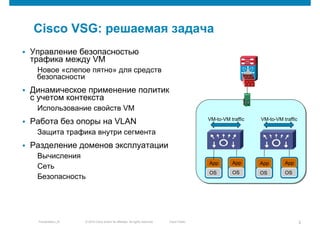
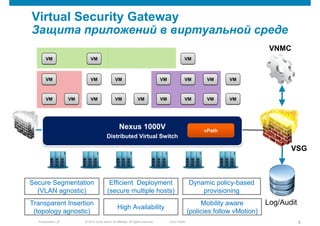
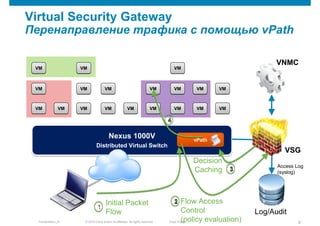
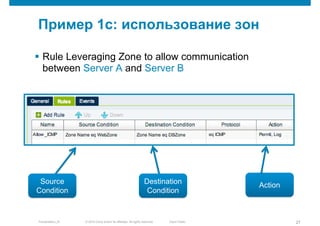
Cisco Virtual Security Gateway (VSG) provides security policies and controls for virtual machine to virtual machine traffic. It analyzes VM attributes and context to dynamically apply access controls. VSG inserts transparently without relying on VLANs to protect intra-segment communication. It also supports multi-tenant environments through security domain separation and granular policy assignment.