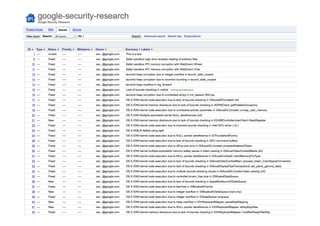
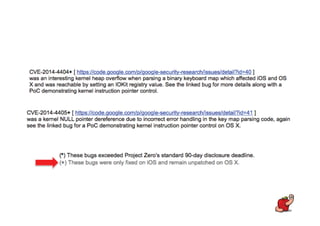
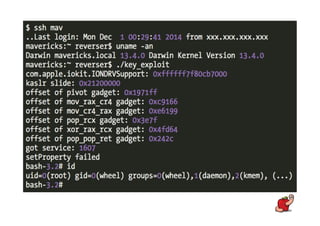
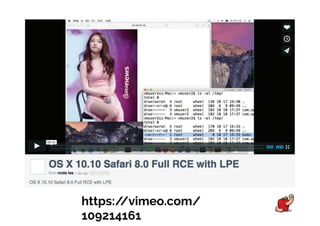
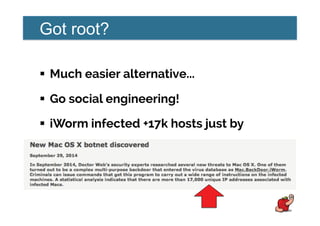
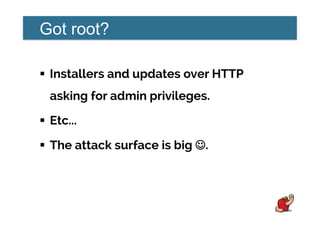
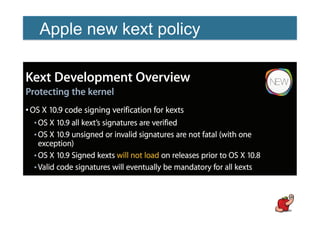
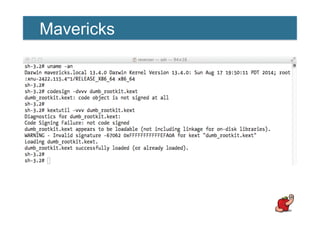
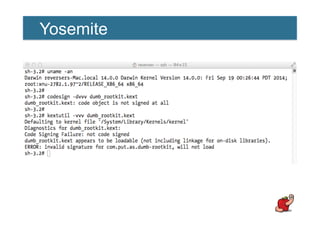
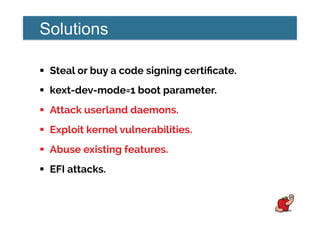
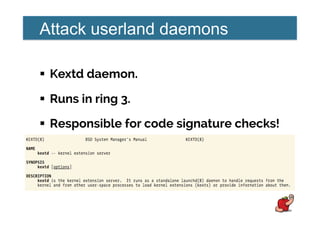
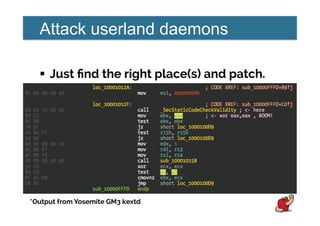
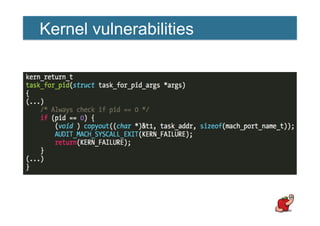
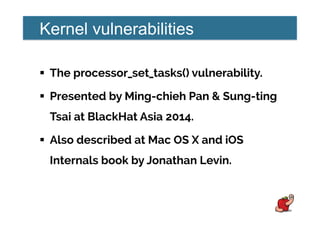
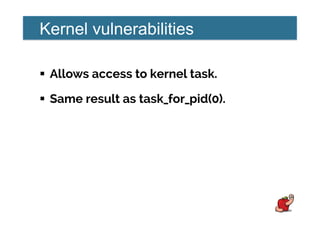
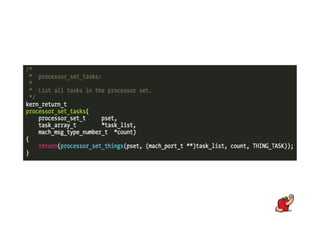
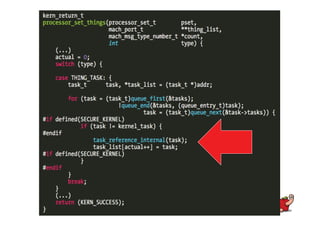
