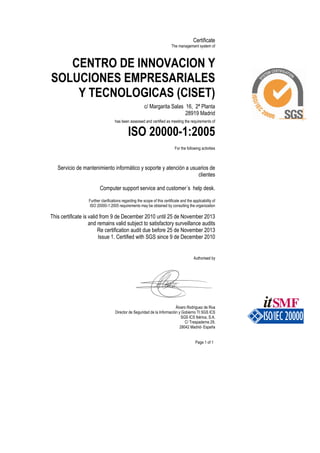
CISET. Certificacion ISO 20000
•
0 likes•608 views
CISET. Certificacion ISO 20000 de su servicio de mantenimiento informatico, soporte y atención a usuarios de clientes
Report
Share
Report
Share
Download to read offline
Recommended
CISET. Mantenimiento informático

Catalogo de servicios de CISET: Mantenimiento informaticio, monitorización de infraestructuras, gestión de redes, gestión de seguridad informatica (virus, accesos no autorizados,...) copias de seguridad
Diptico porfolio CISET

Misión y visión de la empresa CISET. Definición de Catalogo de servicios: Descripción de Servicios y Productos
CISET SAGE Estrategias Innovacion Pymes

Nota de prensa sobre la jornada de divulgación desarrollada por CISET y SAGE acerca de Estrategias de Innovación en PYMES
Recommended
CISET. Mantenimiento informático

Catalogo de servicios de CISET: Mantenimiento informaticio, monitorización de infraestructuras, gestión de redes, gestión de seguridad informatica (virus, accesos no autorizados,...) copias de seguridad
Diptico porfolio CISET

Misión y visión de la empresa CISET. Definición de Catalogo de servicios: Descripción de Servicios y Productos
CISET SAGE Estrategias Innovacion Pymes

Nota de prensa sobre la jornada de divulgación desarrollada por CISET y SAGE acerca de Estrategias de Innovación en PYMES
CISET - Certificacion ISO 27001

Certificación obtención certificado auditoria ISO 27001 para servicio de soporte usuarios TI de CISET
Implantación de help desk basado en itil en una pyme

Ponencia realizada por Emiliano Fernandez Marin, director de CISET, sobre la implantación de un help desk basado en ITIL en una Pyme, dentro del ciclo de conferencias del HELP DESK FORUM de IIR
Formando Un Departamento De Ti Enfocado A ITIL

Una aproximacion a la infomación de areas TI orientadas a Servicios.
ITIL de la Teoría a la Práctica

Presentación en EXO sobre como aplicar las mejores prácticas en la gestión de servicios de TI
Cómo optimizar tu herramienta de Service Desk

Cómo optimizar su herramienta del Service Desk
En el mercado existen múltiples herramientas para gestionar un Service Desk, no obstante antes de aventurarse a la adquisición de una herramienta, la empresa de TI debe inicialmente considerar la alineación del Service Desk a las mejores prácticas de ITIL® e ISO 20000; contar un equipo capacitado y competente en los temas para modelar el Service Desk, para luego sí proceder a la compra, adopción e implementación de una herramienta certificada en ITIL, la cual proporcionará enormes ventajas a la organización.
Click aquí para ver el video del Webinar
Descarga la presentación
Descarga la presentación
Gestion de cambios como habilitador del time to market

La apropiada gestión de los cambios contribuye con el negocio para lograr el Time to Market de los nuevos productos o servicios. Si el negocio se mueve rápido, la gestión de cambios tiene que ser ágil.
¿Todavía hay algo que mejorar en la Gestión de Incidentes?

