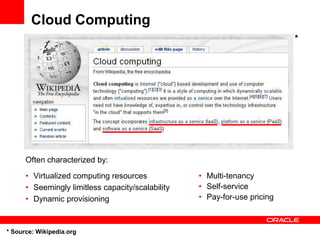
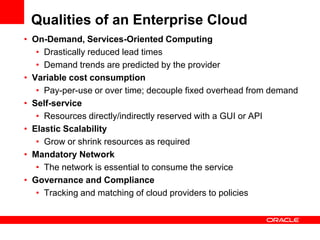
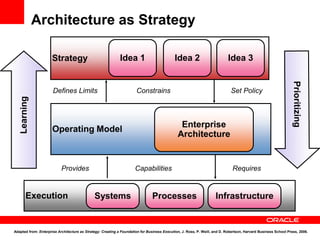
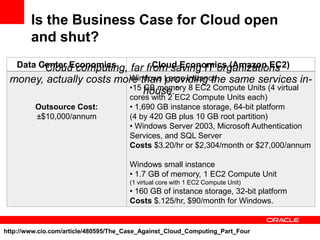
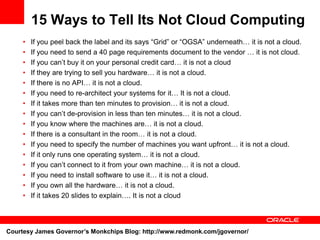
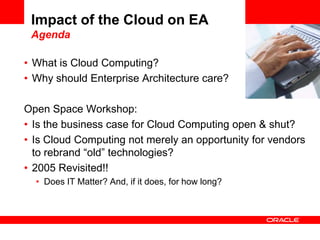
The document discusses the impact of cloud computing on enterprise architecture (EA), emphasizing its characteristics such as scalability, self-service, and governance. It analyzes when cloud computing is a suitable fit for organizations, considering factors like independence of processes and applications, and highlights the potential costs associated with cloud services compared to in-house solutions. Additionally, it identifies misconceptions and criteria to differentiate genuine cloud services from traditional technologies rebranded as cloud computing.