CertificationScrumDevloper
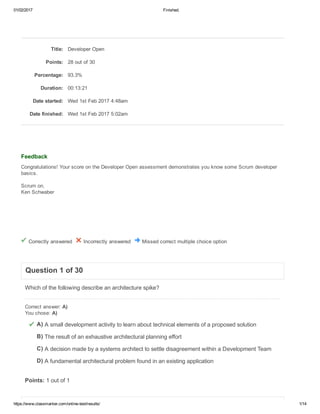
- 1. 01/02/2017 Finished. https://www.classmarker.com/onlinetest/results/ 1/14 Correctly answered Incorrectly answered Missed correct multiple choice option A) B) C) D) Title: Developer Open Points: 28 out of 30 Percentage: 93.3% Duration: 00:13:21 Date started: Wed 1st Feb 2017 4:48am Date finished: Wed 1st Feb 2017 5:02am Feedback Congratulations! Your score on the Developer Open assessment demonstrates you know some Scrum developer basics. Scrum on, Ken Schwaber Question 1 of 30 Which of the following describe an architecture spike? Correct answer: A) You chose: A) A small development activity to learn about technical elements of a proposed solution The result of an exhaustive architectural planning effort A decision made by a systems architect to settle disagreement within a Development Team A fundamental architectural problem found in an existing application Points: 1 out of 1
- 2. 01/02/2017 Finished. https://www.classmarker.com/onlinetest/results/ 2/14 A) B) C) D) E) A) B) C) D) E) Question 2 of 30 What are some shortcomings of code coverage as a measurement for how well a system or product is tested? (choose 3 answers) Correct answer: A) B) C) You chose: C) D) B) Note: This question displayed answer options in random order when taking this Test. Code coverage does not ensure that the most important or highest risk areas of the code are being exercised by tests. Code coverage does not necessarily provide functional coverage. Could create incentives to write tests that simply increase code coverage, rather than tests that find bugs without increasing coverage. Code coverage metrics vary by development platform (e.g., .NET, Java) It is too complicated to explain to management. You did not select all available correct options. Points: 0 out of 1 Feedback Code coverage is a useful metric, but not in isolation. It should not be considered a replacement for effective test design techniques. Question 3 of 30 What are two (2) ways a Development Team can ensure a good application architecture? Correct answer: C) E) You chose: C) E) Note: This question displayed answer options in random order when taking this Test. The Development Team plans a Sprint 0 at the beginning of a project with the objective of developing an architecture model used during the following Sprints. A Development Team doesn't need an architecture model in Scrum and should focus on adding functionality. The architecture will come into place without fail as the Development Team adds functionality. The Development Team should have a set of guiding architecture principles that every Development Team member understands and follows when writing code. The Development Team should assign someone to the role of software architect whose job it is to make sure a consistent architecture is developed. The Development Team plans some time each Sprint to discuss the architecture needed for the features planned in that Sprint.
- 3. 01/02/2017 Finished. https://www.classmarker.com/onlinetest/results/ 3/14 A) B) C) D) A) B) Points: 1 out of 1 Feedback There is no specific "architect" role on a Scrum team, nor is there an architecture planning Sprint. But, a good architecture doesn't just happen automatically. Guiding principles and frequent conversations on the team help ensure that the most appropriate architecture is developed as it is needed by features being developed in the current Sprint. Question 4 of 30 Which are benefits of Test Driven Development (choose all that apply). Correct answer: A) B) C) D) You chose: B) C) Note: This question displayed answer options in random order when taking this Test. It promotes good design and separation of concerns. It improves quality and reduces bugs. It causes you to construct a test harness that can be automated. It speeds the overall development process. You did not select all available correct options. Points: 0 out of 1 Question 5 of 30 Programmers and testers should not be included in refining Product Backlog items. Correct answer: B) You chose: B) True False Points: 1 out of 1 Question 6 of 30 Who should be present during Product Backlog refinement?
- 4. 01/02/2017 Finished. https://www.classmarker.com/onlinetest/results/ 4/14 A) B) C) D) E) F) A) B) C) D) Correct answer: C) D) You chose: C) D) Note: This question displayed answer options in random order when taking this Test. Only the most senior people from the Development Team. The external business analysts that have prepared the functional details. The Development Team. The Product Owner. The integration architects from the release department. The stakeholders. Points: 1 out of 1 Question 7 of 30 While changing software, you find a bug in a previously delivered piece of functionality. What should you do? Correct answer: A) You chose: A) Note: This question displayed answer options in random order when taking this Test. Fix the bug if it is critical or easily fixed. Otherwise, put the new bug into the Product Backlog to be prioritized and fixed in an upcoming Sprint. Stub out the code that caused the bug so it no longer occurs. Revise the tests so that the bug no longer appears on the bug report. Fix the bug. Points: 1 out of 1 Feedback Unless your company has specific guidance on fixing bugs, they represent work to be done and should be ordered on the Product Backlog by the PO. Two exceptions are if the work to fix the bug is less than the work to actually log it, or if the bug is so critical that it would be negligent to leave it unfixed. Question 8 of 30 What is the value of refactoring code?
