Embed presentation
Download to read offline


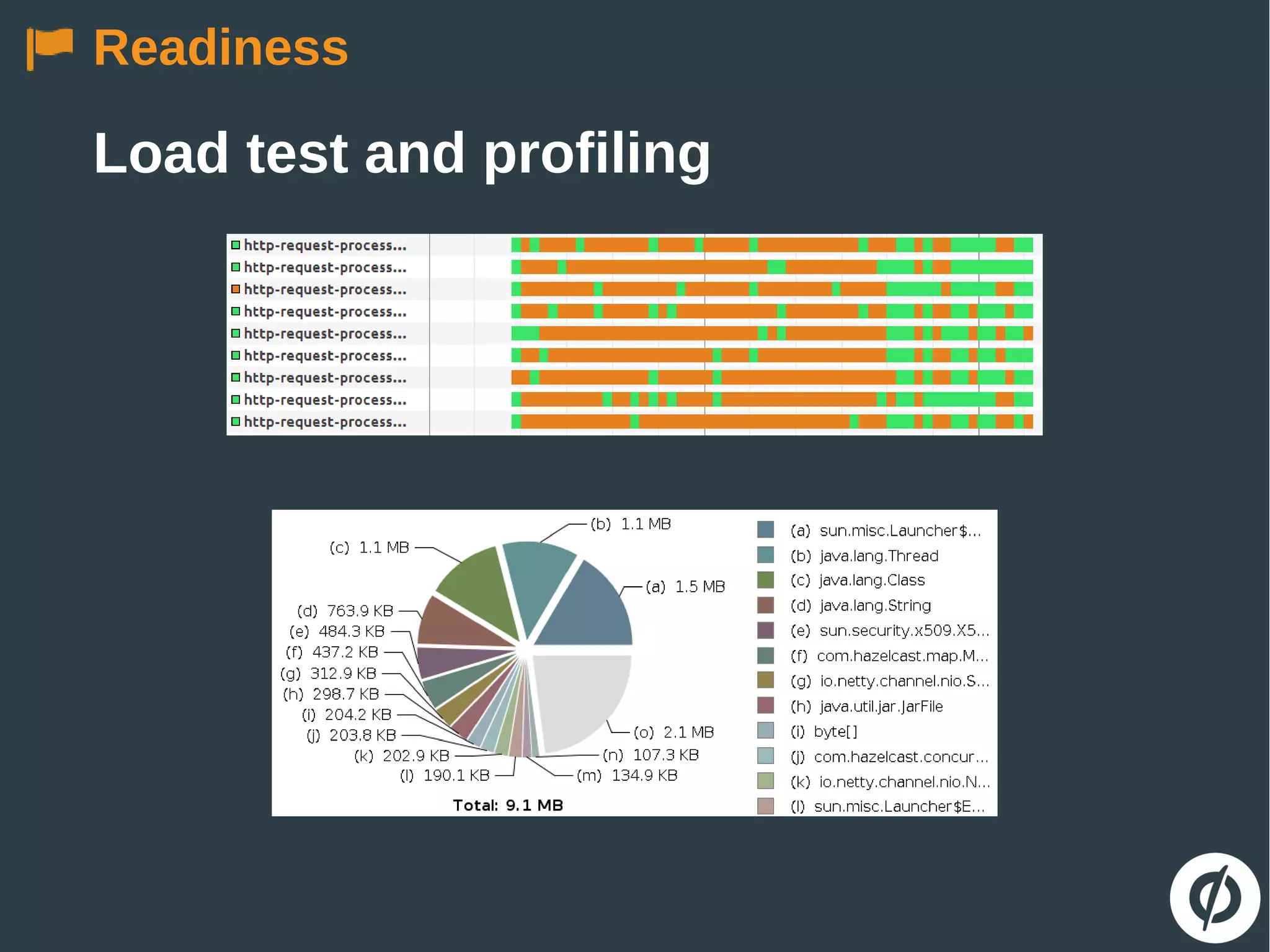
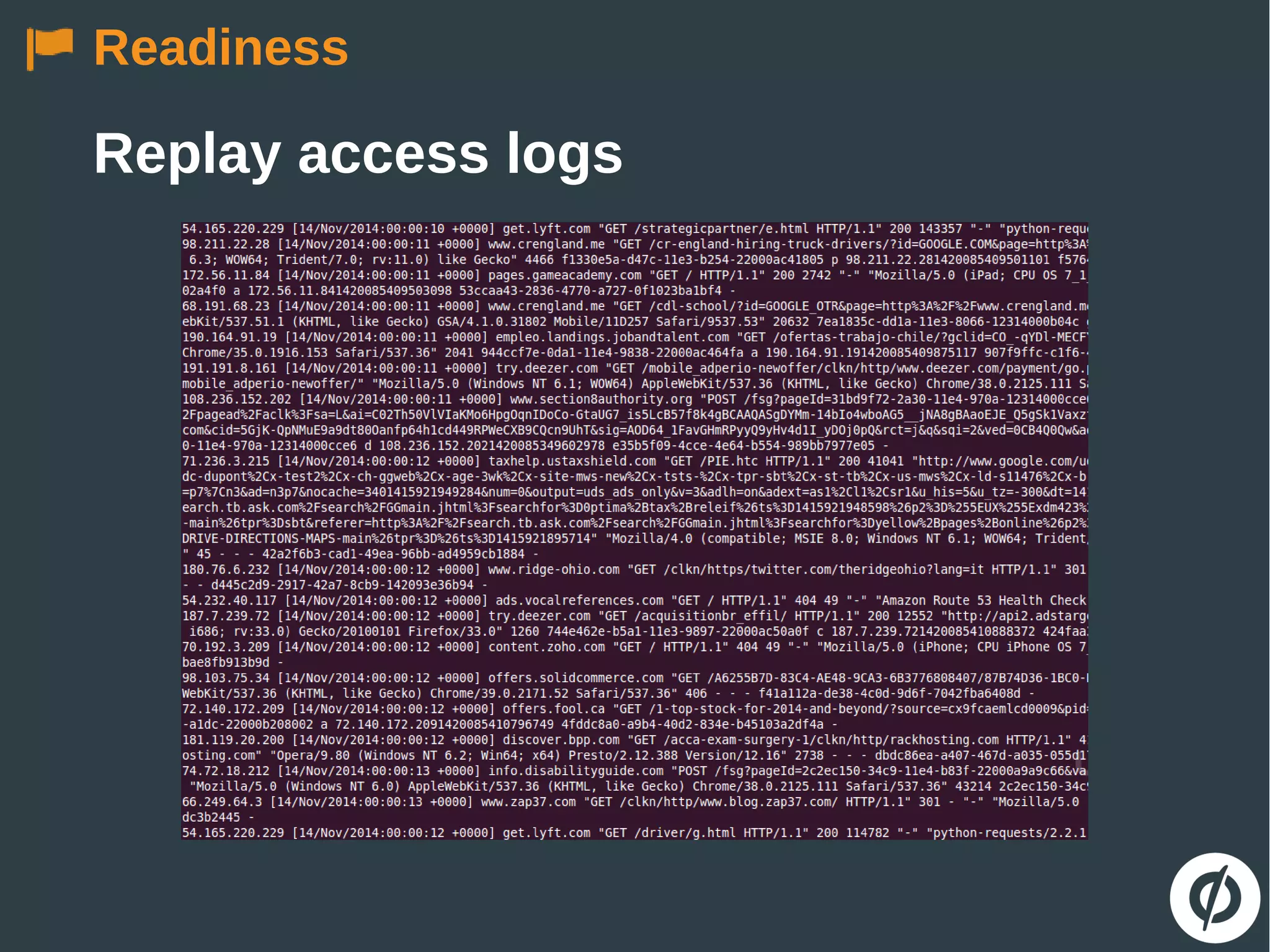
