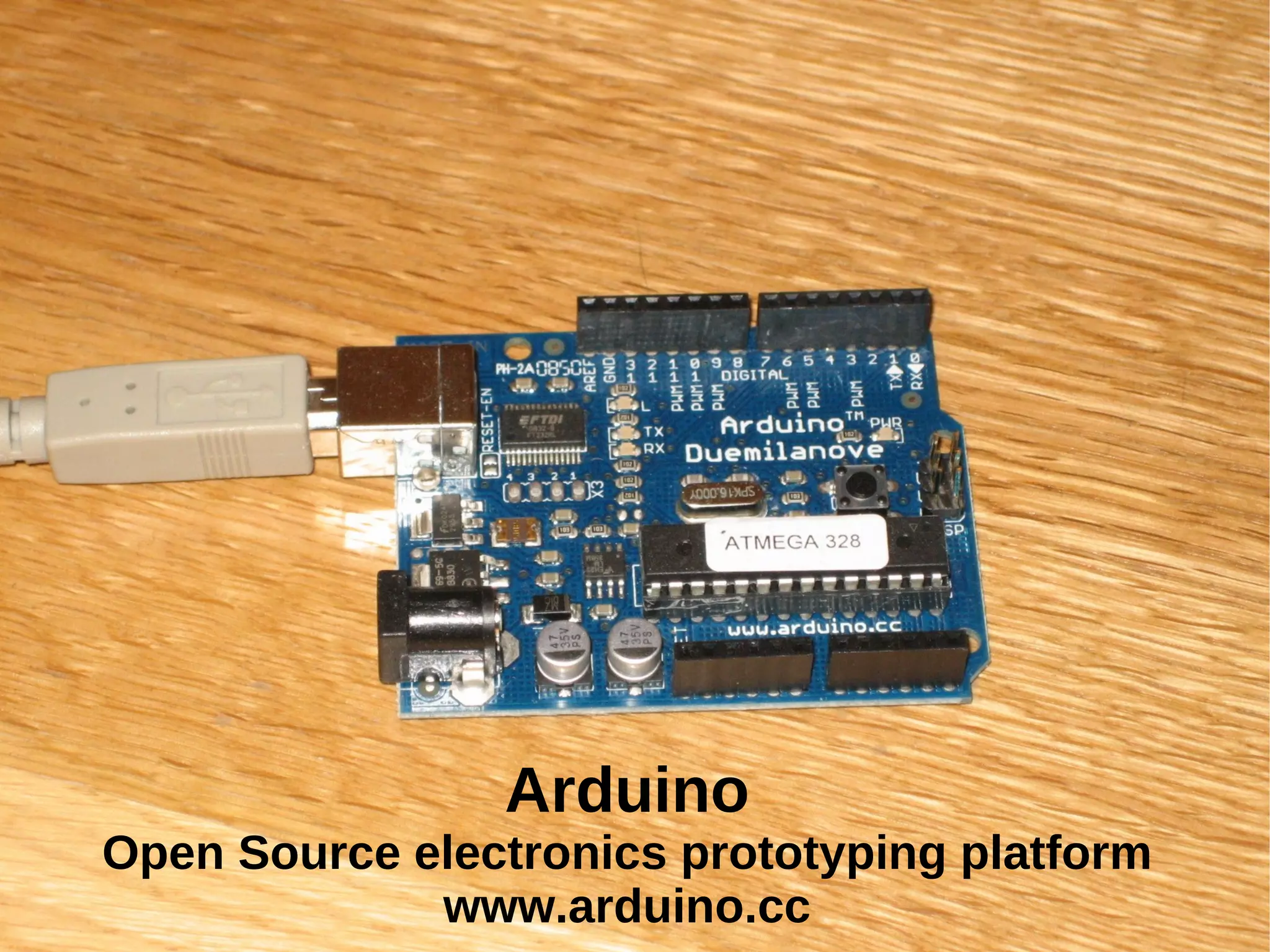
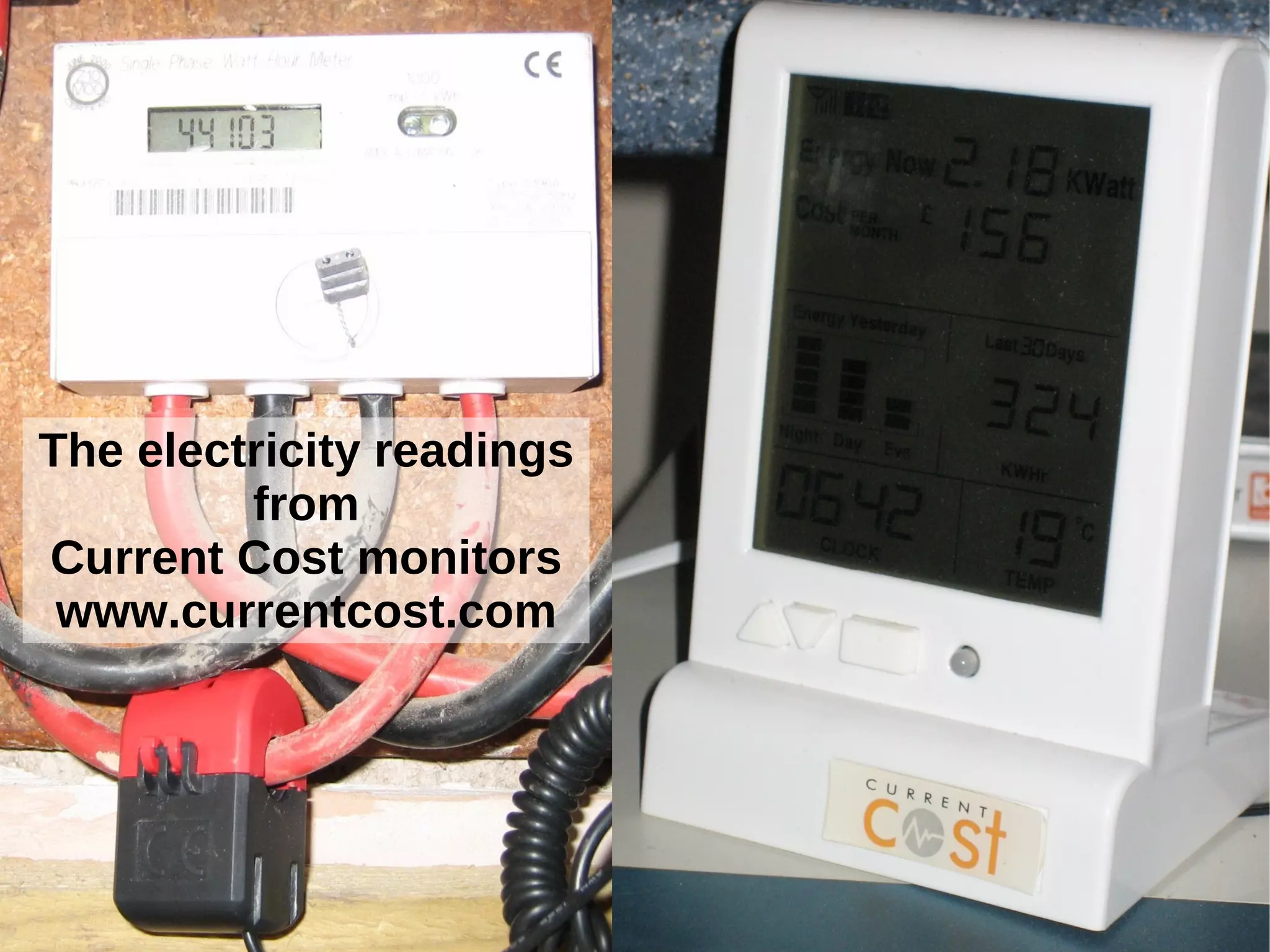