- 5. 01/02/2017 Finished. https://www.classmarker.com/onlinetest/results/ 5/14 A) B) C) D) A) B) C) D) A) B) C) D) E) Correct answer: B) You chose: B) Note: This question displayed answer options in random order when taking this Test. To have all code in a single file for easy printing and code reviews. To improve readability and maintainability. To keep the code moving. To make the software faster at runtime. Points: 1 out of 1 Question 9 of 30 What is test first development? Correct answer: C) You chose: C) Note: This question displayed answer options in random order when taking this Test. Testing existing code before adding more code to it. The continuous restructuring of software to retain flexibility. Designing tests before satisfying them. Having the tester in the Development Team write the test plans before coding. Points: 1 out of 1 Question 10 of 30 Which of the following are NOT metrics of code quality? (choose all that apply) Correct answer: D) E) You chose: D) E) Note: This question displayed answer options in random order when taking this Test. Class coupling Depth of inheritance Cyclomatic complexity Lines of Code Cycle time per feature Points: 1 out of 1
- 6. 01/02/2017 Finished. https://www.classmarker.com/onlinetest/results/ 6/14 A) B) C) D) A) B) C) D) E) F) Question 11 of 30 Which of the following best describes Continuous Integration? Correct answer: A) You chose: A) Note: This question displayed answer options in random order when taking this Test. A software development practice where members of a development team integrate and verify their work frequently, often multiple times each day, to detect integration errors as quickly as possible. A software development practice where members of a development team all work on the same computer to ensure a common code base. A software development practice that continuously integrates feedback from users into software design. A software development practice used by Integration Teams to create best practice branching and merging strategies. Points: 1 out of 1 Question 12 of 30 Which are attributes of a good bug report (choose all that apply)? Correct answer: A) B) C) D) E) F) You chose: C) A) D) B) F) E) Note: This question displayed answer options in random order when taking this Test. Clear title and proper grammar in report. One bug per report. Simple and repeatable reproduction steps. Expected results and observed results. Build/version where bug was found. Screenshots or other pictures of bug in action when user interfaces are involved. Points: 1 out of 1 Question 13 of 30 Which is a benefit of establishing naming standards for code?
- 7. 01/02/2017 Finished. https://www.classmarker.com/onlinetest/results/ 7/14 A) B) C) D) A) B) C) D) A) B) Correct answer: A) You chose: A) Note: This question displayed answer options in random order when taking this Test. To make the code more readable. To communicate the name of the developer that worked on the code. To make it easy to distinguish between different software products. To ensure that "orphan functions" are not created. Points: 1 out of 1 Question 14 of 30 Which describes the practice of expressing requirements as acceptance tests? Correct answer: B) You chose: B) Note: This question displayed answer options in random order when taking this Test. Regression Testing Acceptance Test Driven Development Quality Oriented Requirements Definition. Object Driven Requirements Definition. Points: 1 out of 1 Feedback Advanced practices of testdriven development can lead to Acceptance Testdriven development (ATDD) where the criteria specified by the customer are automated into acceptance tests, which then drive the traditional unit testdriven development (UTDD) process. Question 15 of 30 Select two (2) benefits of Continuous Integration. Correct answer: C) D) You chose: C) D) Note: This question displayed answer options in random order when taking this Test. It eliminates bugs completely. The build is executed once every night and at least once each weekend.
