A Secure and Efficient Cloud centric Internet of Medical Things-Enabled Smart Healthcare system
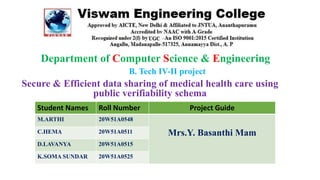
- 1. Department of Computer Science & Engineering B. Tech IV-II project Secure & Efficient data sharing of medical health care using public verifiability schema Student Names Roll Number Project Guide M.ARTHI 20W51A0548 Mrs.Y. Basanthi Mam C.HEMA 20W51A0511 D.LAVANYA 20W51A0515 K.SOMA SUNDAR 20W51A0525
- 2. A Secure & Efficient Cloud-Centric Internet of Medical Things-Enabled Smart Healthcare System with Public Verifiability Scheme
- 3. AGENDA 1.Abstract 2.Existing system 3.Drawbacks 4.Proposed system 5.Advantages 6.Architecture 7.Modules 8.Technology Java 9.Software Requirements 10.Hardware Requirements 11.Refrences
- 4. ABSTRACT The potential of the Internet of Medical Things (IoMT) technology for interconnecting the biomedical sensors in e-health has ameliorated the people’s living standards. Another technology recognized in the recent e-healthcare is outsourcing the medical data to the cloud. There are, however, several stipulations for adopting these two technologies. The most difficult is the privacy of medical data and the challenge resulting from the resource constraint environment of sensor devices. In this paper, we present the state-of-the-art secure and efficient cloud-centric IoMTenabled smart health care system with public verifiability. The system novelty implements an escrow-free identity- based aggregate signcryption (EF-IDASC) scheme to secure data transmission, which is also proposed in this article. The proposed smart healthcare system fetches the medical datafrom multiple sensors implanted on the patient’s body, signcrypts and aggregates them under the proposed EFIDASC scheme, and outsources the data on the medical cloud server via smartphone.
- 5. EXISITING SYSTEM • 1.Li et a present an Identity-based signcryption for low-power devices (sensors) in an online/offline setting that simultaneously fulfills the authentication and confidentiality without authenticating a recipient’s public key separately. • 2.Omala et al. proposed a lightweight certificateless signcryption (CLSC) scheme for secure data transmission for the WBAN system. Yin et al. • 3.Give an efficient hybrid signcryption scheme in a certificateless setting for secure communication for WSNs. • 4.Unlike 1 scheme 2schemes and 3 scheme are resistant to key escrow attack. • 5.Its difficult to handle patient data • 6.Its doesn’t have more security.
- 6. Drawbacks The most difficult is the privacy of medical data. Lack of infrastructure Cyber Security & Privacy issues Fewer customizability possibilities Inaccurate data Clinician Burnout caused by EHRs
- 7. Proposed system 1.First, we propose an escrow-free identity-based aggregated signcryption (EF-IDASC) scheme, which addresses the key escrow problem based on the idea given in the existing system. 2.The system proves that the proposed EF-IDASC scheme is existentially un forgeable under chosen message attack (EUFCMA) and adaptively indistinguishable under the chosen cipher text attack (IND- CCA) in the random oracle model (ROM) and well-known Bilinear Diffie-Hellman Problem (BDHP). 3.The system compares the proposed EF-IDASC scheme with other related signcryption schemes, in which we show that the proposed scheme consumes the least energy as compared to related schemes. Then, we propose a secure D2D aggregated-data communication protocol in the cloud-centric IoMT environment for smart health care, that security is based on the proposed EF-IDASC scheme 4.Further, we evaluate the energy consumption cost (in mJ) in terms of computation, storage and communication. 5.The proposed secure healthcare system achieves the patient’s anonymity, pubic auditing of the integrity of stored data on the cloud, and mutual authenticity of patient’s data with public verifiability.
- 8. Advantages An effective design of system which it ensures that data could not be altered or modifies by any adversary. The Any forgery or modification in the signcrypted data will be caught by the SD during un signcryption. Assuming the BDH problem is hard to solve, any malicious attacker cannot modify the original data.
