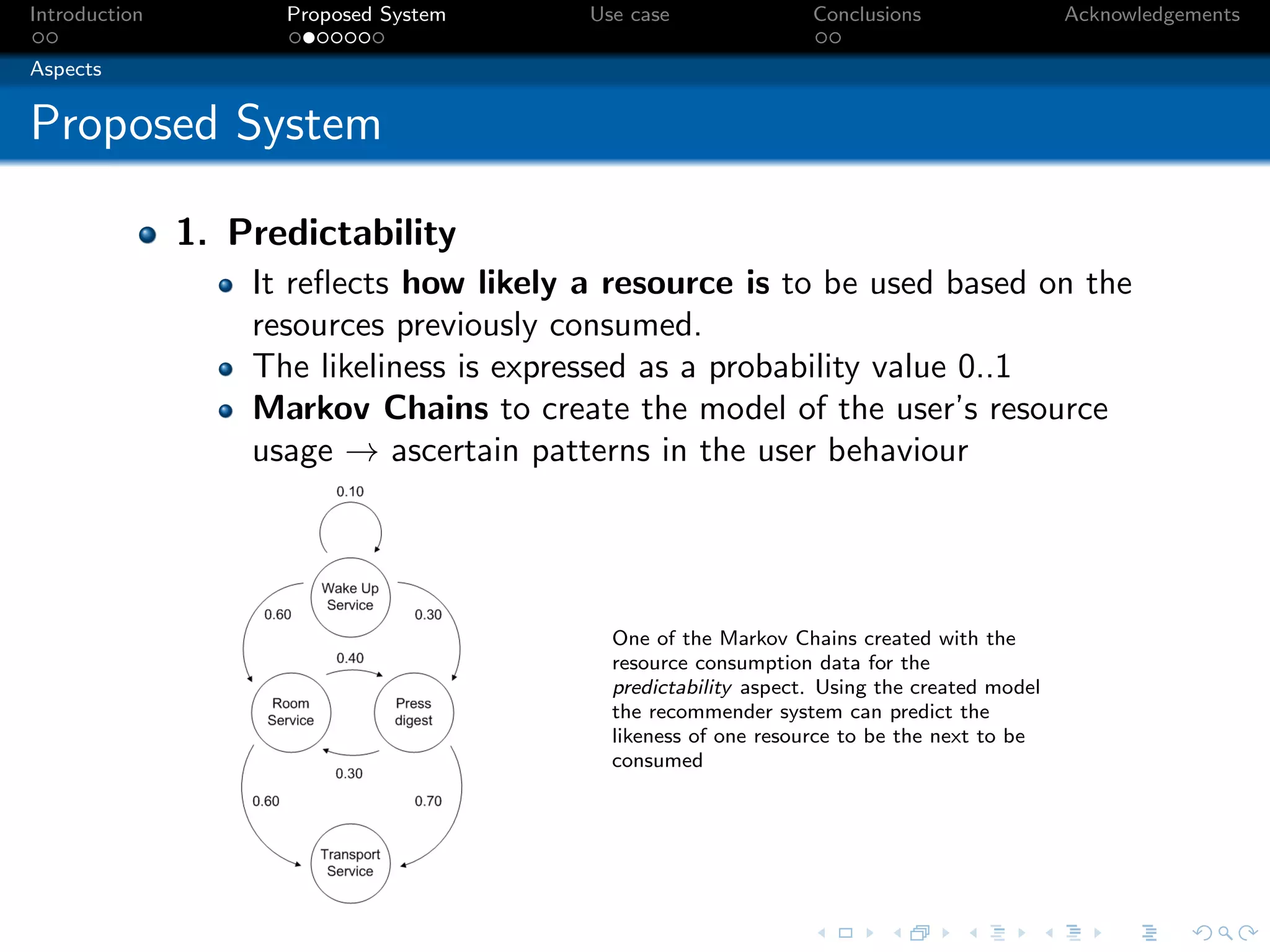
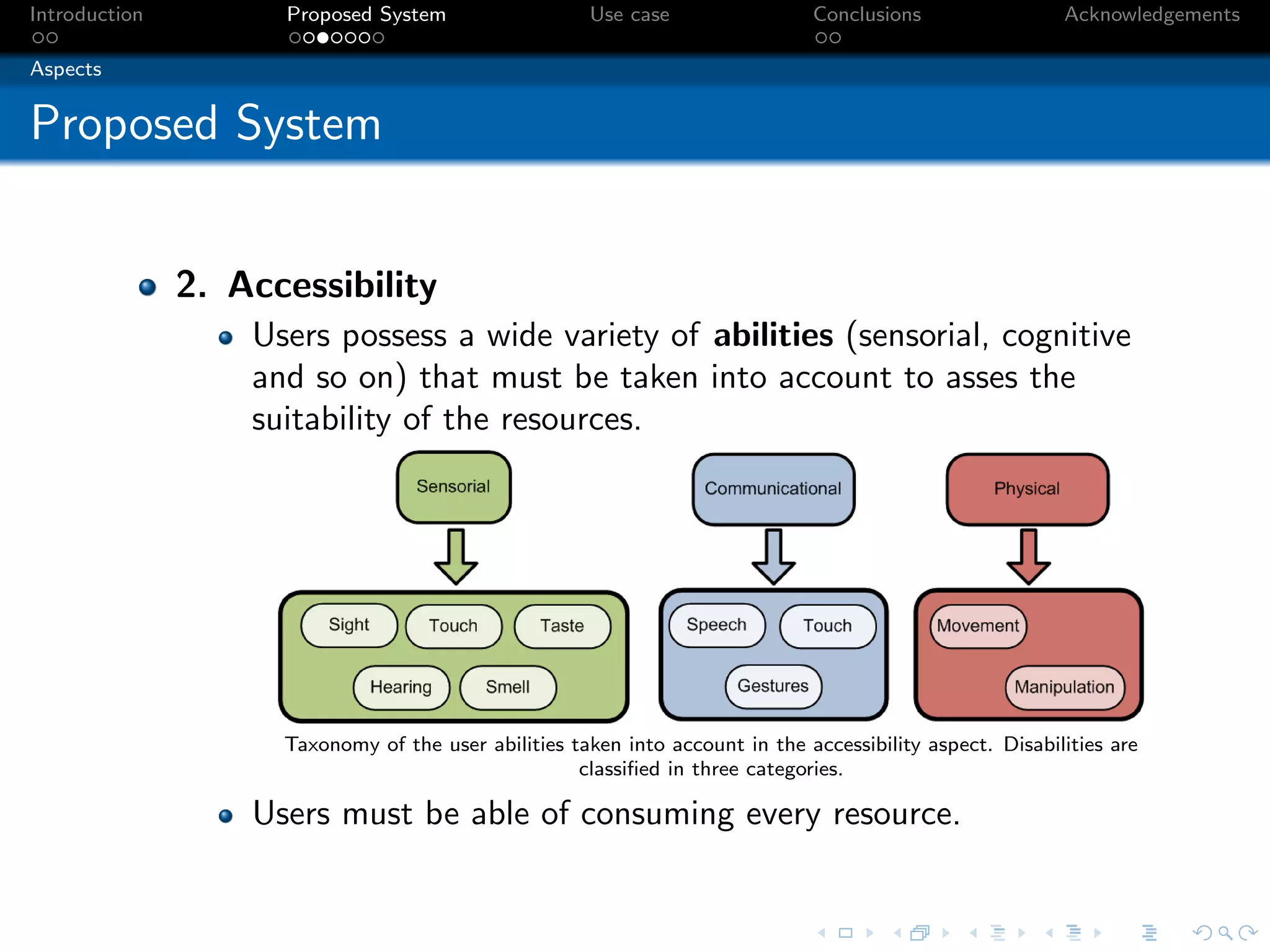
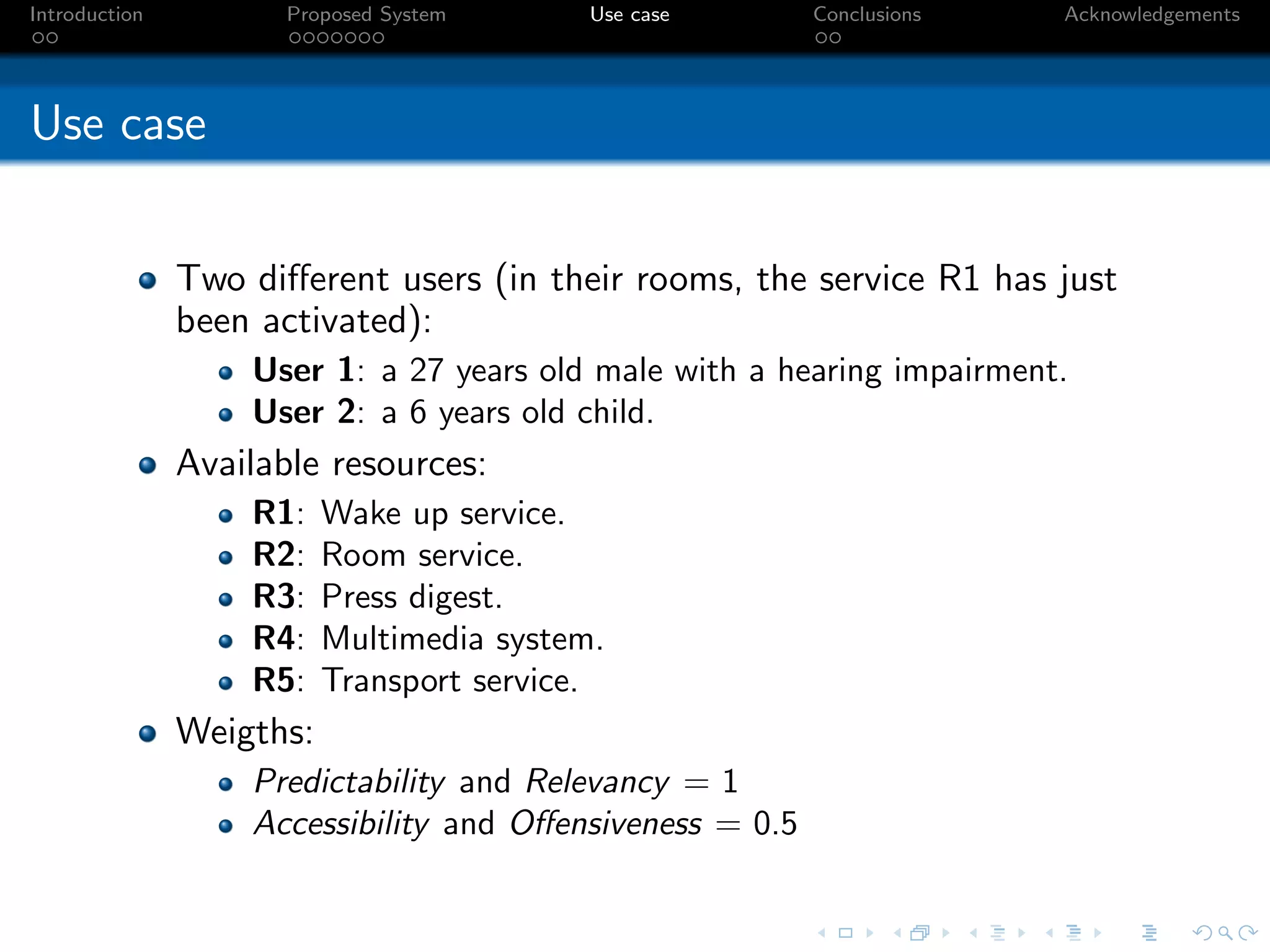
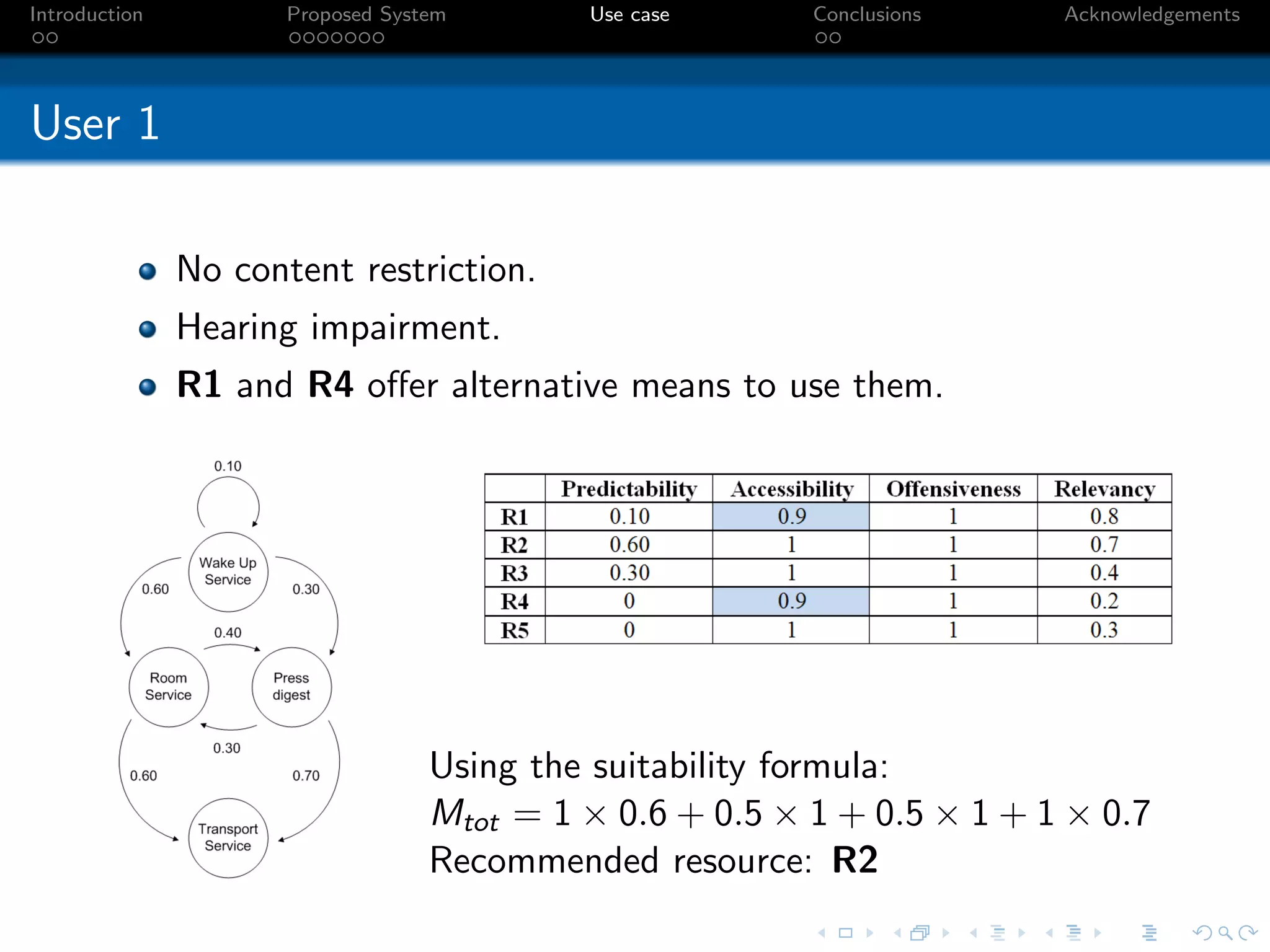