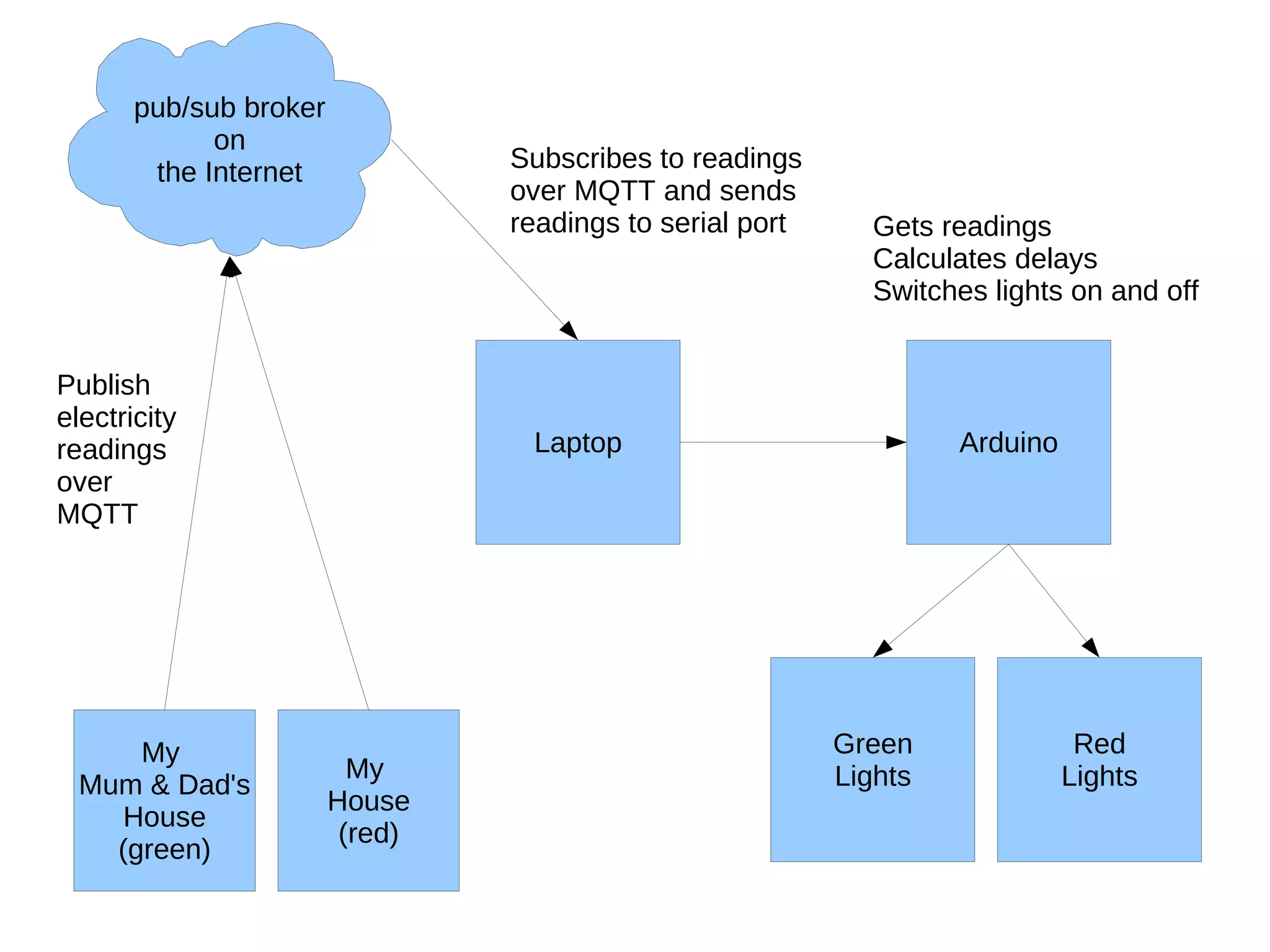
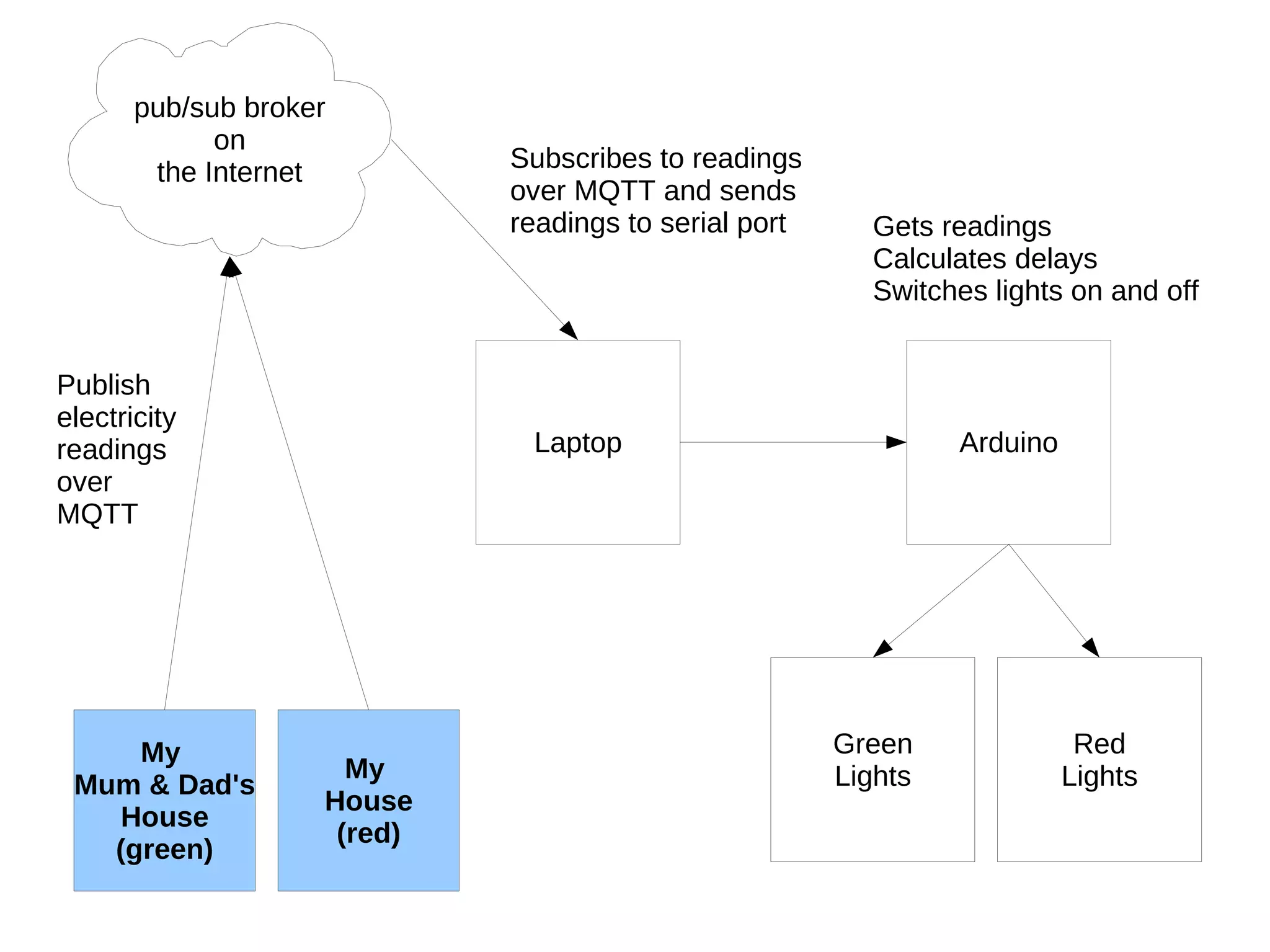