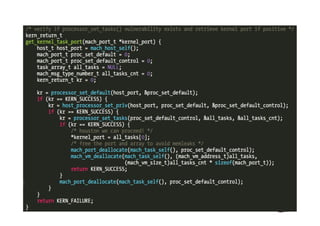
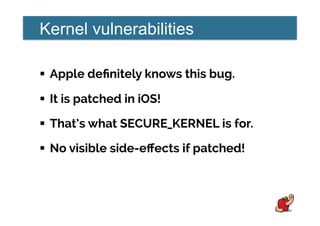
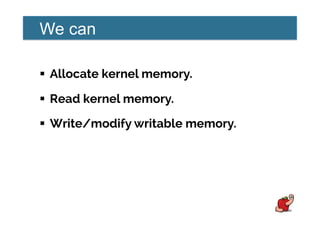
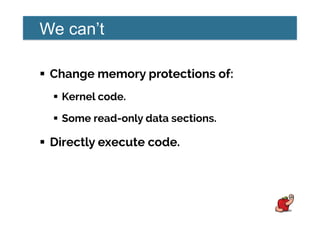
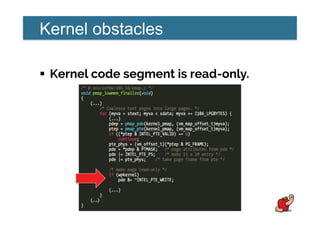
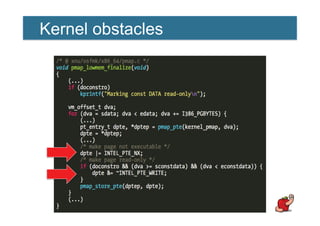
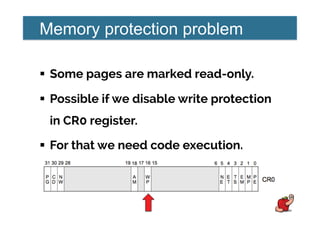
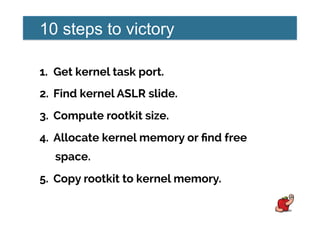
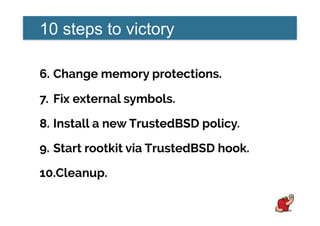
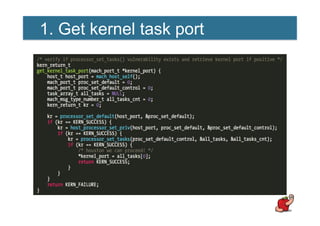
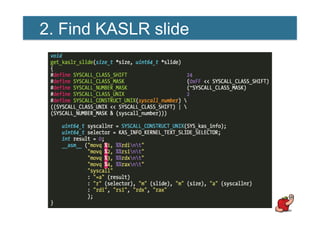
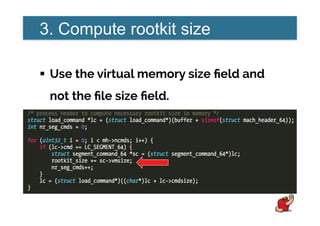
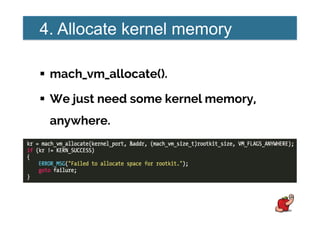
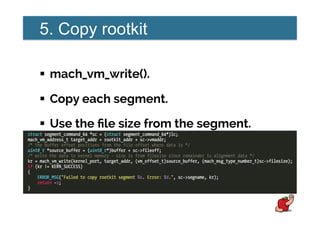
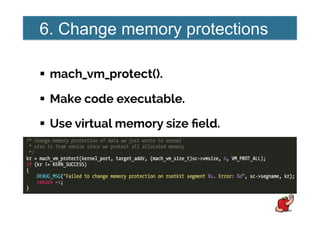
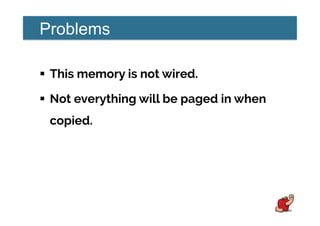