- 8. 01/02/2017 Finished. https://www.classmarker.com/onlinetest/results/ 8/14 C) D) A) B) C) D) E) A) B) C) D) E) Causes team members to consider each other's work and context. It leads to higher transparency and rapid feedback to the team. Points: 1 out of 1 Question 16 of 30 Which are three attributes of a bad bug report? Correct answer: A) D) E) You chose: E) A) D) Note: This question displayed answer options in random order when taking this Test. Generic titles. One bug per report. Simple and repeatable reproduction steps. Vague statements or untested assumptions. Assigning blame. Points: 1 out of 1 Question 17 of 30 To refine Product Backlog items, the following activities will occur implicitly or explicitly: (Select all that apply) Correct answer: A) D) E) You chose: A) E) D) Note: This question displayed answer options in random order when taking this Test. Analysis Programming Testing Design Decomposition Points: 1 out of 1 Question 18 of 30
- 9. 01/02/2017 Finished. https://www.classmarker.com/onlinetest/results/ 9/14 A) B) C) D) A) B) A) B) C) D) You are on a Scrum Team that is enhancing an existing product. Which is the LEAST useful piece of documentation you want to have at your disposal? Correct answer: D) You chose: D) Note: This question displayed answer options in random order when taking this Test. Acceptance tests. Detailed designs. Wellstructured and named code. The full history of retrospective plans and lessons learned. Points: 1 out of 1 Question 19 of 30 Only technical writers can create documentation during a Sprint. Correct answer: B) You chose: B) True False Points: 1 out of 1 Question 20 of 30 What is a unit test? Correct answer: B) You chose: B) Note: This question displayed answer options in random order when taking this Test. A way for the team to ensure that the system satisfies the user requirements. A test that isolates and verifies individual units of source code. A way in which units of programmers ensure their code works. A technique for ensuring that units of codependent or clustered computers perform correctly. Points: 1 out of 1
- 10. 01/02/2017 Finished. https://www.classmarker.com/onlinetest/results/ 10/14 A) B) C) D) E) A) B) C) D) E) Question 21 of 30 Select four (4) desirable characteristics of a unit test. Correct answer: A) B) C) E) You chose: E) C) B) A) Note: This question displayed answer options in random order when taking this Test. The test executes fast. Code in each test is as small as possible while maintaining readability of the code. Each test is independent of other unit tests. They exercise the persistence layer of a solution. Each test makes assertions about only one logical concept. Points: 1 out of 1 Question 22 of 30 The definition of "Done" describes the work that must be completed for every Product Backlog item before it can be deemed releasable. What should the Development Team do when, during the Sprint, it finds out that a problem outside of their control blocks them from doing all this work? Correct answer: A) You chose: A) Note: This question displayed answer options in random order when taking this Test. Immediately raise the issue to the Scrum Master as an impediment. Complete the work that can be done on as much scope as possible and use the Sprint Review to plan the rest with the stakeholders. Complete the work that can be done on as much scope as possible and complete the rest during the "hardening" sprints at the end of the release. Cancel the Sprint. Stop using Scrum. Points: 1 out of 1 Question 23 of 30 Product Backlog items are refined by: Correct answer: C) You chose: C)
- 11. 01/02/2017 Finished. https://www.classmarker.com/onlinetest/results/ 11/14 A) B) C) D) A) B) C) D) A) B) Note: This question displayed answer options in random order when taking this Test. The Development Team The Business analyst and the Product Owner The Development Team and the Product Owner The Product Owner solely Points: 1 out of 1 Question 24 of 30 Why are automated builds important? Correct answer: B) You chose: B) Note: This question displayed answer options in random order when taking this Test. They are part of your "done" criteria. They provide rapid assurance that defects and configuration management issues have not been introduced. Without them you can't tell if your code works. You are unable to checkin code without one. Points: 1 out of 1 Feedback Builds are just an extra level of validation to make sure that you still have a unit of potentially shippable software. Automating builds makes that process faster. Question 25 of 30 What is pair programming? Correct answer: B) You chose: B) Note: This question displayed answer options in random order when taking this Test. The Scrum Team is divided into several twoperson Development Teams that consolidate work in a Scrum of Scrums. Two developers writing code together, providing constant peer review.
- 12. 01/02/2017 Finished. https://www.classmarker.com/onlinetest/results/ 12/14 C) D) E) A) B) C) D) A) B) C) D) A developer and a tester work together to write and test code. Managers doing performance reviews by comparing one programmer's code to another's. Two programmers write code separately. A third programmer integrates the work. Points: 1 out of 1 Question 26 of 30 When are testers and quality experts ideally included in a project? Correct answer: A) You chose: A) From the beginning and throughout all Sprints After Sprint Review When the product is feature complete After developer handoff Points: 1 out of 1 Question 27 of 30 Who is responsible for the system architecture of a product being developed using Scrum? Correct answer: C) You chose: C) Note: This question displayed answer options in random order when taking this Test. The corporate architect. The software architect. The Development Team. The architect chosen by the Development Team. Points: 1 out of 1 Question 28 of 30 What does a test written with Test Driven Development represent?
- 13. 01/02/2017 Finished. https://www.classmarker.com/onlinetest/results/ 13/14 A) B) C) D) A) B) C) D) E) A) B) Correct answer: B) You chose: B) Note: This question displayed answer options in random order when taking this Test. A bug that will be uncovered. A technical requirement that must be satisfied. Something that completes the test coverage of a system. An assignment from the lead quality engineer. Points: 1 out of 1 Feedback Since the test exists before the code that makes it pass, the test acts a requirement of the system under test. Question 29 of 30 Select three reasons why automated builds are important. Correct answer: A) B) C) You chose: C) A) B) Note: This question displayed answer options in random order when taking this Test. They allow frequent validation of the unit of software being worked on, ensuring it remains in a potentially shippable state. They support continuous integration. The build process is clearly defined and scripted, making it easy consistent and repeatable. They eliminate the need for Build Engineers. They ensure your product remains bug free. Points: 1 out of 1 Question 30 of 30 What are three advantages of Continuous Integration? Correct answer: A) C) D) You chose: D) A) C) Note: This question displayed answer options in random order when taking this Test. Broken builds are detected quickly. Readability of code is improved.