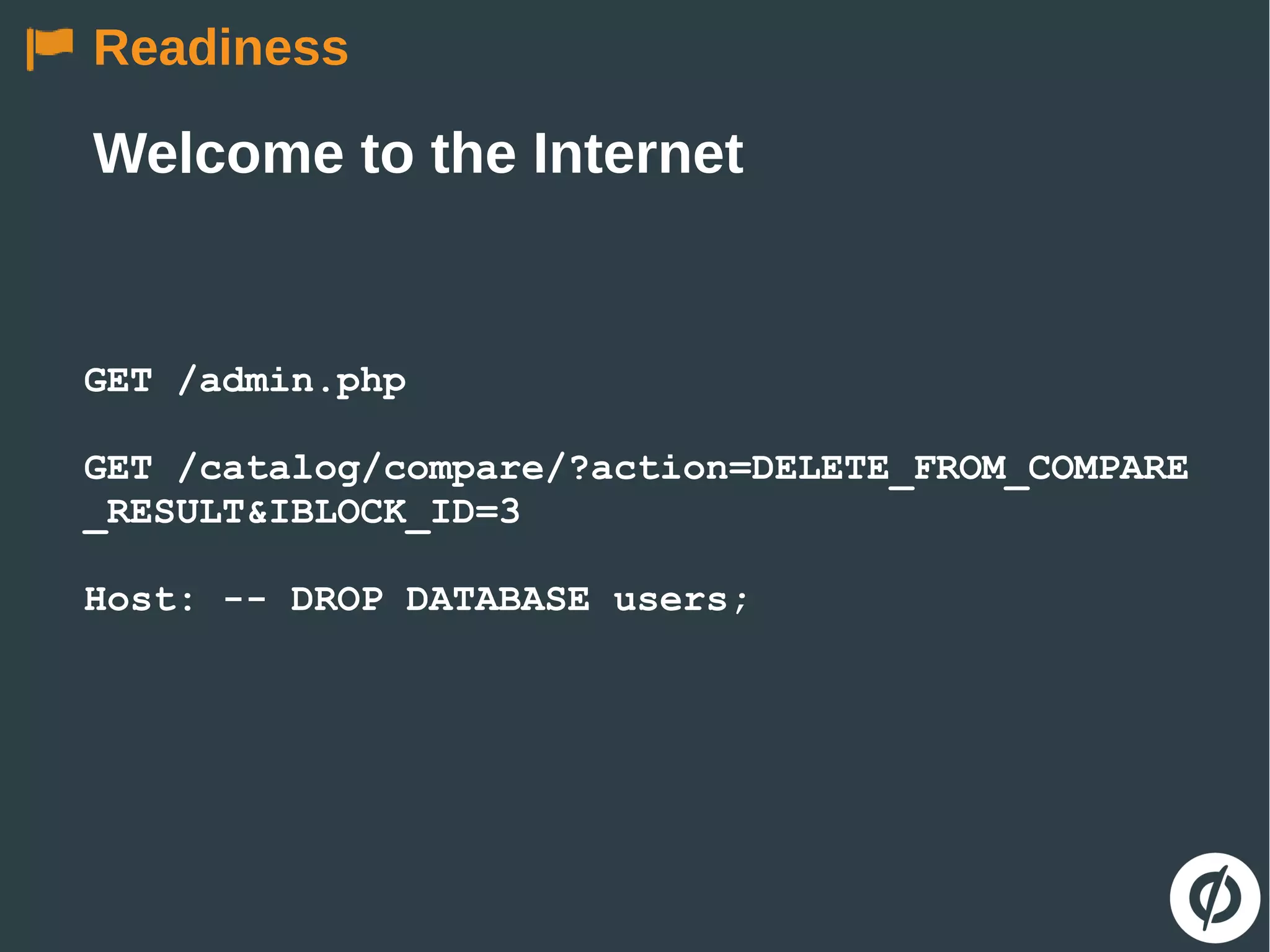
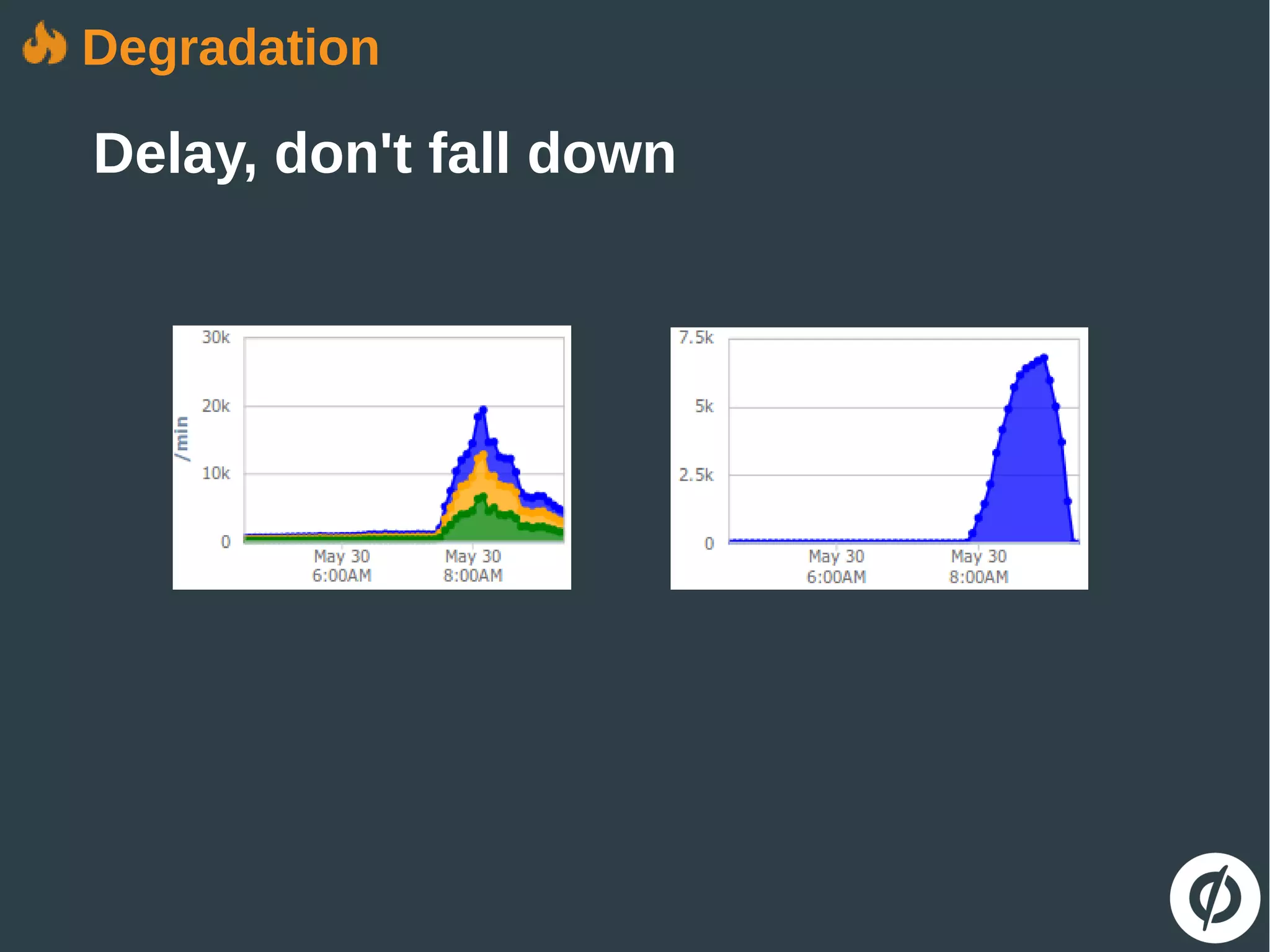

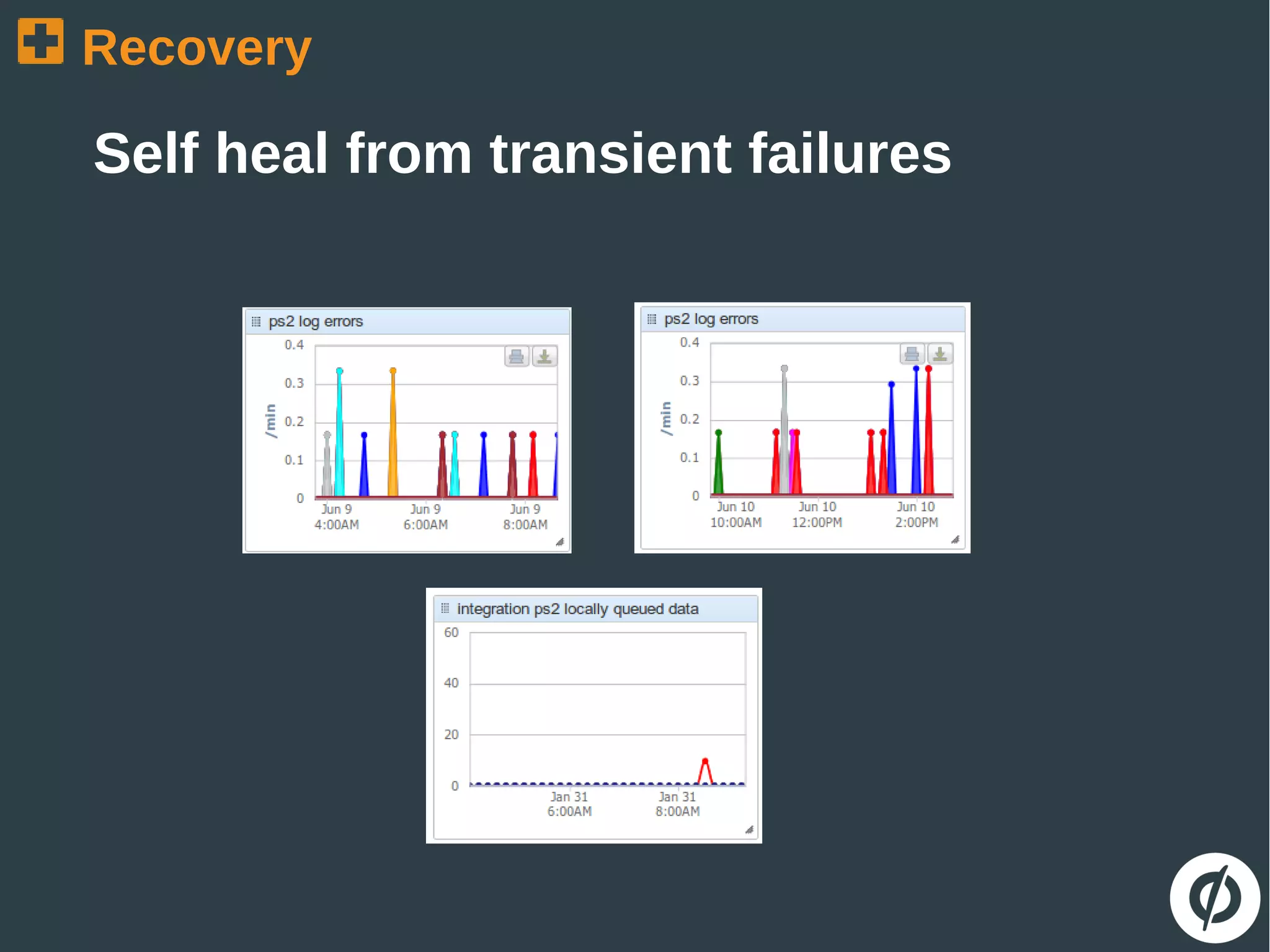
