CMMC 2.0 vs. ISO/IEC 27001 vs. NIST 800-171: What You Need to Know
- 2. • US legislative overview, impacts and update in NIST adoption • Weaving together NIST PF and NIST 800-171 • Definitions for CMMC 2.0, ISO/IEC 27001, and NIST SP 800-171 • What are the differences? • When do I implement each one? • How is compliance measured? • Common scope elements and how they might work together • Related areas of impact (e.g., cyber insurance) • Q&A Agenda
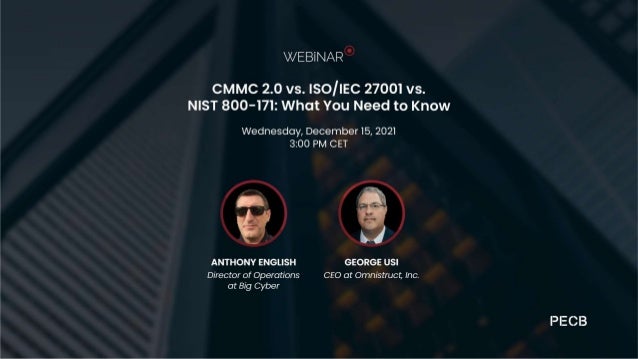
- 3. Introduction
- 4. Introduction (Who Is This ”George” guy?) George Usi, CEO & Co-Founder, Omnistruct Inc. www.omnistruct.com Mentor – www.cyberproud.org ; Curriculum Advisor – www.CSUChico.com Exec Edu; Board of Directors - www.securethevillage.org Co-Chair, California IPv6 Task Force – www.cav6tf.org ● Utility Of Commercial Wireless Study: A Technology Roadmap for Disaster Response for USNORTHCOM; Naval Postgraduate School; Pub 2006 ● IPv6 Forum Pioneer Award; Sacramento CA 2007; MetroNet6; Secure Delay Tolerant Communications & First Responder Interoperability research under the mentorship of Jim B0und and Dr Vint Cerf. Key Publications & Accomplishments ● Internet Scientist/Plumber and Researcher ● Career started at NTT/Verio security ● Owned Information Security Audit, Software and Networking Businesses since 2003 ● Level 2 Certified Blacksmith ● Proud Dad of Three Kids and Married to a Lovely Wife
- 5. Disclaimer The privacy law references and information in these slides and presentation are for informational and educational use represent the interpretations of George Usi. The National Institute of Standards and Technologies Privacy Framework (PF), GDPR, CCPA/CPRA, and other data privacy laws are interpreted for educational purposes as part of the public domain and are not intended as audit, consultative, or legal advice from Omnistruct Inc. (RPO, C3PAO Pending - CMMCab). George Usi is not an attorney or insurance broker. Omnistruct, Inc is not a law firm or insurance broker. Any topics covered where regulations, laws, or insurances of any kind are referenced should be reviewed by a licensed attorney, or insurance broker, respectively.
- 7. Check the past webinars on the PECB website at • https://pecb.com/past-webinars Previous sessions
- 8. Context Why do CMMC 2.0, ISO/IEC 27001, NIST SP800- 171, NIST PF matter in the cybersecurity landscape?