En la mejora de la Gestión de Incidentes podemos toparnos con dos perspectiva: la del Usuario y la del Cliente (El Negocio). A través de esta presentación estudiaremos: Las necesidades y expectativas del usuario; la meta y objetivos de la Gestión de Incidentes;rol de Service Desk en la Gestión de Incidentes; el proceso de Gestión de Incidentes; ¿cómo lo hacemos?; un Service Desk que resuelva; responsabilidades de los grupos de soporte; ¿cómo asegurar que se logre?.
El Catálogo de Servicio de TI con vista al negocio

El Catálogo de Servicio de TI generalmente es confundido con el Catálogo de Solicitudes de Servicio que utiliza el Service Desk. Pero aunque suenen parecido no son lo mismo. En una organización de TI este instrumento es clave porque es el registro de productos y servicios que se usa para describirlos, publicarlos y promoverlos.
Mobile Technologies Solution Showcase

Solution Showcase by Mobile Technologies at the C2C Summit 2022
Common Criteria service overview for Developers - jtsec a CC consultancy company

We can help you to pass a Common Criteria evaluation, we know the tips & the tricks and can help you to save a lot of money. Obtain a Common Criteria Certification assisted by our experts.
More Related Content
Viewers also liked
CISET - Certificacion ISO 27001

Certificación obtención certificado auditoria ISO 27001 para servicio de soporte usuarios TI de CISET
Implantación de help desk basado en itil en una pyme

Ponencia realizada por Emiliano Fernandez Marin, director de CISET, sobre la implantación de un help desk basado en ITIL en una Pyme, dentro del ciclo de conferencias del HELP DESK FORUM de IIR
Formando Un Departamento De Ti Enfocado A ITIL

Una aproximacion a la infomación de areas TI orientadas a Servicios.
ITIL de la Teoría a la Práctica

Presentación en EXO sobre como aplicar las mejores prácticas en la gestión de servicios de TI
Cómo optimizar tu herramienta de Service Desk

Cómo optimizar su herramienta del Service Desk
En el mercado existen múltiples herramientas para gestionar un Service Desk, no obstante antes de aventurarse a la adquisición de una herramienta, la empresa de TI debe inicialmente considerar la alineación del Service Desk a las mejores prácticas de ITIL® e ISO 20000; contar un equipo capacitado y competente en los temas para modelar el Service Desk, para luego sí proceder a la compra, adopción e implementación de una herramienta certificada en ITIL, la cual proporcionará enormes ventajas a la organización.
Click aquí para ver el video del Webinar
Descarga la presentación
Descarga la presentación
Gestion de cambios como habilitador del time to market

La apropiada gestión de los cambios contribuye con el negocio para lograr el Time to Market de los nuevos productos o servicios. Si el negocio se mueve rápido, la gestión de cambios tiene que ser ágil.
¿Todavía hay algo que mejorar en la Gestión de Incidentes?

En la mejora de la Gestión de Incidentes podemos toparnos con dos perspectiva: la del Usuario y la del Cliente (El Negocio). A través de esta presentación estudiaremos: Las necesidades y expectativas del usuario; la meta y objetivos de la Gestión de Incidentes;rol de Service Desk en la Gestión de Incidentes; el proceso de Gestión de Incidentes; ¿cómo lo hacemos?; un Service Desk que resuelva; responsabilidades de los grupos de soporte; ¿cómo asegurar que se logre?.
El Catálogo de Servicio de TI con vista al negocio

El Catálogo de Servicio de TI generalmente es confundido con el Catálogo de Solicitudes de Servicio que utiliza el Service Desk. Pero aunque suenen parecido no son lo mismo. En una organización de TI este instrumento es clave porque es el registro de productos y servicios que se usa para describirlos, publicarlos y promoverlos.
Viewers also liked (16)
Implantación de help desk basado en itil en una pyme

Implantación de help desk basado en itil en una pyme
Gestion de cambios como habilitador del time to market

Gestion de cambios como habilitador del time to market
¿Todavía hay algo que mejorar en la Gestión de Incidentes?

