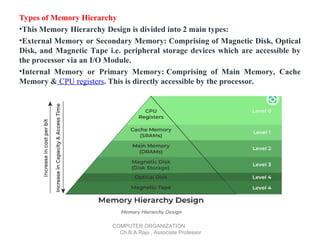
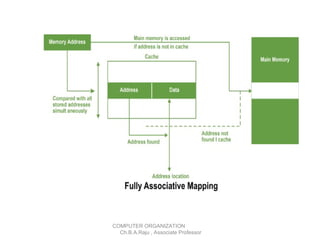
The document outlines the organization of computer memory, emphasizing the hierarchy of memory types, including registers, cache, main memory, and secondary storage. It explains the characteristics, usage, and performance implications of each memory type while discussing input-output organization and peripheral devices. Additionally, it covers cache mapping techniques and the concept of virtual memory, which allows efficient memory utilization in computing systems.