- 9. Why CMMC 2.0 / ISO 27001 / NIST SP 800-171 NIST PF Matter “In terms of safety and security of the Internet... I would have to argue that we are not in a very good place right now.” June 2021 - Dr. Vint Cerf Co-creator of the Internet, NIST VCAT By 2025, cybercrime will cost $10.5 trillion annually. Cybercrime Magazine “Under CMMC 2.0, the “Advanced” level (Level 2) will be equivalent to the NIST SP 800-171. The “Expert” level (Level 3), which is currently under development, will be based on a subset of NIST SP 800-172 requirements.” US Office of the Under Secretary of Defense, Acquisition and Sustainment https://www.acq.osd.mil/cmmc/faq.html “A new trend in privacy and cybersecurity laws [in US] is the introduction of safe harbor clauses [if NIST PF is used].” JD Supra https://youtu.be/PPFeh_105aM?t=43
- 10. It’s About Privacy… Attorneys suggest use of NIST PF in allaying regulators and third-party pursuits. https://www.jdsupra.com/legalnews/the-benefits-of-the-nist-cybersecurity- 76753/ States With Active Privacy Laws – CA, CO, VA https://www.ncsl.org/research/telecommunications-and-information- technology/state-laws-related-to-internet-privacy.aspx Three US States with pending privacy laws offer safe harbor with NIST PF Framework https://www.jdsupra.com/legalnews/new-proposed-laws-include- safe-harbor-2986211/ USA Legislative Overview, Impacts, Updates
- 11. Definitions CMMC 2.0, ISO/IEC 27001, NIST SP800-171, NIST PF
- 12. CMMC 2.0 Definition “The CMMC model is designed to protect Federal Contract Information (FCI) and Controlled Unclassified Information (CUI) that is shared with contractors and subcontractors of the Department through acquisition programs.” https://www.acq.osd.mil/cmmc/model.html
- 13. CMMC 2.0 Practices Level 1 - Foundational Level 2 - Advanced Level 3 - Expert Based on subset of NIST SP 800- 172 Previous Level 5 Mirrors NIST SP 800-171 Same as previous Level 3 Same as previous Level 1
- 14. ISO/IEC 27001:2013 Definition • International standard for information security based on the principles of the CIA triad (confidentiality, integrity and availability) and the model for continuous improvement of the security management system (Plan, Do, Check, Act). • Used a basis for many other security standards and frameworks.
- 15. NIST SP 800-171 Definition Designed by the National Institute of Standards and Technology in the USA, NIST SP 800-171 defines the requirements for US government service providers to follow in order to safeguard Controlled Unclassified Information (CUI) that exists in the service providers’ IT networks.
- 16. NIST Privacy Framework Definition The NIST Privacy Framework is a voluntary tool (for now… see Ohio*) developed in collaboration with stakeholders intended to help organizations identify and manage privacy risk to build innovative products and services while protecting individuals’ privacy. Lt Gov of Ohio Interview Ohio Personal Privacy Act (OPPA*) & NIST PF: https://iapp.org/news/a/ohio-lt-governor-jon-husted-discusses-the-states- privacy-bill/ *References (1st link also on previous slide 8, 2nd link is to actual state of Ohio site): https://www.jdsupra.com/legalnews/new-proposed-laws-include-safe-harbor-2986211/ https://governor.ohio.gov/wps/portal/gov/governor/administration/lt-governor/07132021
- 18. CMMC 2.0 Educate people on cyber threats Implement access controls Authenticate users Monitor your physical space Update security protections https://www.acq.osd.mil/cmmc/implementation.html
- 19. ISO/IEC 27001:2013 Determine scope Risk assess Identify applicable requirements Build your ISMS Measure, monitor, review Certify
- 20. NIST SP 800-171 Locate and Identify CUI Categorize CUI Implement Required Controls Train Your Staff Monitor Your Data Assess Your Systems & Processes
- 21. NIST Privacy Framework (PF) - FUTURES Regulatory Impact Assessment Adopt CORE Protection Activities Develop Profiles Determine Tiers Crosswalk to CMMC (pending) Assess Your Systems & Processes
- 22. Compliance How is it measured for each?
- 23. Comparison of the Three ISO/IEC 27001 CMMC 2.0 NIST SP 800-171 • Defines security guidance for information and includes people, process, and technology in its scope. Serves as a security foundation for an organization. • No levels of compliance – either compliant or not but some requirements can be excluded. • Voluntary compliance. • Meant for US government suppliers to ensure the security of FCI and CUI. • Three levels of compliance. • Compliance can be mandatory. • Based on NIST frameworks. • Based on NIST Cyber Security Framework (CSF). • One of many NIST Special Publications. • Focuses on the security of CUI. • Compliance is voluntary unless required as part of US government requirements.