- 9. ARCHITECTURE Fig. 1. Detailed architecture of proposed secure aggregated signcryption system
- 10. Network manager(NM): The NM is a semi-trusted authority that initializes the system, computes its master and public key. It authenticates an entity and issues a partial private key to it. Key protection servers (KPSs):KPSs protect the private key of an entity using their secret keys and issue a protected private key share to it. They perform computations on the cloud to mitigate the computation overhead. Bio-medical sensor (BMS):It is a tiny sensor that has limited storage space, battery life, and computation power. It is installed either on/outside the patient’s body (wearable sensors) or deployed in the patient’s tissues (implanted sensors). Personal assisted device (PAD):It is a data sink with sufficient computation and storage but not trustworthy as it is effortless for an attacker to retrieve the patient’s sensitive data by physically stealing the phone or statistically attacking it. Medical cloud server (MCS):It is a semi-trusted cloud server, which stores the patient’s PHI. It also validates the PHI and provides the accessibility of PHI to SD. Server Device (SD):A device on the medical institution's side can access the patient's PHI on MCS and diagnose the patient's diseases based on their resulting PHI.
- 11. MODULES 1. IOT based devices 2. Health care 3. Medical cloud services 4. Key protection public key
- 12. TECHNOLOGY JAVA DOMAINS : Cloud computing, Iot 1. Cloud computing: It is used for health care enables medical proffessionals to access a varied range of patient data It is also used for saving the patient data It helps share healthcare data,offer patient health insurance during treatment,prevention and recovery,and enhance availability. 2. Internet of things: The internet of things in healthcare can take many forms — medical devices, public health services, smart sleep technology, medication refills and remote monitoring.
- 13. Software requirements 1.Coding Language - Java/J2EE(JSP,Servlet) 2.Designing - Html, css,javascript. 3.Data Base - MySQL(WAMP Server) 4.IDE - ANACONDA
- 14. HARDWARE REQUIREMENTS • Processor - 13 processor • RAM - 4 GB • Hard Disk - 500 GB • Operating System - Windows Family
- 15. REFERENCES: • 1. Y. Zhang, R. Deng, D. Zheng, J. Li, P. Wu, and J. Cao, “Efficient and robust certificateless signature for data crowdsensing in cloud-assisted industrial IoT,” IEEE Trans. Ind. Informatics, 2019. • 2. M. Kumar and S. Chand, “A Lightweight Cloud-Assisted Identity-based Anonymous Authentication and Key Agreement Protocol for secure Wireless Body Area Network,” IEEE Syst. J., vol. Early acce, 2020 • 3. W. Sun, Z. Cai, Y. Li, F. Liu, S. Fang, and G. Wang, “Security and privacy in the medical Internet of Things: A review,Secur. Commun. Networks, vol. 2018, 2018. • 4. A. Zhang, J. Chen, R. Q. Hu, and Y. Qian, “SeDS: Secure data sharing strategy for D2D communication in LT Advanced networks,” IEEE Trans. Veh. Technol., vol. 65, no. 4, pp. 2659- 2672, 2016. • 5. Z. Li, Z. Yang, and S. Xie, “Computing Resource Trading for Edge Cloud-assisted Internet of Things,” IEEE Trans. Ind.Informatics, 2019. • 6. W. Wang, P. Xu, and L. T. Yang, “Secure data collection, storage and access in cloud-assisted IoT,” IEEE Cloud ComputE., vol. 5, no. 4, pp. 77– 88, 2018.
- 16. 7. D. He, S. Zeadally, and L. Wu, “Certificateless public auditing scheme for cloud-assisted wireless body area networks,” IEEE Syst. J., vol. 12, no. 1, pp. 64–73, 2015. 8. V. Sureshkumar, R. Amin, V. R. Vijaykumar, and S. Rajasekar, “Robust secure communication protocol for smart healthcare system with FPGA implementation,” Futur. Gener. Comput. Syst., 2019. 9. H. Xiong and Z. Qin, “Revocable and scalable certificateless remote authentication protocol with anonymity for wireless body area networks,” IEEE Trans. Inf. forensics Secur., vol. 10, no. 7, pp. 1442– 1455, 2015. 10. J. Shen, S. Chang, J. Shen, Q. Liu, and X. Sun, “A lightweight multi-layer authentication protocol for wireless body area networks,” Futur. Gener. Comput. Syst., vol. 78, pp. 956–963, 2018.