¿Todavía hay algo que mejorar en la Gestión de Incidentes?
El Catálogo de Servicio de TI con vista al negocio

El Catálogo de Servicio de TI con vista al negocio
Similar to CISET. Certificacion ISO 20000
Mobile Technologies Solution Showcase

Solution Showcase by Mobile Technologies at the C2C Summit 2022
Common Criteria service overview for Developers - jtsec a CC consultancy company

We can help you to pass a Common Criteria evaluation, we know the tips & the tricks and can help you to save a lot of money. Obtain a Common Criteria Certification assisted by our experts.
ICT for Covid-19 (Novel Coronavirus) Risk Response

The COVID-19 pandemic is now a major global health threat. In the midst of this turmoil, Information and Communications Technology (ICT) has played an essential role in facilitating the safe relief and treatment of affected populations. ICT has also
shown itself to be essential both to bolstering long term
resiliency against future pandemics and to resolving the secondary challenges that emerge within a socially distanced environment.
https://www.linkedin.com/posts/yalcin-gerek-34b7a21_ict-for-covid-19-novel-coronavirus-risk-activity-6682552645619634176-38E2
A Lean production project in software development at AlmavivA - Lean IT Summi...

A Lean production project in software development at AlmavivA - Lean IT Summi...Institut Lean France
AlmavivA is the leading ICT company in Italy. At the Lean IT Summit 2014, Giuseppe Conigliaro, director of software engineering presented the Lean IT project and the results the teams achieved with it.
More Lean IT stories on www.lean-it-summit.comI Forum GSTI - David Bathiely

Gerenciamento de Serviços de TI baseado na ISO/IEC 20000
David Bathiely - EXIN França
Similar to CISET. Certificacion ISO 20000 (14)
Common Criteria service overview for Developers - jtsec a CC consultancy company

Common Criteria service overview for Developers - jtsec a CC consultancy company
ICT for Covid-19 (Novel Coronavirus) Risk Response

ICT for Covid-19 (Novel Coronavirus) Risk Response
JMD Etiquettes : Tailor made technical tag manufacturer GB

JMD Etiquettes : Tailor made technical tag manufacturer GB
A Lean production project in software development at AlmavivA - Lean IT Summi...

A Lean production project in software development at AlmavivA - Lean IT Summi...
More from CISET. Mantenimiento informático
Microsoft Authorized Education Partner

This is to certify CISET is authorized as a Microsoft Authorized Education Partner - Academic Volume Licensing - from May 3 2018 until May 2 2019. Authorization Number: V108897
CISET. Mantenimiento informático

Presentación corporativa de la empresa CISET. Mantenimiento informático. Ofrecemos servicios de mantenimiento informático y consultoría y tenemos una amplia experiencia en servicios TI. Nuestro sistema de gestión se basa en ISO 20000 y 27001. Cubrimos todo el rango de servicios de asistencia y consultoría informática, lo que nos permite presentarnos a nuestros clientes como proveedor único de soluciones tecnológicas. Nuestra misión es ser el mejor socio de nuestros clientes para convertir la tecnología en una herramienta estratégica para su negocio. Ofrecemos servicios de mantenimiento informático, seguridad informática, soluciones empresariales y renting tecnológico.
Software Agencias de colocación

Sistema software para las Agencias de colocación: gestión de ofertas de trabajo, gestión de bolsa de empleo especialmente dirigido a centros y agencias de empleo local, organismos autónomos, agencias de colocación y servicios universitarios de empleo.
Software ERP Pymes - Connsultoría CISET

Software ERPs, soluciones de gestión al alcance de las PyMES.
Gestion del conocimiento en la Gestión de Servicios TI

Utilización de tecnologías de tratamietno de información y gestión del conocimiento en la gestión de servicios de TI. Ponencia desarrollada por Emiliano Fernández en el Congreso Academico de ITSMF de 2009
CISET Servicios Informaticos

CISET. Servicios informaticos para pequeñas y medianas empresas: mantenimiento informático, ingeniera de sistema, soporte de redes, consultoría tecnológica. Desarrollo de proyectos
More from CISET. Mantenimiento informático (6)
Gestion del conocimiento en la Gestión de Servicios TI

Gestion del conocimiento en la Gestión de Servicios TI
Recently uploaded
Artificial Intelligence for XMLDevelopment

