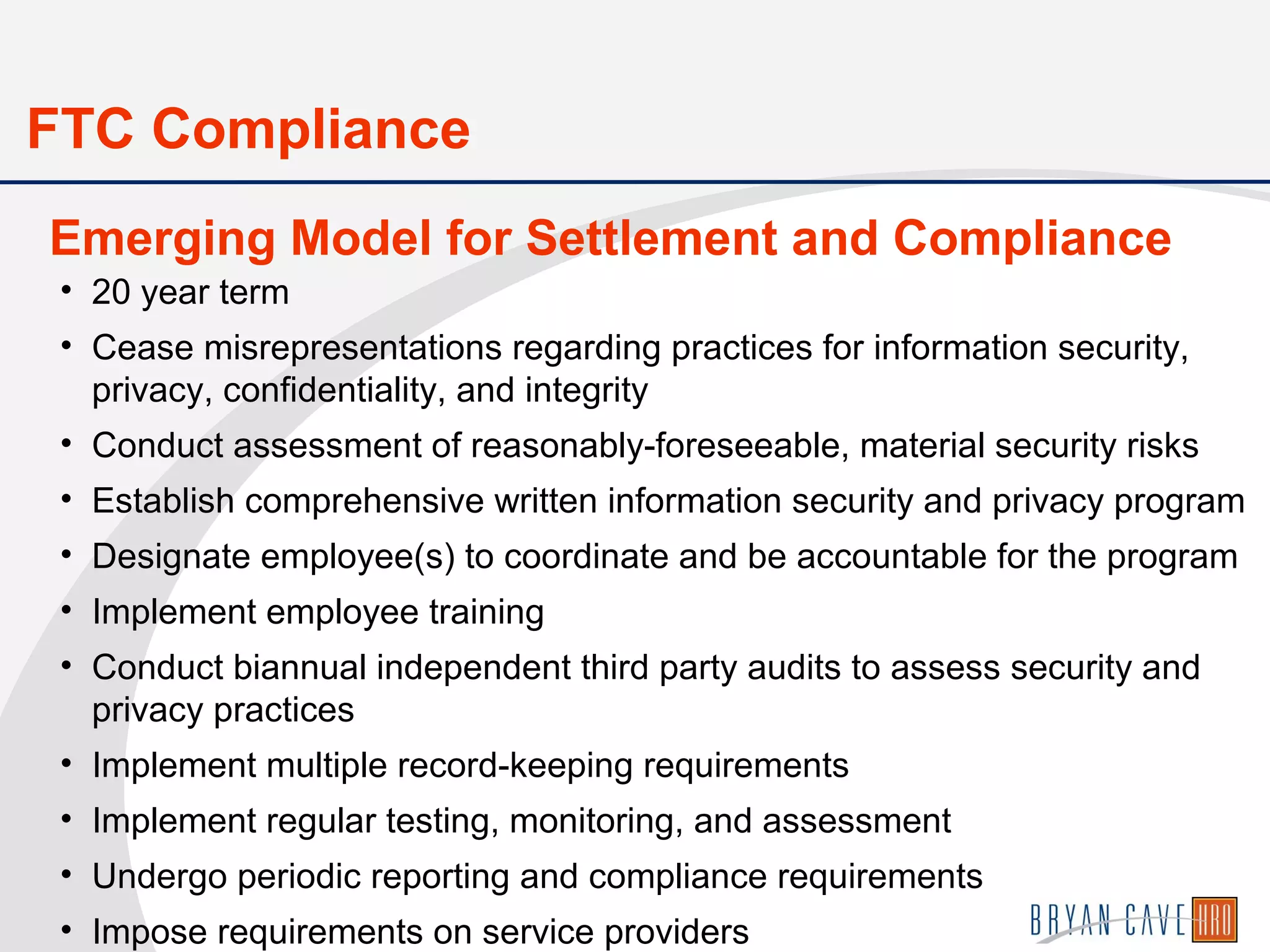
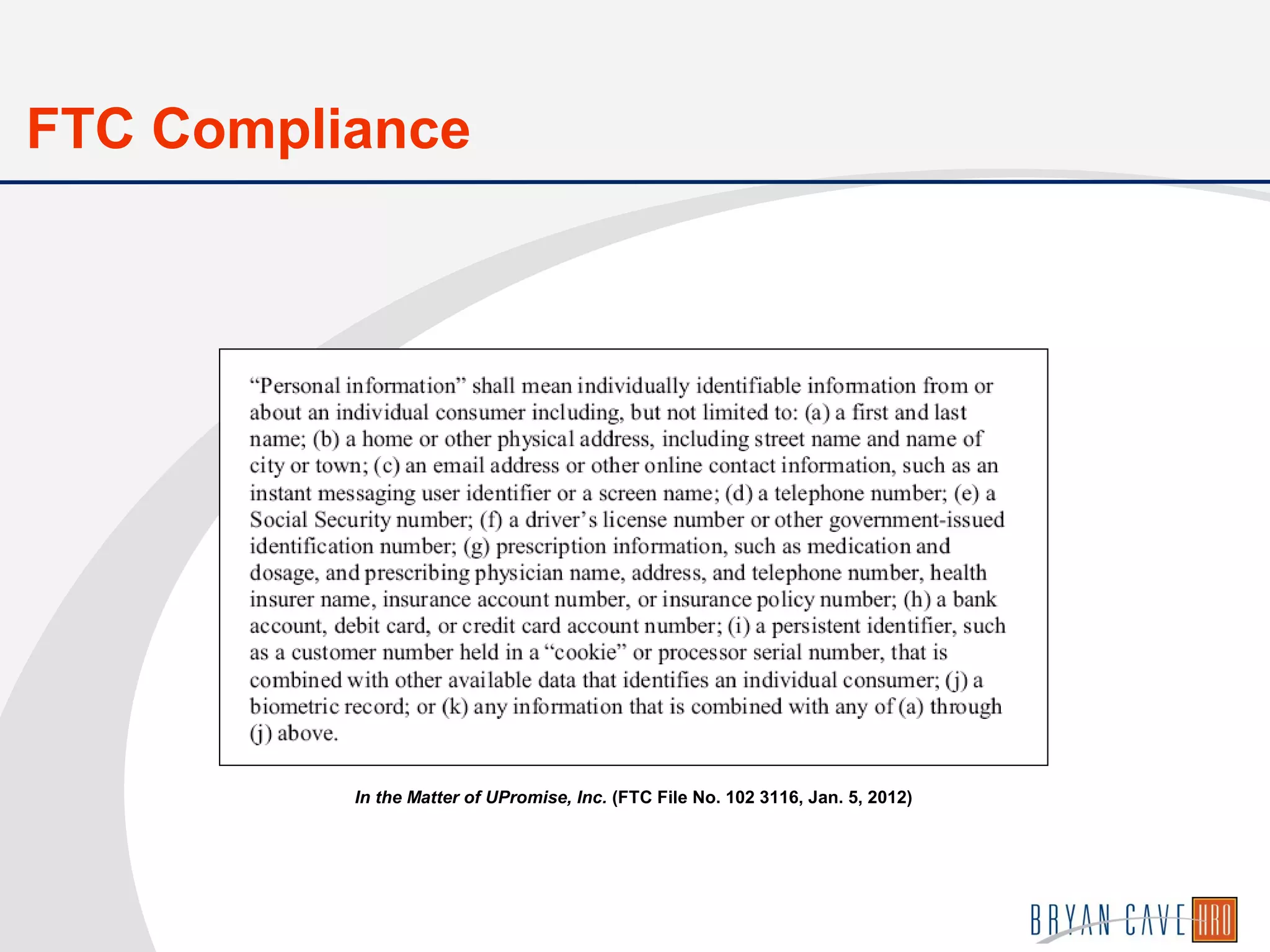
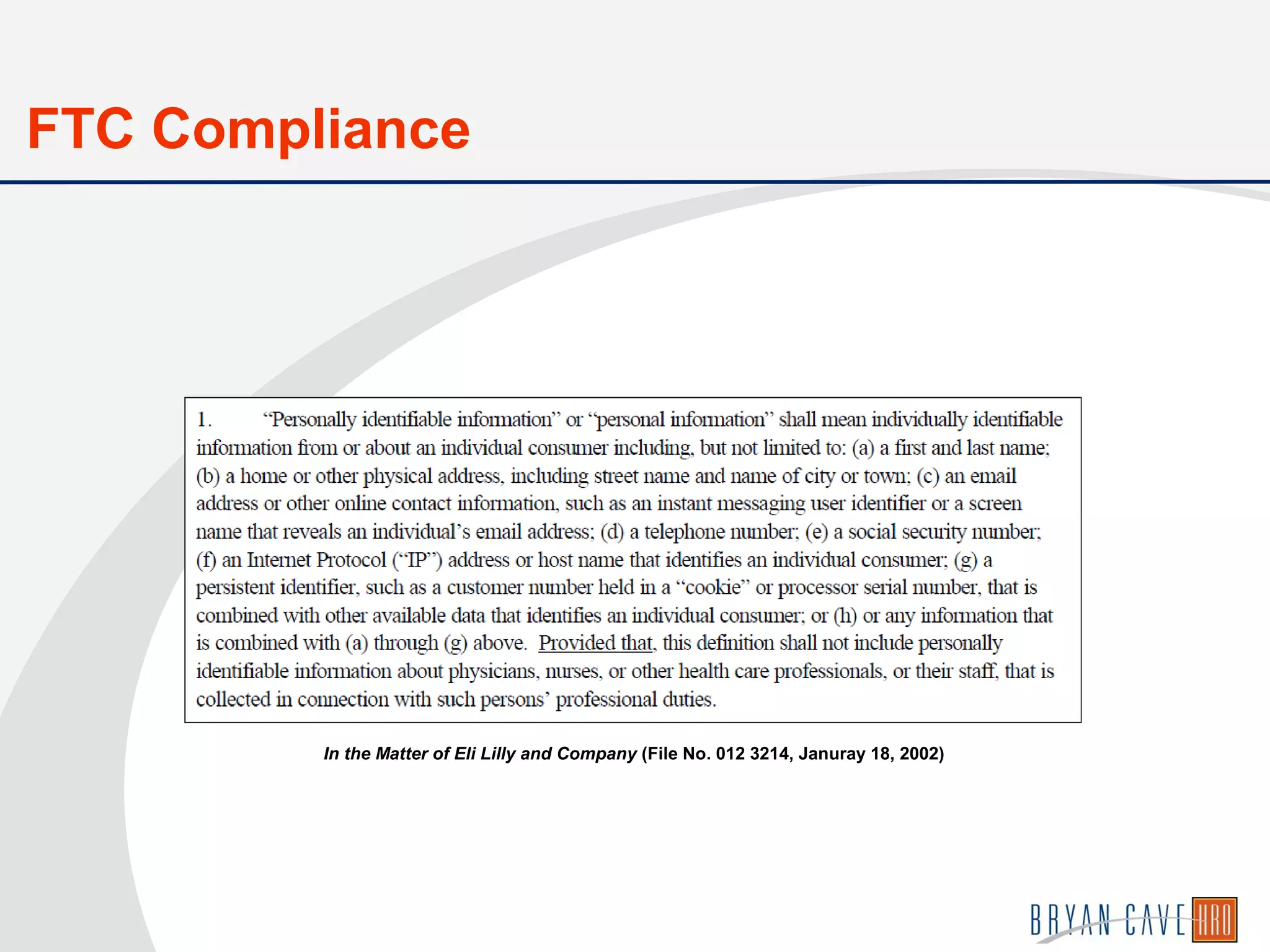