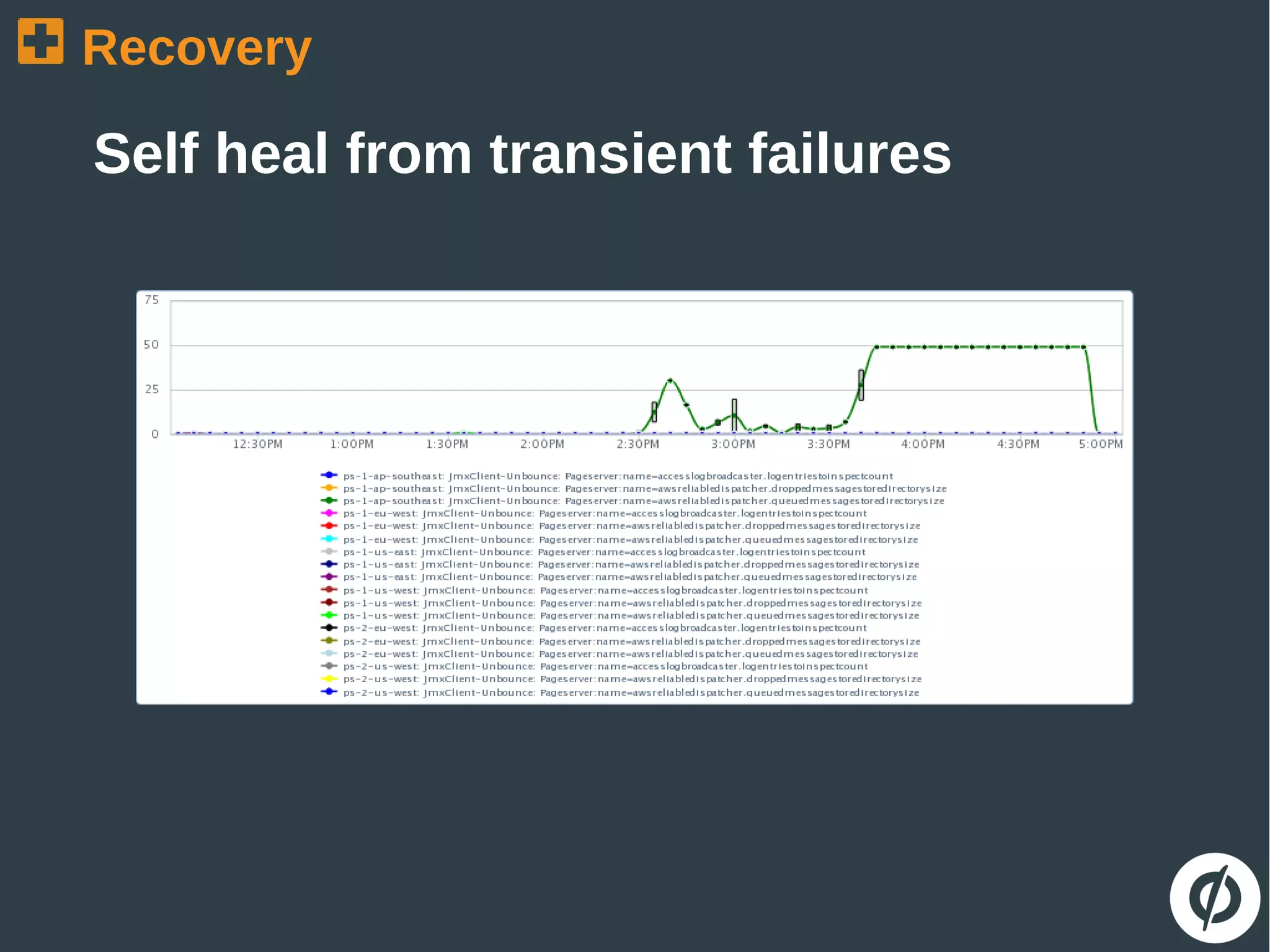




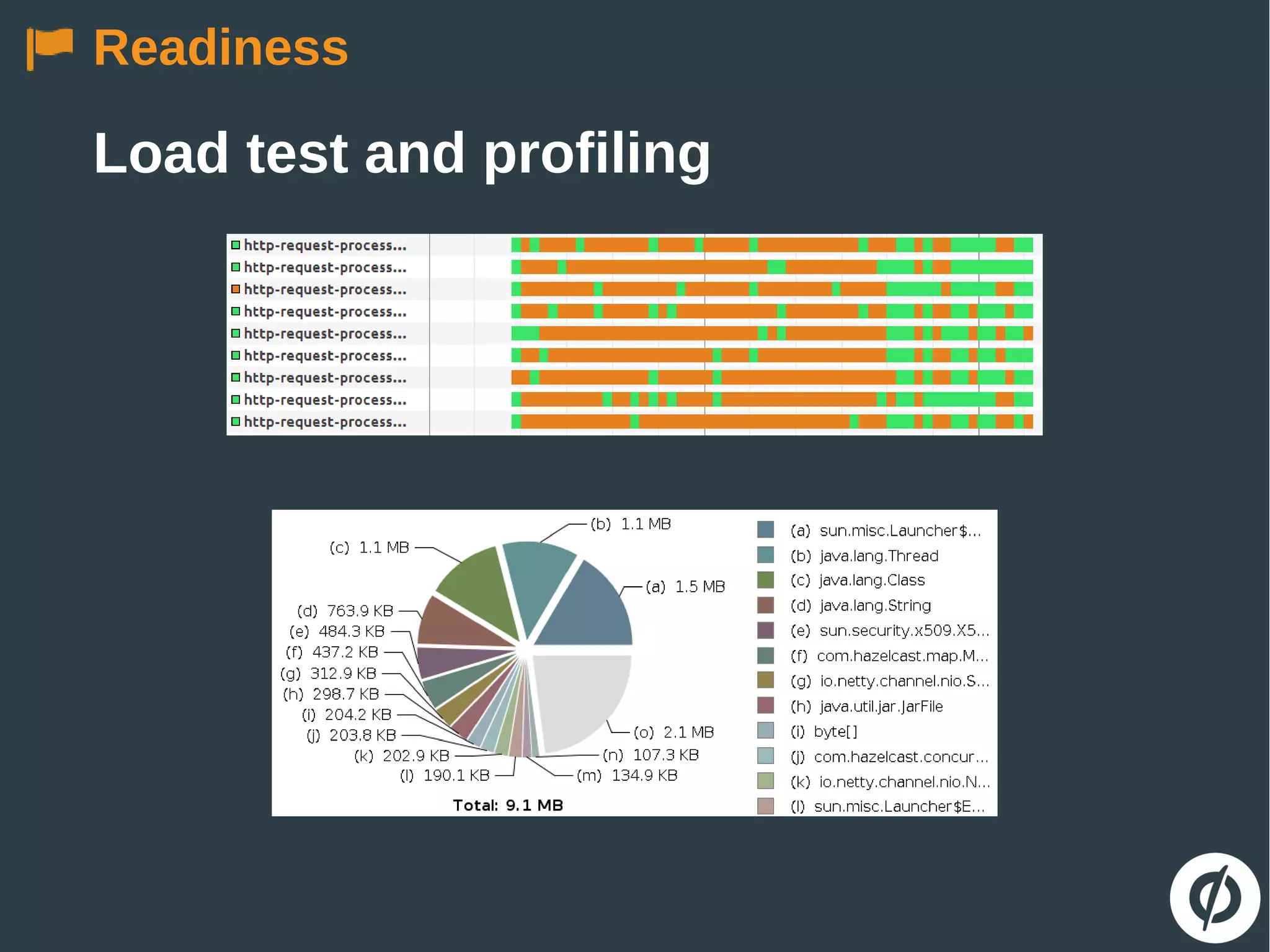
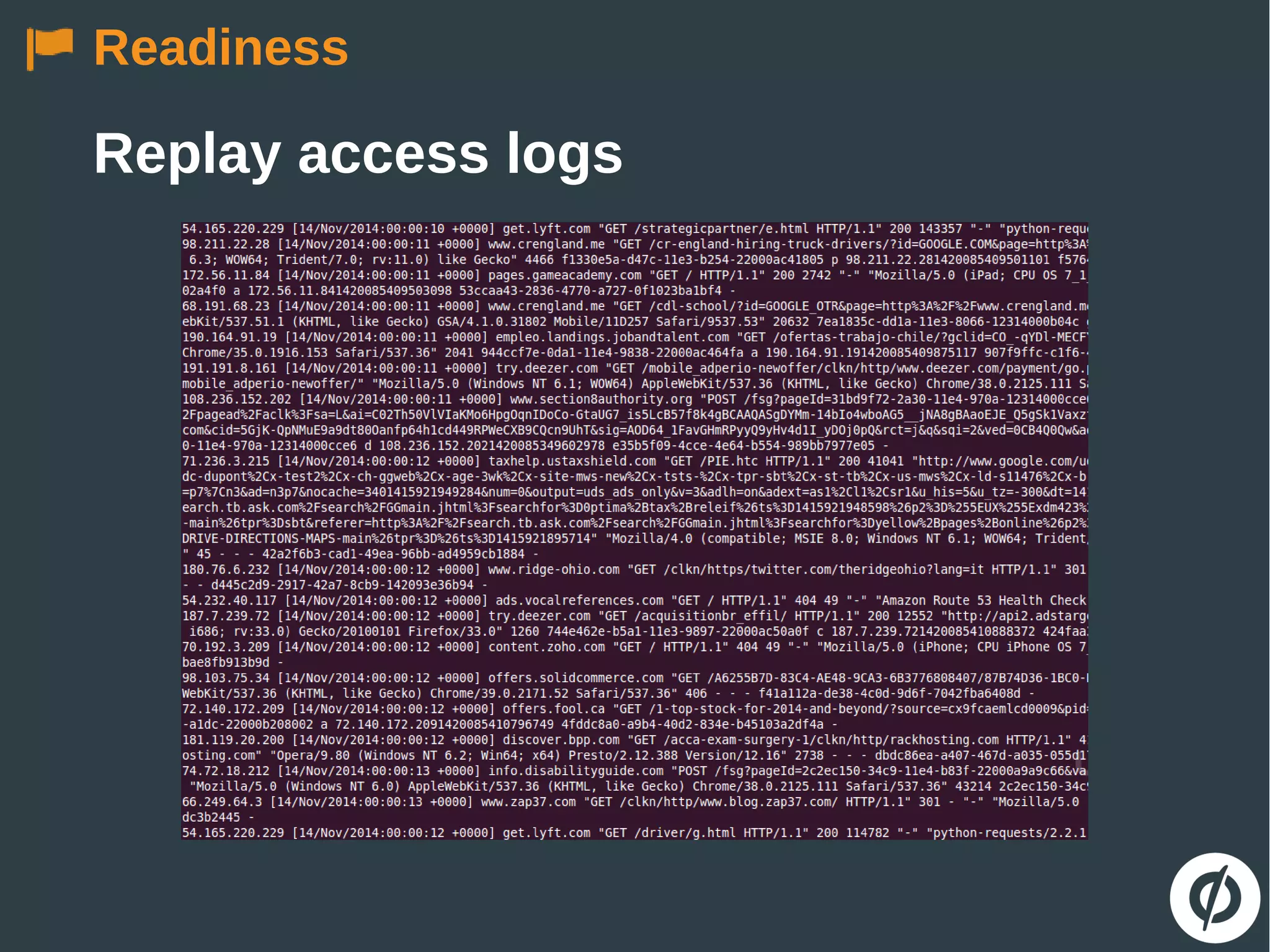
