Embed presentation
Download as PDF, PPTX



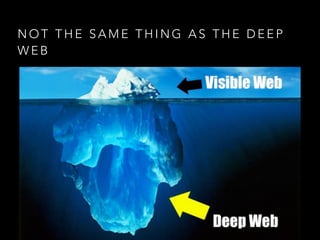

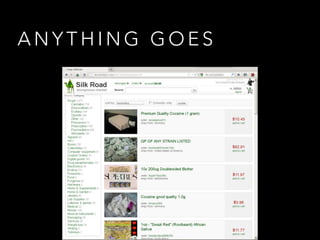
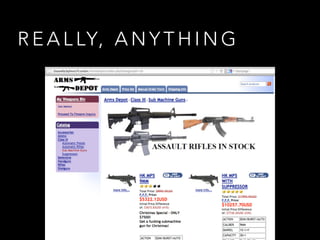
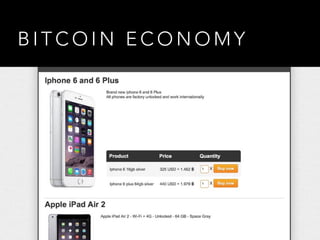


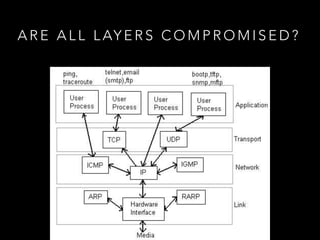



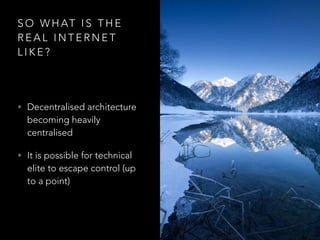


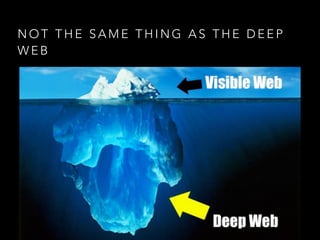
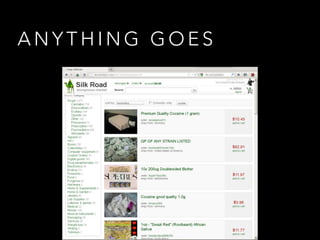
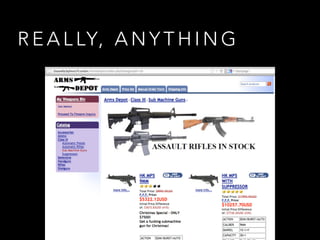
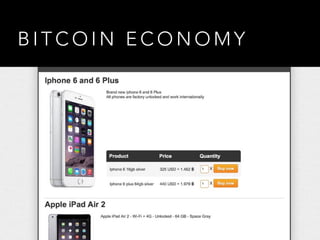
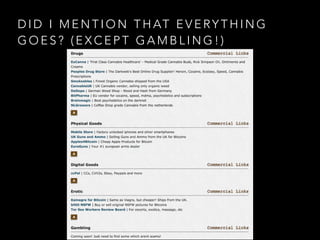
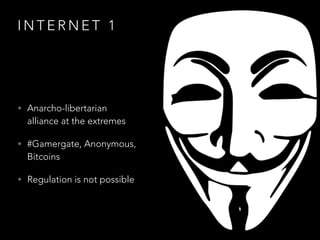
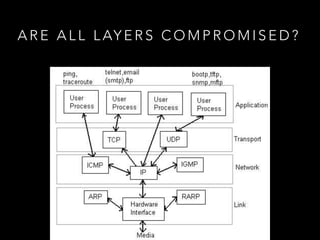
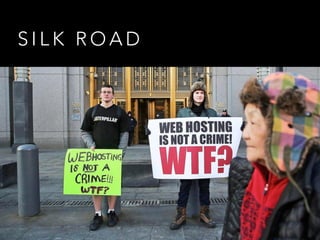
There are two versions of the Internet according to the author. Internet 1 is decentralized and libertarian, allowing anything to be discussed but also housing illegal dark web marketplaces. Internet 2 is centralized and monitored by governments and corporations, eroding privacy and freedom. The real Internet is somewhere in between, with technical users still able to circumvent some control but architecture becoming more centralized over time.