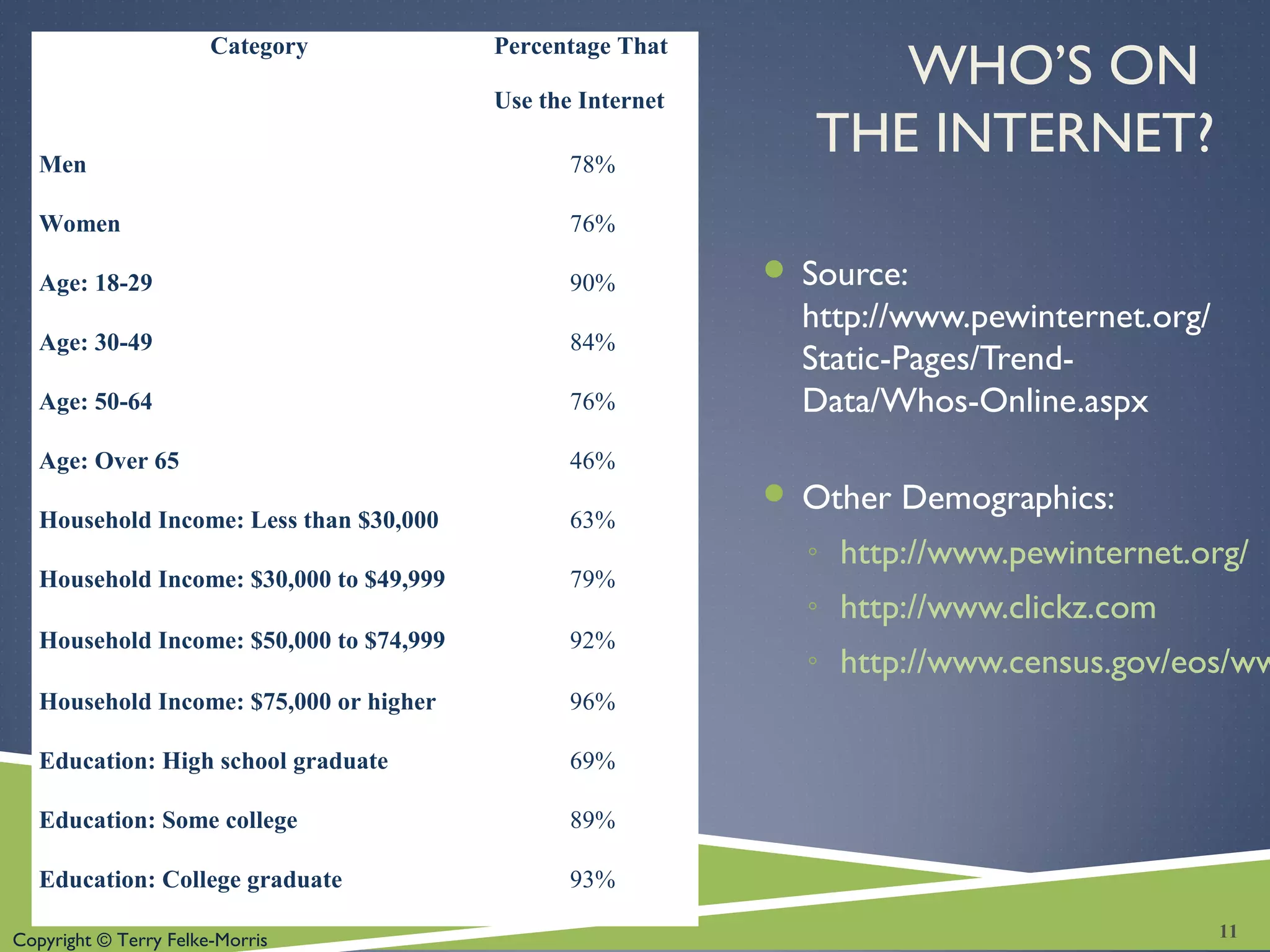
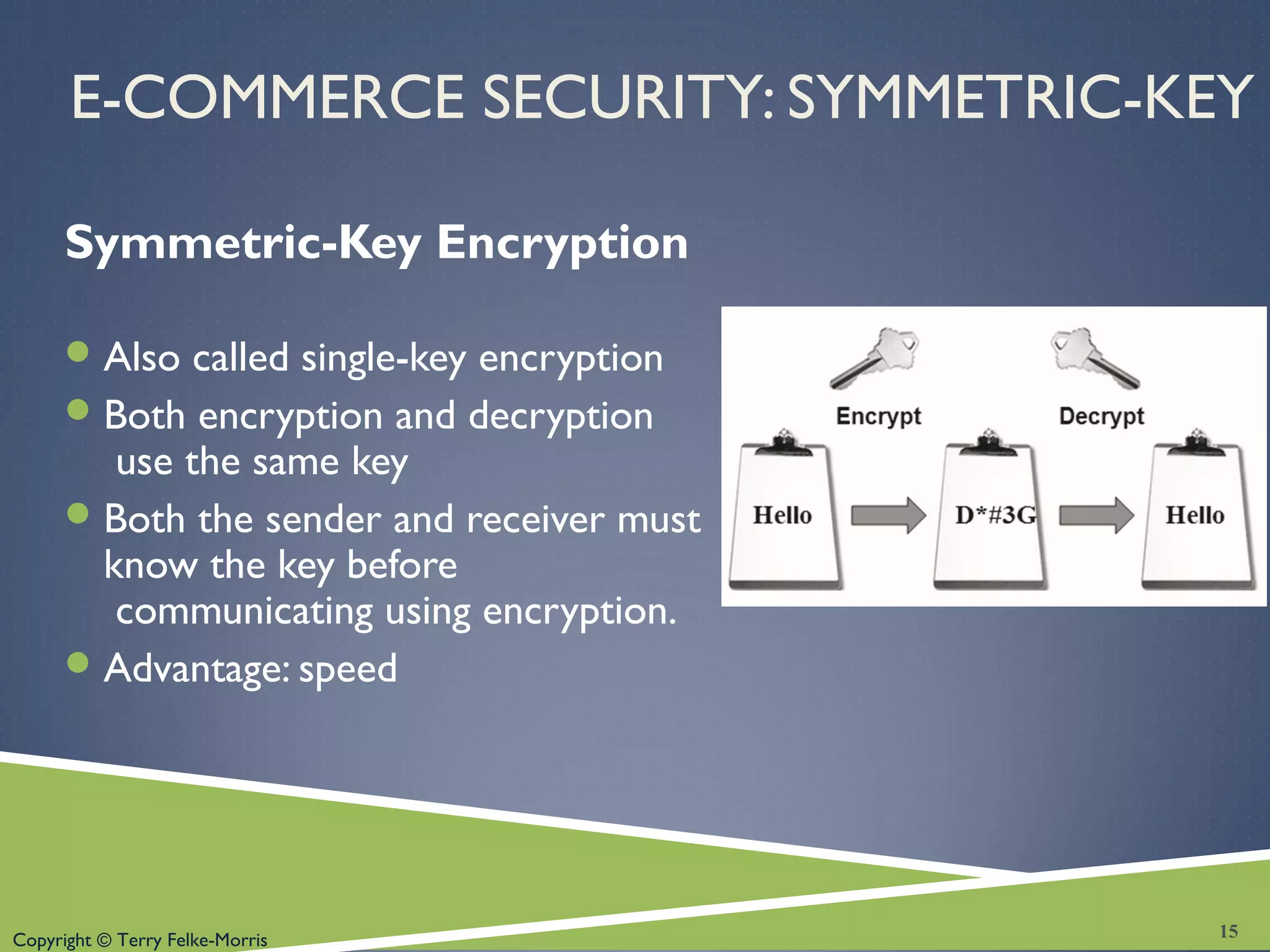
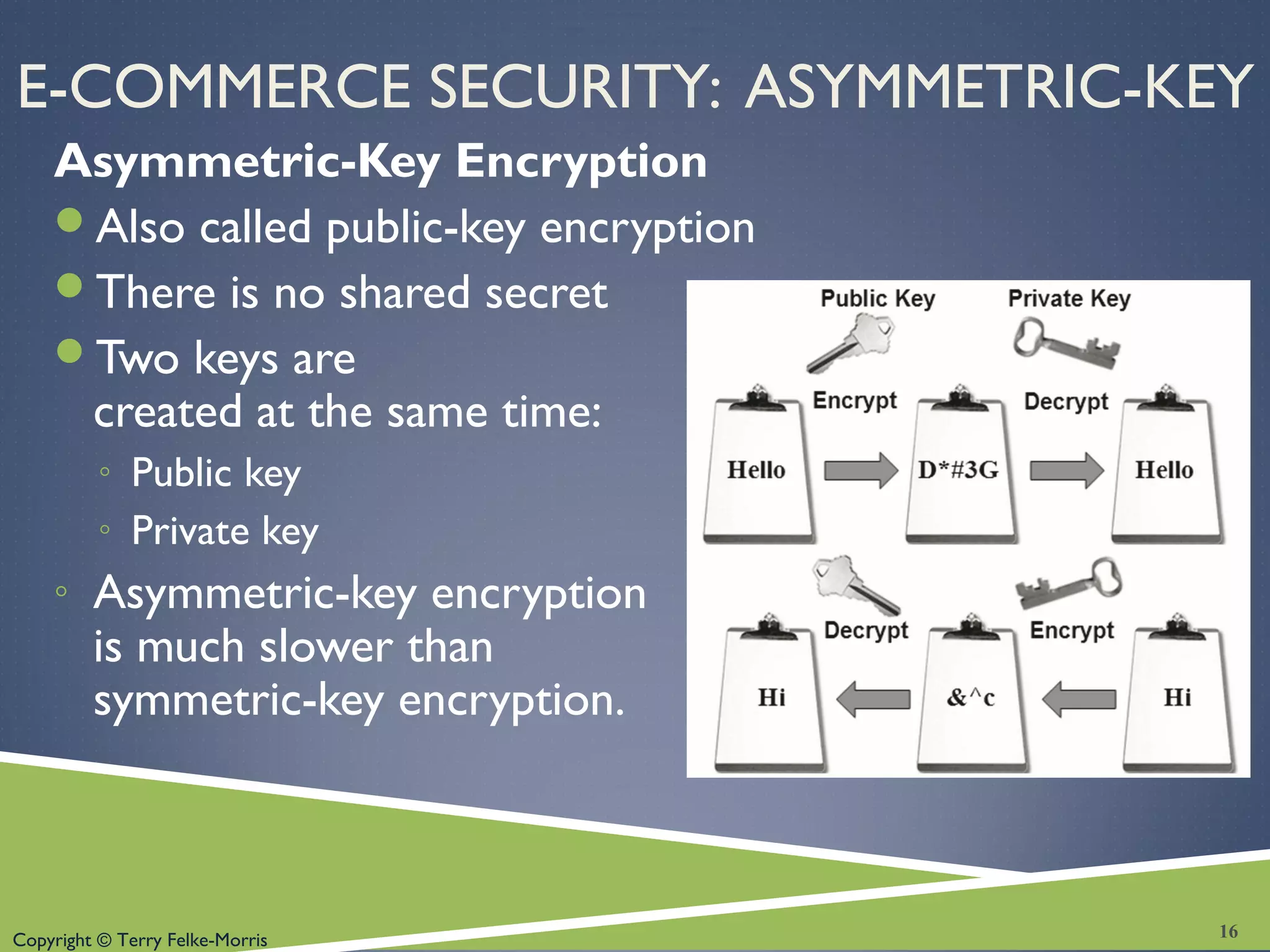