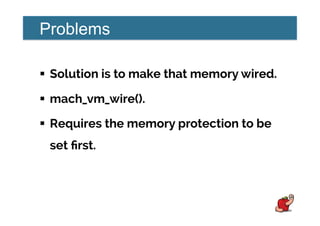
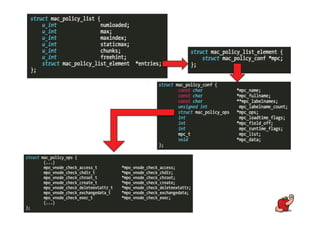
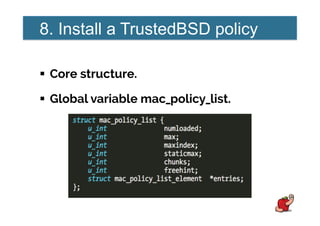
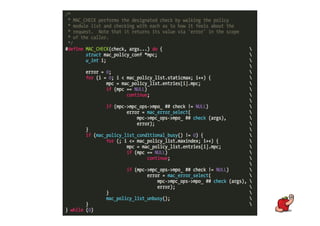
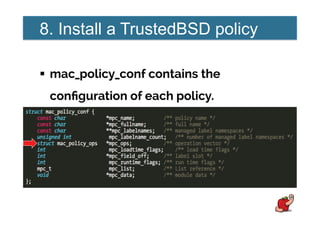
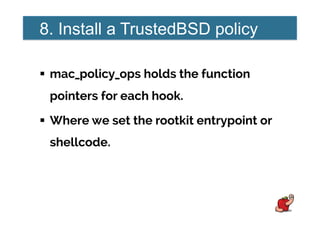
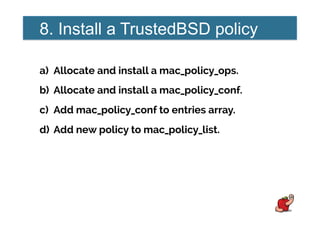
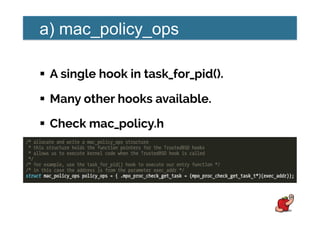
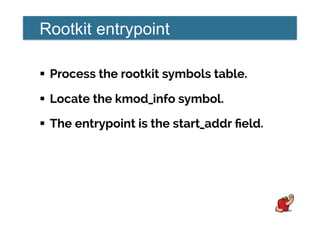
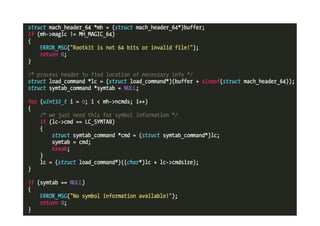
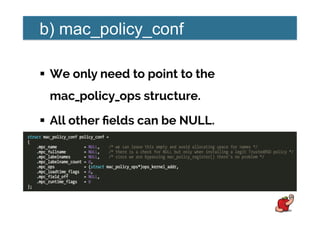
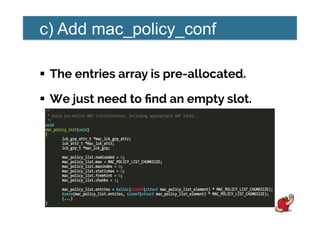
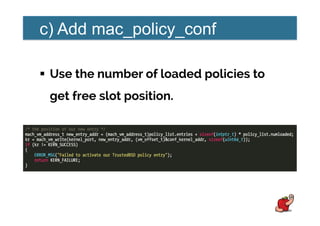
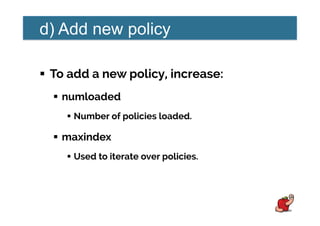
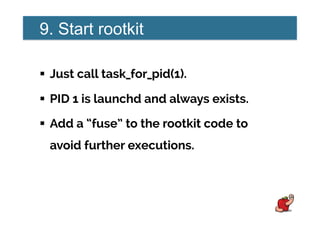
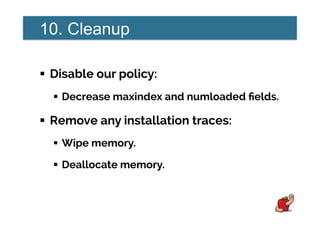
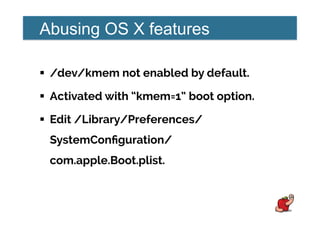
