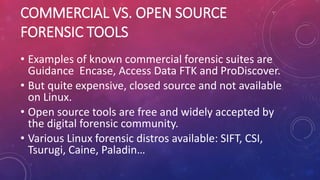
Digital forensics involves the preservation, collection, and analysis of digital evidence using scientifically proven methods to reconstruct events. Key aspects include various branches like computer and mobile forensics, phases such as assessment, acquisition, analysis, and reporting, and concepts like the order of volatility and chain of custody. Tools for digital forensics can be commercial or open-source, with a preference for the latter due to cost and accessibility.

![DEFINITION
Digital forensics can be defined as:
“The use of scientifically derived and proven methods
toward the preservation, collection,validation,
identification, analysis, interpretation, documentation
and presentation of digital evidence derived from digital
sources for the purpose of facilitating or furthering the
reconstruction of events [...]”,
Digital Forensic Research Workshop (DFRWS), 2001](https://image.slidesharecdn.com/dfintro-220923143014-a82ec230/85/Brief-introduction-to-digital-forensics-2-320.jpg)