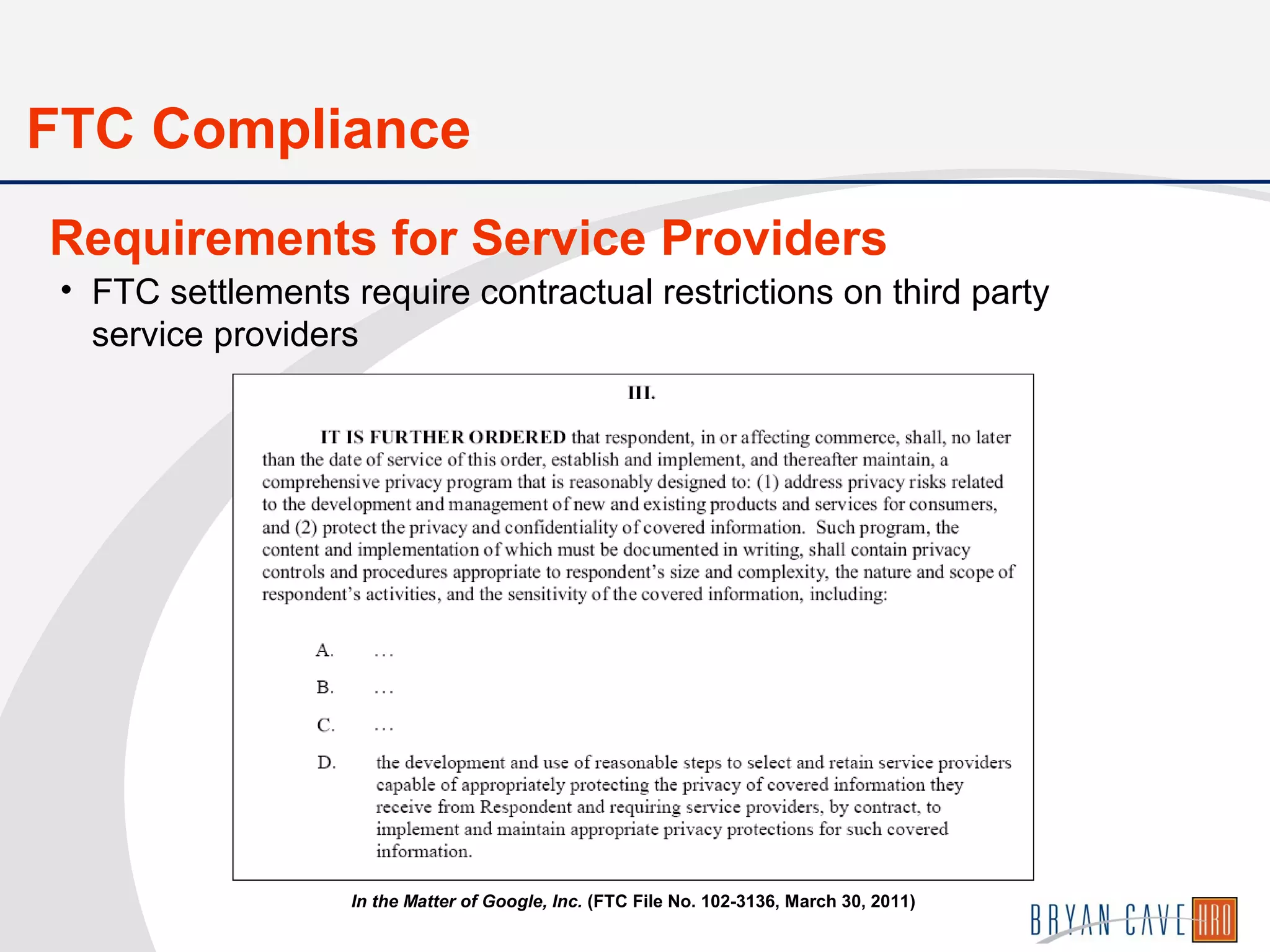
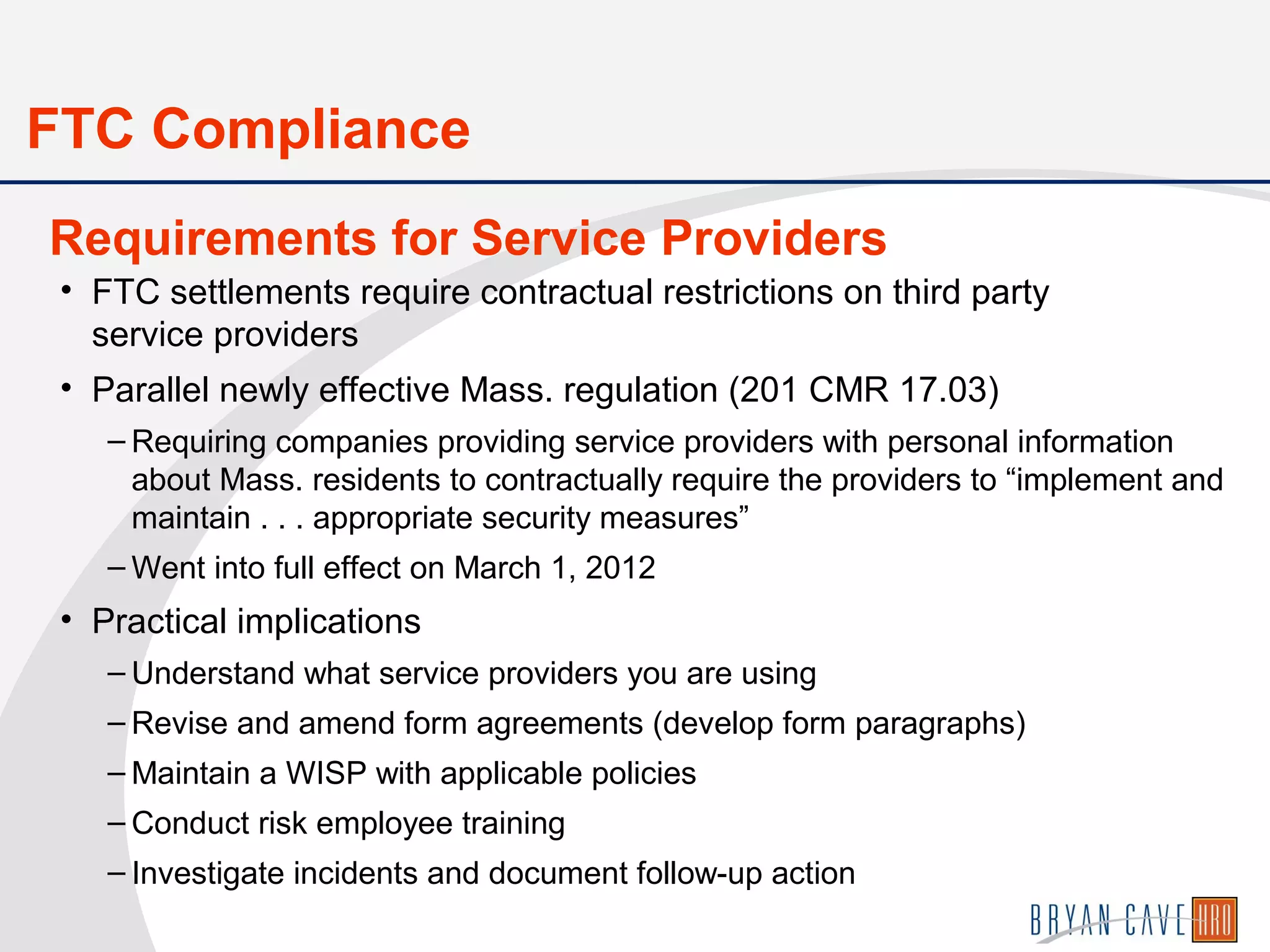
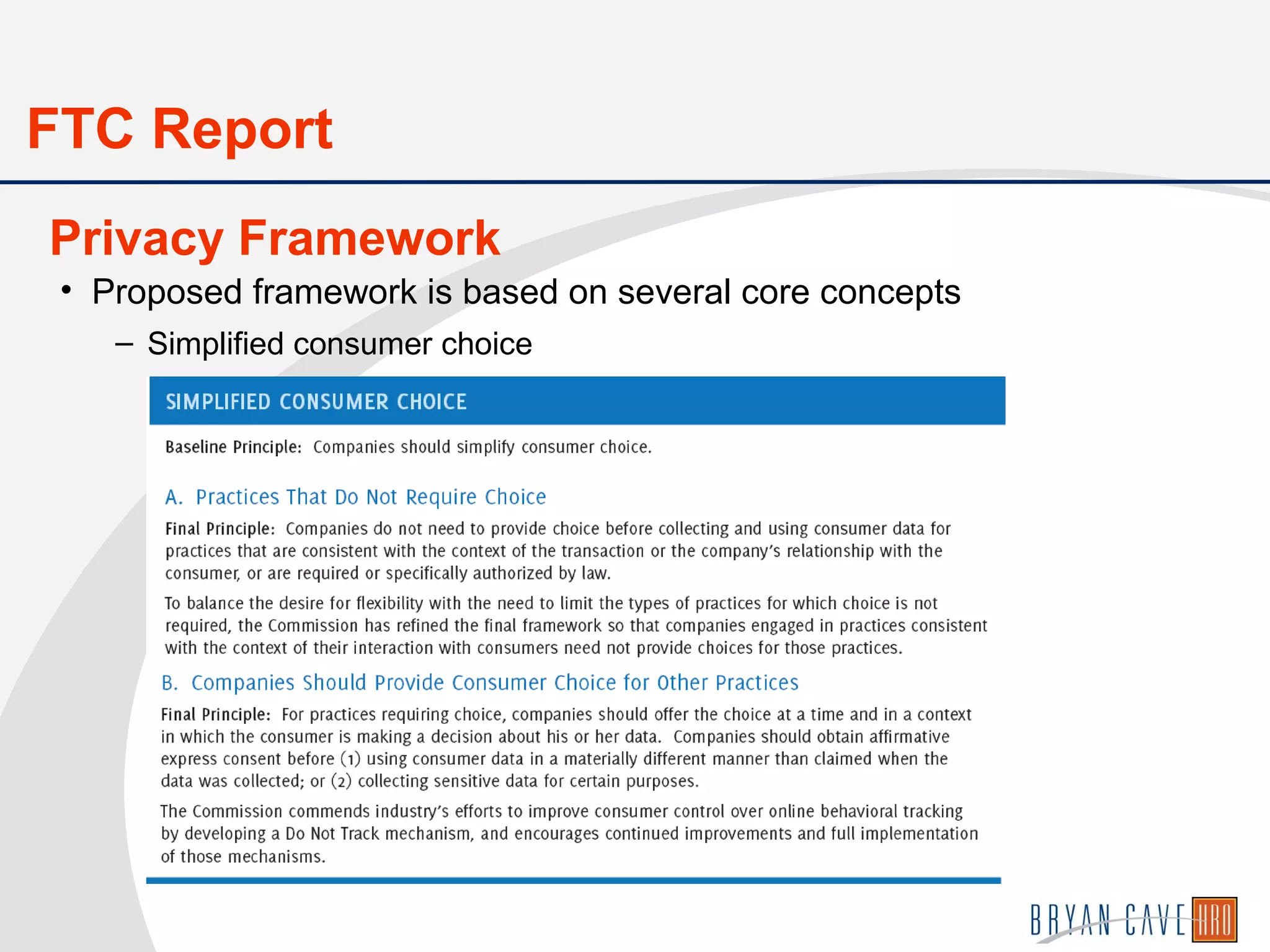
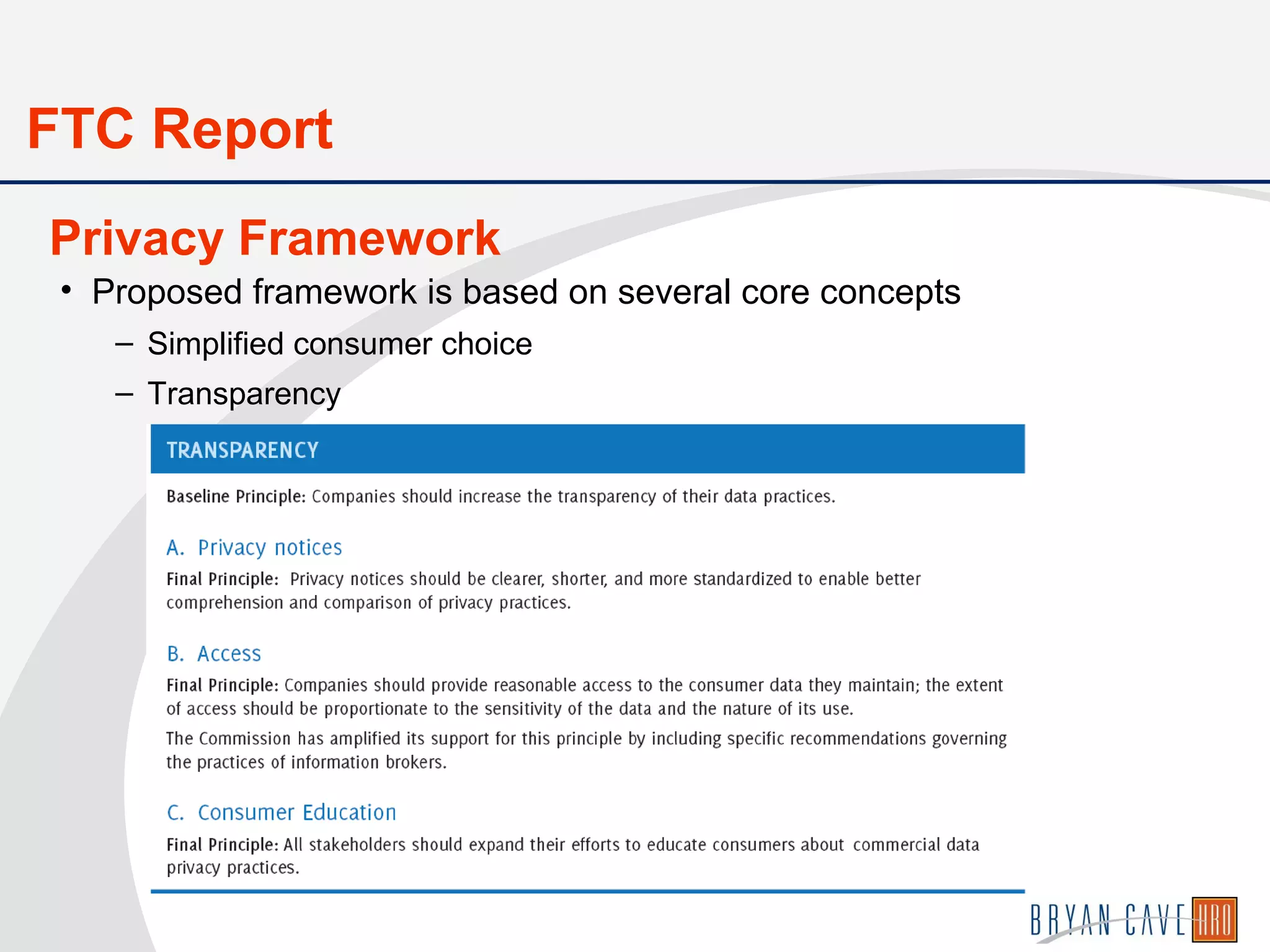