In the rapidly evolving landscape of technologies, XML continues to play a vital role in structuring, storing, and transporting data across diverse systems. The recent advancements in artificial intelligence (AI) present new methodologies for enhancing XML development workflows, introducing efficiency, automation, and intelligent capabilities. This presentation will outline the scope and perspective of utilizing AI in XML development. The potential benefits and the possible pitfalls will be highlighted, providing a balanced view of the subject.
We will explore the capabilities of AI in understanding XML markup languages and autonomously creating structured XML content. Additionally, we will examine the capacity of AI to enrich plain text with appropriate XML markup. Practical examples and methodological guidelines will be provided to elucidate how AI can be effectively prompted to interpret and generate accurate XML markup.
Further emphasis will be placed on the role of AI in developing XSLT, or schemas such as XSD and Schematron. We will address the techniques and strategies adopted to create prompts for generating code, explaining code, or refactoring the code, and the results achieved.
The discussion will extend to how AI can be used to transform XML content. In particular, the focus will be on the use of AI XPath extension functions in XSLT, Schematron, Schematron Quick Fixes, or for XML content refactoring.
The presentation aims to deliver a comprehensive overview of AI usage in XML development, providing attendees with the necessary knowledge to make informed decisions. Whether you’re at the early stages of adopting AI or considering integrating it in advanced XML development, this presentation will cover all levels of expertise.
By highlighting the potential advantages and challenges of integrating AI with XML development tools and languages, the presentation seeks to inspire thoughtful conversation around the future of XML development. We’ll not only delve into the technical aspects of AI-powered XML development but also discuss practical implications and possible future directions.
How to Get CNIC Information System with Paksim Ga.pptx

Pakdata Cf is a groundbreaking system designed to streamline and facilitate access to CNIC information. This innovative platform leverages advanced technology to provide users with efficient and secure access to their CNIC details.
Large Language Model (LLM) and it’s Geospatial Applications

Large Language Model (LLM) and it’s Geospatial Applications.
20240607 QFM018 Elixir Reading List May 2024

Everything I found interesting about the Elixir programming ecosystem in May 2024
GridMate - End to end testing is a critical piece to ensure quality and avoid...

End to end testing is a critical piece to ensure quality and avoid regressions. In this session, we share our journey building an E2E testing pipeline for GridMate components (LWC and Aura) using Cypress, JSForce, FakerJS…
Encryption in Microsoft 365 - ExpertsLive Netherlands 2024

In this session I delve into the encryption technology used in Microsoft 365 and Microsoft Purview. Including the concepts of Customer Key and Double Key Encryption.
Mind map of terminologies used in context of Generative AI

Mind map of common terms used in context of Generative AI.
Alt. GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using ...

Effective Application Security in Software Delivery lifecycle using Deployment Firewall and DBOM
The modern software delivery process (or the CI/CD process) includes many tools, distributed teams, open-source code, and cloud platforms. Constant focus on speed to release software to market, along with the traditional slow and manual security checks has caused gaps in continuous security as an important piece in the software supply chain. Today organizations feel more susceptible to external and internal cyber threats due to the vast attack surface in their applications supply chain and the lack of end-to-end governance and risk management.
The software team must secure its software delivery process to avoid vulnerability and security breaches. This needs to be achieved with existing tool chains and without extensive rework of the delivery processes. This talk will present strategies and techniques for providing visibility into the true risk of the existing vulnerabilities, preventing the introduction of security issues in the software, resolving vulnerabilities in production environments quickly, and capturing the deployment bill of materials (DBOM).
Speakers:
Bob Boule
Robert Boule is a technology enthusiast with PASSION for technology and making things work along with a knack for helping others understand how things work. He comes with around 20 years of solution engineering experience in application security, software continuous delivery, and SaaS platforms. He is known for his dynamic presentations in CI/CD and application security integrated in software delivery lifecycle.
Gopinath Rebala
Gopinath Rebala is the CTO of OpsMx, where he has overall responsibility for the machine learning and data processing architectures for Secure Software Delivery. Gopi also has a strong connection with our customers, leading design and architecture for strategic implementations. Gopi is a frequent speaker and well-known leader in continuous delivery and integrating security into software delivery.
Microsoft - Power Platform_G.Aspiotis.pdf

Revolutionizing Application Development
with AI-powered low-code, presentation by George Aspiotis, Sr. Partner Development Manager, Microsoft
Why You Should Replace Windows 11 with Nitrux Linux 3.5.0 for enhanced perfor...

