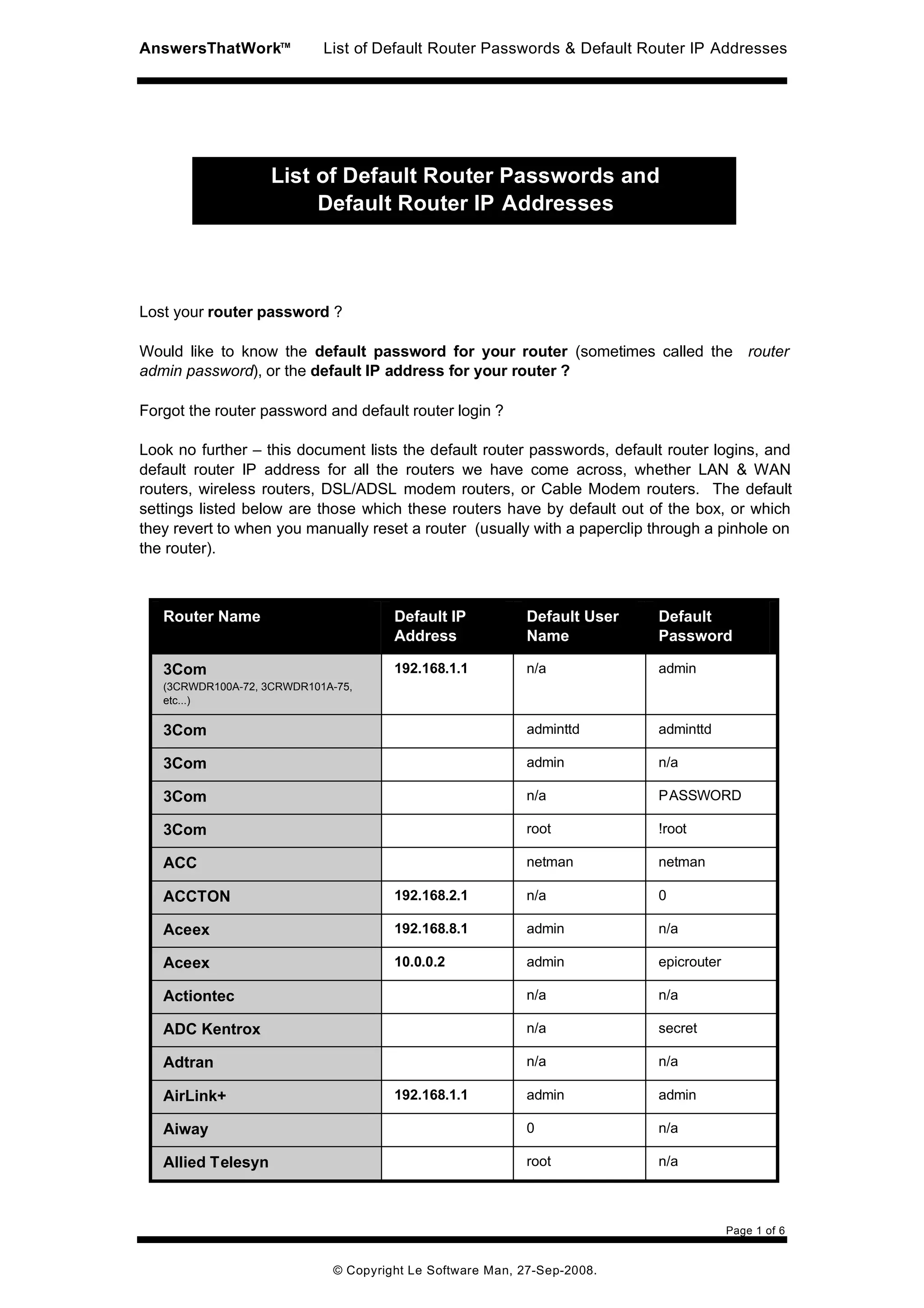
This document lists default router passwords, usernames, and IP addresses for many common router models. It provides this information to help users who have forgotten or lost their router's credentials. The list includes 3 columns for each router: the router name, default IP address, default username and default password. There are over 100 routers included in the list, covering brands like Linksys, D-Link, Netgear, Cisco and others. The passwords provided are those assigned at the factory or after a router reset.