Embed presentation
Download to read offline





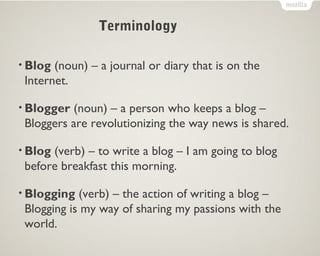

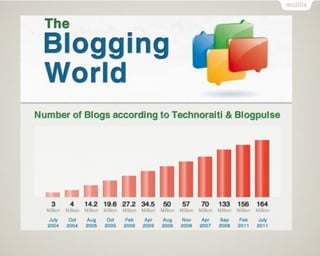




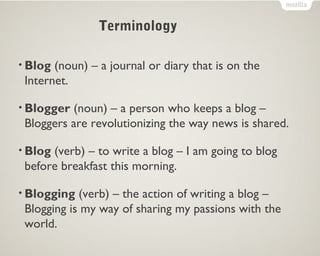
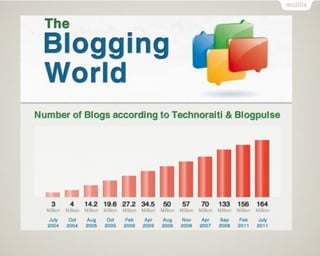
The document discusses the concept of a blog, defining it as an online journal or diary and the role of a blogger who contributes to this medium. It highlights how bloggers are transforming news dissemination and emphasizes the personal nature of blogging as a means of sharing passions. Additionally, the text includes a thank you note and social media handles.