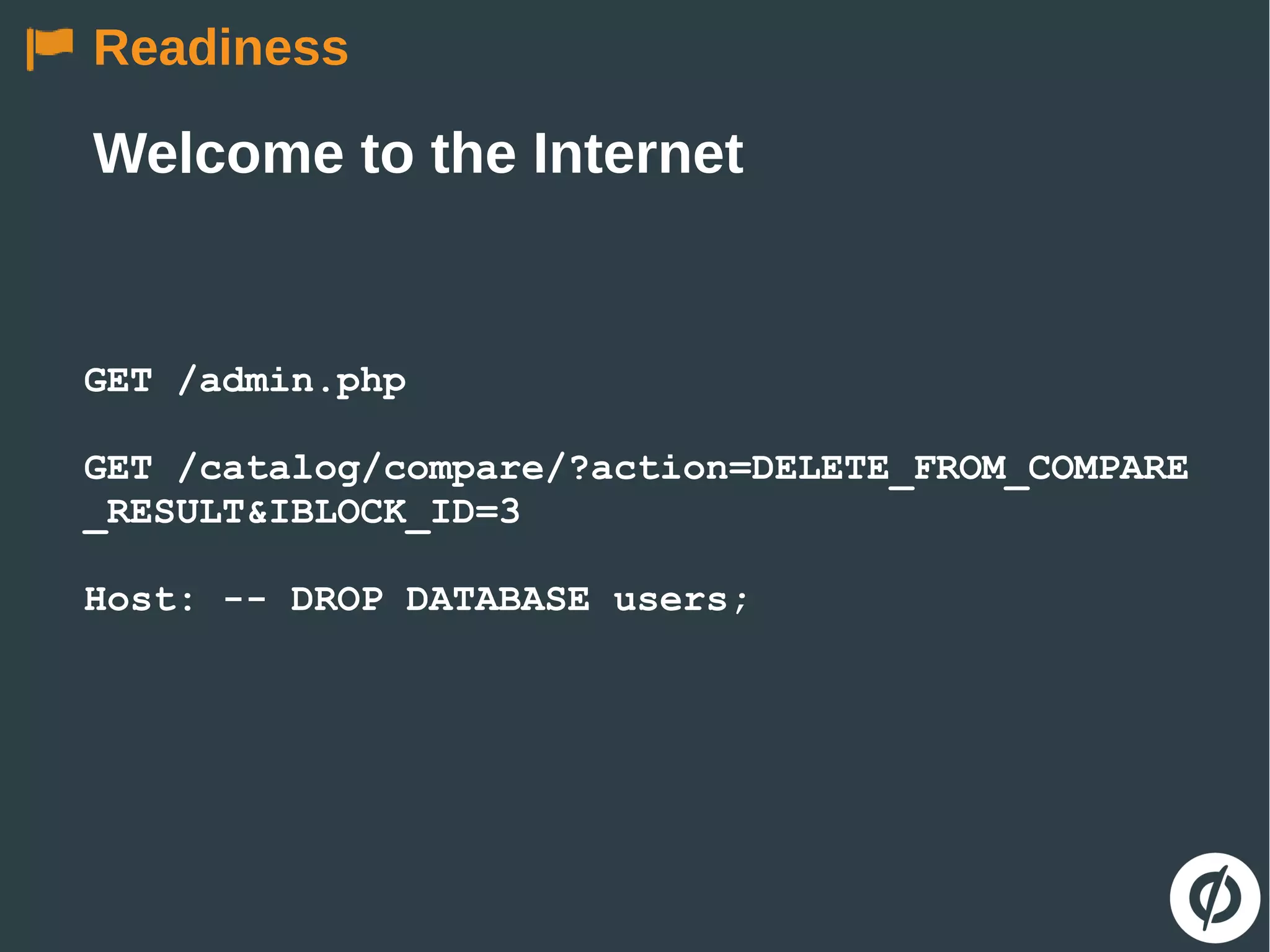
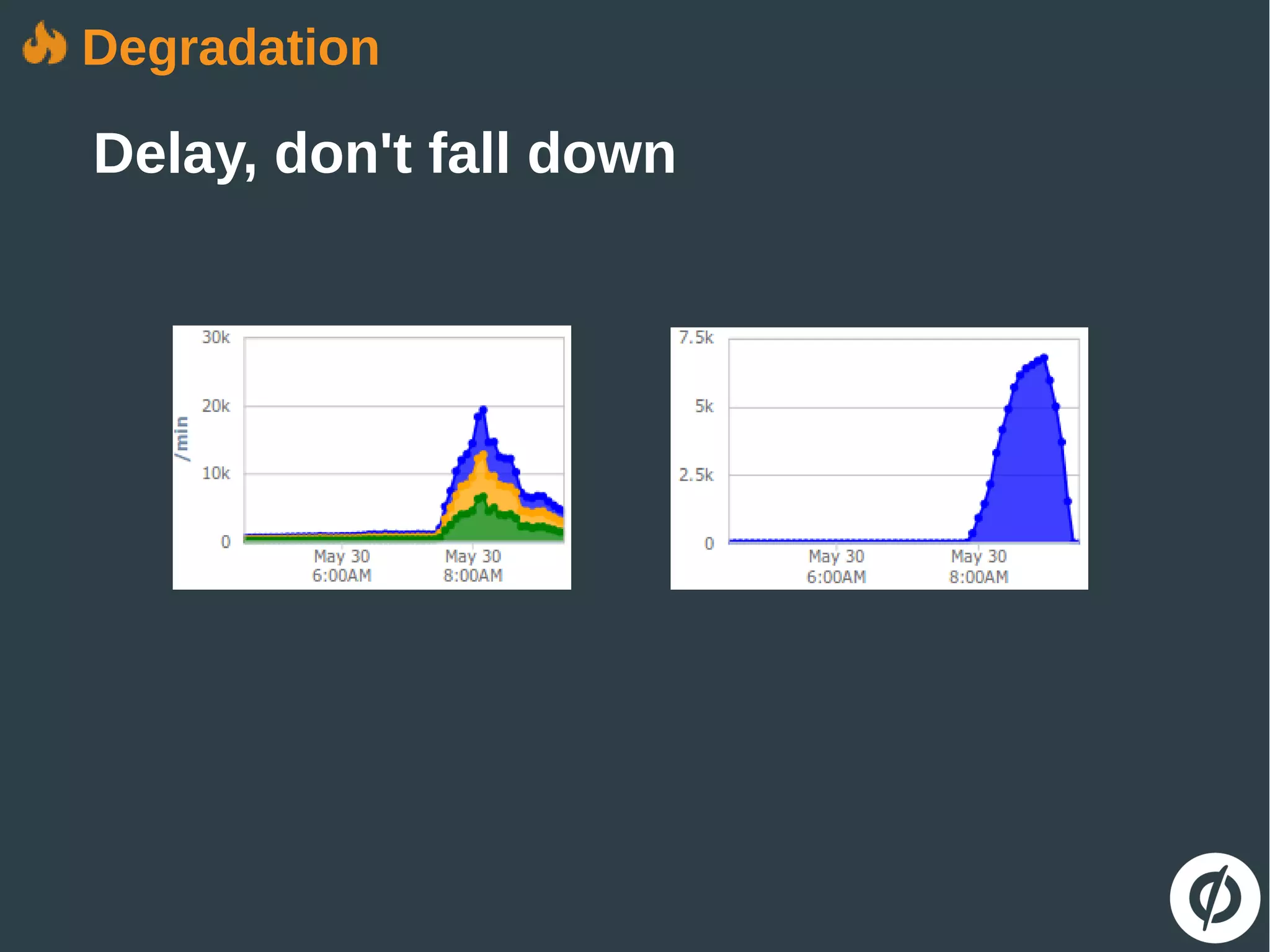