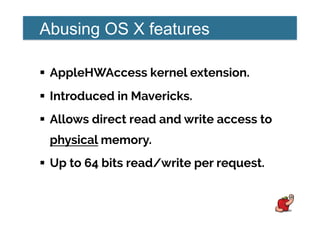
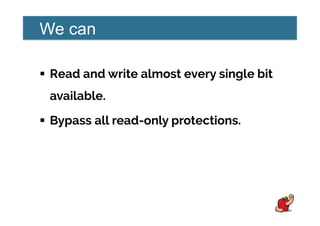
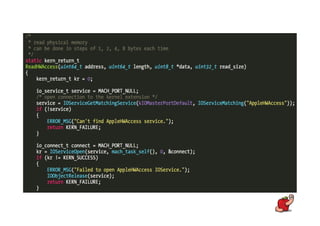
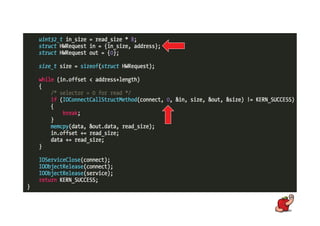
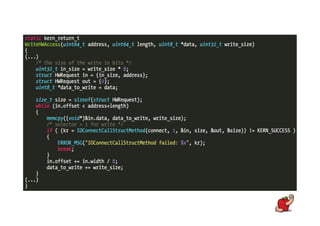
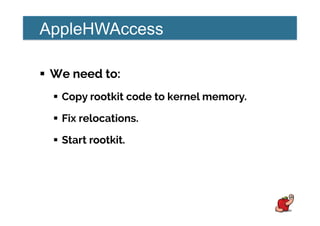
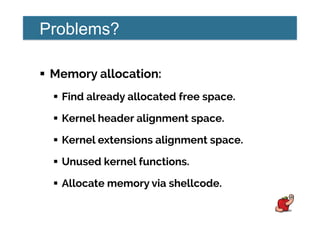
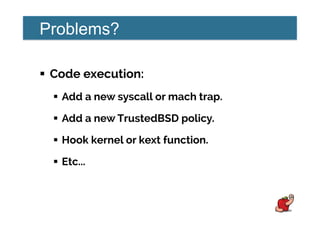
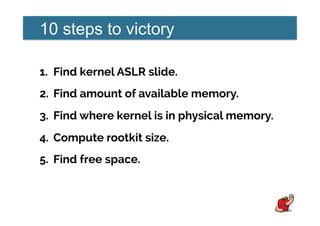
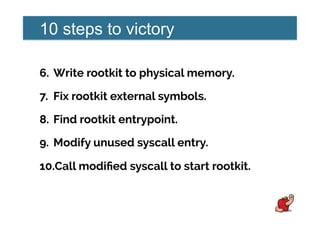
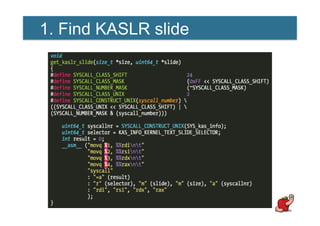
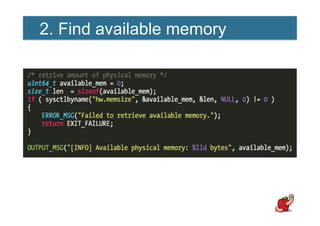
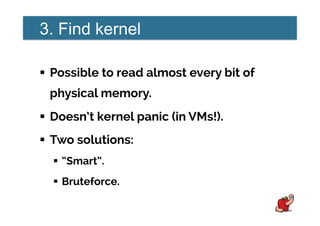
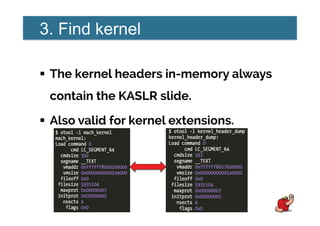
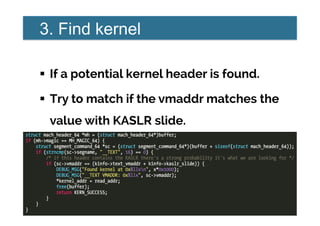
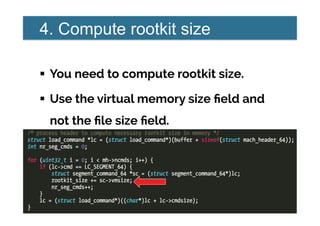
