Computer Virus
•Download as PPTX, PDF•
0 likes•41 views
Computer Virus
Report
Share
Report
Share
Recommended
Recommended
More Related Content
What's hot
What's hot (20)
Antivirus programs and Security Teams in E-Commerce by Ilakia

Antivirus programs and Security Teams in E-Commerce by Ilakia
Computer Virus by Neeraj Bhandari ( Surkhet.Nepal )

Computer Virus by Neeraj Bhandari ( Surkhet.Nepal )
Recently uploaded
TEST BANK For Principles of Anatomy and Physiology, 16th Edition by Gerard J. Tortora, Verified Chapters 1 - 29, Complete Newest Version.TEST BANK For Principles of Anatomy and Physiology, 16th Edition by Gerard J....

TEST BANK For Principles of Anatomy and Physiology, 16th Edition by Gerard J....rightmanforbloodline
Recently uploaded (20)
Finding Java's Hidden Performance Traps @ DevoxxUK 2024

Finding Java's Hidden Performance Traps @ DevoxxUK 2024
Stronger Together: Developing an Organizational Strategy for Accessible Desig...

Stronger Together: Developing an Organizational Strategy for Accessible Desig...
The Zero-ETL Approach: Enhancing Data Agility and Insight

The Zero-ETL Approach: Enhancing Data Agility and Insight
Decarbonising Commercial Real Estate: The Role of Operational Performance

Decarbonising Commercial Real Estate: The Role of Operational Performance
TEST BANK For Principles of Anatomy and Physiology, 16th Edition by Gerard J....

TEST BANK For Principles of Anatomy and Physiology, 16th Edition by Gerard J....
Six Myths about Ontologies: The Basics of Formal Ontology

Six Myths about Ontologies: The Basics of Formal Ontology
Observability Concepts EVERY Developer Should Know (DevOpsDays Seattle)

Observability Concepts EVERY Developer Should Know (DevOpsDays Seattle)
AI+A11Y 11MAY2024 HYDERBAD GAAD 2024 - HelloA11Y (11 May 2024)

AI+A11Y 11MAY2024 HYDERBAD GAAD 2024 - HelloA11Y (11 May 2024)
Choreo: Empowering the Future of Enterprise Software Engineering

Choreo: Empowering the Future of Enterprise Software Engineering
WSO2's API Vision: Unifying Control, Empowering Developers

WSO2's API Vision: Unifying Control, Empowering Developers
Modular Monolith - a Practical Alternative to Microservices @ Devoxx UK 2024

Modular Monolith - a Practical Alternative to Microservices @ Devoxx UK 2024
Harnessing Passkeys in the Battle Against AI-Powered Cyber Threats.pptx

Harnessing Passkeys in the Battle Against AI-Powered Cyber Threats.pptx
Less Is More: Utilizing Ballerina to Architect a Cloud Data Platform

Less Is More: Utilizing Ballerina to Architect a Cloud Data Platform
How to Check CNIC Information Online with Pakdata cf

How to Check CNIC Information Online with Pakdata cf
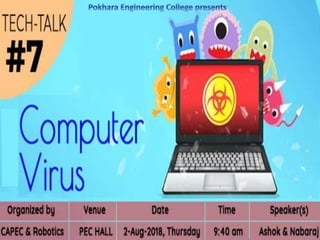
Computer Virus
- 2. WHAT IS THIS TECH-TALK ABOUT?
- 3. OR
- 5. A virus is a program that enters the computer system by attacking itself to another program and then spreads itself across the system.
- 15. *Try this at your own risk.
- 16. *Try this at your own risk.