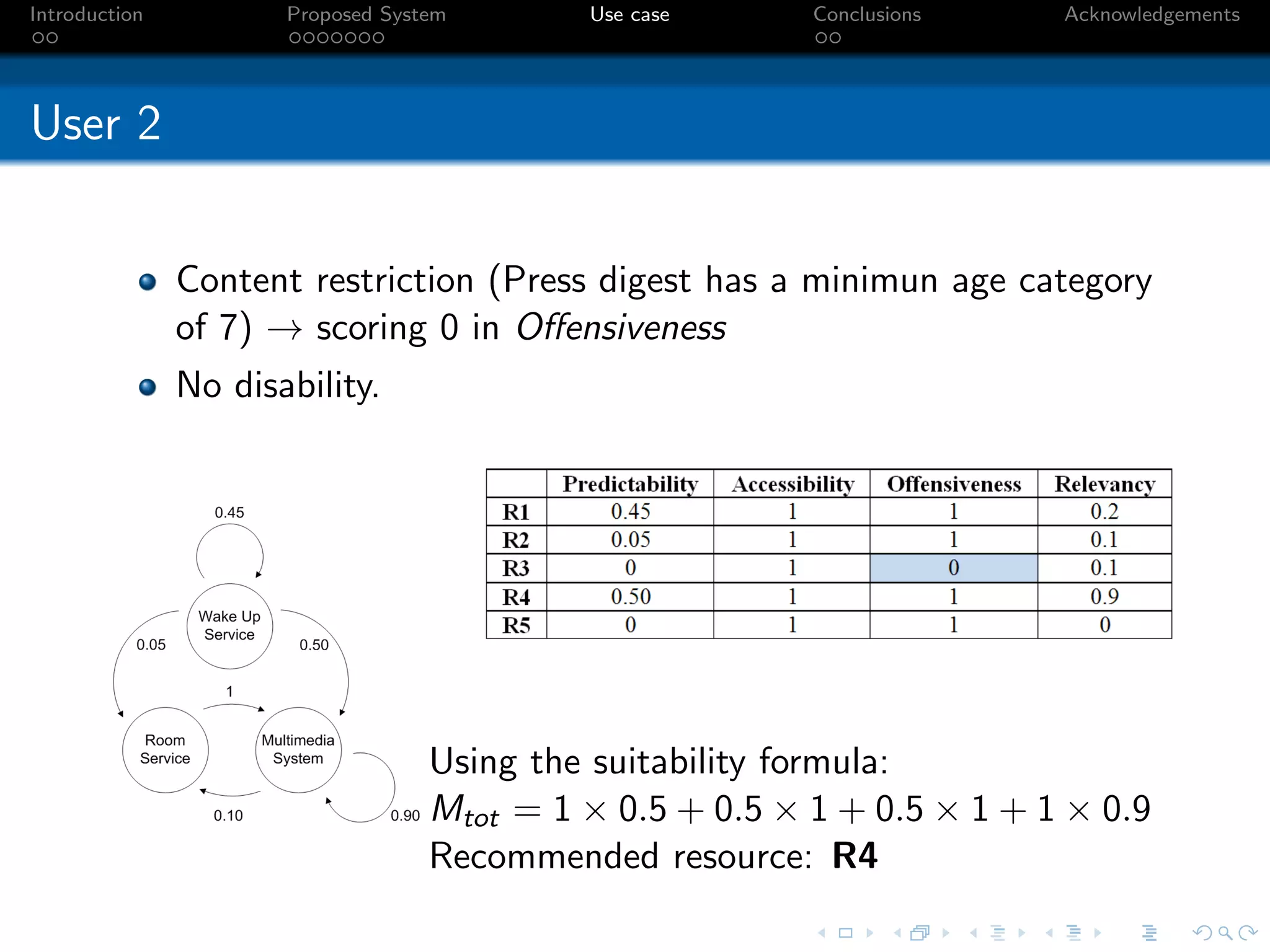
This document proposes an aspect-based resource recommendation system for smart hotels. It describes resources as physical services, virtual services, multimedia content or other information. It defines aspects to describe resources, including predictability, accessibility, relevancy and offensiveness. The system calculates a suitability value for each resource based on aspect values and user-defined weights. Two use cases demonstrate how the system recommends different resources to users based on their profiles and context. The system has advantages of being applicable across resource types and configurable, but limitations around predictive modeling and needing additional aspects.