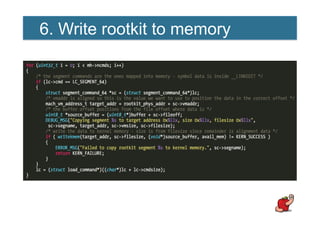
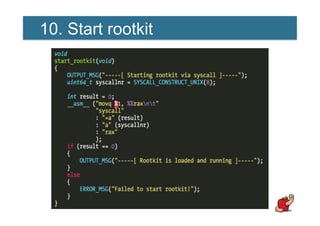
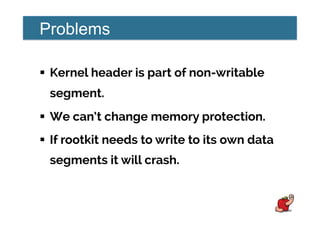
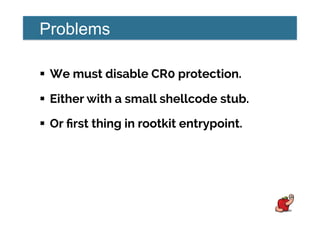
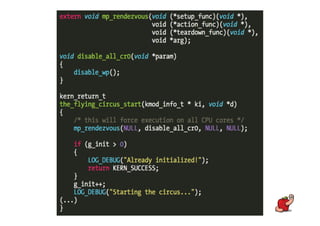
This document discusses various techniques for bypassing security measures and loading kernel rootkits on Apple operating systems like OS X. It describes how to leverage features like TrustedBSD and AppleHWAccess to gain kernel code execution. It also notes several kernel vulnerabilities that could enable privilege escalation, and argues that OS X security is not very effective overall. The speaker claims there are many ways to load rootkits despite code signing requirements.