CA_TST2
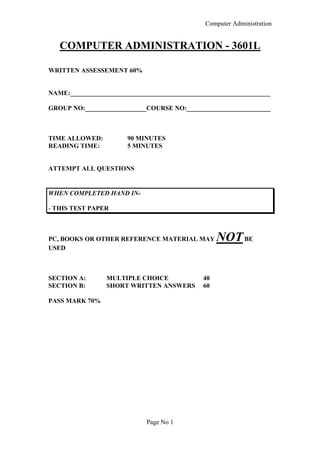
- 1. Computer Administration Page No 1 COMPUTER ADMINISTRATION - 3601L WRITTEN ASSESSEMENT 60% NAME:______________________________________________________________ GROUP NO:___________________COURSE NO:__________________________ TIME ALLOWED: 90 MINUTES READING TIME: 5 MINUTES ATTEMPT ALL QUESTIONS WHEN COMPLETED HAND IN- - THIS TEST PAPER PC, BOOKS OR OTHER REFERENCE MATERIAL MAY NOTBE USED SECTION A: MULTIPLE CHOICE 40 SECTION B: SHORT WRITTEN ANSWERS 60 PASS MARK 70%
- 2. Computer Administration Page No 2 SECTION A - MULTIPLE CHOICE Circle the correct answers SAMPLE: e.g.: Which of the following groups are input devices only? a/ printer, keyboard, scanner b/ keyboard, scanner, mouse c/ monitor, printer, mouse d/ printer, keyboard, monitor THE FIRST 20 QUESTIONS ARE WORTH TWO MARKS EACH 1 Wordprocessors, data-bases and spreadsheet programs are examples of: a/ operating systems b/ custom-build software c/ application packages d/ firmware 2 Which of the following has the least in common with the other three ? a/ CD-ROM b/ mouse c/ magnetic disk d/ memory 3 You are to supply software for checking the profits and losses on daily trading on the stock exchange. The formula and base figures change frequently depending on market activity. Which of the following would you recommend as the most suitable package to meet this requirement ? a/ wordprocessor b/ spreadsheet c/ graphics package d/ CAD package
- 3. Computer Administration Page No 3 4 You are to supply hardware to an architect who designs house plans. The architect already has an industry-standard PC. Which of the following would you recommend as the most suitable hardware/software combination to meet this requirement ? a/ CMS package and dot-matrix printer b/ CAD package and plan driver c/ CAD package and plotter d/ Drawing package and OCR 5 Which of the following is an effect of a virus ? a/ slows down the system b/ prevents access to programs c/ destroys programs d/ all of the above 6 Which of the following is not usually affected by a virus ? a/ data files b/ program files c/ boot sector d/ memory 7 When using virus protection software, which of the following should the computer user do ? a/ keep the virus protection software in a virus protected disk area b/ load the virus protection software in high memory area c/ copy the virus protection software to another virus-free disk d/ load the watch version of the software as a resident program 8 Select one word in the list below that refers to virus activity ? a/ polymorphic b/ polygraphic c/ polyphase d/ polyoptic 9 From the list below, select the duty which is most likely to be carried out by a computer administrator: a/ keeps records of computer purchases b/ maintain records of help desk calls c/ provide user support and advise d/ all of the above
- 4. Computer Administration Page No 4 10 An author’s exclusive right to print, publish and sell work is called : a/ legal copy b/ copyright c/ software license d/ property rights 11 A key role for a computer administrator is to: a/ write system requirement specifications b/ change software when needed c/ assist users to make the most out of their computer resources d/ deliver the main lectures at software training sessions 12 A major reason why companies unknowingly infringe copyright laws is: a/ they purchase large volumes of software b/ they purchase at discount prices c/ they don’t monitor the number of machines on which software is installed d/ employees bring their own software to work e/ company records get into a mess TRUE/FALSE QUESTIONS 13 A virus is data stored on a computer disk T F 14 Diskettes are a cheap and easy medium for backups T F 15 Software piracy is a way of breaking copyright law T F 16 In most situations a restoration of files from backup copies is required if a new hard disk is installed T F 17 The word modem is made from the first letters of the words method of depacking modules T F 18 Fixing first-level (simple) hardware faults is done by a computer administrator T F 19 Software Integration is undesirable because it slows down the user’s productivity T F 20 A dot-matrix printer is usually used for high quality graphic output T F
- 5. Computer Administration Page No 5 SECTION B - WRITTEN ANSWERS 21 You are employed as a computer administrator for a small financial institution. They have over 200,000 records which 30% of they records are altered daily. What type or types of backup would you implement to be suitable for such an organisation. Give your reason. (10) _______________________________________________________________ _______________________________________________________________ _______________________________________________________________ _______________________________________________________________ _______________________________________________________________ _______________________________________________________________ _______________________________________________________________ _______________________________________________________________ _______________________________________________________________ _______________________________________________________________ 21 You have been asked by your superior what is the difference between a word processor and a desktop publishing program. Write down your answer stating advantages and disadvantages for each program. (5) _______________________________________________________________ _______________________________________________________________ _______________________________________________________________ _______________________________________________________________ _______________________________________________________________ _______________________________________________________________ _______________________________________________________________
- 6. Computer Administration Page No 6 22 You have been requested to set up a stand-alone computer system for the supervisors secretary. The computer is to be ‘modern’ with the latest ‘ease of use’ software. Accountancy records and word processing are the computers main functions Fill in the table below what equipment should be purchased and it’s approximate cost. (10) Hardware App Cost Computer Hardware Input Devices Output devices Other Devices Software Operating System Software Applications Other Items Total
- 7. Computer Administration Page No 7 23 Explain what rights a person acquires on a purchasing a software package. (5) _______________________________________________________________ _______________________________________________________________ _______________________________________________________________ _______________________________________________________________ _______________________________________________________________ _______________________________________________________________ 24 In a five-point form, present a policy to be given to a company’s employees to protect the company’s computers from viruses. (5) 1______________________________________________________________ 2______________________________________________________________ 3______________________________________________________________ 4______________________________________________________________ 5______________________________________________________________ 25 List several factors (minimum four) that must be considered when purchasing computer software for an organisation. (5) ___________________________________________________________ ___________________________________________________________ ___________________________________________________________ ___________________________________________________________ ___________________________________________________________ ___________________________________________________________
- 8. Computer Administration Page No 8 26 In a six-point form what safety features would you implement in a computer based office environment. (10) 1__________________________________________________________ 2__________________________________________________________ 3__________________________________________________________ 4__________________________________________________________ 5__________________________________________________________ 6__________________________________________________________ 27 What is the significance of keeping and maintaining Hardware and Software Inventory forms ? (5) _______________________________________________________________ _______________________________________________________________ _______________________________________________________________ _______________________________________________________________ _______________________________________________________________ 28 A special ‘In-house’ software is being developed for your business and is near completion. What type of training procedure should be implemented for your staff.- Give reasons. (5) _______________________________________________________________ _______________________________________________________________ _______________________________________________________________ _______________________________________________________________ _______________________________________________________________ _______________________________________________________________ _______________________________________________________________