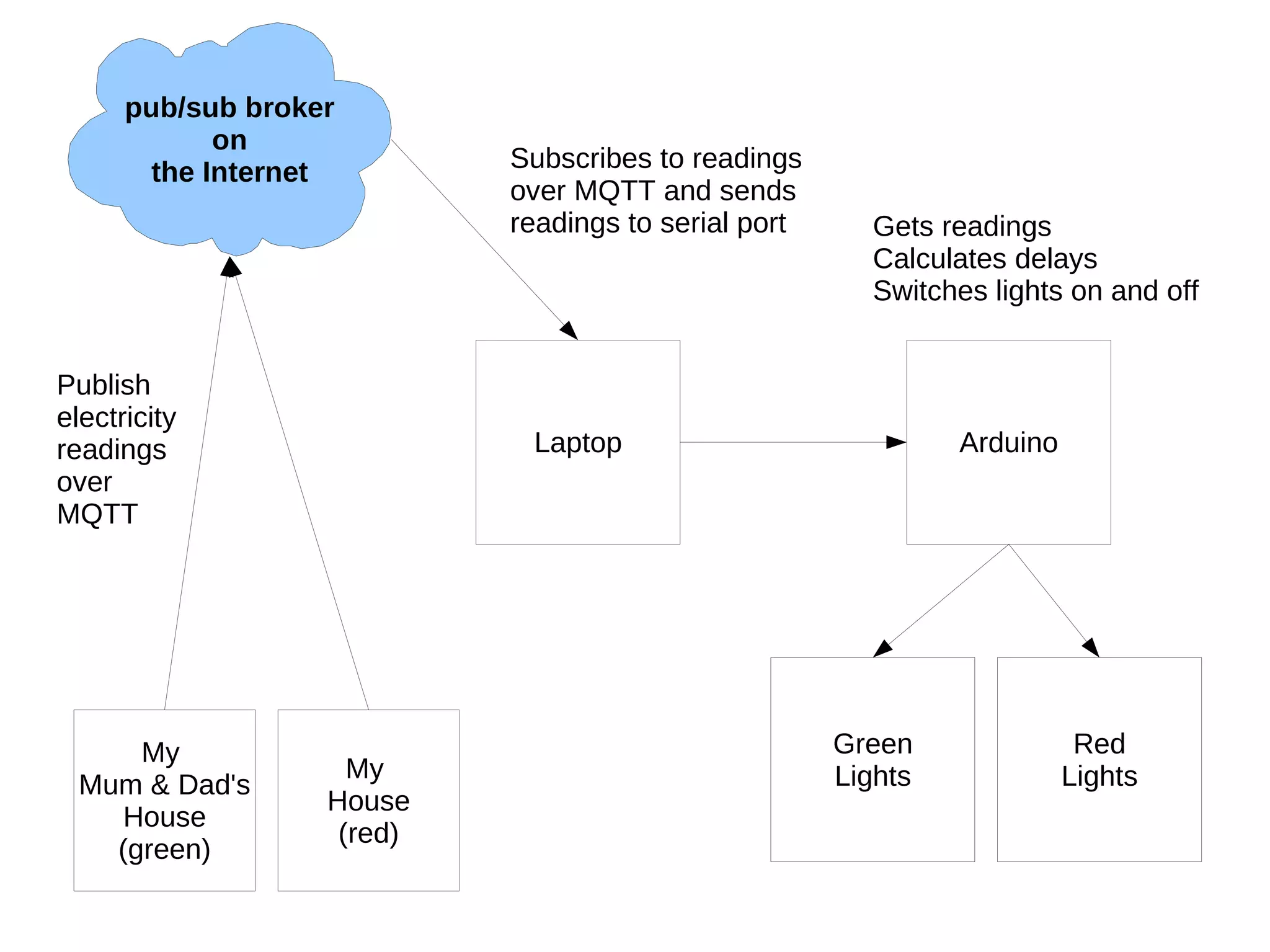
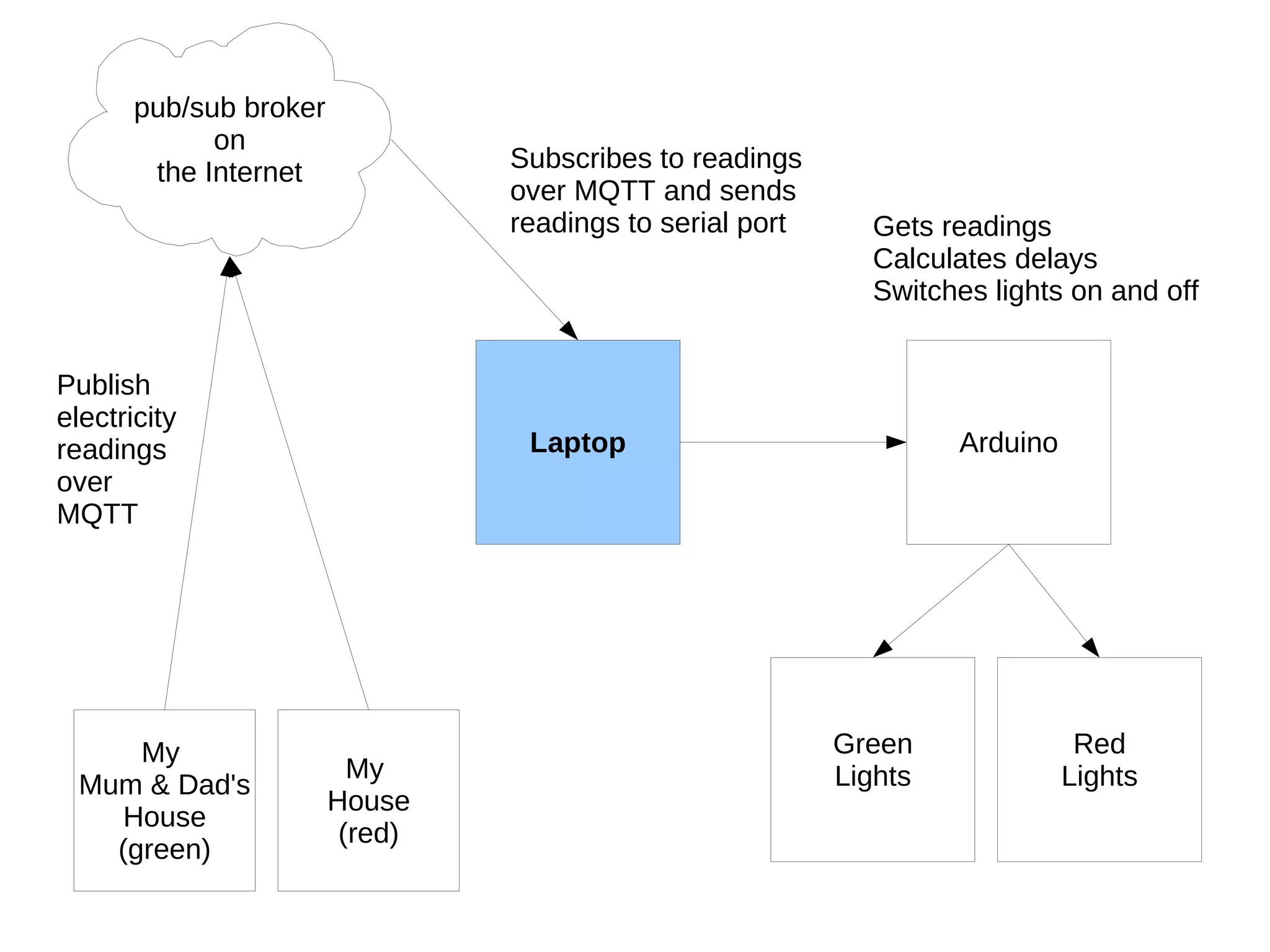
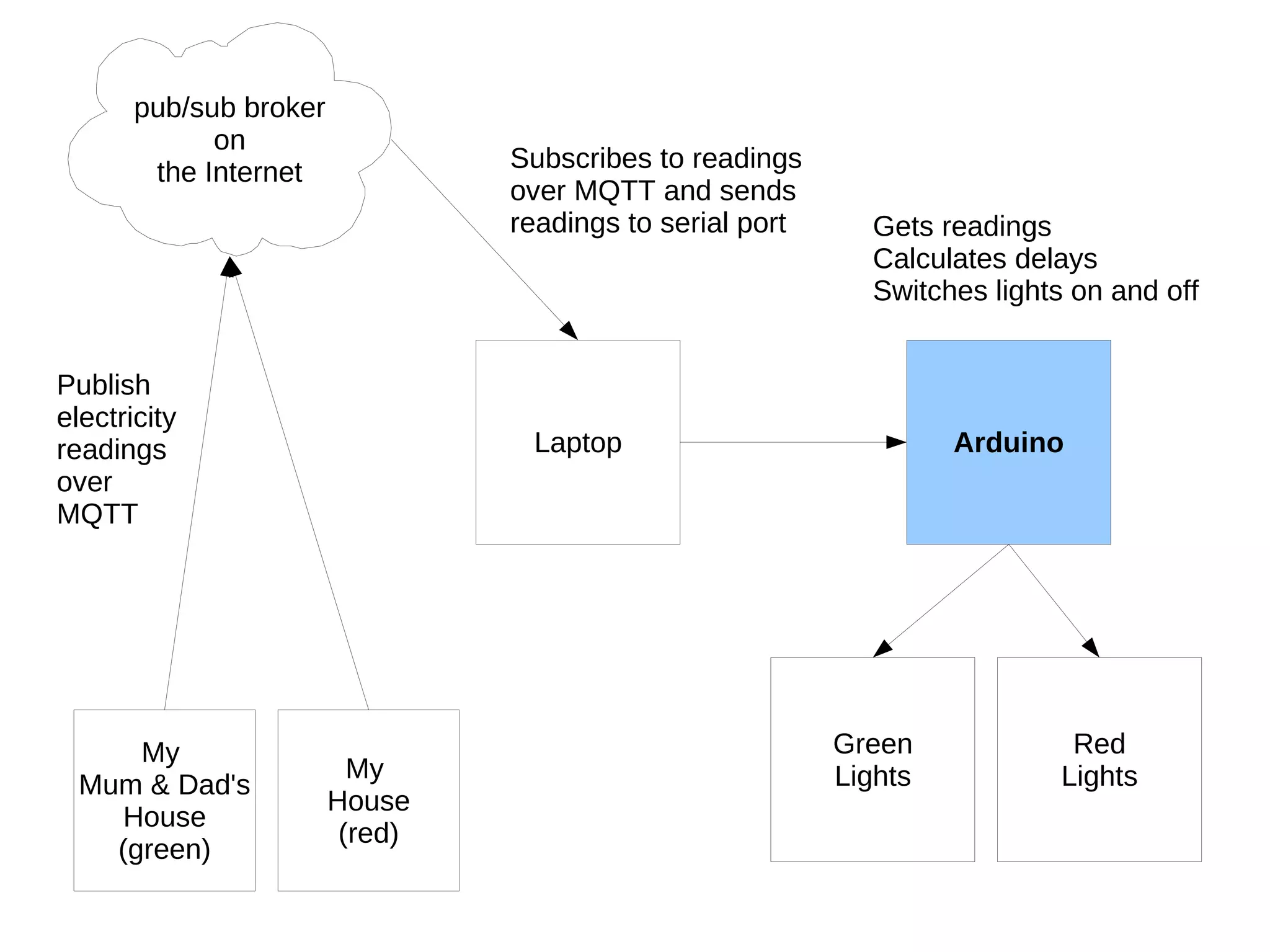
