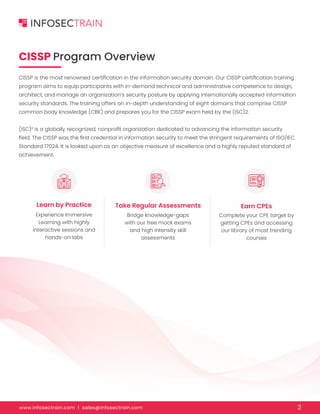
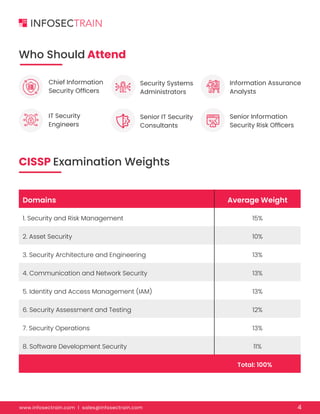
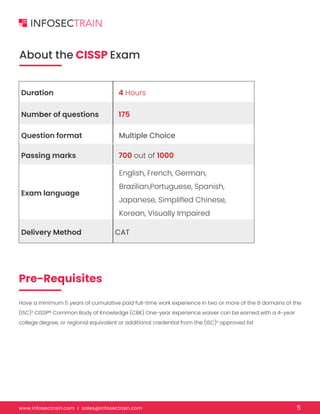
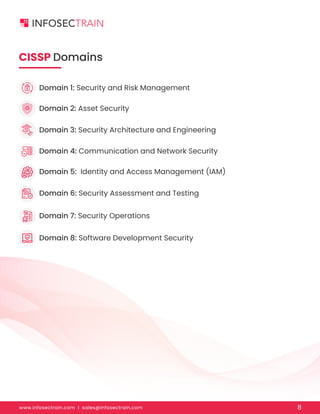
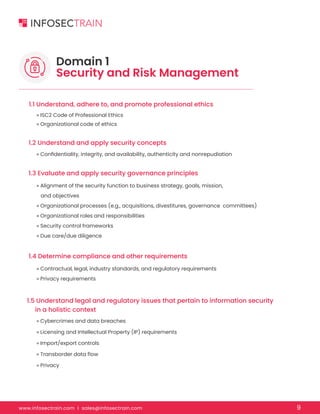
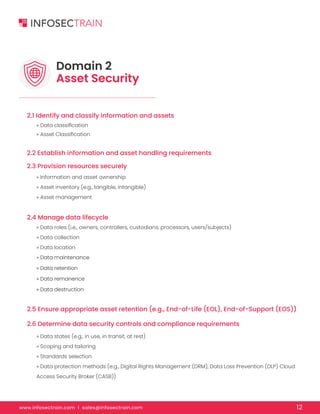
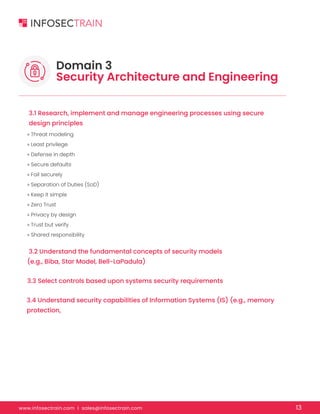
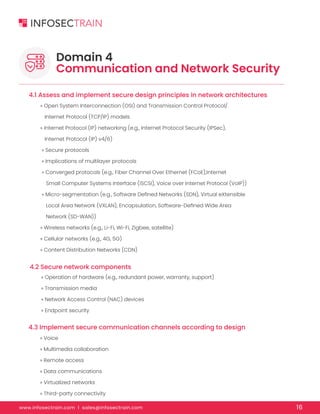
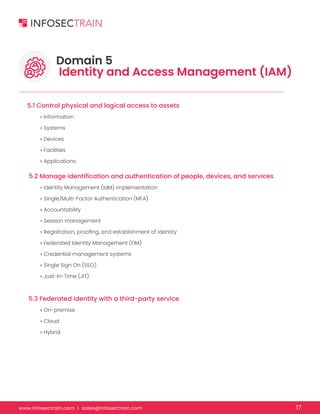
The document provides an overview of the CISSP (Certified Information Systems Security Professional) exam preparation training program, emphasizing its importance in the information security domain. It details the structure of the training, including hands-on labs, a satisfaction guarantee, and post-training support, while outlining the essential domains covered in the exam. Additionally, it specifies the exam format, prerequisites, and target audience for prospective participants seeking to enhance their security management skills.