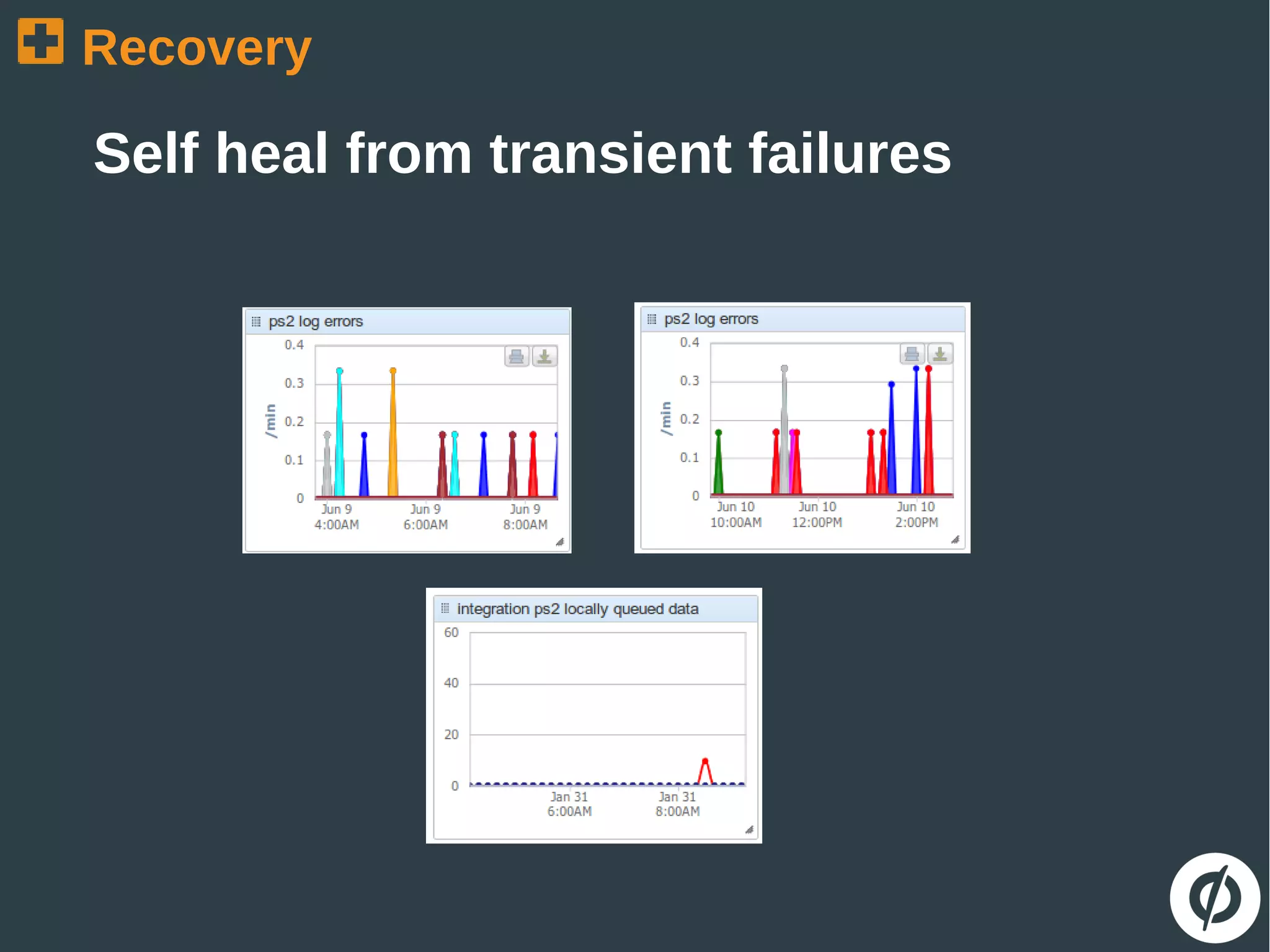
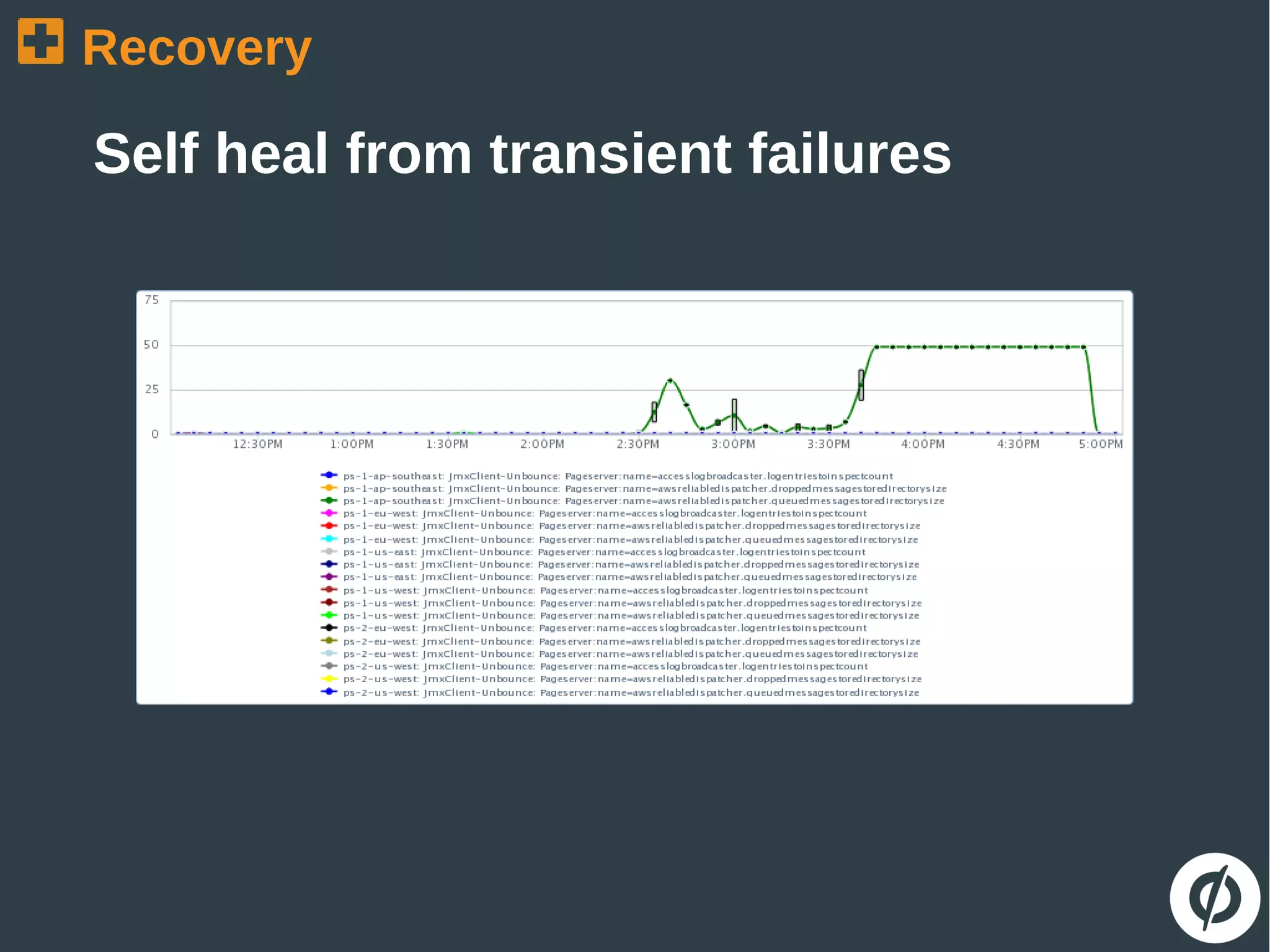
The document discusses the challenges and strategies in building robust applications capable of handling heavy web traffic and potential failures. It emphasizes the importance of strategies such as load testing, queue decoupling, and healthy logging for system recovery and stability. The overall message revolves around viewing failures as opportunities for improvement and implementing defensive coding practices.