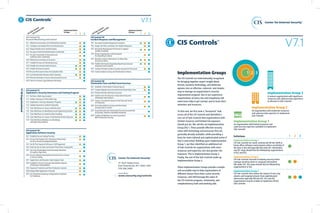
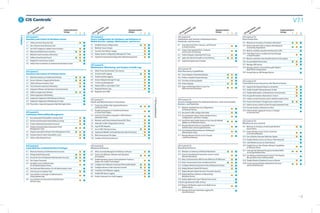
The document describes three implementation groups for categorizing CIS Controls based on an organization's resources and cybersecurity expertise. Implementation Group 1 is for organizations with limited resources and expertise, Group 2 is for those with moderate resources and expertise, and Group 3 is for organizations with significant resources and experience to implement the most advanced controls. The groups are meant to help organizations focus their security efforts based on their capabilities.