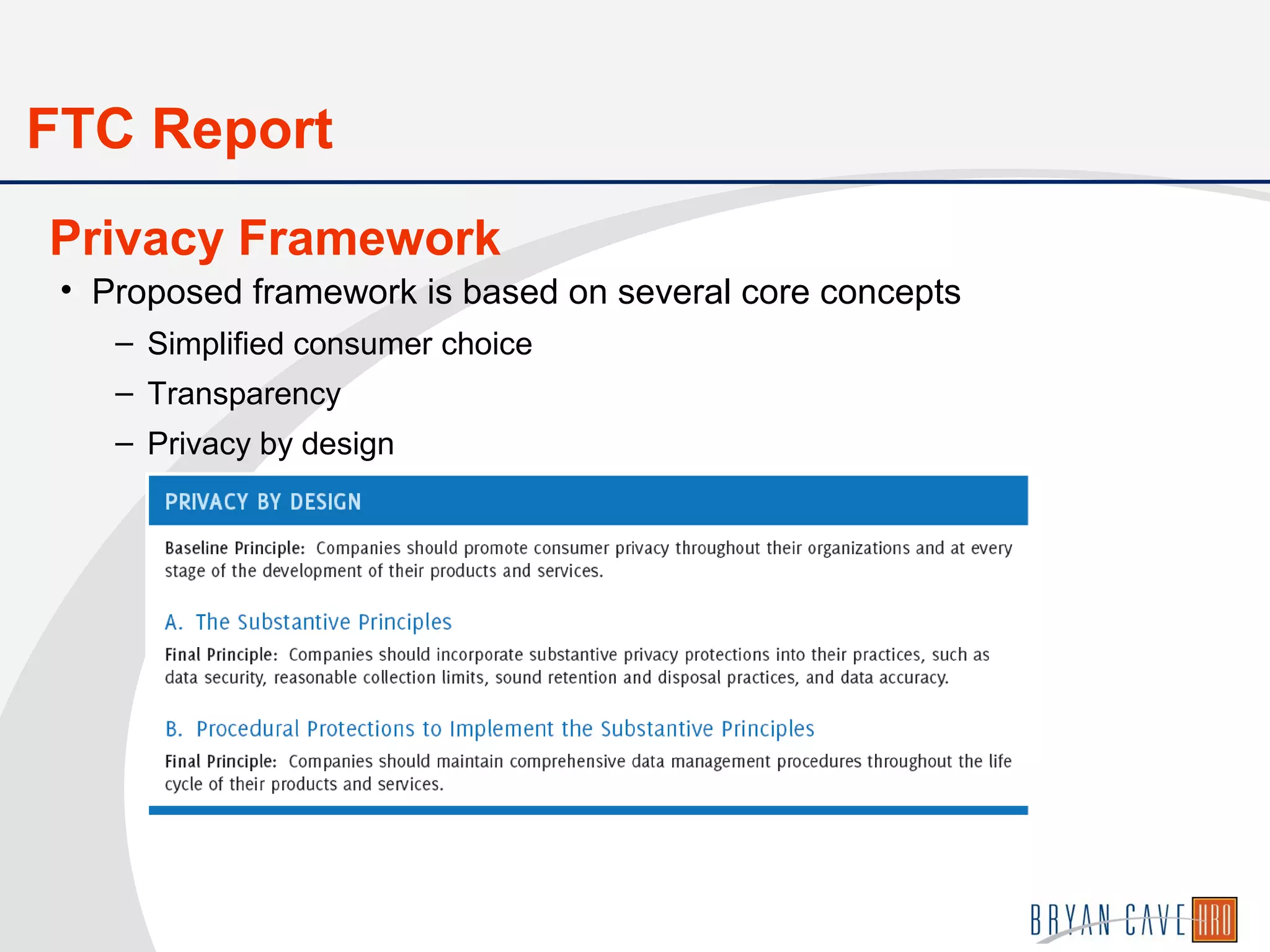
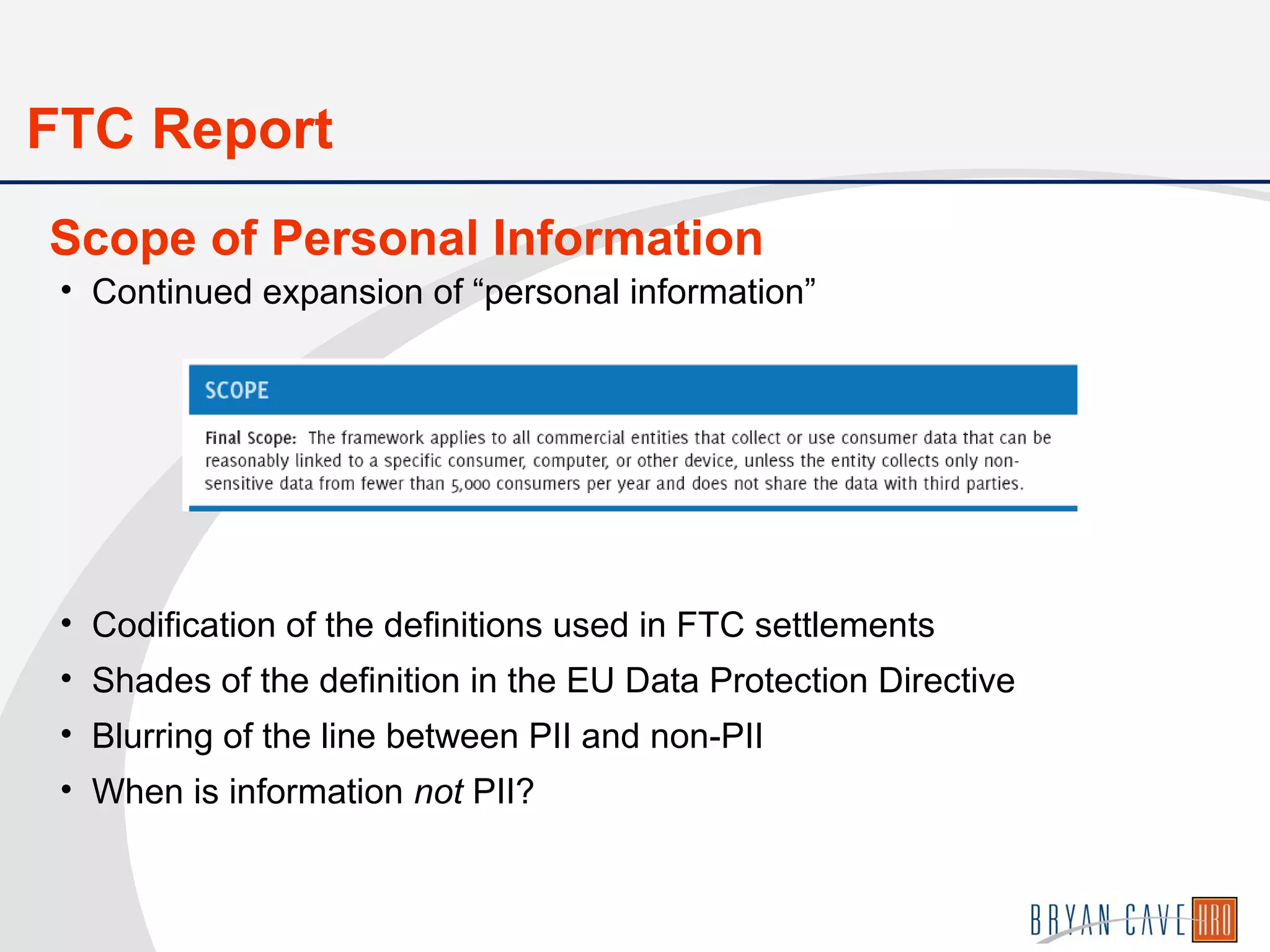
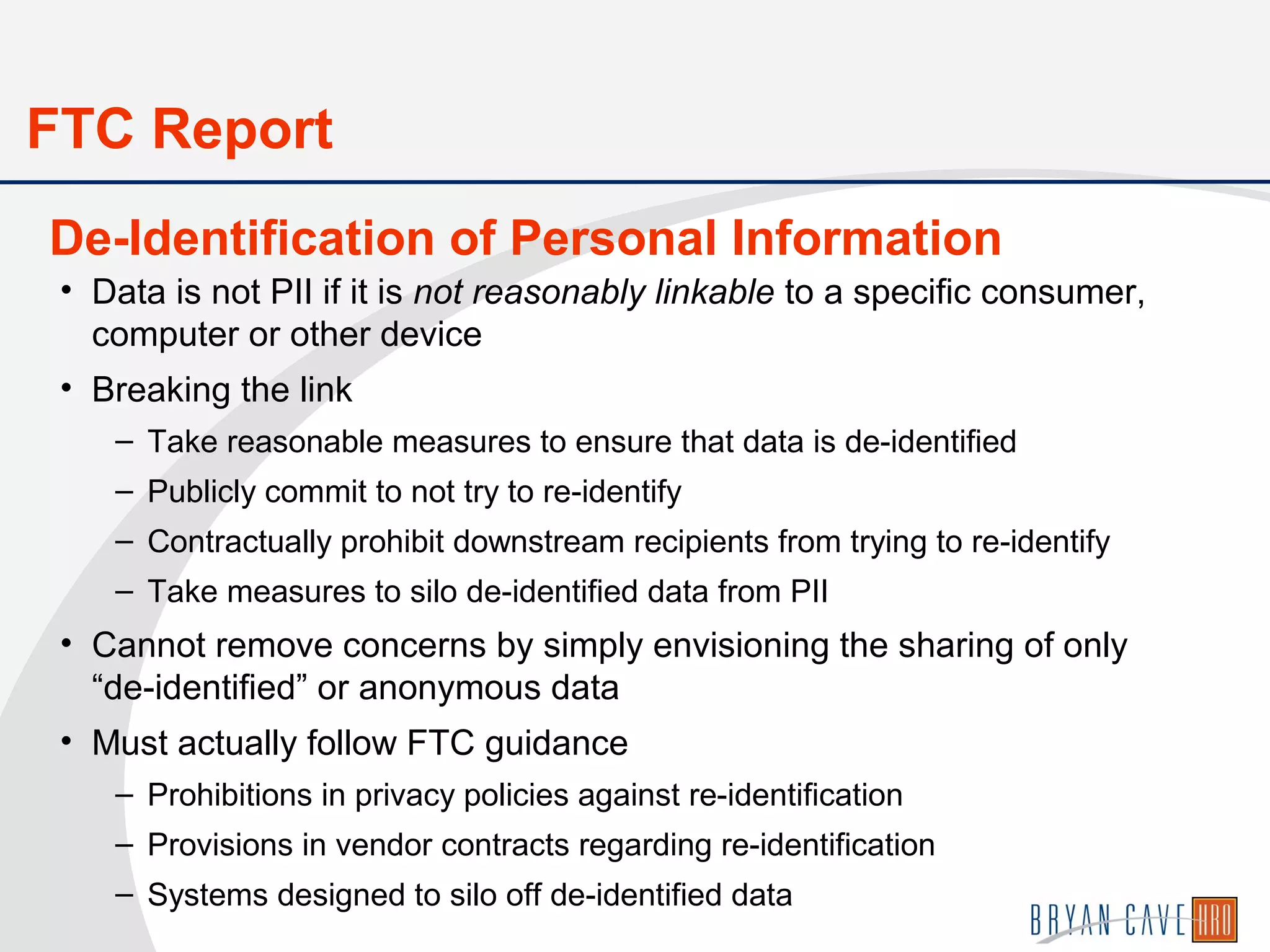