- 24. Overlap – Can they support each other? “The Department is pursuing development of acceptance standards between CMMC and other cybersecurity standards and assessments, to include between CMMC Level 2 (Advanced) and the NIST SP 800-171 DoD Assessment Methodology for the high assessment confidence level, as well as CMMC Level 2 and the GSA Federal Risk and Authorization Management Program (FedRAMP) requirements for commercial cloud service offerings. Furthermore, DoD is working with international partners to coordinate on potential agreements between CMMC and their respective cybersecurity programs. Any such equivalencies or acceptance standards, if established, will be implemented as part of the rulemaking process.” https://www.acq.osd.mil/cmmc/implementation.html#impHero.
- 25. What is Personal Information In The USA? Call a US Attorney. Chances are they will say: Any information related to an identified or identifiable data subject (natural person), every US State is different, and “Beware California.”
- 26. Comprehensive Consumer Privacy is Here/Coming • The regulatory train of comprehensive consumer privacy is coming in the US • State by state with CA (CCPA/CPRA), Colorado (CPA), and Virginia (VCDPA) notable enforcement dates of 1/1/2023 (some of you have one year); • California already enforcing since 1/1/2020 with some snags’ • Federal privacy law unlikely anytime soon (exception is Federal Law for HIPAA covered entities who use NIST PF – Federal HR 8998*) • NIST Privacy Framework foretold as the “easy button” (see Ohio; prior slides) *Source: JD Supra, Bullet 4: https://www.jdsupra.com/legalnews/new-proposed-laws-include-safe-harbor-2986211/
- 27. Related Impacts What else can these standards/frameworks influence?
- 28. Some Spinoff Benefits • Although CMMC 2.0 and NIST SP 800-171 are both focused on suppliers to the US government and the security of data related to such a relationship, they do provide security elements that are common in other security standards and frameworks. • ISO/IEC 27001:2013 certification offers any organization an internationally recognized security certification. • A NIST PF Program makes for easy mapping to other NIST SPs (including NIST 800-171) and illustrating a NIST PF Program during sales cycles in US may make contracts/sales go faster when compared with those with “just” NIST 800-171.
- 30. Privacy Law Legislation Tracker https://iapp.org/resources/article/us-state-privacy-legislation-tracker/
- 31. European Union - GDPR UK (Brexit Note) - DPA Australia – APP/PA Brazil - LGPD Canada - PIPEDA China - PIPL Hong Kong – PDPO S1 Singapore - PDPA South Korea - PIPA Turkey - PDPL Global Data Privacy
- 32. NIST Privacy Framework Overview NIST CSF (Left) & NIST Privacy Framework (Right) https://nvlpubs.nist.gov/nistpubs/CSWP/NIST.CSWP.01162020.pdf
- 33. Due to CMMCab changes, George suggests using the California CCPA/CPRA to NIST PF crosswalk until new mapping is done. Use the California CCPA/CPRA Crosswalk LINK TO NIST PF CROSSWALK: https://www.nist.gov/privacy-framework/ccpa-cpra-crosswalk-bakerhostetler
- 34. ISO/IEC 27701 Training Courses • ISO/IEC 27701 Foundation 2 Day Course • ISO/IEC 27701 Lead Implementer 5Days Course Exam and certification fees are included in the training price. https://pecb.com/en/education-and-certification-for-individuals/iso- 27701 www.pecb.com/events
- 35. Appendix
- 36. Ramping up… Relevant PECB Training courses
- 37. Relevant Training PIMS • PECB ISO 27701 Foundation • PECB ISO 27701 LI • PECB ISO 27701 LA Information Security • PECB ISO 27001 LI • PECB ISO 27001 LA • PECB ISO 27002 LM
- 38. Relevant Training Data protection • PECB Certified Data protection Officer (GDPR) Privacy • PECB ISO29100 LI
- 39. Check the PECB agenda, select the ISO/IEC 27701 Lead Implementer https://pecb.com/en/partnerEvent/event_schedule_list Training Events For full detailed information about an event click on the ‘View’ button on the right hand side under ‘View full details’. Note: Before applying for any training courses listed below, please make sure you are registered to PECB Training Agenda
- 40. THANK YOU ? tony@botsecuritysolutions.com https://www.linkedin.com/in/englishtony/ George@securethevillage.org https://www.linkedin.com/in/georgeusi/