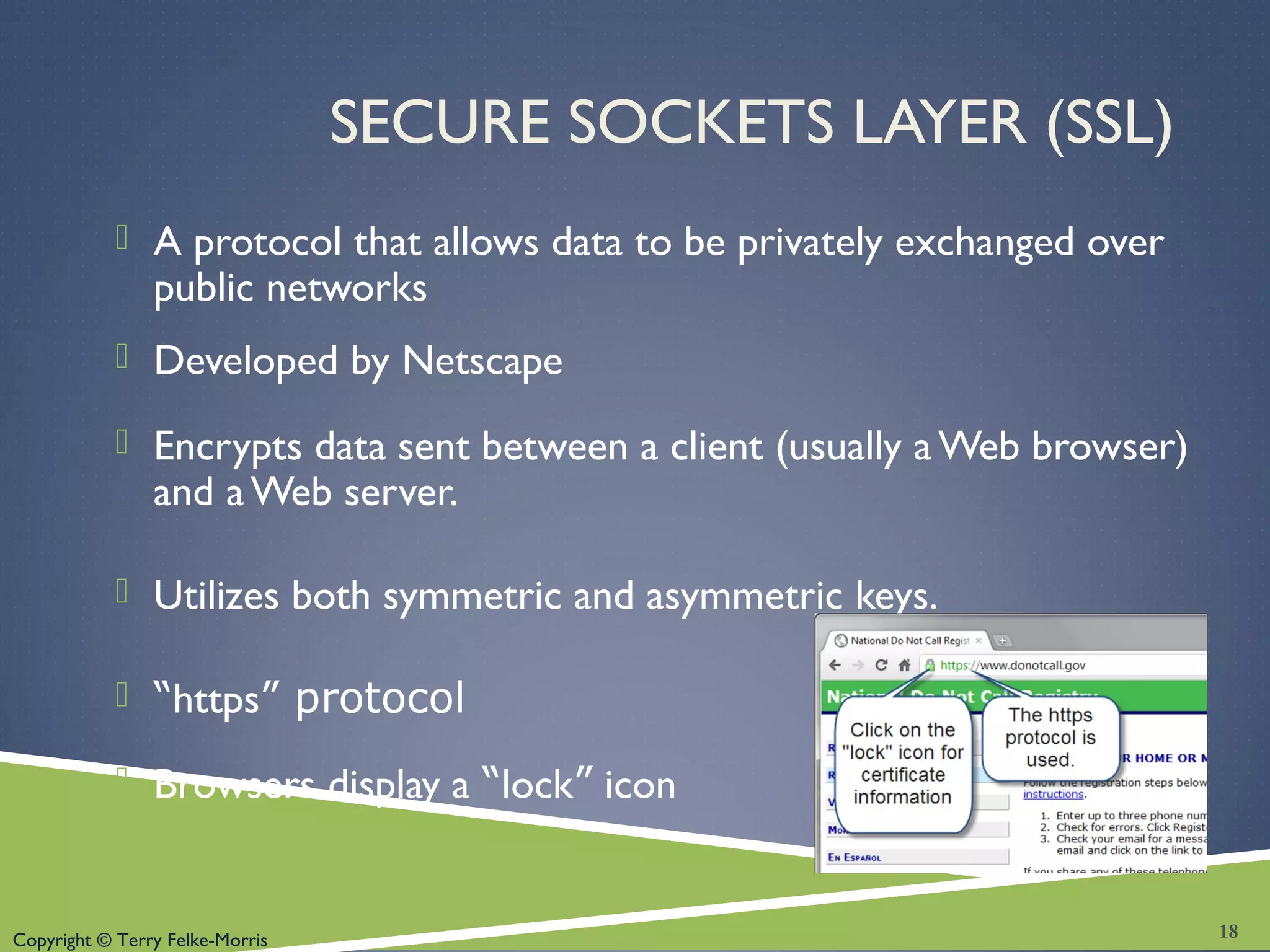
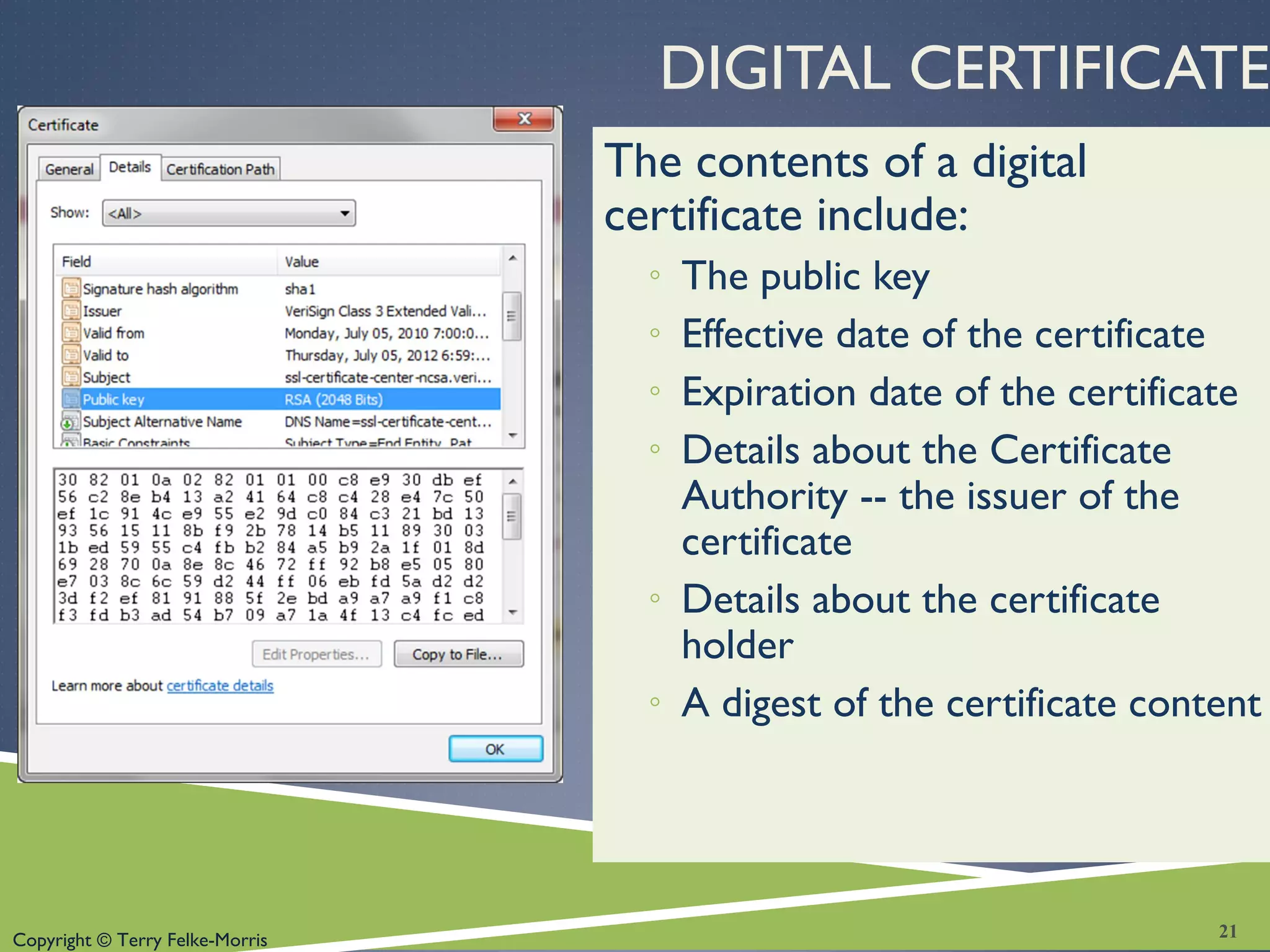
This chapter discusses e-commerce concepts such as definitions of e-commerce, business models, security methods like encryption, and trends in online retail sales. It covers advantages and risks of e-commerce for businesses and consumers. Payment processing options and solutions for building an e-commerce site are also described. The chapter aims to provide foundational knowledge of e-commerce and suggests further study in this important field of web development.