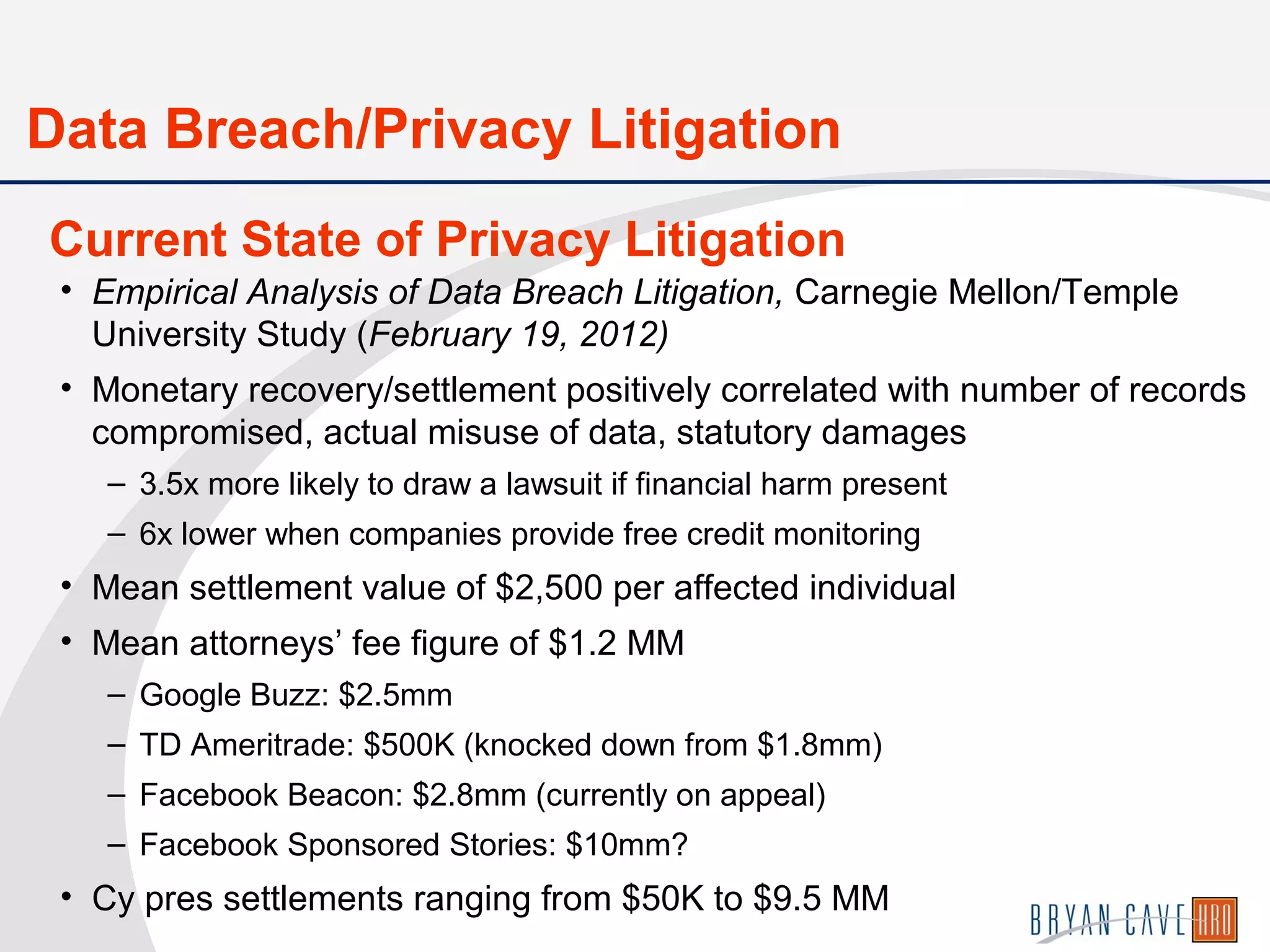
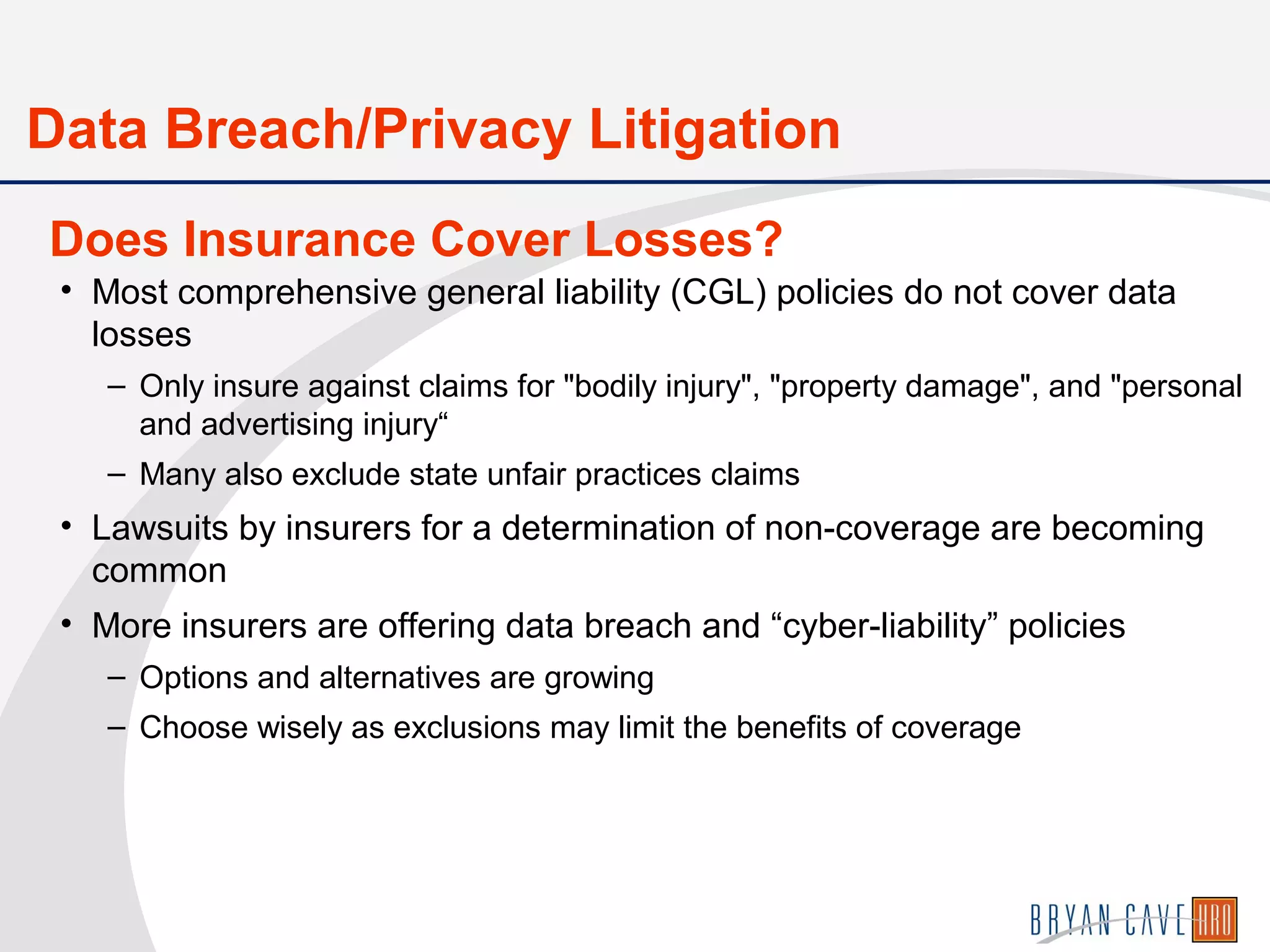
The document discusses data privacy and security, outlining the complex legal landscape in the U.S. compared to the EU, including various federal and state laws regulating personal data and consumer protections. It emphasizes the importance of companies knowing their data, implementing comprehensive information security programs, and complying with regulations while preparing for potential breaches. Additionally, it highlights the increasing scrutiny and enforcement actions surrounding data practices, stressing the need for transparency and adherence to best practices in data management.