The choice of an operating system plays a pivotal role in shaping our computing experience. For decades, Microsoft's Windows has dominated the market, offering a familiar and widely adopted platform for personal and professional use. However, as technological advancements continue to push the boundaries of innovation, alternative operating systems have emerged, challenging the status quo and offering users a fresh perspective on computing.
One such alternative that has garnered significant attention and acclaim is Nitrux Linux 3.5.0, a sleek, powerful, and user-friendly Linux distribution that promises to redefine the way we interact with our devices. With its focus on performance, security, and customization, Nitrux Linux presents a compelling case for those seeking to break free from the constraints of proprietary software and embrace the freedom and flexibility of open-source computing.
Communications Mining Series - Zero to Hero - Session 1

This session provides introduction to UiPath Communication Mining, importance and platform overview. You will acquire a good understand of the phases in Communication Mining as we go over the platform with you. Topics covered:
• Communication Mining Overview
• Why is it important?
• How can it help today’s business and the benefits
• Phases in Communication Mining
• Demo on Platform overview
• Q/A
Climate Impact of Software Testing at Nordic Testing Days

My slides at Nordic Testing Days 6.6.2024
Climate impact / sustainability of software testing discussed on the talk. ICT and testing must carry their part of global responsibility to help with the climat warming. We can minimize the carbon footprint but we can also have a carbon handprint, a positive impact on the climate. Quality characteristics can be added with sustainability, and then measured continuously. Test environments can be used less, and in smaller scale and on demand. Test techniques can be used in optimizing or minimizing number of tests. Test automation can be used to speed up testing.
GraphSummit Singapore | Neo4j Product Vision & Roadmap - Q2 2024

Maruthi Prithivirajan, Head of ASEAN & IN Solution Architecture, Neo4j
Get an inside look at the latest Neo4j innovations that enable relationship-driven intelligence at scale. Learn more about the newest cloud integrations and product enhancements that make Neo4j an essential choice for developers building apps with interconnected data and generative AI.
A tale of scale & speed: How the US Navy is enabling software delivery from l...

Rapid and secure feature delivery is a goal across every application team and every branch of the DoD. The Navy’s DevSecOps platform, Party Barge, has achieved:
- Reduction in onboarding time from 5 weeks to 1 day
- Improved developer experience and productivity through actionable findings and reduction of false positives
- Maintenance of superior security standards and inherent policy enforcement with Authorization to Operate (ATO)
Development teams can ship efficiently and ensure applications are cyber ready for Navy Authorizing Officials (AOs). In this webinar, Sigma Defense and Anchore will give attendees a look behind the scenes and demo secure pipeline automation and security artifacts that speed up application ATO and time to production.
We will cover:
- How to remove silos in DevSecOps
- How to build efficient development pipeline roles and component templates
- How to deliver security artifacts that matter for ATO’s (SBOMs, vulnerability reports, and policy evidence)
- How to streamline operations with automated policy checks on container images
LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...

Do you want to learn how to model and simulate an electrical network from scratch in under an hour?
Then welcome to this PowSyBl workshop, hosted by Rte, the French Transmission System Operator (TSO)!
During the webinar, you will discover the PowSyBl ecosystem as well as handle and study an electrical network through an interactive Python notebook.
PowSyBl is an open source project hosted by LF Energy, which offers a comprehensive set of features for electrical grid modelling and simulation. Among other advanced features, PowSyBl provides:
- A fully editable and extendable library for grid component modelling;
- Visualization tools to display your network;
- Grid simulation tools, such as power flows, security analyses (with or without remedial actions) and sensitivity analyses;
The framework is mostly written in Java, with a Python binding so that Python developers can access PowSyBl functionalities as well.
What you will learn during the webinar:
- For beginners: discover PowSyBl's functionalities through a quick general presentation and the notebook, without needing any expert coding skills;
- For advanced developers: master the skills to efficiently apply PowSyBl functionalities to your real-world scenarios.
20240605 QFM017 Machine Intelligence Reading List May 2024