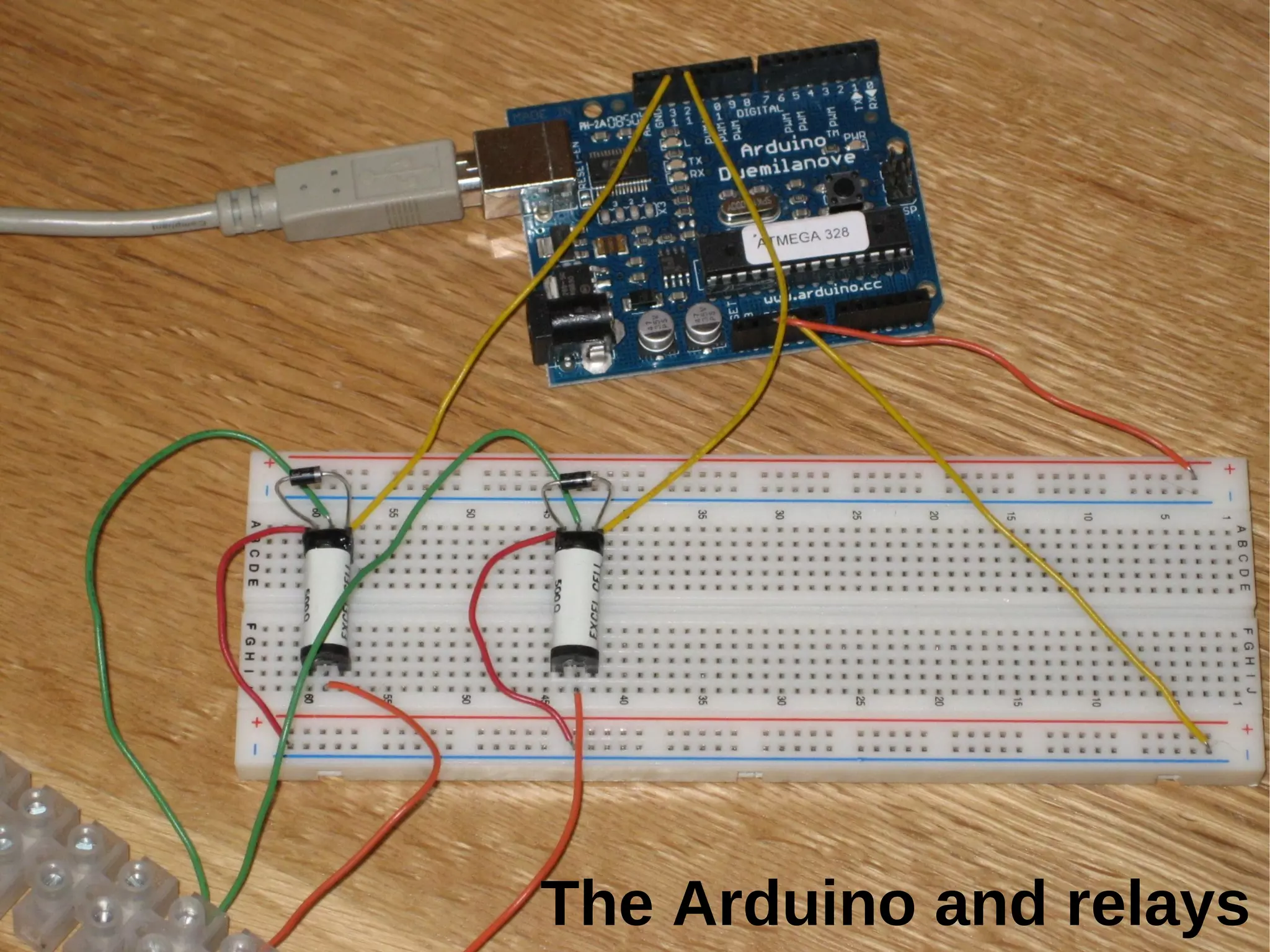
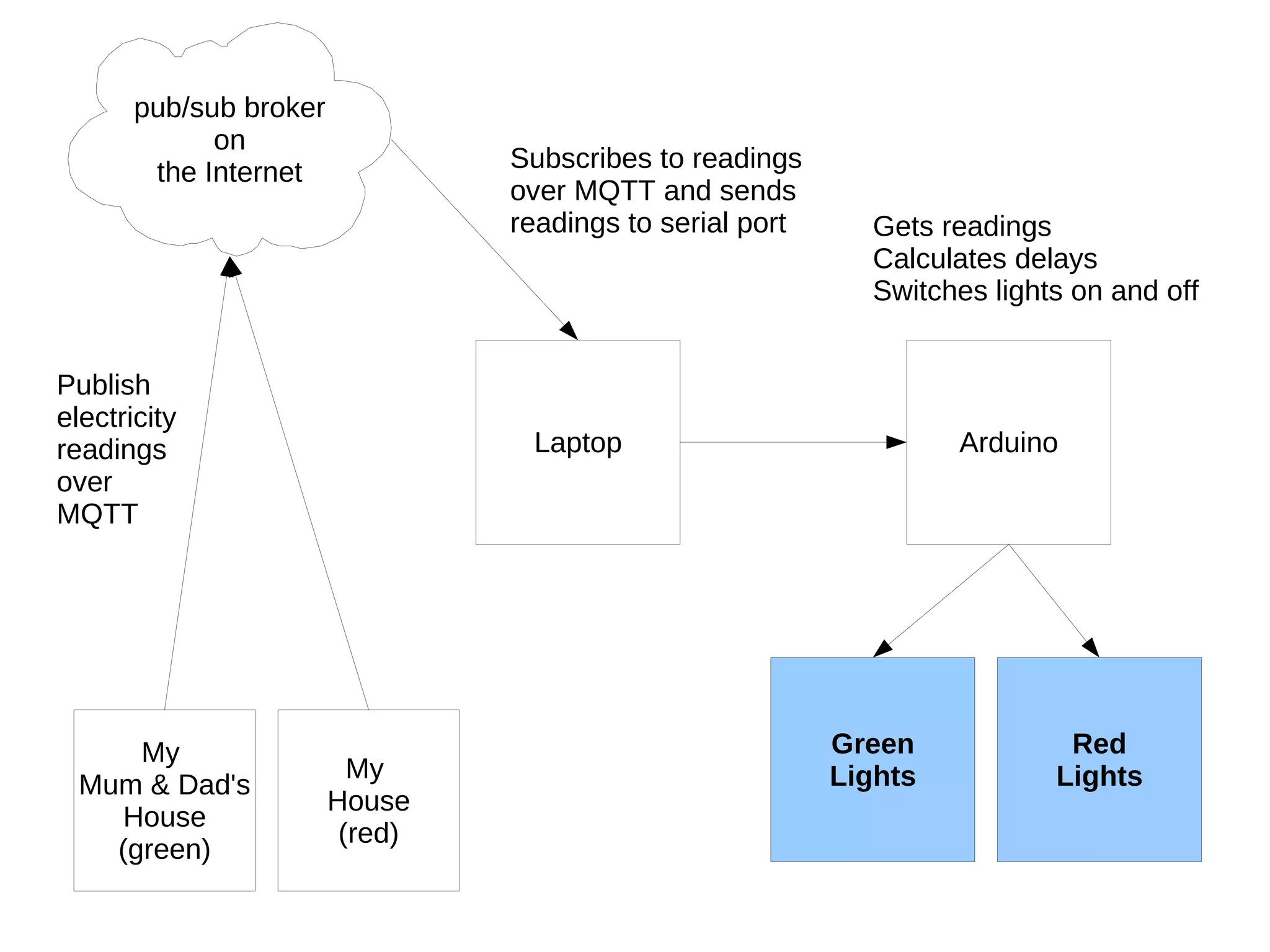
The document describes a Christmas project by Laura Cowen using Arduino to monitor and control electricity readings from Current Cost monitors. It details how electricity readings are published and subscribed via MQTT to switch lights on and off in both her house and her parents' house. The project also acknowledges contributions from several individuals.