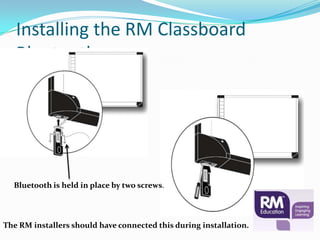
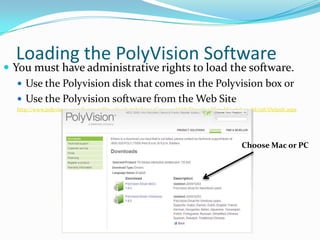
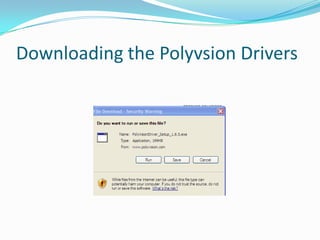
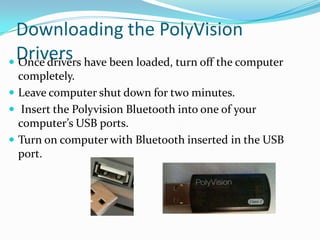
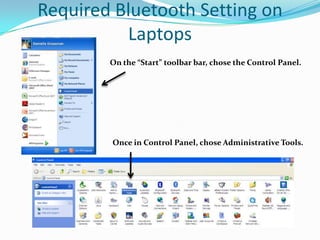
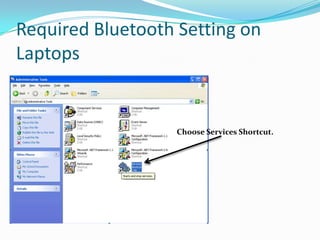
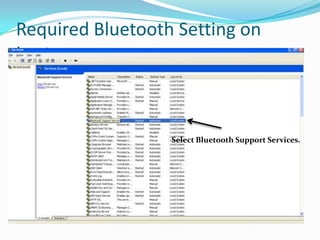
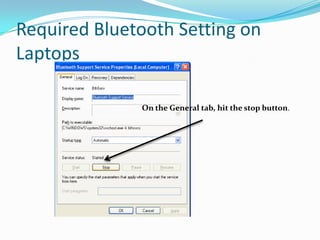
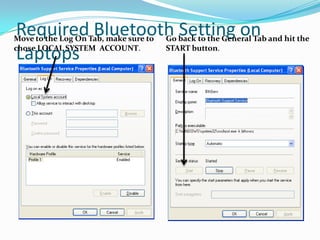
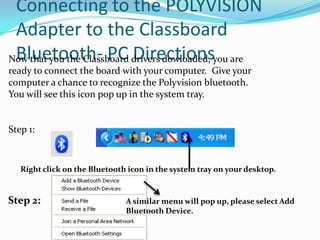
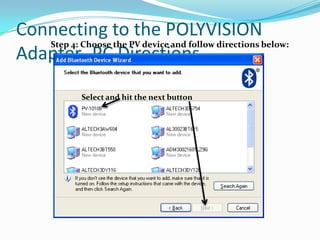
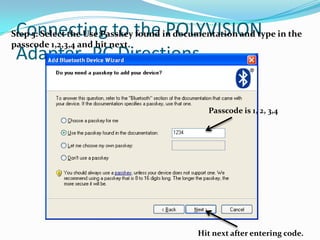
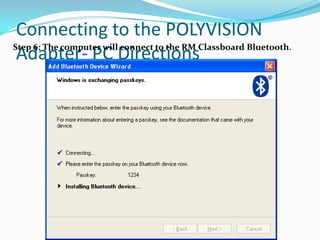
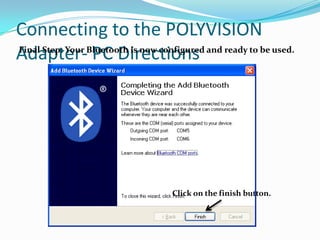
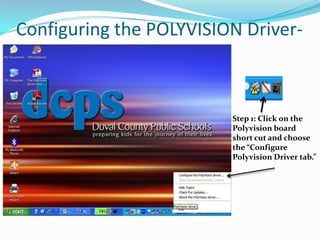
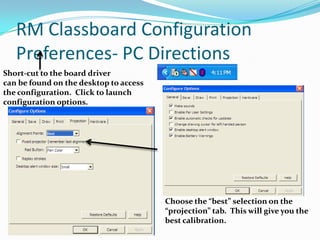
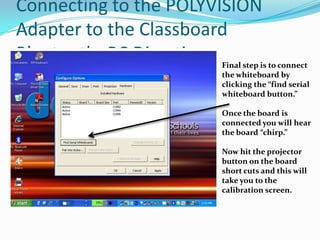
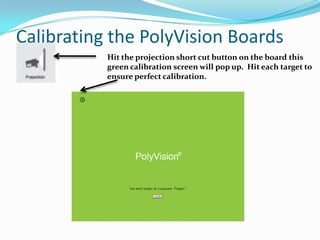
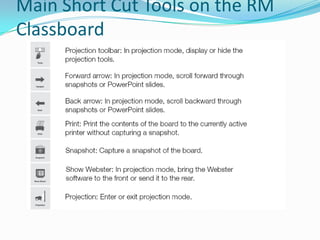
The document provides instructions for connecting an RM Classboard Touch interactive whiteboard to a computer via Bluetooth. It discusses downloading the necessary PolyVision software and drivers. For PCs, it describes setting the Bluetooth service to start automatically and pairing the computer to the IWB's Bluetooth adapter by entering a passcode. Once configured, the computer should automatically connect to the IWB on startup. The document also outlines calibrating the IWB screen.