Everything I found interesting about machines behaving intelligently during May 2024
National Security Agency - NSA mobile device best practices

Threats to mobile devices are more prevalent and increasing in scope and complexity. Users of mobile devices desire to take full advantage of the features
available on those devices, but many of the features provide convenience and capability but sacrifice security. This best practices guide outlines steps the users can take to better protect personal devices and information.
Elizabeth Buie - Older adults: Are we really designing for our future selves?

Elizabeth Buie - Older adults: Are we really designing for our future selves?
Pushing the limits of ePRTC: 100ns holdover for 100 days

At WSTS 2024, Alon Stern explored the topic of parametric holdover and explained how recent research findings can be implemented in real-world PNT networks to achieve 100 nanoseconds of accuracy for up to 100 days.
Recently uploaded (20)
How to Get CNIC Information System with Paksim Ga.pptx

How to Get CNIC Information System with Paksim Ga.pptx
Large Language Model (LLM) and it’s Geospatial Applications

Large Language Model (LLM) and it’s Geospatial Applications
GridMate - End to end testing is a critical piece to ensure quality and avoid...

GridMate - End to end testing is a critical piece to ensure quality and avoid...
Encryption in Microsoft 365 - ExpertsLive Netherlands 2024

Encryption in Microsoft 365 - ExpertsLive Netherlands 2024
Mind map of terminologies used in context of Generative AI

Mind map of terminologies used in context of Generative AI
Alt. GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using ...

Alt. GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using ...
Why You Should Replace Windows 11 with Nitrux Linux 3.5.0 for enhanced perfor...

Why You Should Replace Windows 11 with Nitrux Linux 3.5.0 for enhanced perfor...
Communications Mining Series - Zero to Hero - Session 1

Communications Mining Series - Zero to Hero - Session 1
Climate Impact of Software Testing at Nordic Testing Days

Climate Impact of Software Testing at Nordic Testing Days
GraphSummit Singapore | Neo4j Product Vision & Roadmap - Q2 2024

GraphSummit Singapore | Neo4j Product Vision & Roadmap - Q2 2024
A tale of scale & speed: How the US Navy is enabling software delivery from l...

A tale of scale & speed: How the US Navy is enabling software delivery from l...
LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...

LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...
20240605 QFM017 Machine Intelligence Reading List May 2024

20240605 QFM017 Machine Intelligence Reading List May 2024
National Security Agency - NSA mobile device best practices

National Security Agency - NSA mobile device best practices
Elizabeth Buie - Older adults: Are we really designing for our future selves?

Elizabeth Buie - Older adults: Are we really designing for our future selves?
Pushing the limits of ePRTC: 100ns holdover for 100 days

Pushing the limits of ePRTC: 100ns holdover for 100 days
CISET. Certificacion ISO 20000
- 1. Certificate The management system of CENTRO DE INNOVACION Y SOLUCIONES EMPRESARIALES Y TECNOLOGICAS (CISET) c/ Margarita Salas 16, 2ª Planta 28919 Madrid has been assessed and certified as meeting the requirements of ISO 20000-1:2005 For the following activities Servicio de mantenimiento informático y soporte y atención a usuarios de clientes Computer support service and customer´s help desk. Further clarifications regarding the scope of this certificate and the applicability of ISO 20000-1:2005 requirements may be obtained by consulting the organization This certificate is valid from 9 de December 2010 until 25 de November 2013 and remains valid subject to satisfactory surveillance audits Re certification audit due before 25 de November 2013 Issue 1. Certified with SGS since 9 de December 2010 Authorised by Álvaro Rodriguez de Roa Director de Seguridad de la Información y Gobierno TI SGS ICS SGS ICS Ibérica, S.A. C/ Trespaderne 29, 28042 Madrid- España Page 1 of 1
